Cyber Attack
-

 298
298Security Researchers Reveal Cyber Espionage Attacks By Copykittens Hackers
Security researchers have discovered a new and massive cyber espionage campaign by copykittens hackers, especially aimed at people working in government organizations,...
-

 271
271A Hacker Stole Millions From Veritaseum (Ethereum platform)
Veritaseum Ethereum platform confirmed today that a hacker was able to steal millions of $ 8.4 from the ICO Ethereum (Coin Initial...
-
 227
227New LeakerLocker Ransomware Send Your Internet History & Pics to All Your Friends
After episodes of WannaCry and Petya ransomware, a new LeakerLocker ransomware (but creative) is spreading through special applications from the Google Play...
-

 324
324Reliance Jio Sim Data Breach Customer’s Data Allegedly Hacked
Reliance Jio Sim Data Breach, Personal data of about 120 million customers were reported exposed on the Internet probably the largest personal...
-

 176
176Millions Of Android Devices Infected By CopyCat Malware Around The World
A new malware called CopyCat malware hit more than 14 million Android devices around the world, rooting phones and kidnapping applications to...
-

 273
273Over $1 Million Worth Bitcoin and Ether Stolen !! World’s Largest Cryptocurrency Hack
One of the biggest exchanges and cryptocurrencies Ether Bitcoin worlds, Bithumb has recently been violated, resulting in a loss of Over $1...
-

 388
388SQL Injection Vulnerability Found In WordPress Plugin Used By 300,000+ Sites
SQL Injection Vulnerability Found in WordPress plugin, WP Statistics is one of the most popular WordPress plugins installed on 300,000 websites. The...
-
 280
280Linux PC Can Be Hacked Remotely With Malicious DNS Response
A critical loophole has been discovered in SystemD, the popular first character system and service manager for Linux operating systems, which can...
-
 205
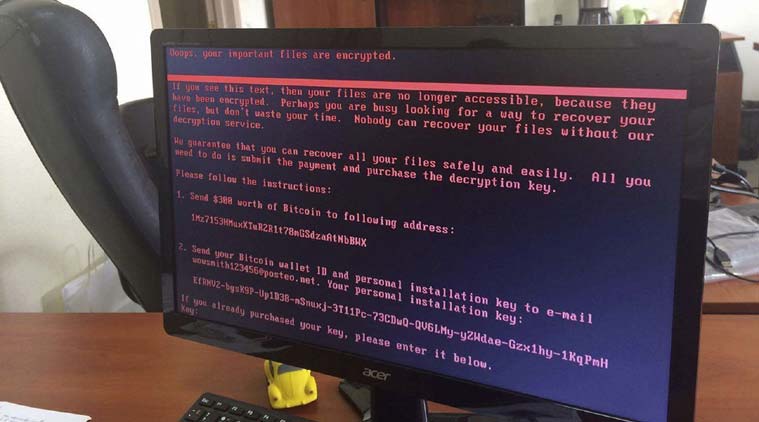
205Petya Ransomware Is Actually A Malware, You Won’t Get Your Files Back
Is Petya ransomware defective or too smart? Petya Ransomware is a nasty piece of malware that, unlike other traditional ransomware, does not...
-
 189
189Just Like Wannacry, Petya Ransomware Is Spreading Worldwide
In the new ransom attack (Petya Ransomware) is currently attacking a large number of countries all over the world, including Ukraine, the...
-

 254
254UK Parliament Hit by Cyberattack Hackers attempted to access MP emails
UK Parliament Hit by Cyberattack Hackers attempted to access MP emails, gentlemen and staff and security services are to stop access for anyone...
-
 223
223Data of 200 Million Voters Compromised On Unsecured Server
Information Has exposed Data of 200 Million Voters Compromised On Unsecured Server and more than 60% of the US population to what...
-

 215
215DeltaCharlie – A North Korean DDoS Botnet Malware Warned By US
The US government issued a warning about a rare piracy operation going on in North Korea last eight years. He presented the...
-

