Posts By root
-

 169Incidents
169IncidentsToyota Corolla Hybrid Car Hacked via Smartphone
Researcher also launches a DoS attack on the car’s computer. A professor at Hiroshima City University was able to hack an Internet-connected car...
-

 219Data Security
219Data SecurityTokyo Uses Drone Equipped With Giant Net To Catch Illegally-Flying Drones
The Tokyo Metropolitan Police Department has taken maintaining law and order to another level: it uses a massive drone to catch other...
-

 259Hacked
259Hacked4 Teenage Hackers Trace ISIS Twitter Accounts To The UK Government
Image | fossBytes Short Bytes: A group of teenage hackers has traced multiple ISIS Twitter accounts to the UK Government’s Department of...
-

 93Data Security
93Data SecurityMan arrested in toymaker hack that exposed data for millions of kids
VTech site remained vulnerable to an old SQL injection exploit. UK police said they have arrested a 21-year-old man in connection to...
-
 185Incidents
185IncidentsHacker Lexicon: Botnets, the Zombie Computer Armies That Earn Hackers Millions
ZOMBIE ARMIES AREN’T just invading movie screens these days. They’re also taking over the Internet in the form of massive botnets. A...
-

 476Data Security
476Data SecurityHow to implement enterprise data protection services and solutions ?
There is an increase in people who have been victims of identity theft and unauthorized use of credit cards because of many...
-

 323Geek
323GeekFake Microsoft Helpdesk Calls Aim To Install Malware on PC
Scammers have been targeting Microsoft customers since the very first day — The only change in their tactic is that it’s getting...
-

 322Geek
322GeekUK Government Department Links Back To ISIS Twitter Handles
Nowadays, every individual who uses the internet is well aware of IP and MAC addresses but for those who don’t, MAC address...
-

 264News
264News11 Ongoing Anonymous Operations You Must Know About
Anonymous is known for conducting cyber attacks against injustice but not every operation makes it to the news — There are several...
-

 180Cyber Crime
180Cyber CrimeEuropol makes 12 arrests in Remote Access Trojan crackdown
Europol have been working alongside a number of European law enforcement authorities in an attempt to crackdown against the use of Remote...
-

 347News
347NewsMacKeeper Hacked: Researcher Finds 13 Million Credentials Online
ShortRead: MacKeeper, a utility software suite for Mac OS X faced a data breach which has exposed details in relation to its...
-
 264Hacked
264HackedGCHQ Open Sources Its Spy Software – So, Am I Going To Hate Them Less?
Image | GCHQ Short Bytes: NSA’s British counterpart GCHQ has just open sourced its spying tool named Gaffer. The software is written...
-

 214Data Security
214Data SecurityThis New Secom Drone Will Hunt The Suspects Down
Japanese company “Secom” has developed a drone that could be tough to handle for intruders trying to escape after committing any crime....
-
 264Hacked
264HackedAnonymous Hacker Tells How She Attacks ISIS In The Recent Video
Image | fossBytes Short Bytes: A hacker from Anonymous collective has come forward to explain how Anonymous locates ISIS-affiliated Twitter handles and...
-
 116Data Security
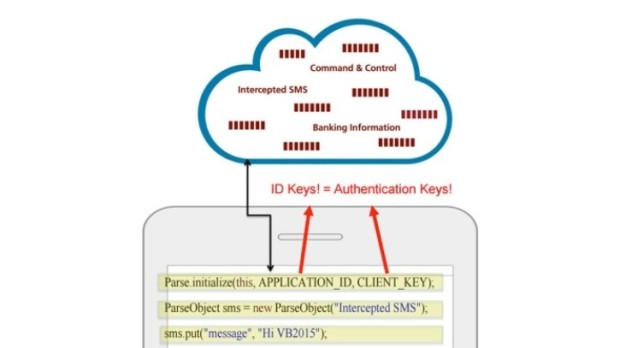
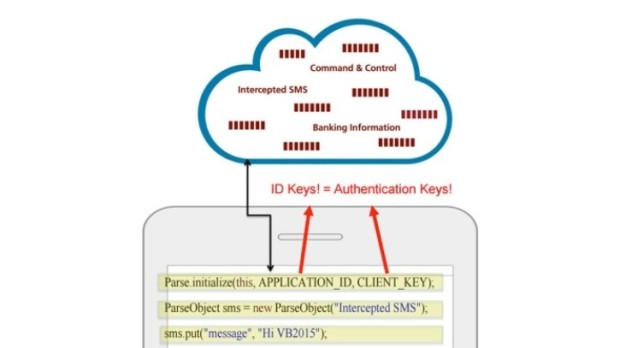
116Data SecurityTwo Mobile Banking Trojans Used Facebook Parse as C&C Server
Attackers carry out SMS fraud via the infected phones. The Android/OpFake and the Android/Marry malware families, two banking trojans targeting mobile devices, have...
-
 97Incidents
97IncidentsMacKeeper Exposed Details for 13 Million Users
Leaky database server left exposed online is at fault.For the past few weeks, security researcher Chris Vickery has been working on discovering...
-
 191Hacked
191HackedMacro Malware Is Back From The Dead, Here’s How To Defeat It
Short Bytes: The notorious macro malware from the 1990s is making a comeback in a big manner. The latest security reports suggest...
-

 195Data Security
195Data SecurityWhat the government should’ve learned about backdoors from the Clipper Chip
The Obama administration’s calls for backdoors echo the Clinton-era key escrow fiasco. In the face of a Federal Bureau of Investigation proposal...
-

 172Malware
172MalwareRAT trap: Norway police nab five in remote-access Trojan Europol swoop
Today’s arrests are part of a co-ordinated Europol initiative to crack down on all levels of computer crime. Norway’s Kripos national criminal...
-

 225Vulnerabilities
225VulnerabilitiesHackers actively exploit critical vulnerability in sites running Joomla
Wave of attacks grows. Researchers advise sites to install just-released patch. Attackers are actively exploiting a critical remote command-execution vulnerability that has...
-

 241Geek
241GeekResearchers Found Critical Vulnerabilities in Android Parking Apps
A new research has found out that numerous parking applications available in the smartphone market contain strong vulnerabilities that can allow hackers...






