Search results for "cybercriminals"
-

 4.0KMalware
4.0KMalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
The Microsoft Threat Intelligence team said it has observed a threat actor it tracks under the name Storm-1811 abusing the client management...
-

 3.9KMalware
3.9KMalwareCybercriminals Targeting Latin America with Sophisticated Phishing Scheme
A new phishing campaign has set its eyes on the Latin American region to deliver malicious payloads to Windows systems. “The phishing...
-
 509Malware
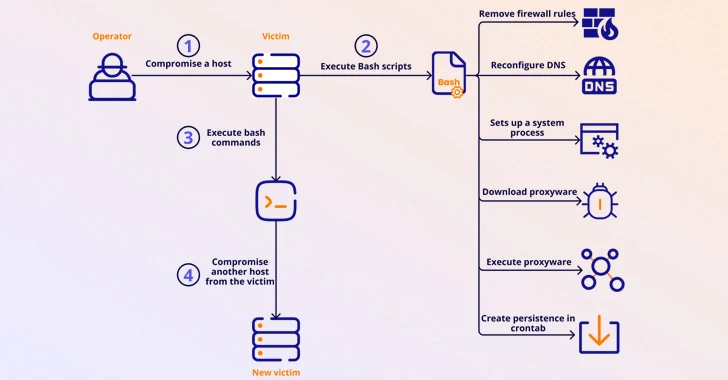
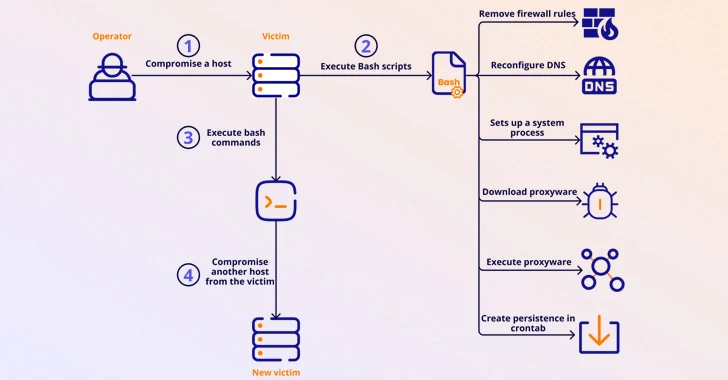
509MalwareMalicious Apps Caught Secretly Turning Android Phones into Proxies for Cybercriminals
Several malicious Android apps that turn mobile devices running the operating system into residential proxies (RESIPs) for other threat actors have been...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesAPIs Drive the Majority of Internet Traffic and Cybercriminals are Taking Advantage