 160
160Beware!Hundreds Of Google Play Store Apps Affected By Xavier Malware
Over 800 different Android apps downloaded millions of times from the Google Play store, which was infected with a malicious ad library...
-

 179
179Warning! Hackers Are Now Using ‘SambaCry Vulnerability’ To Hack Linux
SambaCry uses weaknesses in Samba’s facilities to make Linux machine concessions and use them as victims in the process of extracting decoded...
-

 174
174A New Social Media Attack Called “DoubleSwitch” Is Being Used By Hackers
Security researchers have discovered a new intelligent way (DoubleSwitch) currently used by attackers to take over Twitter accounts verified and rename famous...
-

 186
186Android Rooting Malware With Code Injection Ability Found On Play Store
A new Roaring Android rooting malware has been detected with the ability to disable device security settings in an attempt to perform...
-
 179
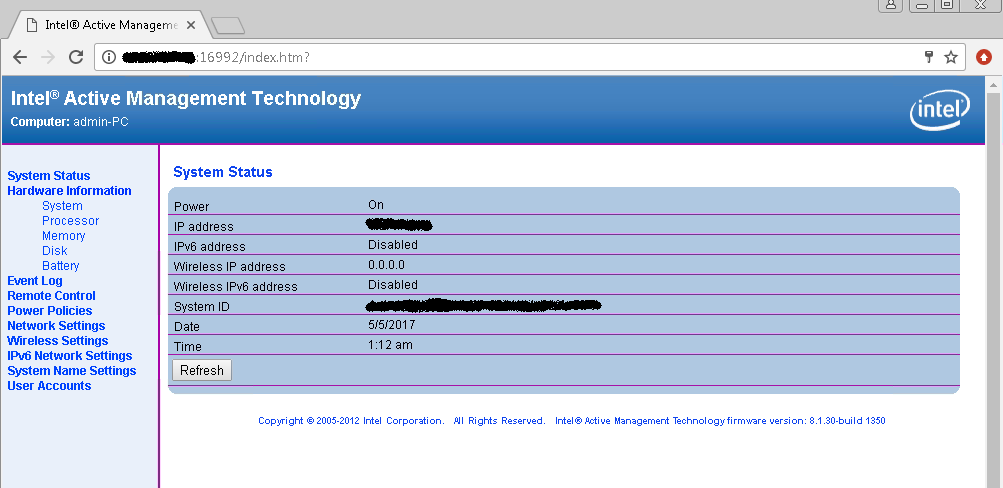
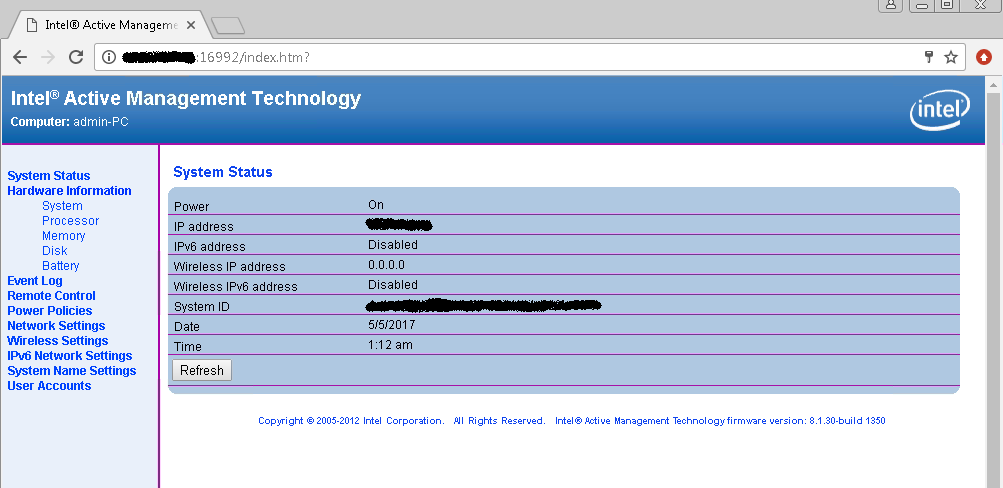
