Geek
-

 439
439Agent Smith Android malware has infected 25 million devices so far
Agent Smith malware exploits Android vulnerabilities to target unsuspected users for credential stealing. The IT security researchers at CheckPoint have discovered a...
-
 336
336Twitter is down – Twitter’s website & app suffering outage (Updated)
As surprising as it may sound, Facebook is up but Twitter is down. The online news and social networking site Twitter is...
-

 352
352Vulnerability in Zoom video conference app lets Mac’s camera hijacking
The vulnerability in the Zoom video conference app lets attackers hijack Mac’s camera by merely using malicious websites. The Zoom video conference...
-
 430
4309 Best Linux Distros For Beginner Users — 2019 Edition
Are you looking for a Linux distro that’s suitable for new users who are willing to start an exciting Linux journey? Well, you’re...
-

 351
351Popular Android Zombie game phish users to steal Gmail credentials
The app made its way to Google Play Store was also found phishing users for Facebook credentials. Scary Granny ZOMBY Mod: The...
-
 402
402ViceLeaker Android malware steals call recordings, photos, videos & texts
Israeli Citizens are the Primary Target of New Android Mobile Spying Campaign Using ViceLeaker Malware, says Kaspersky. Kaspersky Lab researchers discovered an...
-

 355
355New Windows 10 bug causes PCs to take longer to shut down
Windows 10 bug: If you have a device connected via cable to the USB Type-C input, you may have to wait another...
-

 280
2807 Easy-to-Use Java Performance Tuning Tips
Are you looking for easy-to-use Java performance tuning tips because you want to learn more developer knowledge and experience because of the...
-