Application programming interfaces (APIs) are the connective tissue behind digital modernization, helping applications and databases exchange data more effectively. The State of...
-
 2.6KData Breach
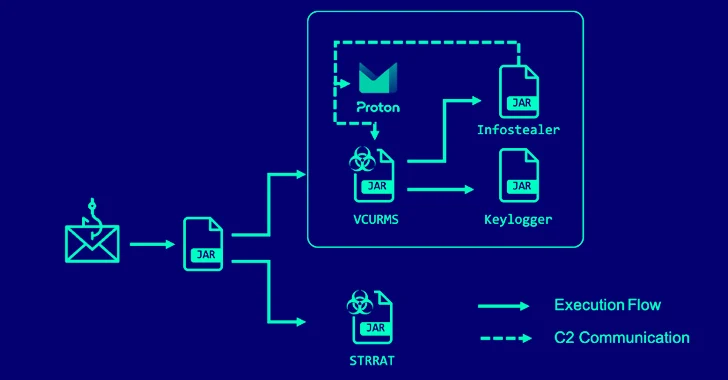
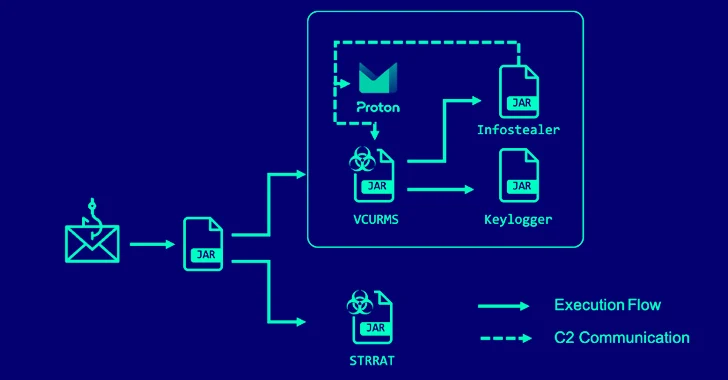
2.6KData BreachAlert: Cybercriminals Deploying VCURMS and STRRAT Trojans via AWS and GitHub
A new phishing campaign has been observed delivering remote access trojans (RAT) such as VCURMS and STRRAT by means of a malicious...
-
 2.2KData Breach
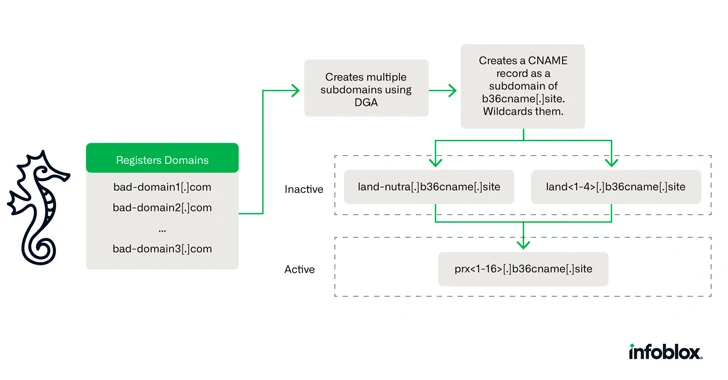
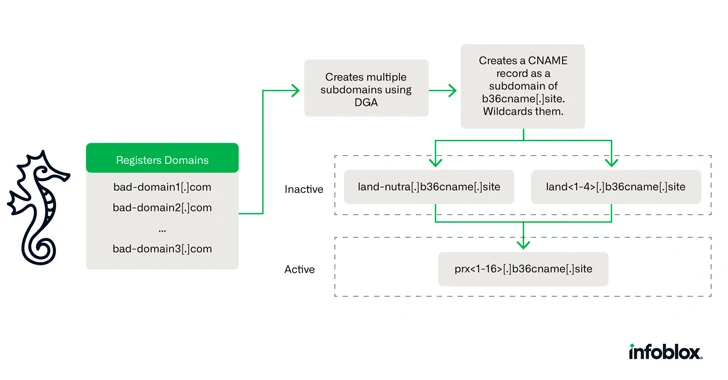
2.2KData BreachCybercriminals Using Novel DNS Hijacking Technique for Investment Scams
A new DNS threat actor dubbed Savvy Seahorse is leveraging sophisticated techniques to entice targets into fake investment platforms and steal funds....
-

