Search results for "hack"
-

 2.6KVulnerabilities
2.6KVulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
Cybersecurity researchers have discovered a new campaign that’s exploiting a recently disclosed security flaw in Fortinet FortiClient EMS devices to deliver ScreenConnect...
-

 2.8KMalware
2.8KMalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
The threat actor tracked as TA558 has been observed leveraging steganography as an obfuscation technique to deliver a wide range of malware...
-

 4.7KCyber Attack
4.7KCyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
Threat actors have been exploiting the newly disclosed zero-day flaw in Palo Alto Networks PAN-OS software dating back to March 26, 2024,...
-

 2.3KMalware
2.3KMalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
The Iranian threat actor known as MuddyWater has been attributed to a new command-and-control (C2) infrastructure called DarkBeatC2, becoming the latest such...
-

 3.3KVulnerabilities
3.3KVulnerabilitiesWebinar: Learn How to Stop Hackers from Exploiting Hidden Identity Weaknesses
We all know passwords and firewalls are important, but what about the invisible threats lurking beneath the surface of your systems? Identity...
-

 Vulnerabilities
VulnerabilitiesHow to hack a LG Smart TV via vulnerabilities in LG WebOS?
In a recent disclosure, cybersecurity firm Bitdefender has revealed a series of critical vulnerabilities within LG’s WebOS, the operating system used in...
-
 3.4KVulnerabilities
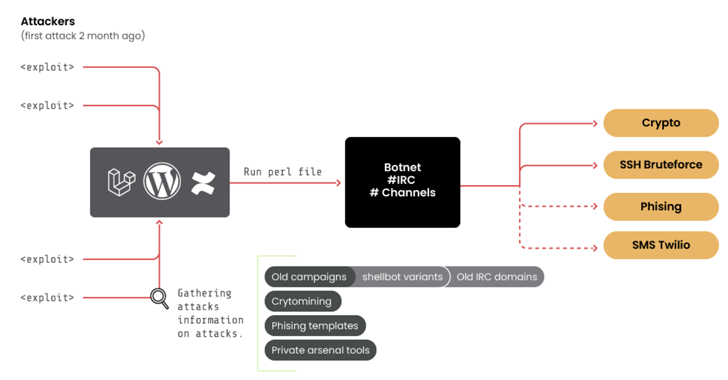
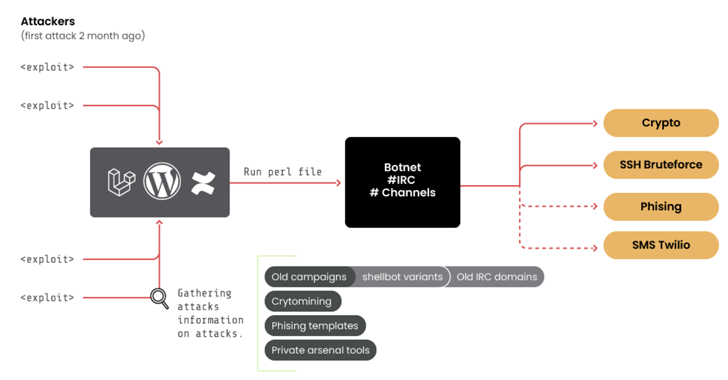
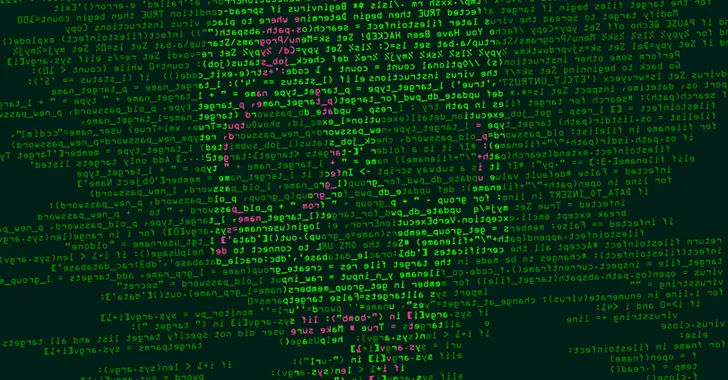
3.4KVulnerabilities10-Year-Old ‘RUBYCARP’ Romanian Hacker Group Surfaces with Botnet
A threat group of suspected Romanian origin called RUBYCARP has been observed maintaining a long-running botnet for carrying out crypto mining, distributed...
-

 3.7KMalware
3.7KMalwareHackers Targeting Human Rights Activists in Morocco and Western Sahara
Human rights activists in Morocco and the Western Sahara region are the targets of a new threat actor that leverages phishing attacks...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesHackers Exploit Magento Bug to Steal Payment Data from E-commerce Websites
Threat actors have been found exploiting a critical flaw in Magento to inject a persistent backdoor into e-commerce websites. The attack leverages...
-

