Data Breach
-

 4.2K
4.2KUnified Identity – look for the meaning behind the hype!
If you’ve listened to software vendors in the identity space lately, you will have noticed that “unified” has quickly become the buzzword...
-
 2.6K
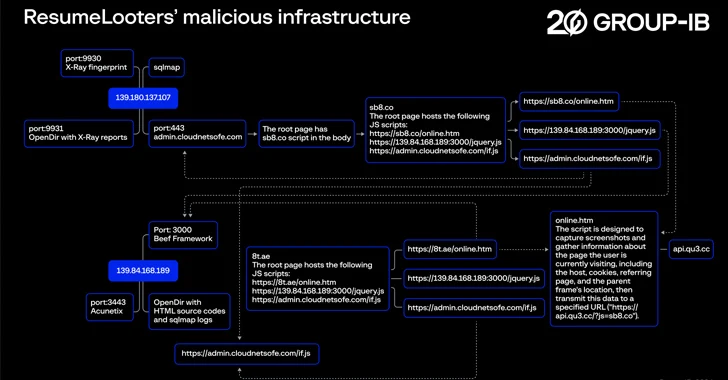
2.6KHackers Exploit Job Boards, Stealing Millions of Resumes and Personal Data
Employment agencies and retail companies chiefly located in the Asia-Pacific (APAC) region have been targeted by a previously undocumented threat actor known...
-

 3.5K
3.5KHands-On Review: SASE-based XDR from Cato Networks
Companies are engaged in a seemingly endless cat-and-mouse game when it comes to cybersecurity and cyber threats. As organizations put up one...
-

 2.4K
2.4KFormer CIA Engineer Sentenced to 40 Years for Leaking Classified Documents
A former software engineer with the U.S. Central Intelligence Agency (CIA) has been sentenced to 40 years in prison by the Southern...
-

 2.5K
2.5KCloudflare Breach: Nation-State Hackers Access Source Code and Internal Docs
Cloudflare has revealed that it was the target of a likely nation-state attack in which the threat actor leveraged stolen credentials to...
-

 2.4K
2.4KThe SEC Won’t Let CISOs Be: Understanding New SaaS Cybersecurity Rules
The SEC isn’t giving SaaS a free pass. Applicable public companies, known as “registrants,” are now subject to cyber incident disclosure and...
-

 545
545Top Security Posture Vulnerabilities Revealed
Each New Year introduces a new set of challenges and opportunities for strengthening our cybersecurity posture. It’s the nature of the field...
-

 414
414Tech Giant HP Enterprise Hacked by Russian Hackers Linked to DNC Breach
Hackers with links to the Kremlin are suspected to have infiltrated information technology company Hewlett Packard Enterprise’s (HPE) cloud email environment to...
-

 1.6K
1.6KU.S., U.K., Australia Sanction Russian REvil Hacker Behind Medibank Breach
Governments from Australia, the U.K., and the U.S. have imposed financial sanctions on a Russian national for his alleged role in the...
-

 2.0K
2.0KBreachForums Founder Sentenced to 20 Years of Supervised Release, No Jail Time
Conor Brian Fitzpatrick has been sentenced to time served and 20 years of supervised release for his role as the creator and...
-

 483
483MFA Spamming and Fatigue: When Security Measures Go Wrong
In today’s digital landscape, traditional password-only authentication systems have proven to be vulnerable to a wide range of cyberattacks. To safeguard critical...
-
 2.2K
2.2K29-Year-Old Ukrainian Cryptojacking Kingpin Arrested for Exploiting Cloud Services
A 29-year-old Ukrainian national has been arrested in connection with running a “sophisticated cryptojacking scheme,” netting them over $2 million (€1.8 million)...
-

 2.4K
2.4KThere is a Ransomware Armageddon Coming for Us All
Generative AI will enable anyone to launch sophisticated phishing attacks that only Next-generation MFA devices can stop The least surprising headline from...
-

 1.3K
1.3KGetting off the Attack Surface Hamster Wheel: Identity Can Help
IT professionals have developed a sophisticated understanding of the enterprise attack surface – what it is, how to quantify it and how...
-
 1.2K
1.2KUnifying Security Tech Beyond the Stack: Integrating SecOps with Managed Risk and Strategy
Cybersecurity is an infinite journey in a digital landscape that never ceases to change. According to Ponemon Institute1, “only 59% of organizations...
-

 435
435Russian Hackers Had Covert Access to Ukraine’s Telecom Giant for Months
Ukrainian cybersecurity authorities have disclosed that the Russian state-sponsored threat actor known as Sandworm was inside telecom operator Kyivstar’s systems at least...
-

 1.9K
1.9KBritish LAPSUS$ Teen Members Sentenced for High-Profile Attacks
Two British teens part of the LAPSUS$ cyber crime and extortion gang have been sentenced for their roles in orchestrating a string...
-

 1.8K
1.8KRogue WordPress Plugin Exposes E-Commerce Sites to Credit Card Theft
Threat hunters have discovered a rogue WordPress plugin that’s capable of creating bogus administrator users and injecting malicious JavaScript code to steal...
-
 2.2K
2.2KCost of a Data Breach Report 2023: Insights, Mitigators and Best Practices
John Hanley of IBM Security shares 4 key findings from the highly acclaimed annual Cost of a Data Breach Report 2023 What...
-

 1.1K
1.1KRemote Encryption Attacks Surge: How One Vulnerable Device Can Spell Disaster
Ransomware groups are increasingly switching to remote encryption in their attacks, marking a new escalation in tactics adopted by financially motivated actors...
-

 3.5K
3.5KProduct Explained: Memcyco’s Real-Time Defense Against Website Spoofing
Hands-On Review: Memcyco’s Threat Intelligence Solution Website impersonation, also known as brandjacking or website spoofing, has emerged as a significant threat to...