 3.9KMalware
3.9KMalwareHow Cybercriminals are Exploiting India’s UPI for Money Laundering Operations
Cybercriminals are using a network of hired money mules in India using an Android-based application to orchestrate a massive money laundering scheme....
-

 802Malware
802MalwareCybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying...
-

 2.8KMalware
2.8KMalwareSyrian Hackers Distributing Stealthy C#-Based Silver RAT to Cybercriminals
Threat actors operating under the name Anonymous Arabic have released a remote access trojan (RAT) called Silver RAT that’s equipped to bypass...
-
 4.7KMalware
4.7KMalwareCybercriminals Using Telekopye Telegram Bot to Craft Phishing Scams on a Grand Scale
More details have emerged about a malicious Telegram bot called Telekopye that’s used by threat actors to pull off large-scale phishing scams....
-

 2.2KData Breach
2.2KData Breach34 Cybercriminals Arrested in Spain for Multi-Million Dollar Online Scams
Spanish law enforcement officials have announced the arrest of 34 members of a criminal group that carried out various online scams, netting...
-
 828Malware
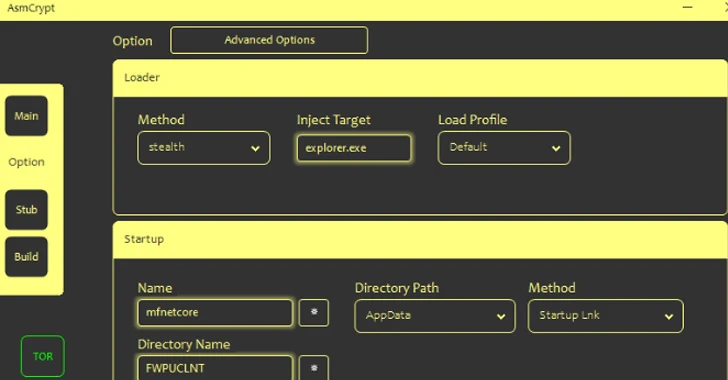
828MalwareCybercriminals Using New ASMCrypt Malware Loader to Fly Under the Radar
Threat actors are selling a new crypter and loader called ASMCrypt, which has been described as an “evolved version” of another loader...
-
 1.1KCyber Attack
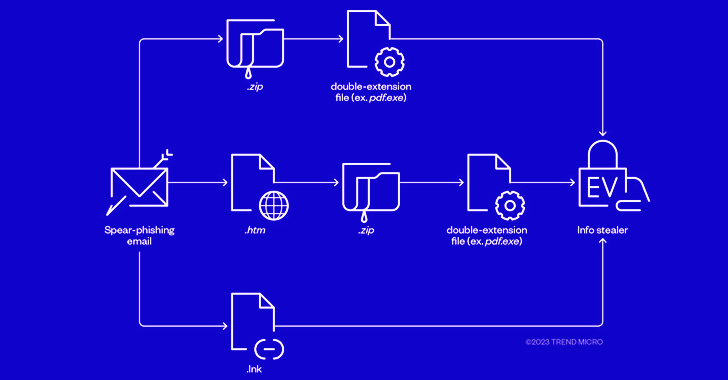
1.1KCyber AttackCybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads
The threat actors behind RedLine and Vidar information stealers have been observed pivoting to ransomware through phishing campaigns that spread initial payloads...
-

