Cyber Crime
-

 159
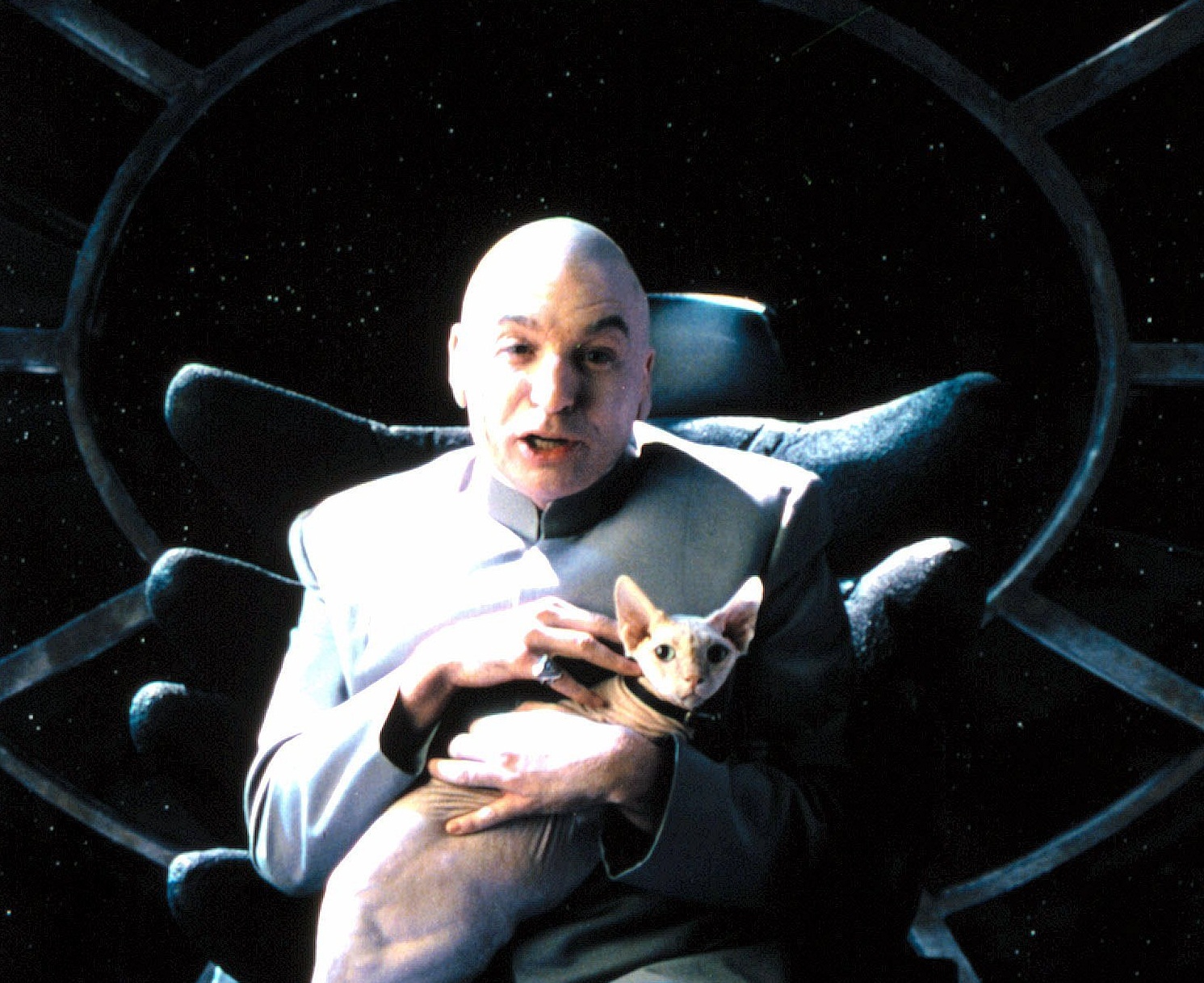
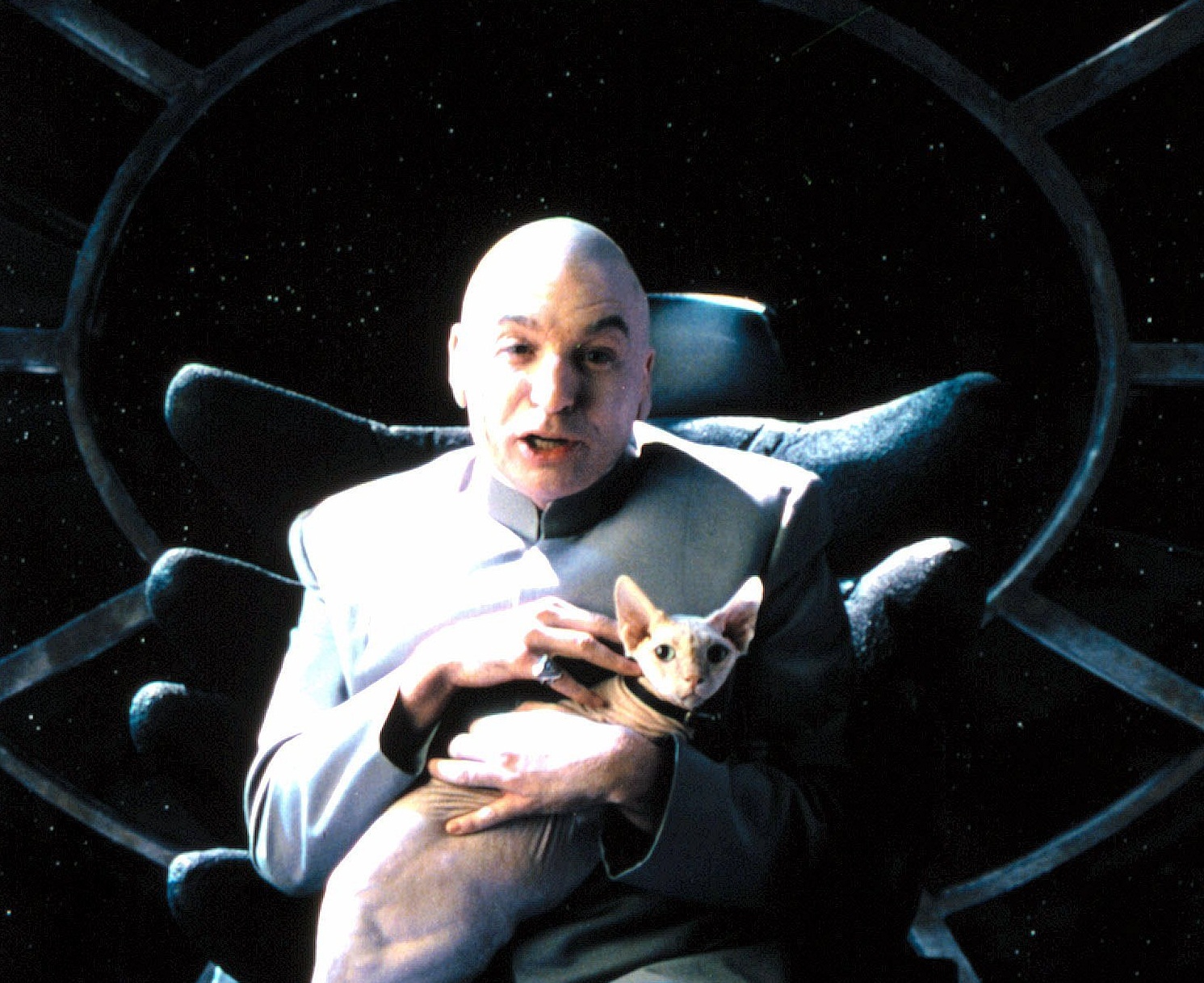
159Big companies still fall for social engineering “hacks” by phone – and it’s not getting better
Major companies such as Disney, Boeing and General Electric are still handing out information to “hackers” using the most basic tool of...
-
 77
77Windows XP users already facing malware invasion – before Microsoft “pulls plug”
Windows XP users already face far higher risks from malware - with XP users facing infection rates six times higher than Windows...
-