 434
434New cryptomining botnet malware hits Android devices
The new malware exploits Android Debug Bridge (ADB) ports. In a research conducted by the Tokyo-based cybersecurity and threat defense firm Trend...
-
 344
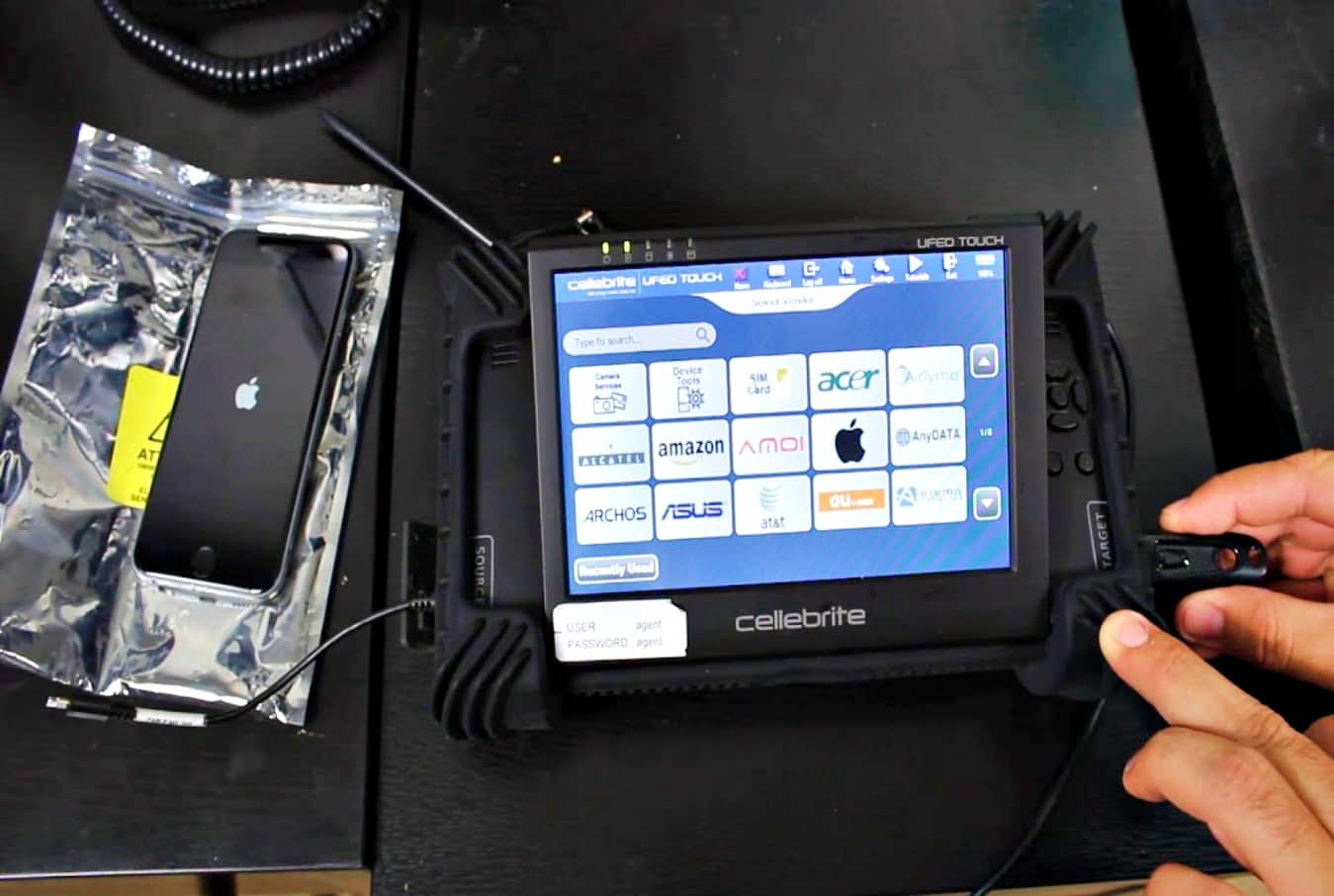
