Data Security
-

 1.5K
1.5KAzure DDoS Protection service was unable to protect Microsoft, how it will protect clients?
In recent weeks, a hacker collective calling itself Anonymous Sudan has been responsible for launching distributed denial of service attacks (DDoS) on...
-
 1.2K
1.2KEasily hack into Azure Bastion and Azure Container Registry via XSS vulnerabilities
Microsoft Azure Bastion and Azure Container Registry have each been found to have one potentially “dangerous” security flaw that, if taken advantage...
-

 729
729Hack networks using Citrix ShareFile StorageZones Controller using the flaw with CVSS score of 9.1
In the constantly shifting field of cybersecurity, new problems are always cropping up, which requires prompt attention and comprehensive answers. A severe...
-

 4.1K
4.1KHacking WooCommerce websites to get order details and customer personal information
The ever-changing topography of cyberspace always results in the introduction of new security flaws and vulnerabilities. A major vulnerability, which is now...
-

 1.4K
1.4KBig german university shuts down every computer on campus after ransomware attack
Following events that have affected at least a half dozen other comparable institutions in recent months, the Kaiserslautern University of Applied Sciences...
-

 2.3K
2.3KNew AiTM Phishing Attack Technique Makes It Easy to Hack Business Email Accounts
Experts from Microsoft Defender discovered a multi-stage adversary-in-the-middle (AiTM) phishing and business email compromise (BEC) attack that targeted firms that provide banking...
-