 1.8KMalware
1.8KMalwareVietnam-Based Hackers Steal Financial Data Across Asia with Malware
A suspected Vietnamese-origin threat actor has been observed targeting victims in several Asian and Southeast Asian countries with malware designed to harvest...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesU.S. Cyber Safety Board Slams Microsoft Over Breach by China-Based Hackers
The U.S. Cyber Safety Review Board (CSRB) has criticized Microsoft for a series of security lapses that led to the breach of...
-
 4.2KMalware
4.2KMalwareChina-linked Hackers Deploy New ‘UNAPIMON’ Malware for Stealthy Operations
A threat activity cluster tracked as Earth Freybug has been observed using a new malware called UNAPIMON to fly under the radar....
-

 4.6KMalware
4.6KMalwareHackers Target macOS Users with Malicious Ads Spreading Stealer Malware
Malicious ads and bogus websites are acting as a conduit to deliver two different stealer malware, including Atomic Stealer, targeting Apple macOS...
-

 1.7KMalware
1.7KMalwareFinland Blames Chinese Hacking Group APT31 for Parliament Cyber Attack
The Police of Finland (aka Poliisi) has formally accused a Chinese nation-state actor tracked as APT31 for orchestrating a cyber attack targeting...
-

 4.0KMalware
4.0KMalwareHackers Hit Indian Defense, Energy Sectors with Malware Posing as Air Force Invite
Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of...
-

 4.2KData Breach
4.2KData BreachKey Lesson from Microsoft’s Password Spray Hack: Secure Every Account
In January 2024, Microsoft discovered they’d been the victim of a hack orchestrated by Russian-state hackers Midnight Blizzard (sometimes known as Nobelium)....
-

 4.9KMalware
4.9KMalwareRussian Hackers May Have Targeted Ukrainian Telecoms with Upgraded ‘AcidPour’ Malware
The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne...
-

 3.6KData Security
3.6KData SecurityHack-Proof Your Cloud: The Step-by-Step Continuous Threat Exposure Management CTEM Strategy for AWS & AZURE
Continuous Threat Exposure Management (CTEM) is an evolving cybersecurity practice focused on identifying, assessing, prioritizing, and addressing security weaknesses and vulnerabilities in...
-
 4.1KMalware
4.1KMalwareHackers Using Sneaky HTML Smuggling to Deliver Malware via Fake Google Sites
Cybersecurity researchers have discovered a new malware campaign that leverages bogus Google Sites pages and HTML smuggling to distribute a commercial malware...
-
 432Malware
432MalwareAPT28 Hacker Group Targeting Europe, Americas, Asia in Widespread Phishing Scheme
The Russia-linked threat actor known as APT28 has been linked to multiple ongoing phishing campaigns that employ lure documents imitating government and...
-
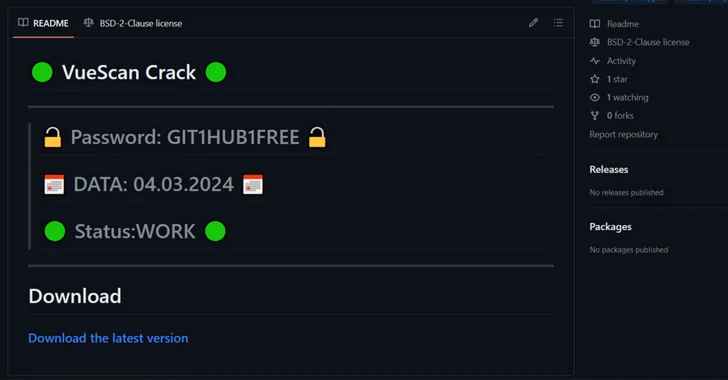
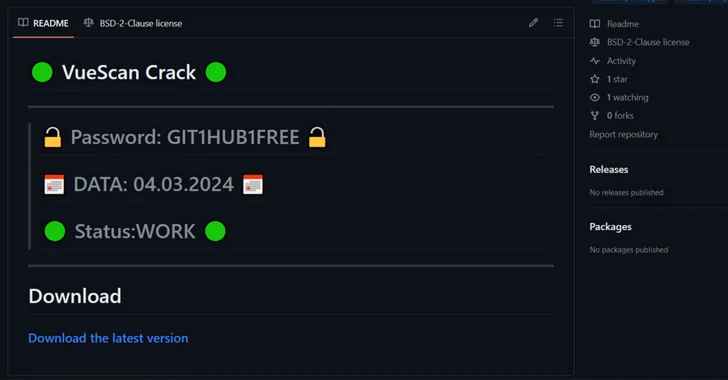 2.1KMalware
2.1KMalwareHackers Using Cracked Software on GitHub to Spread RisePro Info Stealer
Cybersecurity researchers have found a number of GitHub repositories offering cracked software that are used to deliver an information stealer called RisePro....