 5.0KMalware
5.0KMalwareCybercriminals Using PowerShell to Steal NTLMv2 Hashes from Compromised Windows
A new cyber attack campaign is leveraging the PowerShell script associated with a legitimate red teaming tool to plunder NTLMv2 hashes from...
-
 1.1KMalware
1.1KMalwareCybercriminals Weaponizing Legitimate Advanced Installer Tool in Crypto-Mining Attacks
A legitimate Windows tool used for creating software packages called Advanced Installer is being abused by threat actors to drop cryptocurrency-mining malware...
-
 1.6KMalware
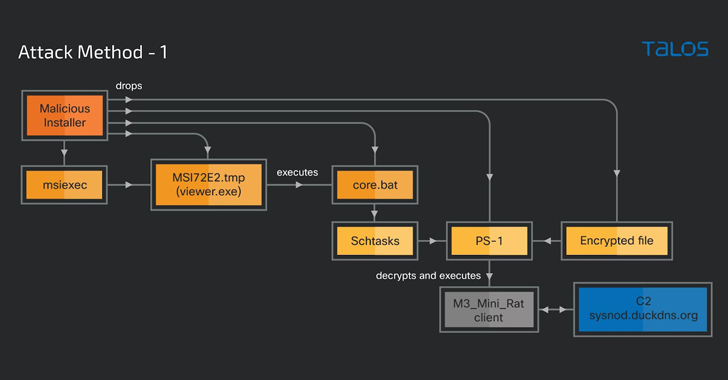
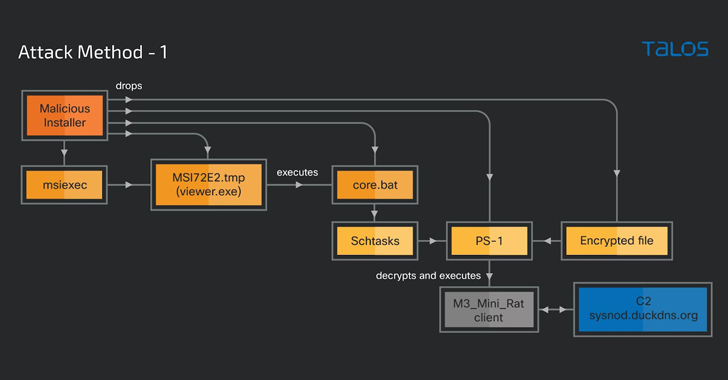
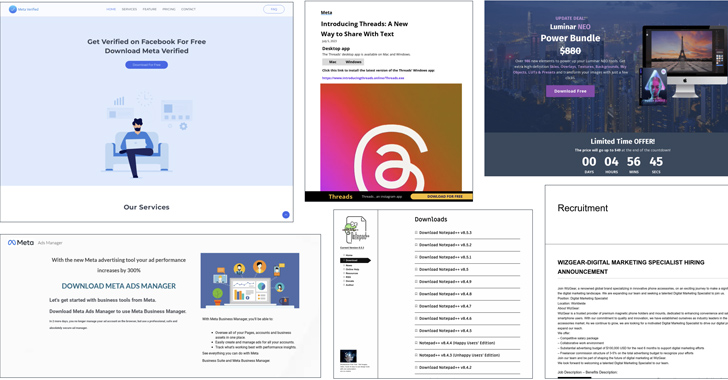
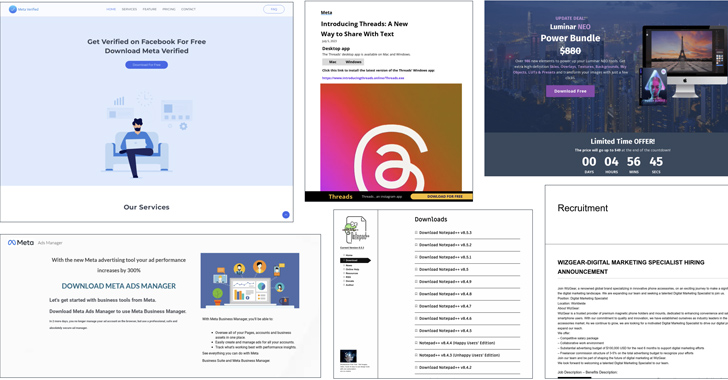
1.6KMalwareVietnamese Cybercriminals Targeting Facebook Business Accounts with Malvertising
Malicious actors associated with the Vietnamese cybercrime ecosystem are leveraging advertising-as-a-vector on social media platforms such as Meta-owned Facebook to distribute malware....
-
 810Cyber Attack
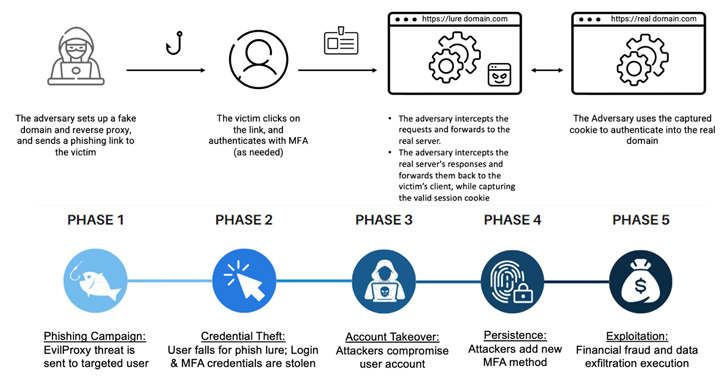
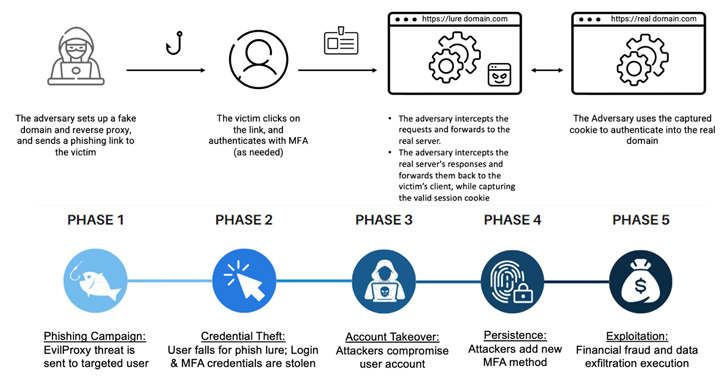
810Cyber AttackCybercriminals Increasingly Using EvilProxy Phishing Kit to Target Executives
Threat actors are increasingly using a phishing-as-a-service (PhaaS) toolkit dubbed EvilProxy to pull off account takeover attacks aimed at high-ranking executives at...
-

