Data Security
-

 85
85US banks attacked, manipulated and left (heart)bleeding
In April 2014 the cybersecurity world was rocked by the discovery of Heartbleed, the name given to a vulnerability found in one...
-
 207
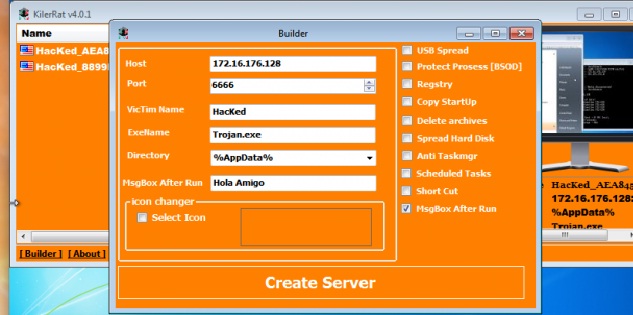
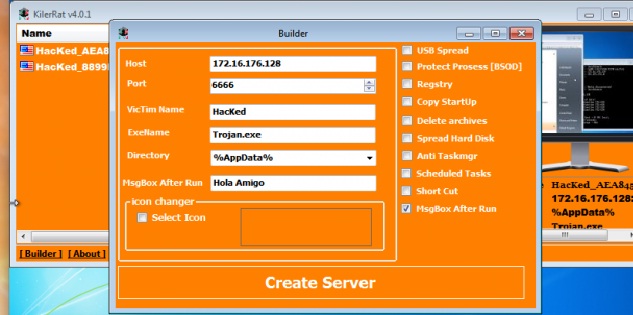
207KilerRat: Taking over where Njrat remote access trojan left off
This remote access trojan (RAT) has capabilities ranging from manipulating the registry to opening a reverse shell. From stealing credentials stored in...
-

 283
283Man Hacks Norwich International Airport Website for Passengers Safety
A hacker going by the handle of His Royal Gingerness (HRG) hacked into the official website of Norwich International Airport last month...
-

 78
78High-Risk SAP HANA Vulnerabilities Patched
Critical business applications such as SAP and Oracle ERP products process and store the Fortune 2000’s most critical data, yet spur relatively...
-
 231
231NSA claims it shares 91% of security flaws with its manufactures
NSA discloses 91 percent of the zero-day bugs it finds in the online systems to its manufacturers while it keeps the 9...
-
 100
100The Infernal-Twin tool, easy hacking wireless networks
The Infernal-Twin is an automated tool designed for penetration testing activities, it has been developed to automate the Evil Twin Attack. The Infernal-Twin...
-

 177
177NSA Discloses 91 Percent of Zero-Day Bugs It Finds, Keeps the Rest for Itself
US spying agency reveals bug disclosure program’s stats An NSA spokesperson said the agency discloses zero-day bugs to manufacturers and affected companies...
-
 305
305The Economist’s Ad-Blocker was Hacked, Delivered Malware to Windows Users
Economist’s anti-ad blocking analytics service got hacked on 31st October (company’s officials didn’t disclose until 5th November) and the exposed site made...
-

 140
140New Android Malware Surfaced, Only Way Out Throw Away Your Phone
Researchers at Lookout Security have found a Shuanet malware that masquerades as some of the most downloaded apps like Facebook, Twitter, and...
-

 168
168Ransomware Found Targeting Linux Servers and Coding Repositories
Malware operators are taking aim at Web developers. A newly discovered ransomware is attacking Linux Web servers, taking aim at Web development environments...
-

 73
73HIDDEN IN PLAIN SIGHT: BRUTE FORCING SLACK PRIVATE FILES
Last year we switched to using Slack for all our internal communication and it’s working out nicely. It’s very developer centric in...
-

 114
114Epic Fail: Power Worm Ransomware Accidentally Destroys Victim’s Data During Encryption
A variant of the Power Worm ransomware is infecting computers, encrypting their data files, and throwing away the encryption key, all because...
-
 91
91CIA Email Hackers Return With Major Law Enforcement Breach
HACKERS WHO BROKE into the personal email account of CIA Director John Brennan have struck again. This time the group, which goes...
-

 143
143Quick Q&A with the Author of Mabouia, First Mac OS X Ransomware
Rafael Salema Marques is a Brazilian cyber-security researcher and, above all, a devoted Mac user. Today, Mr. Marques published a LinkedIn blog...
-
 84
84Top FBI lawyer: You win, we’ve given up on encryption backdoors
We’re your servants, says general counsel unconvincingly After spending months pressuring tech companies to add backdoors into their encryption software, the FBI...
-
 99
99Crypto e-mail service pays $6,000 ransom, gets taken out by DDoS anyway
Follow-on attacks show capabilities “commonly possessed by state-sponsored actors.” A provider of end-to-end encrypted e-mail said it paid a ransom of almost...
-

 331
331SDK Security Flaw Puts 100 Million Android Users Vulnerable to Backdoor Attack
A software development kit that has been provided by Baidu (A Chinese search engine) can easily be exploited for installing backdoors on...
-

 160
160Linux Servers to Blame for 45 Percent of All DDoS Attacks in the Past 3 Months
Cyber-security vendors are revealing their statistics for the third quarter (Q3) of 2015, and a popular topic is DDoS attacks, a tactic...
-

 180
180UK cyber-spy law takes Snowden’s revelations of mass surveillance – and sets them in stone
IPB The encryption bothering parts of the UK’s Investigatory Powers Bill have left IT security experts flabbergasted. Introducing the draft internet surveillance...
-

 319
319Teen Hackers Who Doxed CIA Chief Are Targeting More Government Officials
A cybersecurity expert once told me something I’ll never forget: “don’t underestimate what bored teenagers can do.” A group teenagers that call...
-

 105
105Russian Banks Under Attack from Tinba Banking Botnet
Customers of Russia’s biggest banks are under attack.Dell SecureWorks has detected an ongoing campaign that is targeting users of several Russian banks...