 3.5K
3.5KNew zero day vulnerability in MOVEit Transfer & Cloud. How many more victims there will be?
As more organizations come out to declare data breaches that were caused by the program’s flaws, the developer of the popular MOVEit...
-
 4.5K
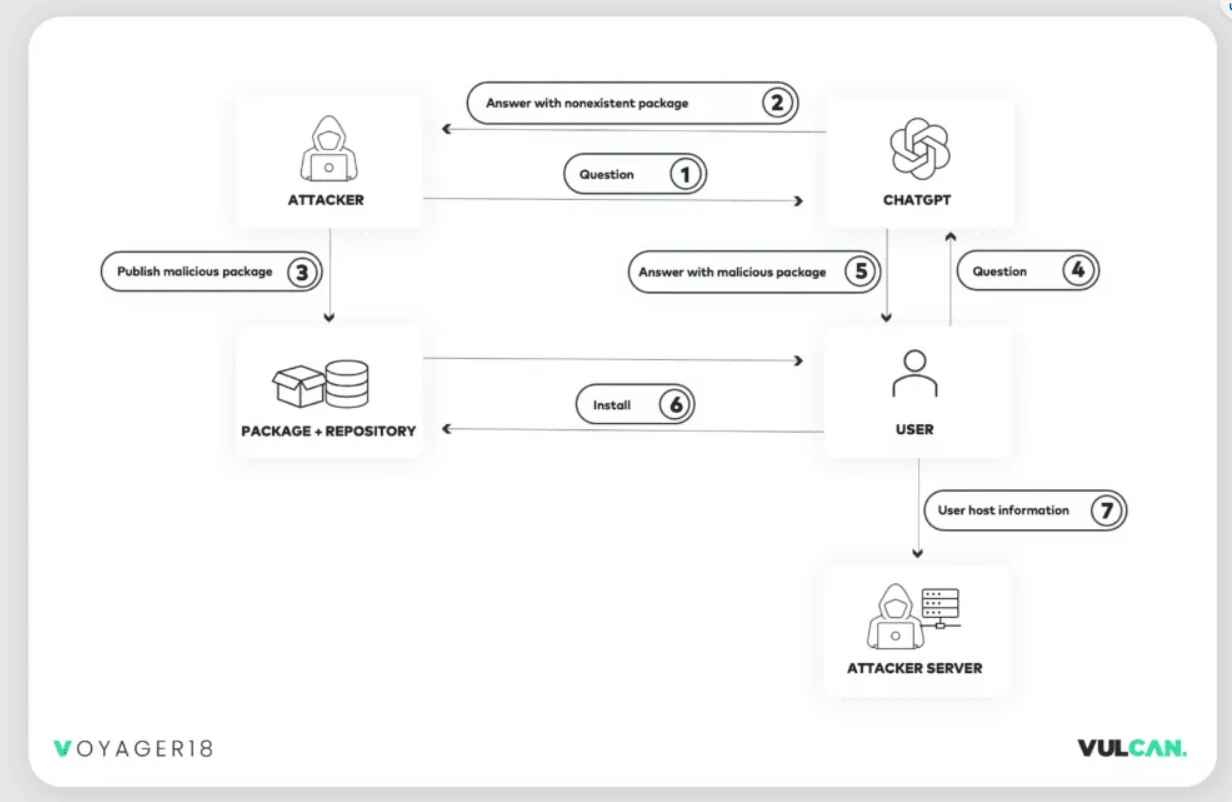
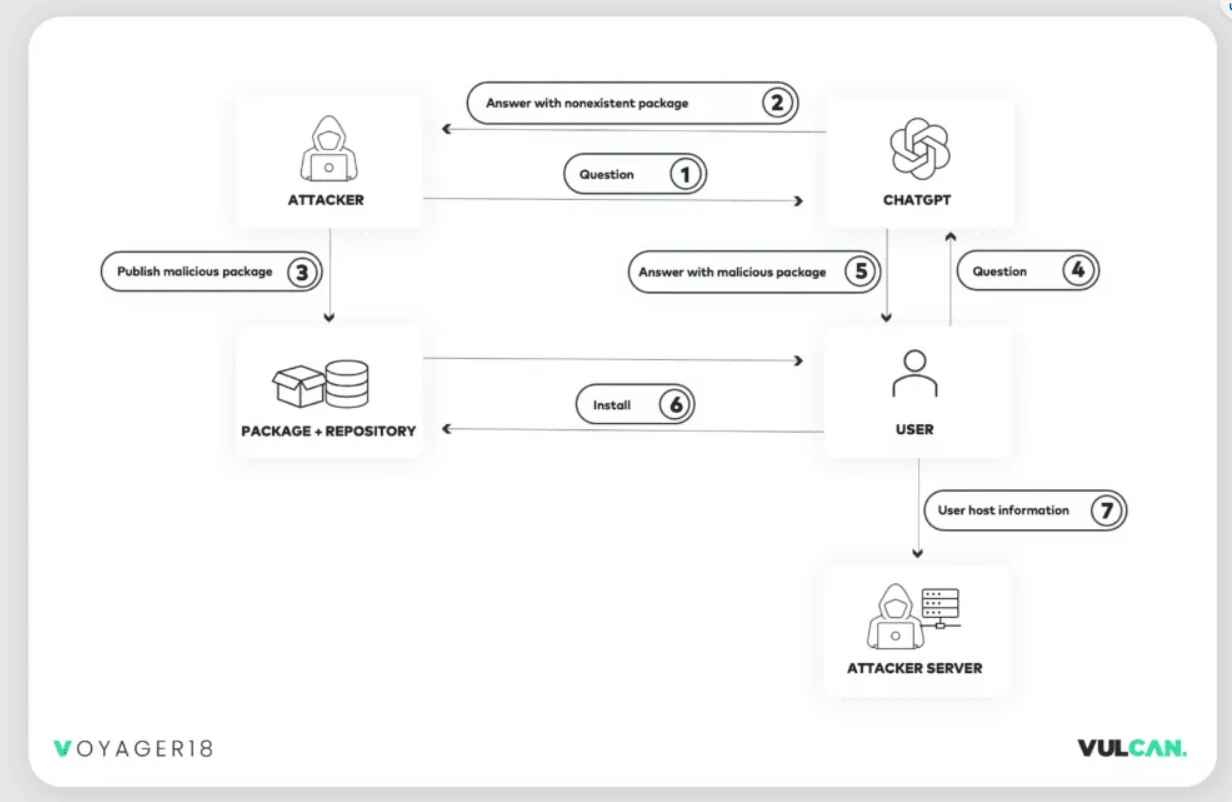
4.5KNew undetectable technique allows hacking big companies using ChatGPT
According to the findings of recent study conducted, harmful packages may be readily propagated into development environments with the assistance of ChatGPT,...
-

 4.2K
4.2KYes it is possible to hack someone via Chrome, Brave, Opera browser using this zero day flaw
The most widely used web browser in the world, Google Chrome, has been found to have a critical zero-day vulnerability that has...
-

 2.7K
2.7KI am being blackmailed with my fake nude images & porn video. What should I do?
The Federal Bureau of Investigation (FBI) has issued a warning about an emerging pattern in which bad actors are increasingly producing deepfake...
-