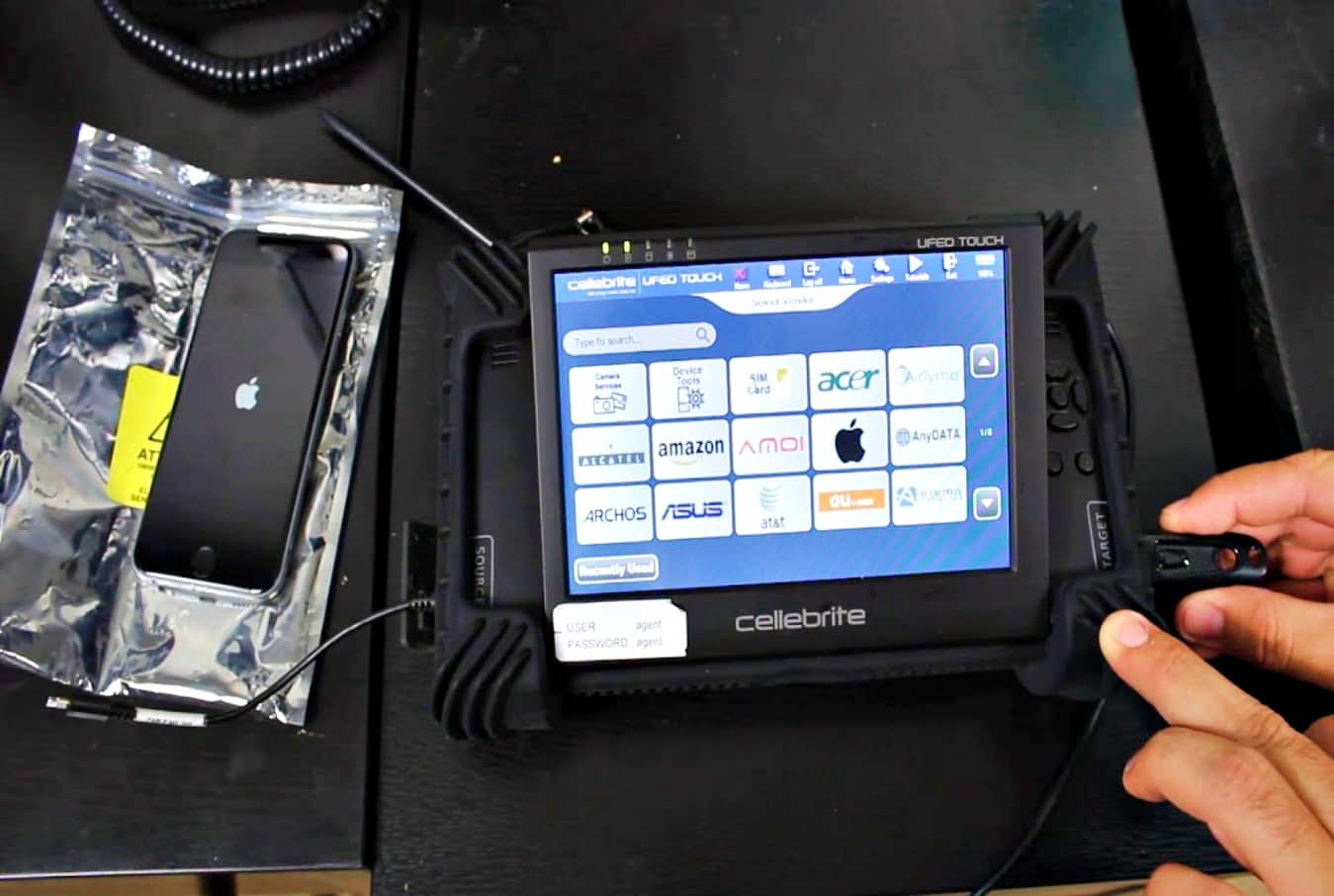
344Cellebrite claims its new tool unlocks almost any iOS or Android device
Cellebrite is the same company which helped the FBI to unlock iPhone device of San Bernardino shooter. Renowned Law Enforcement contractor, the...
-