179A Malware Is Using Inbuilt Intel’s Amt Vulnerability To Steal Data
Intel AMT Vulnerability SOL detected hidden network interface This is the result of the Intel AMT Vulnerability SOL component of Intel ME...
-
 185
185QakBot Virus Locked Out Various of Active Directory Users
IBM security researchers Qakbot Virus many Active Directory domains, the user can block his business found. Active Directory is a directory developed...
-
 249
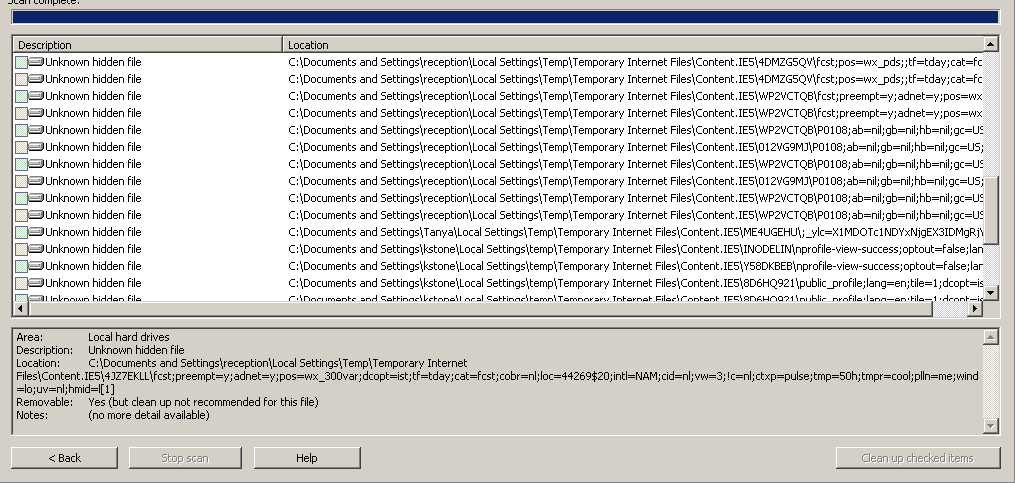
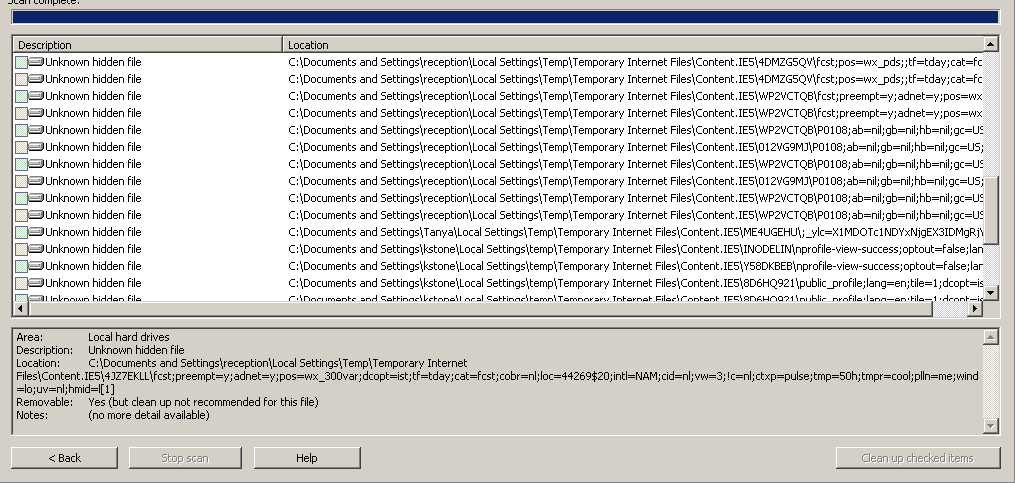