 601
601Send spoofed phishing emails to Gmail accounts
The most people use Gmail, which has a total user base of a staggering 1.5 billion people. This represents 18.75% of the...
-

 2.8K
2.8KIsolate or shut down your MOVEit Transfer servers and machines immediately
The significance of keeping one’s data safe has never been more pressing than it is in today’s increasingly linked society. Zero-day vulnerabilities...
-

 2.2K
2.2KThrow away your iPhones Says Putin to Russians & claims NSA has a backdoor in iPhones
The Russian Federal Security Service (FSB) has accused the United States Intelligence Community of hacking into “thousands of Apple phones” in order...
-

 4.0K
4.0KIf you own a Toyota, hackers know your past location where you have been in last 6 years
According to Reuters, Toyota Motor Corporation has admitted to a huge data breach that has left customer information exposed throughout Oceania and Asia,...
-

 2.0K
2.0KIf your Laptop or PC has Gigabyte motherboard then it has backdoor for hackers
Researchers at the cybersecurity firm Eclypsium, which focuses on firmware, reported today that they have found a secret backdoor in the firmware of...
-
 4.7K
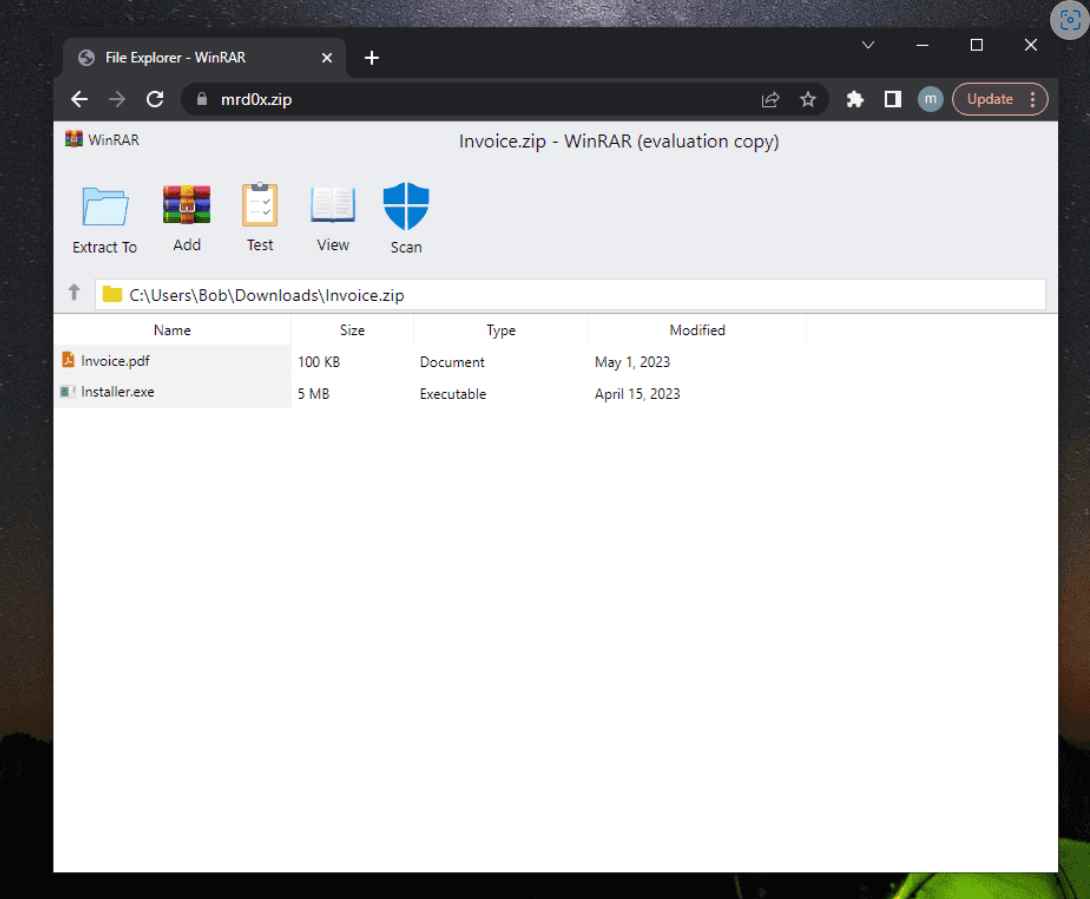
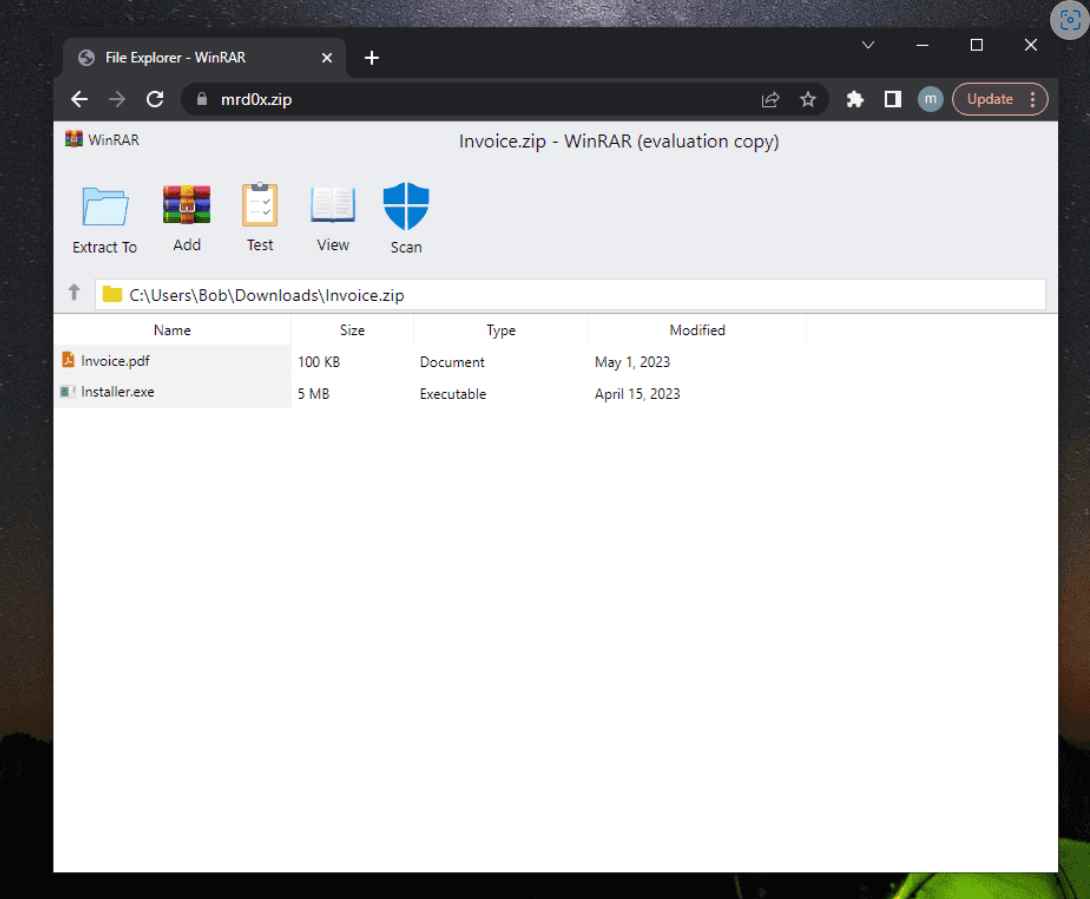
4.7KNew phishing technique to allows hacking someone using .zip & .mov domains
When a victim visits a website ending in .ZIP, a recently developed phishing method known as “file archiver in the browser” may...
-

 2.0K
2.0KOpenSSL flaw allows slowing down websites and applications with client authentication
For your online application or server to be secure, SSL/TLS certificates are necessary. While many trustworthy certificate authorities charge a fee for...
-

 3.6K
3.6KPortuguese banks customers beware these hackers want to steal your money
According to a report published by SentinelLabs on Thursday, a Brazilian hacking crew targeted users of more than 30 Portuguese financial institutions...
-