 459
459Instagram down: Social networking site suffering service outage
Instagram down? You are not alone; Instagram is down for everyone. Another day, another service outage at social media giant Facebook. Yes,...
-
 281
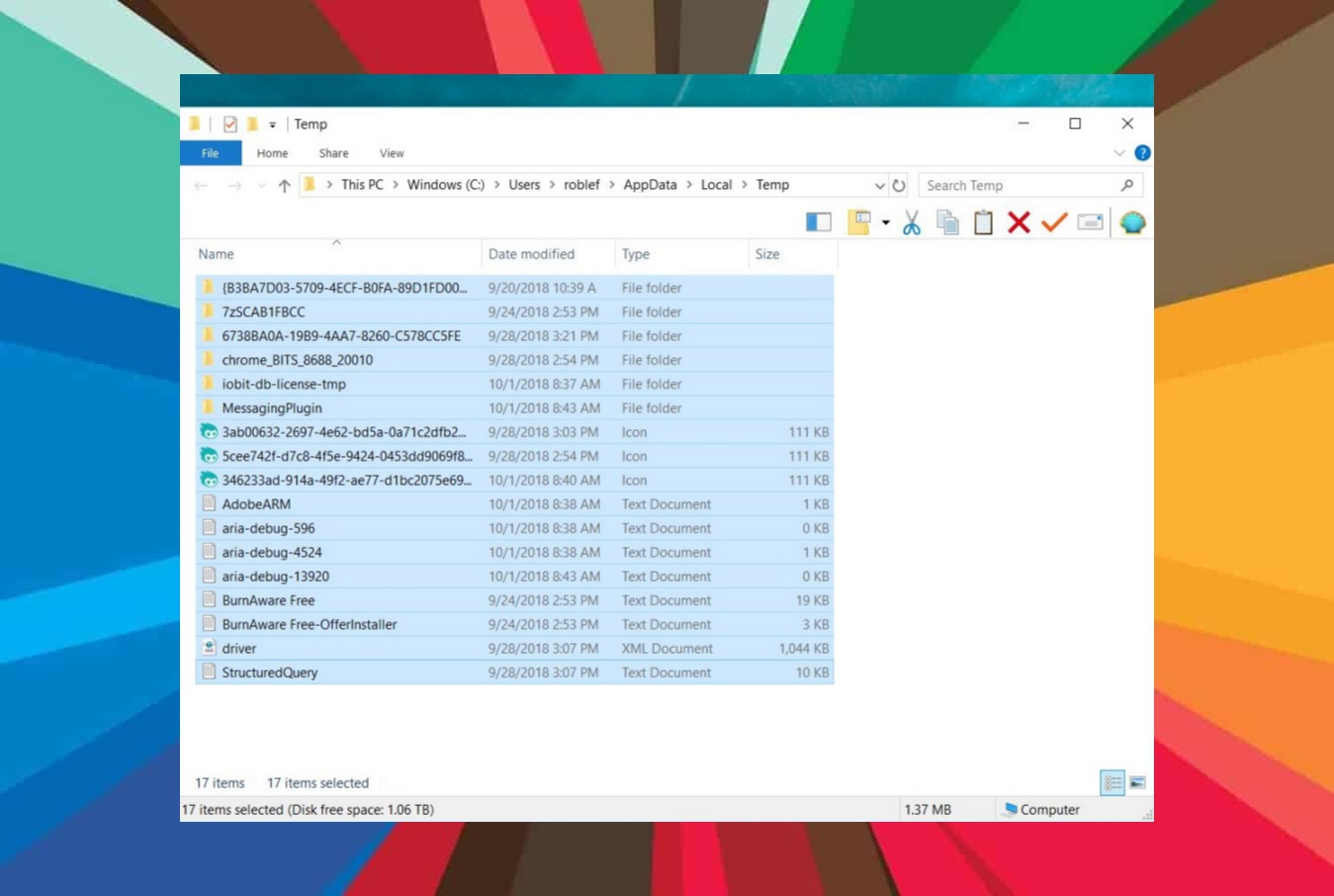
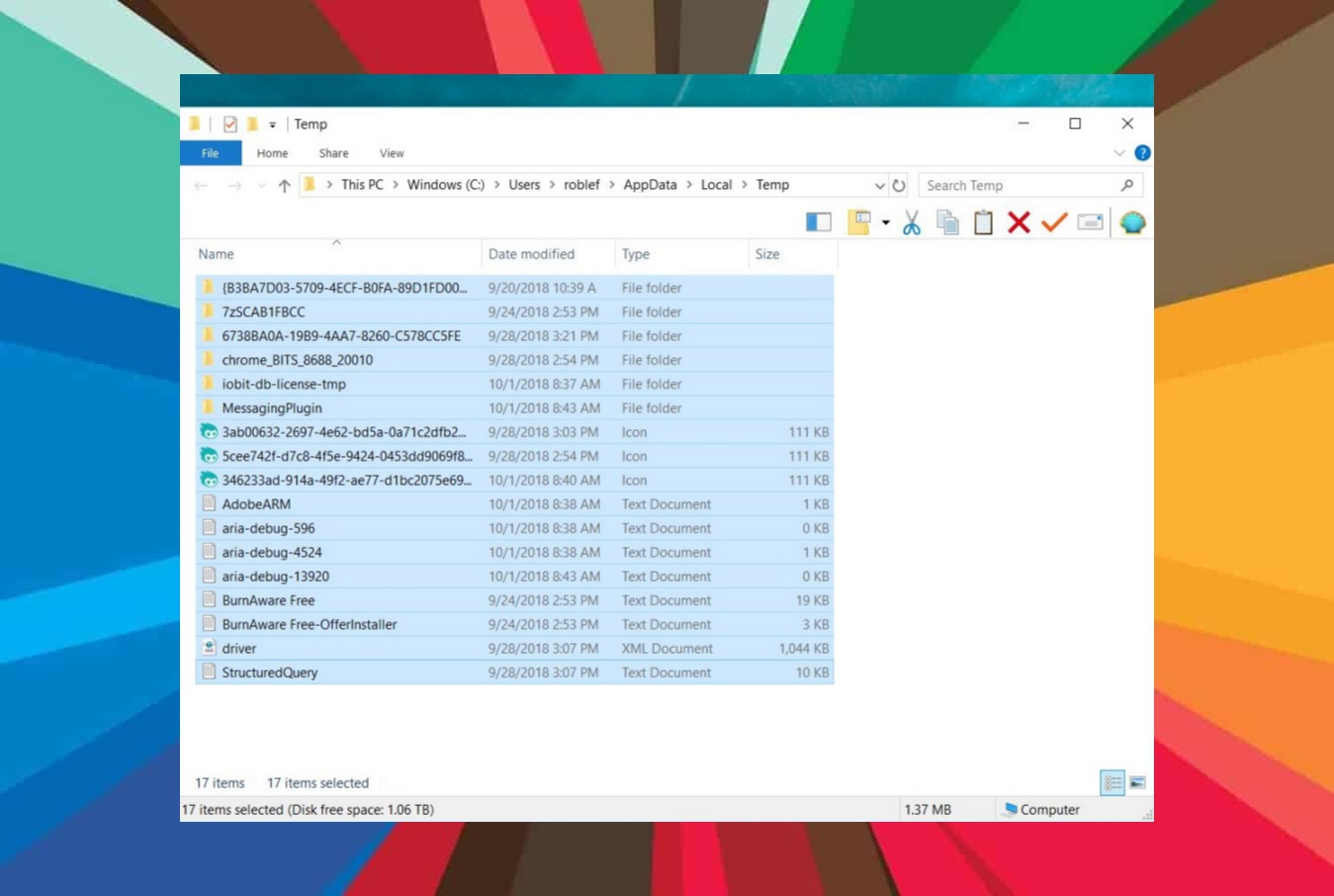
281How to Remove Temporary Files In Windows 10?
Over time, temporary files can accumulate and take up storage space. If you want to free up storage space, you can delete...
-

