Data Security
-

 294
294A bug lets you crash anyone’s iPhone with a text message
Apple iOS mobile operating system’s Message App bug causes its devices iPad, iPhone and Apple Watch to crash and/or reboot. Apple announced...
-

 258
258Thanks IRS for poor security: Financial Info On 100,000 Taxpayers Stolen
The IRS announced in an official statement today that it has closed down an online service to obtain tax records after sensing...
-
 304
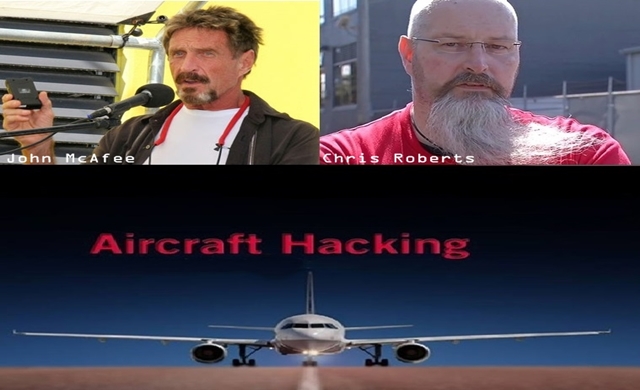
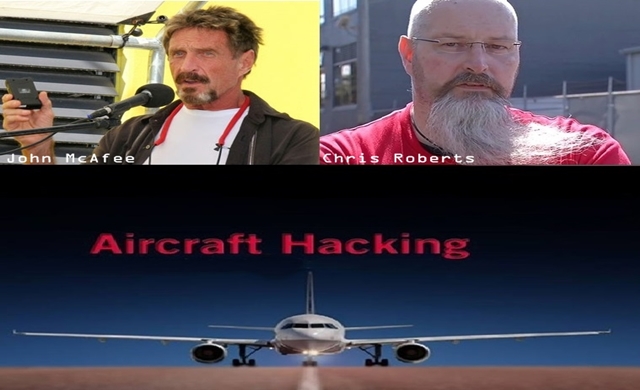
304John McAfee supports his pal who found security flaw, hacked an aircraft
Summary: An official statement issued by an FBI agent reveals that InfoSec researcher Chris Roberts has confessed to hacking into the controls of...
-

 184
184“Failure in Parcel Delivery” Fake Email Drops Malware on USPS Customers’ PC
Please note that the email that appears to be sent by USPS informing that due to incorrect address the firm has failed...
-
 234
234WhatsApp users hit with ‘You Just Got an Audio Recording’ Email Malware
The email apparently is sent from the popular messaging service WhatsApp and claims that you have received an audio recording. A malicious...
-
 289
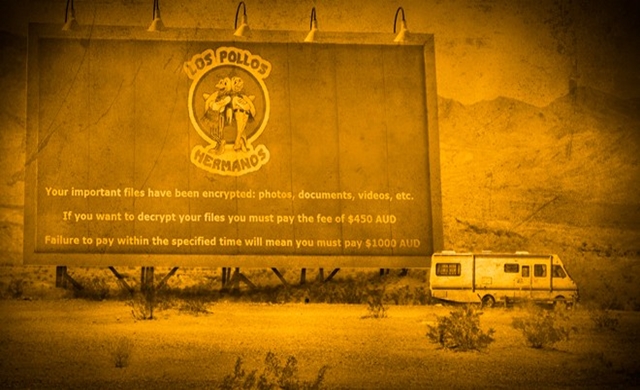
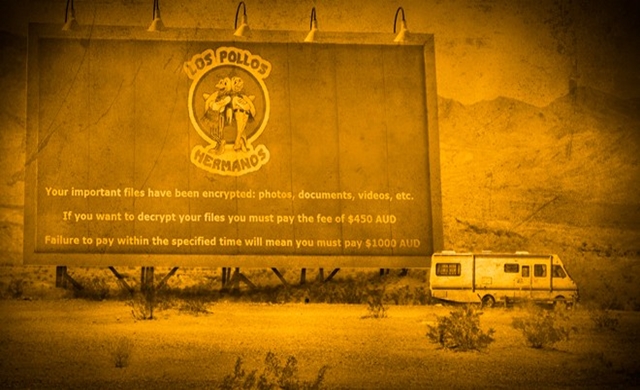
289Internet users hit with Breaking Bad Theme Crypto-Malware
To demonstrate their creativity cybercriminals have released a new ransomware equipped with file encryption abilities and this time they have chosen logo...
-

 351
351United Airlines Bug Bounty Program: Report Security Flaw, Get Rewards
If you are a hacker or an IT security researcher, United Airlines has announced its first ever Bug Bounty program for you...
-

 220
220Anonymous team hides malware in Nvidia GPUs, can harm Mac, Linux, Windows
Summary: In a bid to raise awareness regarding the way malware can affect GPUs, a team of developers recently created a Linux...
-

 160
160Researcher claims Starbucks mobile app got hacked, credit card data stolen
Summary: Earlier this week Bob Sullivan reported that hackers can easily access Starbucks customer accounts by stealing their username and passwords and naturally Starbucks...
-