 72
72Adobe breach far bigger than thought – 38 million records, Photoshop code leaked in attack
Previously, it had been estimated that around three million users had data accessed, but a new report by Brian Krebs of KrebsonSecurity...
-

 79
79President Obama’s Twitter and Facebook accounts hijacked by hacktivist group
President Obama’s Twitter and Facebook accounts were briefly compromised this week - with two Tweets and one post altered to send links...
-

 74
74Rogue’s gallery? New app aims to “out” cybercriminals who prey on online daters
A new app, Truly.am, aims to put a stop to a fast-growing area of online fraud - online dating scams - by...
-

 345
345Rebuffed! Social site Buffer fights off onslaught of fruity weight‑loss spam
An invasion of fruity posts offering miraculous weight loss flooded Facebook and Twitter accounts linked to the social sharing app Buffer -...
-

 93
93Cyberattack in Israel “shuts down” road for hours
Attackers used a Trojan program to target a security camera system in the Carmel Tunnels toll road in Haifa, shutting down the...
-

 231
231Bill Proposed by Sen. Feinstein would Incriminate Anyone Who Would Speak Against Courts and NSA’s Spying
Diane Feinstein who is member of the senate committee of US and the lawmaker has said that she supports NSA and its...
-

 81
81PHP site WAS serving malicious code, owners admit after Google raises red flag
When Google’s Safe Browsing service said that programming site PHP.net was hosting and serving malware, it sparked furious discussion - but the...
-

 170
170Is this how Indonesia topped the malicious traffic charts?
Indonesia as a major source of malicious traffic? That's what a recent infographic from content delivery network provider Akamai seemed to say....
-

 423
423Millions at risk as guest information from hotel Wi‑Fi provider “goes on sale” in China
A huge amount of private information harvested via hotel Wi-Fi networks is on sale in China - including phone numbers, dates of...
-

 89
89Cyberattacks against major firms “double in one year”, report warns
Cyber attacks have doubled in the year 2012-2013, according to a fraud report released by investigators Kroll - and the target is...
-

 91
91Adobe hackers behind breach at PR Newswire – but company claims “no fake releases” have gone out
The global press release distribution firm PR Newswire has admitted to a large-scale breach, in which usernames and passwords were stolen -...
-

 85
85Indonesia overtakes China as leading source of cyberattacks, Akamai reports
Cyberattacks seem to be a growth industry in Indonesia, with the region having pushed China off the top spot as the leading...
-

 78
78Law “may need longer arm” to tackle international cyber gangs, British police chief admits
Bringing the international gang lords of cybercrime to justice is a “challenge”, the interim head of Britain’s new National Cyber Crime Unit...
-

 400
400Some D‑Link routers contain “backdoor” which allows remote access, researcher warns
Some models of the popular routers made by D-Link contain a “backdoor” which could allow a remote attacker access to settings and...
-

 87
87The wrong cable guys: Card skimmers install bogus wires into cash registers in Nordstrom store
A trio of men plugged keyloggers disguised as ordinary connectors into cash registers in a Nordstrom department store in Florida, and returned...
-
 211
211UK Police Orders Registrars to Shutdown Major Torrent Sites
The newly formed Intellectual Property Crime Unit of the City of London Police (IPCU) is in action. In its first operation the...
-

 73
73EU cyber agency warns of “outdated” systems in power plants – and suggests new safety measures
Cyber attacks against Industrial Control Systems pose a risk to power plants and other critical infrastructure - and action is needed to...
-
 75
75Ponemon study shows costs of cybercrime still rising – each attack now costs $1 million
The costs of cybercrime have continued to rise for victims, for the fourth consecutive year, according to a survey conducted by the...
-

 117
117Waking Shark: Banks to face biggest cyber war game ever in UK
A cyber “war game” will test Britain’s financial system to its limits in a virtual attack which will test the defenses of...






