Cryptocurrency
-

 291
291World’s Fourth Largest Cryptocurrency “Bithumb” Hacked and Many Number of User Accounts Compromised
Worlds Fourth Largest Cryptocurrency called “Bithumb ” hacked by unknown hackers and stolen around 31,800 Bithumb users account details which are 3%...
-
 181
181AES-256 keys can be sniffed within Seconds Using €200 Worth Hardware kit
Side-channel attacks over AES is not new, previous attacks required a direct access. Now the security experts from Fox-IT and Riscure show how...
-

 320
320Biggest Bitcoin Wallet Hack in History, Around US$5 Million Worth Bitcoin Currency Stolen
Four Bitcoin Hot-Wallets of South Koren Bitcoin exchange Firm Yapizon Hacked and Stolen Around “3816.2028 Bitcoin” ( Nearly 5 Million USD) and...
-

 205
205Confide App used by White House staffers Found Vulnerable for MITM attacks
Confide is an a encrypted texting application for Android and iOS, which used by staffers in White House for their secret communication. Security...
-
 281
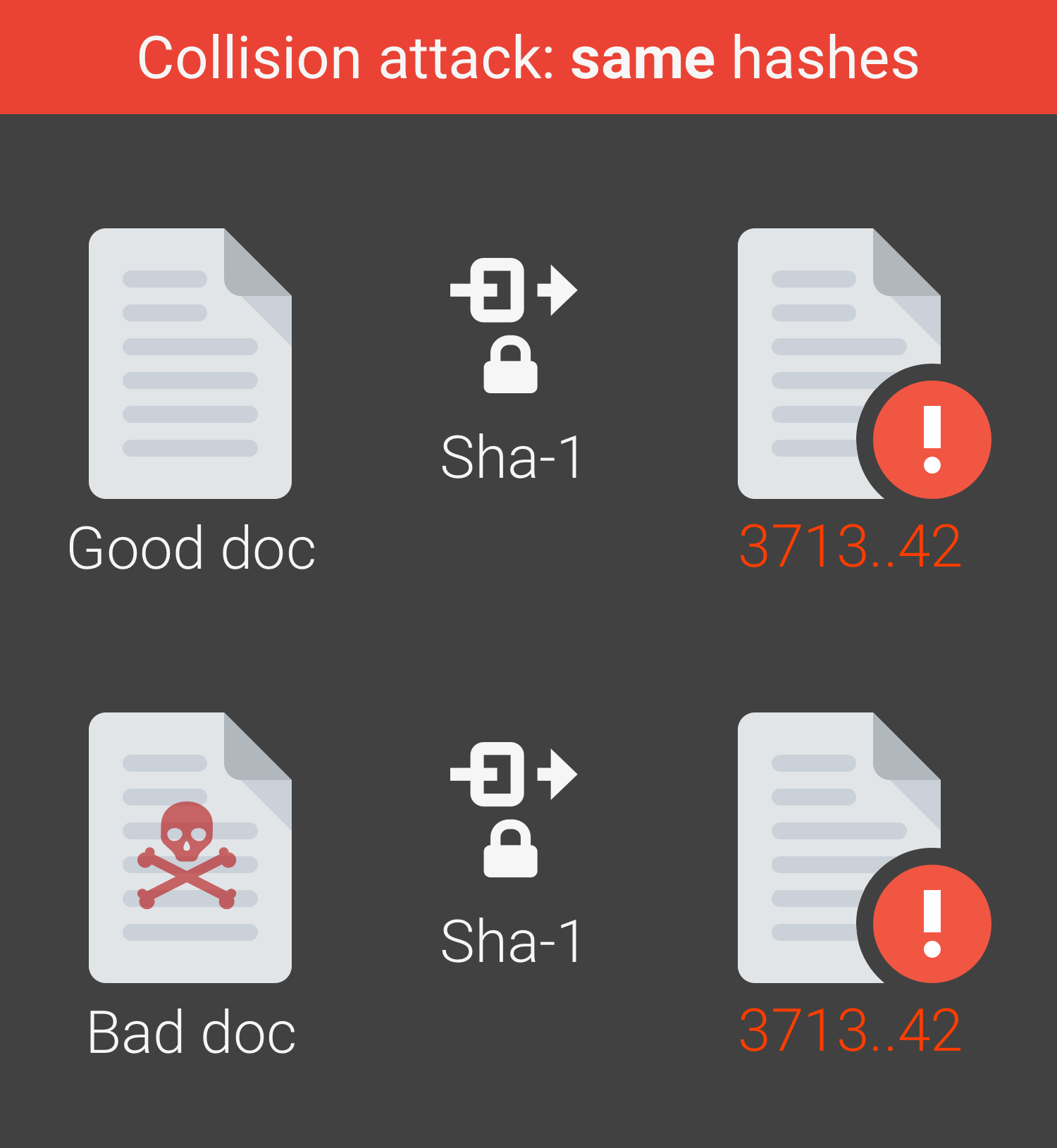
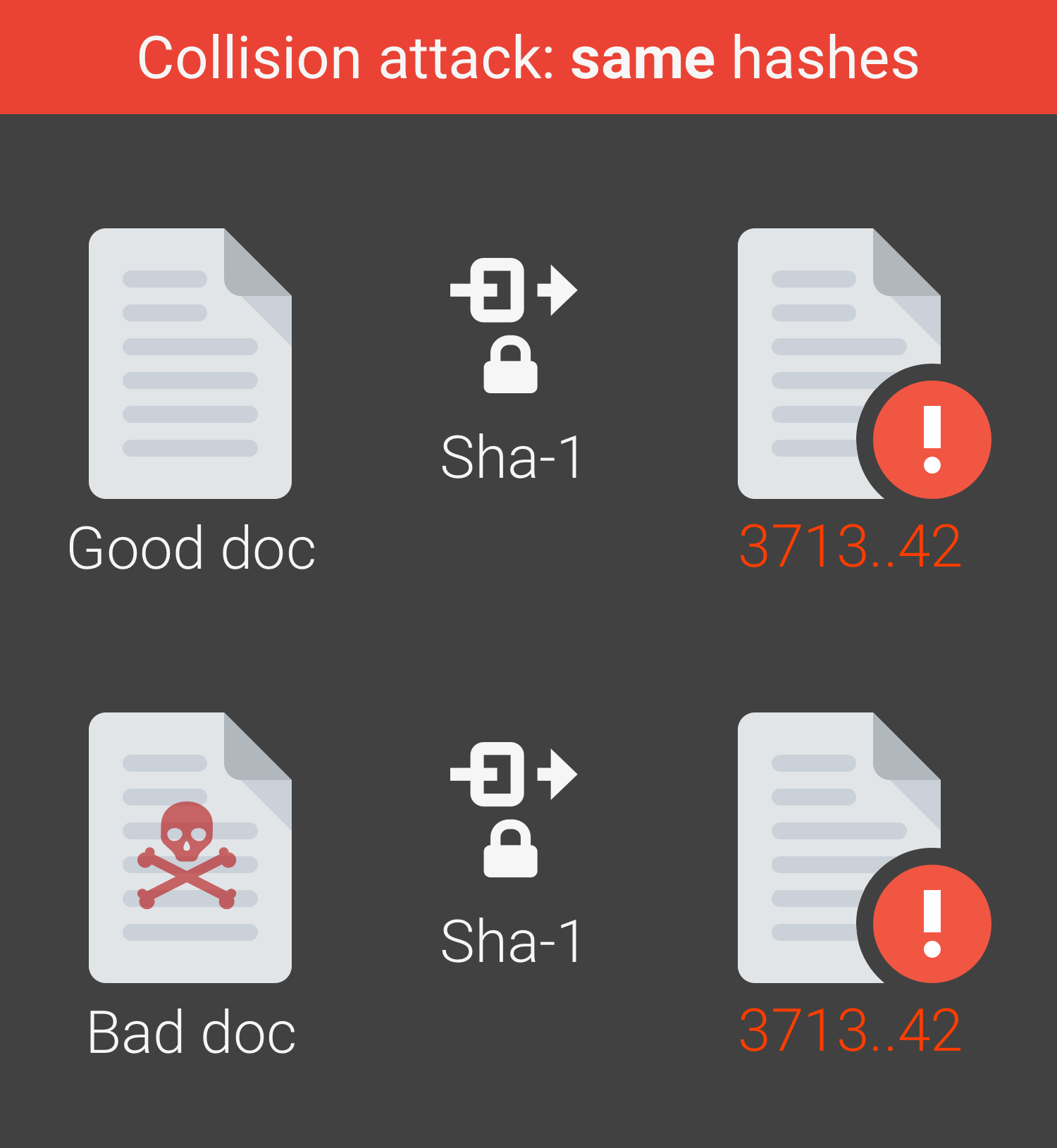
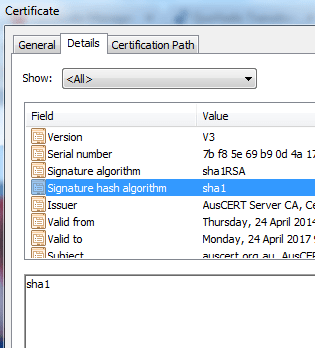
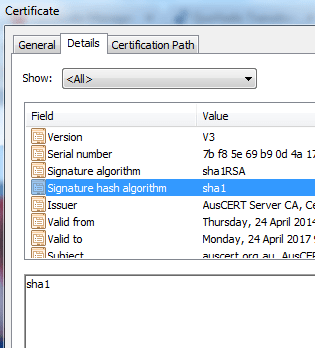
281Google Declares First-Ever SHA-1 attack
The use of SHA-1 certificates has been depreciated due to the ever-present necessity to strengthen procedures and strategies against a background of...
-

 289
289Project Wycheproof – Test crypto libraries against known attacks
Google announced Project Wycheproof – Test crypto libraries against known attacks, it is created and kept up by individuals from Google Security Team,...
-

 118
118Cerber 5.0.1 ransomware spreading via Google and Tor
What is cerber? Cerber is a ransomware-type malware that infiltrates the system and encrypts various file types including .jpg, .doc, .raw, .avi,...
-
 252
252Ransomware attack hit San Francisco train system
A ransomware attack took ticket machines for San Francisco’s light rail transit system offline all day Saturday during one of the busiest...
-

 132
132ImageGate attack – Malware through poisoned .JPG
ImageGate attack : Security people from Check Point Software Technologies identified a new malware campaign through Facebook. Crooks leverage an image obfuscation trick, dubbed...
-
 208
208Final countdown for SHA-1 SSL certificates
SHA-1 SSL certificates which are more popular and an sucessor of MD5 algorithm are now in the final days of what was once...
-
 560
560Dos attack with openssl CVE-2016-6304,CVE-2016-6305,CVE-2016-6306
What is Openssl? OpenSSL is a an open source project that provides a robust, commercial-grade, and full-featured toolkit for the Transport Layer...