 4.9KMalware
4.9KMalwareIranian Company Cloudzy Accused of Aiding Cybercriminals and Nation-State Hackers
Services offered by an obscure Iranian company known as Cloudzy are being leveraged by multiple threat actors, including cybercrime groups and nation-state...
-

 3.7KMalware
3.7KMalwareCybercriminals Renting WikiLoader to Target Italian Organizations with Banking Trojan
Organizations in Italy are the target of a new phishing campaign that leverages a new strain of malware called WikiLoader with an...
-
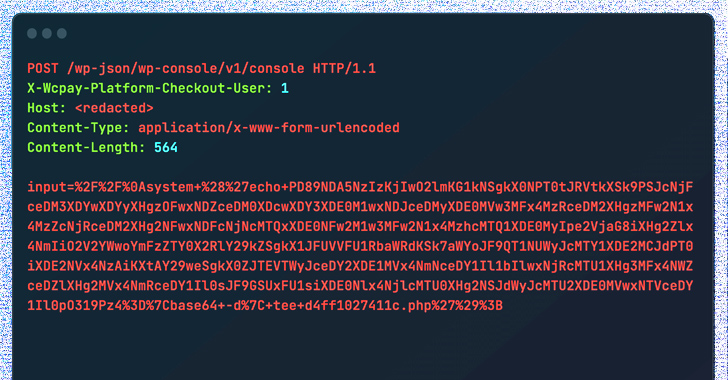
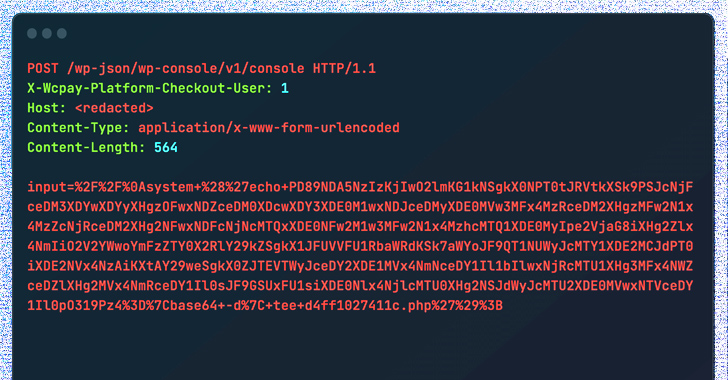 351Vulnerabilities
351VulnerabilitiesCybercriminals Exploiting WooCommerce Payments Plugin Flaw to Hijack Websites
Threat actors are actively exploiting a recently disclosed critical security flaw in the WooCommerce Payments WordPress plugin as part of a massive...
-
 4.5KMalware
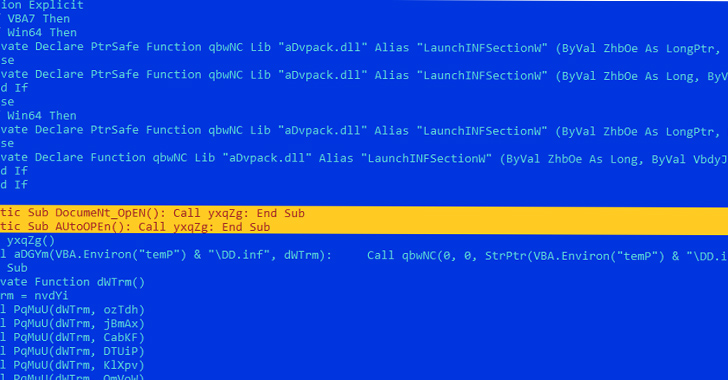
4.5KMalwareCybercriminals Exploit Microsoft Word Vulnerabilities to Deploy LokiBot Malware
Microsoft Word documents exploiting known remote code execution flaws are being used as phishing lures to drop malware called LokiBot on compromised...