 4.6K
4.6KHack GitLab with this flaw of CVSS score of 10 to leak program code, user passwords, tokens
GitLab Inc. is an open-core corporation that runs GitLab, a software package that may be used to build, protect, and administer software....
-
 1.4K
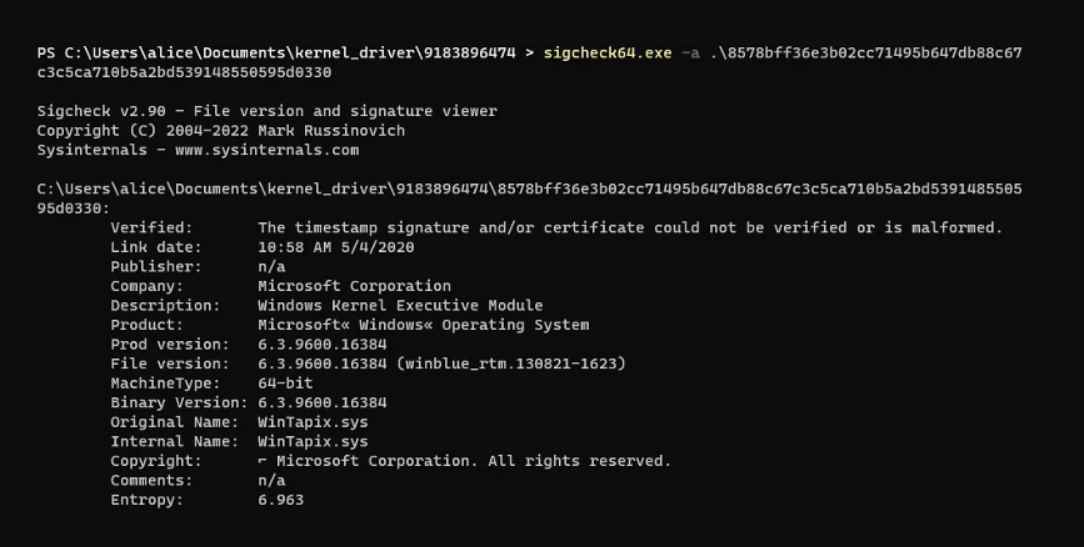
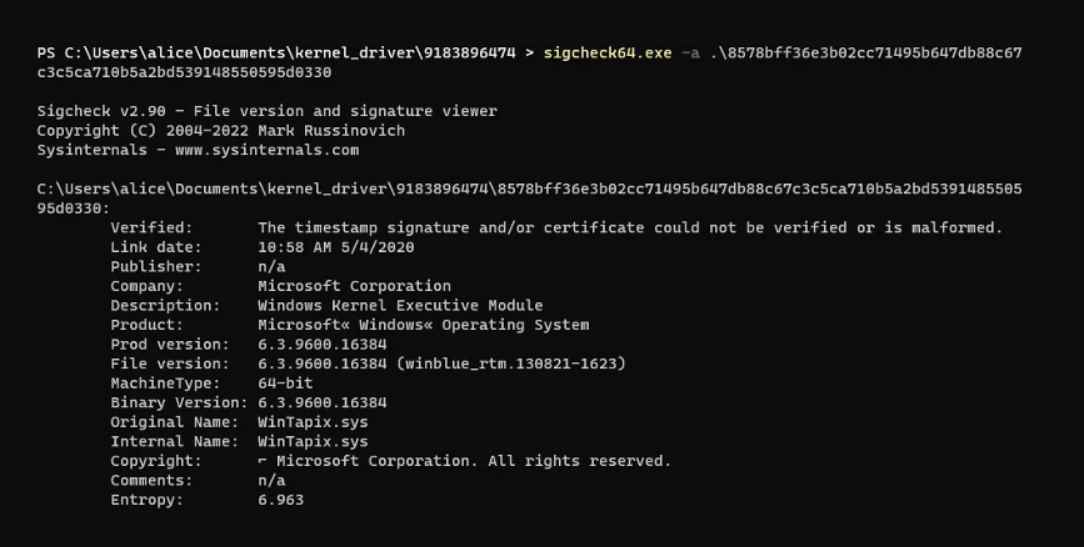
1.4KWinTapix: A Windows kernel driver that hackers are exploiting. Check your system processes!
WinTapix is a driver developed by Microsoft for Windows.Donut is a position-independent shellcode that is used by this driver. It loads.NET Assemblies,...
-
 3.8K
3.8KPyPI gives up against hackers, stops new user signups and new packages uploads
Python Package Index (PyPI), the official third-party software repository for the Python programming language, has temporarily restricted the ability for users to...






