Search results for "uber"
-
 1.3KData Security
1.3KData SecurityCVE-2023-5528: Kubernetes Flaw Jeopardizing Windows Node That Can’t Be Ignored
In recent developments, cybersecurity experts have raised alarms over a high-severity vulnerability identified in Kubernetes, marked as CVE-2023-5528. This critical flaw has...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesResearchers Detail Kubernetes Vulnerability That Enables Windows Node Takeover
Details have been made public about a now-patched high-severity flaw in Kubernetes that could allow a malicious attacker to achieve remote code...
-
 4.3KMalware
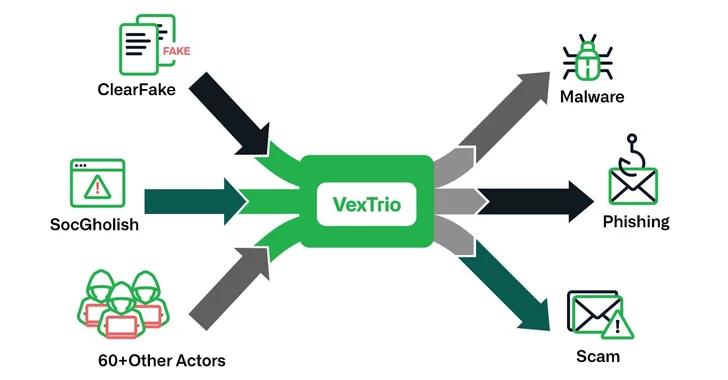
4.3KMalwareVexTrio: The Uber of Cybercrime – Brokering Malware for 60+ Affiliates
The threat actors behind ClearFake, SocGholish, and dozens of other actors have established partnerships with another entity known as VexTrio as part...
-

 2.1KData Security
2.1KData SecurityHow to hack Google Kubernetes Engine (GKE)? Securing against GKE threats
A recent investigation by Unit 42 of Palo Alto Networks has uncovered a dual privilege escalation chain in Google Kubernetes Engine (GKE)....
-

 3.2KVulnerabilities
3.2KVulnerabilitiesGoogle Cloud Resolves Privilege Escalation Flaw Impacting Kubernetes Service
Google Cloud has addressed a medium-severity security flaw in its platform that could be abused by an attacker who already has access...
-

 302Tutorials
302TutorialsIs Your etcd an Open Door for Cyber Attacks? How to Secure Your Kubernetes Clusters & Nodes
Kubernetes has become the de facto orchestration platform for managing containerized applications, but with its widespread adoption, the security of Kubernetes clusters...
-

 631Vulnerabilities
631VulnerabilitiesHow to hack Kubernetes pods and executing malicious code remotely
According to the findings of Akamai’s security experts, a high-severity vulnerability in Kubernetes may be exploited to accomplish remote code execution (RCE)...
-
 5.4KTutorials
5.4KTutorialsRBAC Buster – A new K8s attack technique to hack in Kubernetes cluster
The first known proof that attackers are using Kubernetes (K8s) Role-Based Access Control (RBAC) in the field to construct backdoors was found...
-

 1.8KCyber Attack
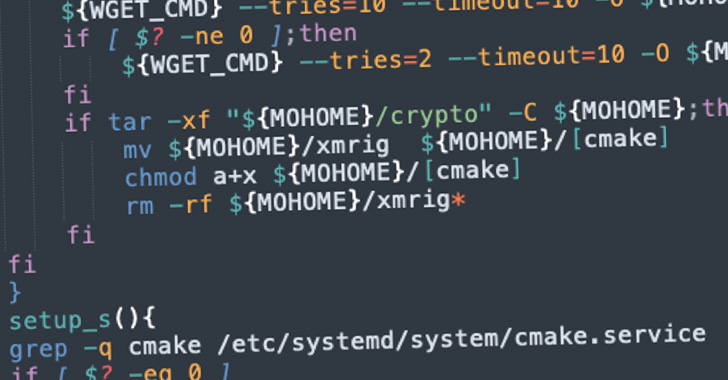
1.8KCyber AttackKubernetes RBAC Exploited in Large-Scale Campaign for Cryptocurrency Mining
A large-scale attack campaign discovered in the wild has been exploiting Kubernetes (K8s) Role-Based Access Control (RBAC) to create backdoors and run...
-

 5.0KIncidents
5.0KIncidentsUber gave sensitive driver data to a law firm for legal actions, but the law firm leaked all the data
An unknown number of Uber drivers have been informed by a legal firm that represents Uber Technologies that sensitive data, including their...
-

 1.7KData Breach
1.7KData BreachUber Driver Data Stolen Again From the Servers of Law Firm
Uber faces various cyber attacks that result in the disclosure of employee email addresses, company reports, and information related to IT assets....
-
 1.8KData Security
1.8KData SecurityNew cryptojacking malware can hack in Kubernetes clusters using this easy trick
Dero is a relatively new cryptocurrency that places a strong emphasis on privacy. It utilizes directed acyclic graph (DAG) technology, which allows...
-

 3.7KVulnerabilities
3.7KVulnerabilities2 Critical vulnerabilities in Argo CD allow complete take over of your Kubernetes
Argo CD is a Kubernetes-based declarative GitOps continuous delivery platform. It is built as a Kubernetes controller that constantly monitors running apps...
-

 2.5KInfosec
2.5KInfosecSecuring Kubernetes Deployments on AWS – Guide
Kubernetes Deployment on AWS Kubernetes is open-source software for deploying and managing containerized applications at scale. Kubernetes can manage clusters on Amazon...
-
 460Tutorials
460TutorialsTop 8 Free Tools for security testing and audit of your Kubernetes cluster in 2022
Docker is a technology for containerization, while Kubernetes is a tool for orchestrating container deployments. In the subsequent subsections, we will discuss...
-
 907Malware
907MalwareNew Cryptojacking Campaign Targeting Vulnerable Docker and Kubernetes Instances
A new cryptojacking campaign has been uncovered targeting vulnerable Docker and Kubernetes infrastructures as part of opportunistic attacks designed to illicitly mine...
-
 2.3KData Breach
2.3KData BreachFormer Uber Security Chief Found Guilty of Data Breach Coverup
A U.S. federal court jury has found former Uber Chief Security Officer Joseph Sullivan guilty of not disclosing a 2016 breach of...
-

 4.5KData Breach
4.5KData BreachLondon Police Arrested 17-Year-Old Hacker Suspected of Uber and GTA 6 Breaches
The City of London Police on Friday revealed that it has arrested a 17-year-old teenager from Oxfordshire on suspicion of hacking. “On...
-

 393Data Breach
393Data BreachUber Claims No Sensitive Data Exposed in Latest Breach… But There’s More to This
Uber, in an update, said there is “no evidence” that users’ private information was compromised in a breach of its internal computer...
-

 305Data Breach
305Data BreachUber Hacked – Attackers Breached Critical IT Systems & Windows Domain
Uber’s computer network has been hacked on Thursday, leading the company to take some of its internal communications and engineering systems offline. ...
-

 4.6KData Breach
4.6KData BreachUber Hacked – Attackers Breached Critical IT Systems & Windows Domain
Uber’s computer network has been hacked on Thursday, leading the company to take some of its internal communications and engineering systems offline. ...