 218
218Notion of Cloud’s Unmatched Security Shattered by ‘Venom’ vulnerability
The CrowStrike researchers discovered that any attacker can burst out of specific virtual machines and exploit whatever is running nearby — The...
-
 252
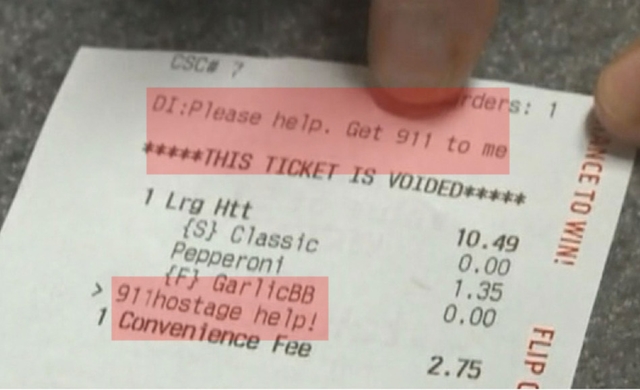
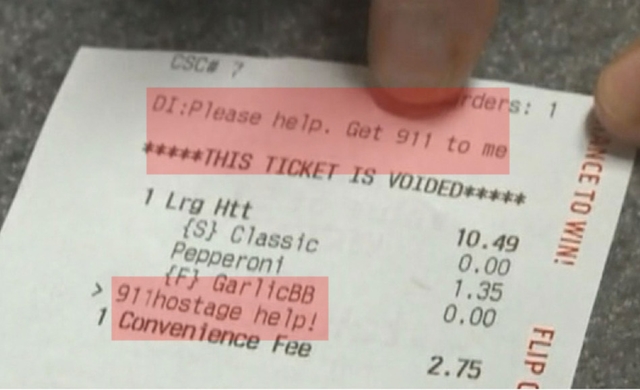
252Mother uses Pizza Hut online Order to inform police about hostage situation
A Florida based woman thwarted a dangerous hostage situation by using the delivery instructions section of an online pizza ordering service by...
-

 240
240Hackers charge $90 to hack Gmail, $200 to $350 for Facebook, WhatsApp
Can you believe there are several online forums who actually claim to provide hackers in case you want to get someone’s Website, Facebook,...
-

 203
203TeslaCrypt looks like AlphaCrypt Malware uses TOR to transfer ransomware
AlphaCrypt Crypto-Malware the actual mind blower is that it Looks like TeslaCrypt and acts like CryptoWall. the latest piece of ransomware with...
-
 198
198Seemingly Legit Resume actually contains Crypto-Malware
The malicious email, targeted at a company’s resume screening department, is equipped with file encryption capabilities. A new ransomware having capabilities of...
-

 267
267Lenovo accused of ‘massive security risk’ by researchers
The IOActive researchers reported that Lenovo devices software has serious security flaws and vulnerabilities that can be easily exploited by cyber criminals...
-
 194
194This New Rombertik Malware Crashes Your PC Once Detected
A complex malware dubbed as Rombertik has been designed to steal user data and comprises of several layers of anti-analysis functionality and...
-
 309
309Simple Tips to manage and Prevent Social Engineering Attacks
The web is an interconnected maze consisting of people, organization and computers. The easiest way to hack into such a system is...
-

 277
277Boeing 787s can lose control while flying due to Software bug
A warning has been issued by the FAA regarding the software glitch in the system of Boeing’s 787 Dreamliner — This glitch...
-

 383
383Banking Malware Delivered via Macro in PDF Embedded Word Document
Delivering banking malware through Microsoft Word documents has been a less common method. However, it is currently being used for spreading malicious...
-

 268
268WikiLeaks’ Anonymous Leak Submission Website Relaunched after 6 years
Expect exposure of confidential news pieces and government/corporate classified documents every now and then because WikiLeaks, the anti-secrecy group has re-launched its...
-
 307
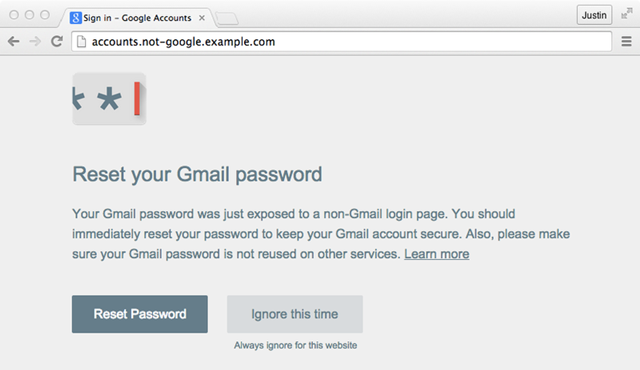
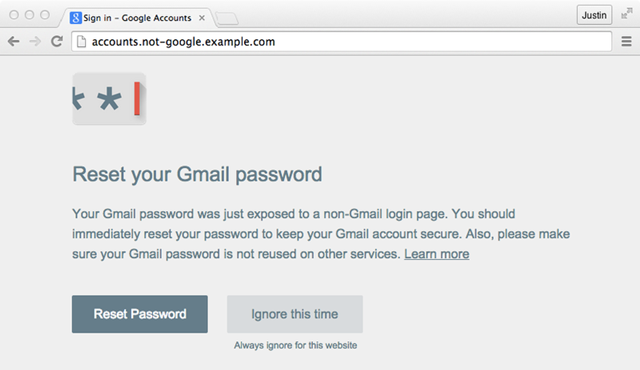
307New Google Chrome extension will save you from Phishing Attacks
Google has recently unveiled a new Chrome extension called Password Alert, designed as a defense tool for phishing threats by issuing an...






