Geek News
Popular Posts
-
 5.2KCyber Attack
5.2KCyber AttackU.S. Sanctions 6 Iranian Officials for Critical Infrastructure Cyber Attacks
The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) announced sanctions against six...
-
 5.1KVulnerabilities
5.1KVulnerabilitiesNew Findings Challenge Attribution in Denmark’s Energy Sector Cyberattacks
The cyber attacks targeting the energy sector in Denmark last year may not have...
-
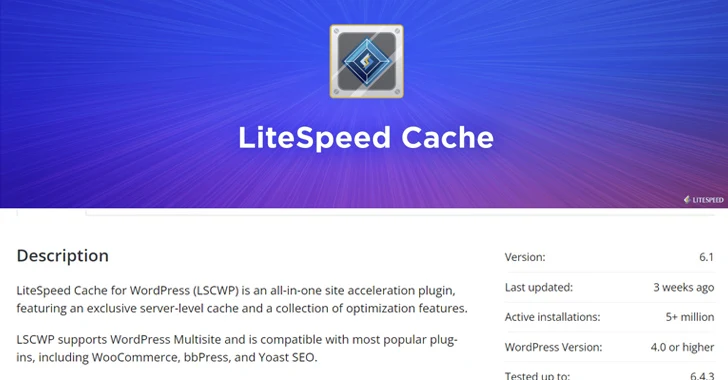
 5.1KVulnerabilities
5.1KVulnerabilitiesWordPress LiteSpeed Plugin Vulnerability Puts 5 Million Sites at Risk
A security vulnerability has been disclosed in the LiteSpeed Cache plugin for WordPress that...
-

 5.0KCyber Attack
5.0KCyber AttackAfter FBI Takedown, KV-Botnet Operators Shift Tactics in Attempt to Bounce Back
The threat actors behind the KV-botnet made “behavioral changes” to the malicious network as...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesMalicious Code in XZ Utils for Linux Systems Enables Remote Code Execution
The malicious code inserted into the open-source library XZ Utils, a widely used package...
-

 2.0KData Breach
2.0KData BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
Users of the CrushFTP enterprise file transfer software are being urged to update to the latest version following the discovery of a...
-

 2.1KData Breach
2.1KData BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
A new Android trojan called SoumniBot has been detected in the wild targeting users in South Korea by leveraging weaknesses in the...
-

 887Malware
887MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
A previously undocumented “flexible” backdoor called Kapeka has been “sporadically” observed in cyber attacks targeting Eastern Europe, including Estonia and Ukraine, since...
-

 1.5KVulnerabilities
1.5KVulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
Threat actors are exploiting unpatched Atlassian servers to deploy a Linux variant of Cerber (aka C3RB3R) ransomware. The attacks leverage CVE-2023-22518 (CVSS...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
Cybersecurity researchers have discovered a new campaign that’s exploiting a recently disclosed security flaw in Fortinet FortiClient EMS devices to deliver ScreenConnect...
-

 3.8KVulnerabilities
3.8KVulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
CVE-2024-31497 has emerged as a critical security flaw affecting PuTTY, a widely used SSH and Telnet client, from versions 0.68 through 0.80,...
-

 2.8KMalware
2.8KMalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
The threat actor tracked as TA558 has been observed leveraging steganography as an obfuscation technique to deliver a wide range of malware...
-

 1.7KVulnerabilities
1.7KVulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
New cybersecurity research has found that command-line interface (CLI) tools from Amazon Web Services (AWS) and Google Cloud can expose sensitive credentials...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
The maintainers of the PuTTY Secure Shell (SSH) and Telnet client are alerting users of a critical vulnerability impacting versions from 0.68...
-

 1.2KData Breach
1.2KData BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
The U.S. Federal Trade Commission (FTC) has ordered mental telehealth company Cerebral from using or disclosing personal medical data for advertising purposes....
-

 703Malware
703MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
Two individuals have been arrested in Australia and the U.S. in connection with an alleged scheme to develop and distribute a remote...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
A security flaw impacting the Lighttpd web server used in baseboard management controllers (BMCs) has remained unpatched by device vendors like Intel...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
Imagine a world where the software that powers your favorite apps, secures your online transactions, and keeps your digital life could be...
-

 1.4KData Breach
1.4KData BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
The threat actor known as Muddled Libra has been observed actively targeting software-as-a-service (SaaS) applications and cloud service provider (CSP) environments in...
-

 561Data Breach
561Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
To minimize the risk of privilege misuse, a trend in the privileged access management (PAM) solution market involves implementing just-in-time (JIT) privileged...
-

 820Malware
820MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
Cybersecurity researchers have discovered a “renewed” cyber espionage campaign targeting users in South Asia with the aim of delivering an Apple iOS...
-

 1.8KVulnerabilities
1.8KVulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
Palo Alto Networks has released hotfixes to address a maximum-severity security flaw impacting PAN-OS software that has come under active exploitation in...
-

 2.9KCyber Attack
2.9KCyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) on Friday announced sanctions against an official associated with Hamas for his...
-

 4.7KCyber Attack
4.7KCyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
Threat actors have been exploiting the newly disclosed zero-day flaw in Palo Alto Networks PAN-OS software dating back to March 26, 2024,...
-

 3.9KMalware
3.9KMalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
“Test files” associated with the XZ Utils backdoor have made their way to a Rust crate known as liblzma-sys, new findings from...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files