249CIA’s New Software can turn your Windows PC into Trojan Horse in your Network
“Pandemic”, as the implant is coded, to install malicious file server software in the secret of the CIA by the carrier, according...
-
 285
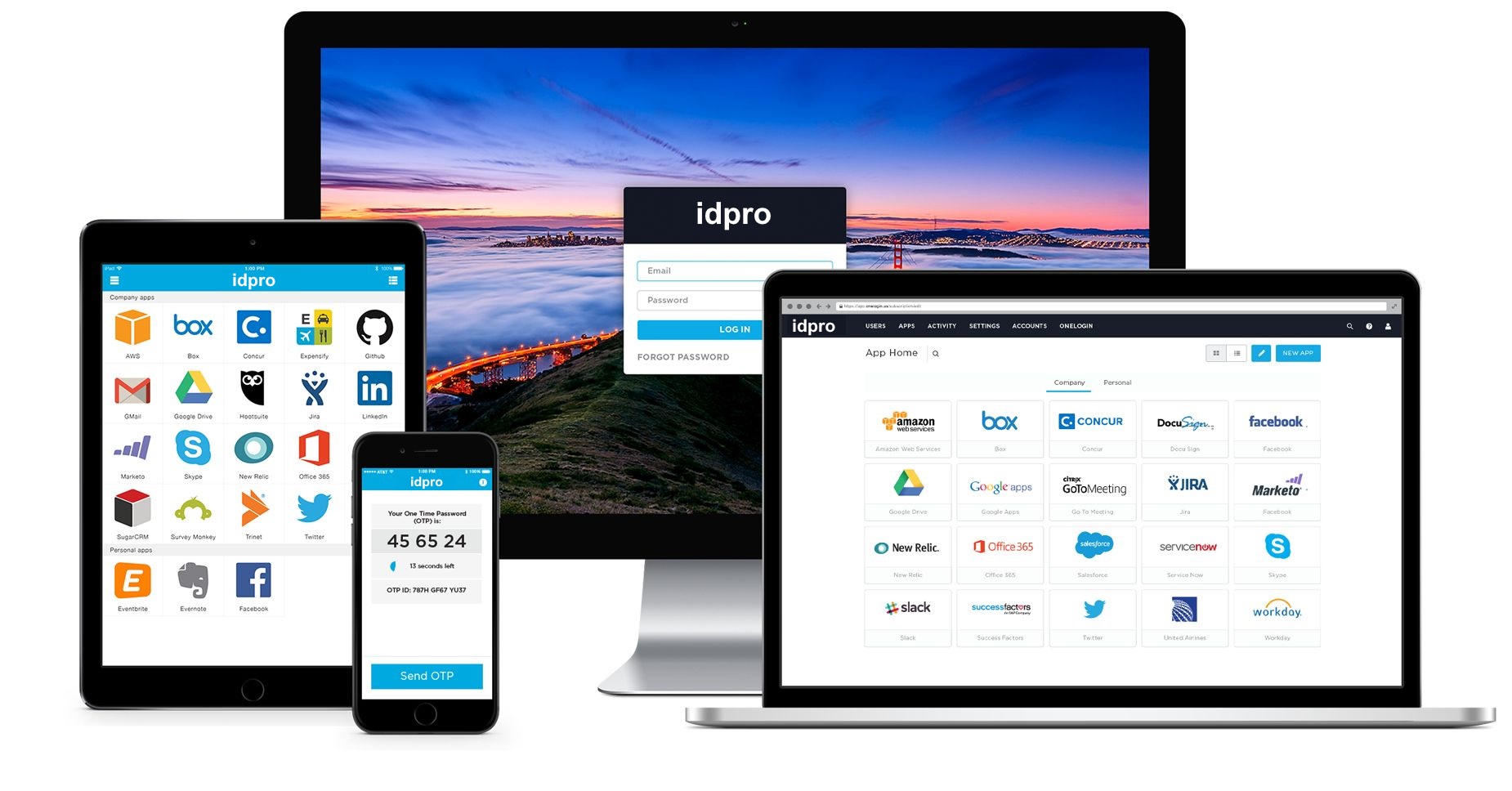
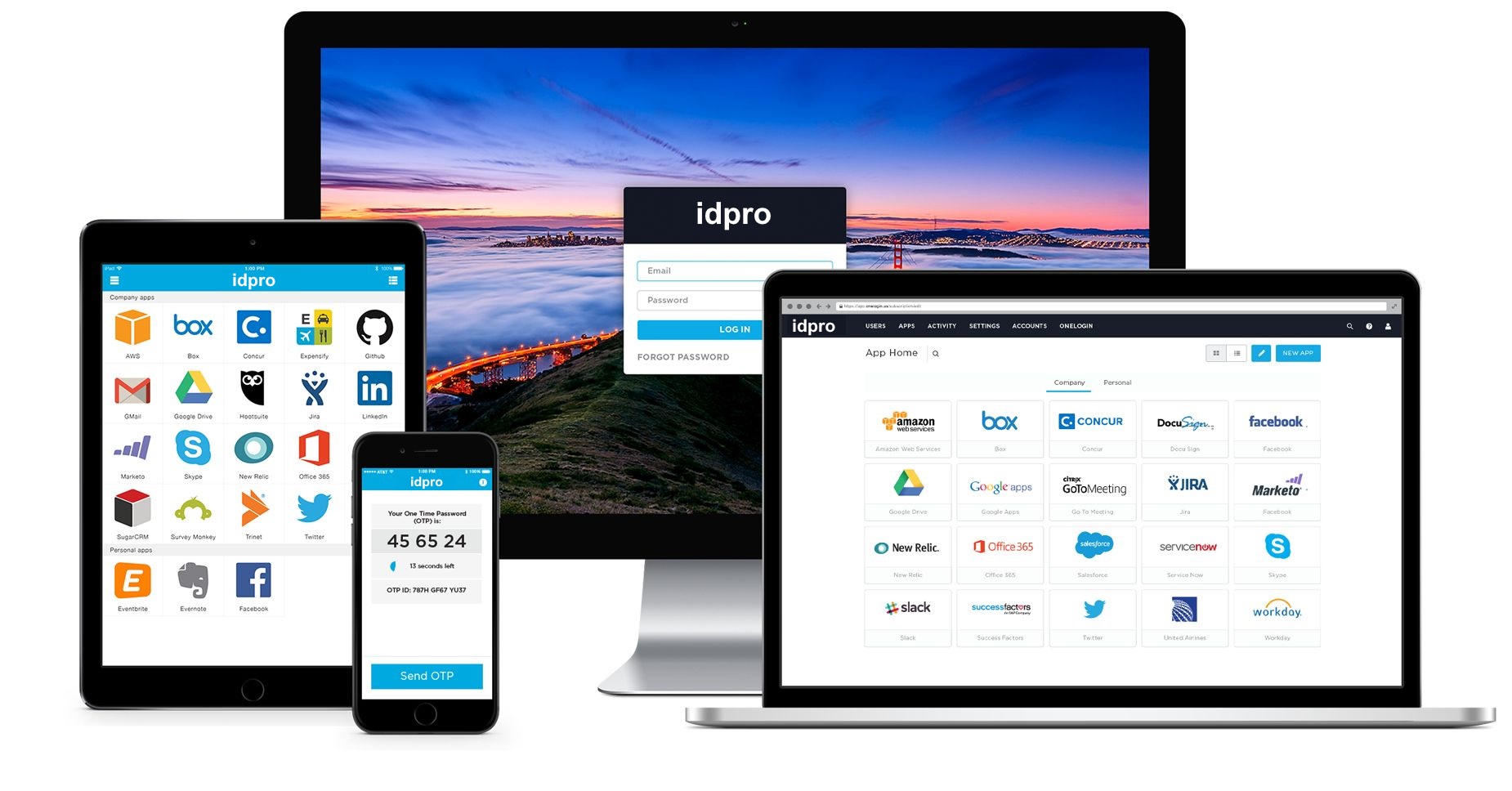
285OneLogin Password Manager User’s Database Breached
Password Manager using the OneLogin? If you just change your account password for all. OneLogin, password management and word-based identity management software...






