The U.K. National Cyber Security Centre (NCSC) is calling on manufacturers of smart devices to comply with new legislation that prohibits them from using default passwords, effective April 29, 2024.
“The law, known as the Product Security and Telecommunications Infrastructure act (or PSTI act), will help consumers to choose smart devices that have been designed to provide ongoing protection against cyber attacks,” the NCSC said.
To that end, manufacturers are required to not supply devices that use guessable default passwords, provide a point of contact to report security issues, and state the duration for which their devices are expected to receive important security updates.
Default passwords can not only be easily found online, they also act as a vector for threat actors to log in to devices for follow-on exploitation. That said, a unique default password is permissible under the law.
The law, which aims to enforce a set of minimum security standards across the board and prevent vulnerable devices from being corralled into a DDoS botnet like Mirai, applies to the following products that can be connected to the internet –
- Smart speakers, smart TVs, and streaming devices
- Smart doorbells, baby monitors, and security cameras
- Cellular tablets, smartphones, and game consoles
- Wearable fitness trackers (including smart watches)
- Smart domestic appliances (such as light bulbs, plugs, kettles, thermostats, ovens, fridges, cleaners, and washing machines)
Companies that fail to adhere to the provisions of the PSTI act are liable to face recalls and monetary penalties, attracting fines of up to £10 million ($12.5 million) or 4% of their global annual revenues, depending on whichever is higher.
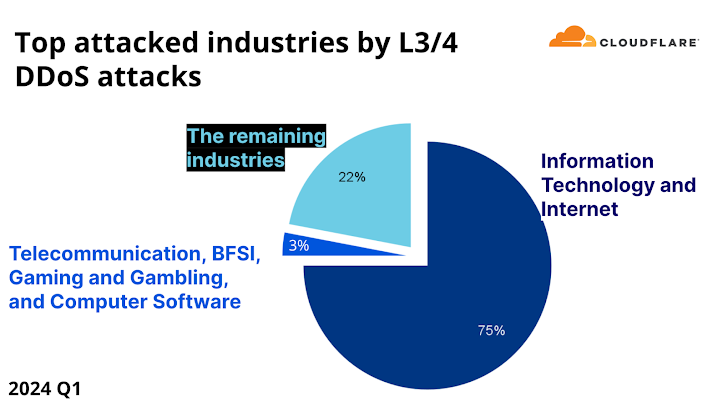
The development makes the U.K. the first country in the world to outlaw default usernames and passwords from IoT devices. According to Cloudflare’s DDoS threat report for Q1 2024, Mirai-based attacks continue to be prevalent despite the original botnet being taken down in 2016.
“Four out of every 100 HTTP DDoS attacks, and two out of every 100 L3/4 DDoS attacks are launched by a Mirai-variant botnet,” Omer Yoachimik and Jorge Pacheco said. “The Mirai source code was made public, and over the years there have been many permutations of the original.”
It also follows a $196 million fine issued by the U.S. Federal Communications Commission (FCC) against telecom carriers AT&T ($57 million), Sprint ($12 million), T-Mobile ($80 million), and Verizon ($47 million) for illegally sharing customers’ real-time location data without their consent to aggregators like LocationSmart and Zumigo, who then sold the information to third-party location-based service providers.
“No one who signed up for a cell plan thought they were giving permission for their phone company to sell a detailed record of their movements to anyone with a credit card,” U.S. Senator Ron Wyden, who revealed the practice in 2018, said in a statement.