 417
417Google confirms presence of Triada backdoor in cheap Android phones
Triada Banking Trojan came Preinstalled as Backdoor in Budget Android Smartphones- Google Confirms. It would probably be the first time ever in...
-

 550
55010 Best Raspberry Pi Alternatives Comparison: x86 And ARM SBCs For 2019
In the search for the best Raspberry Pi alternatives, we often forget that the original Pi-SBC is arguably one of the most...
-

 212
212MetaTrader 4 vs MetaTrader 5 iPhone app
If you are an online trading enthusiast, you can use MetaTrader 5 and MetaTrader 4 iPhone apps to trade forex. Though the...
-
 366
366Google may limit ad blockers for Chrome users
Google May Limit Ad blockers for Regular Users Amidst Criticism from Consumer Advocates. Google Chrome is perhaps the most popular of all...
-

 250
250Teen hacked Apple twice hoping for a job
He hacked his way into the tech giant’s mainframe by creating false credentials. Now that is what we call a very unorthodox...
-

 272
2726 Open Source Android Alternative Operating Systems For Mobiles
In the wake of the ongoing US-Huawei-Google tussle, many Android enthusiasts are wondering about the different alternative phone operating systems that are...
-

 253
253Google bans Huawei from accessing Android & its licensed apps
Intel Corp., Broadcom Inc., Qualcomm Inc., Xilinx Inc., etc., have also refused to supply critical components and software to Huawei. The US...
-
 563
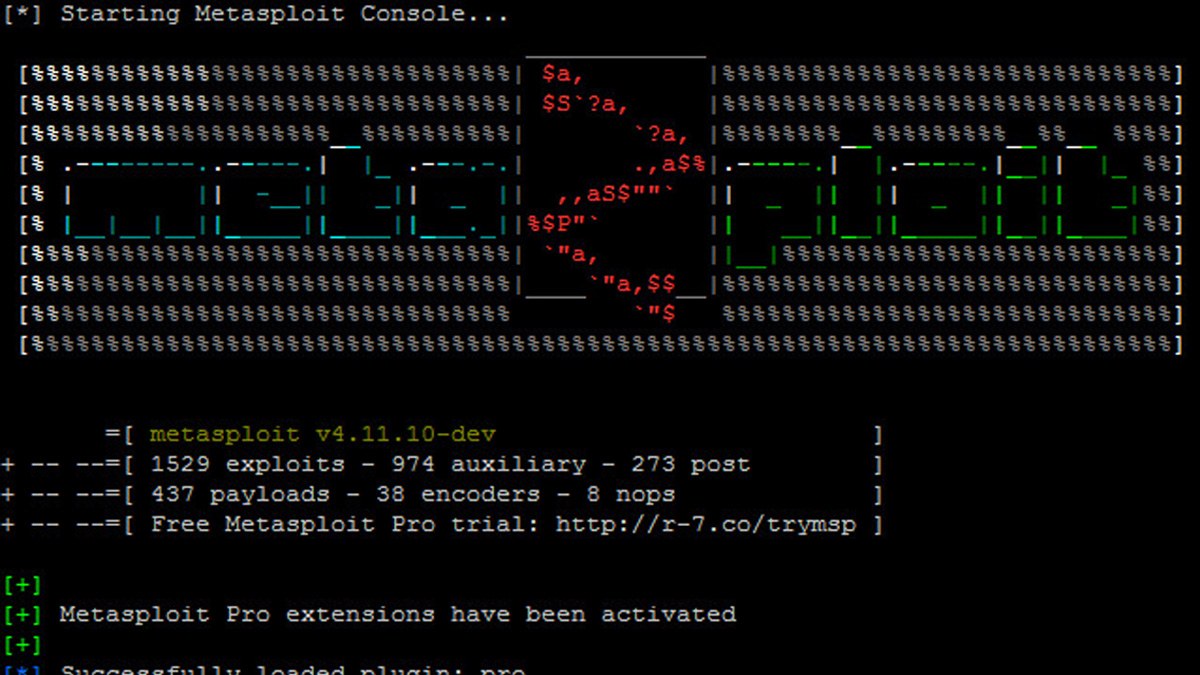
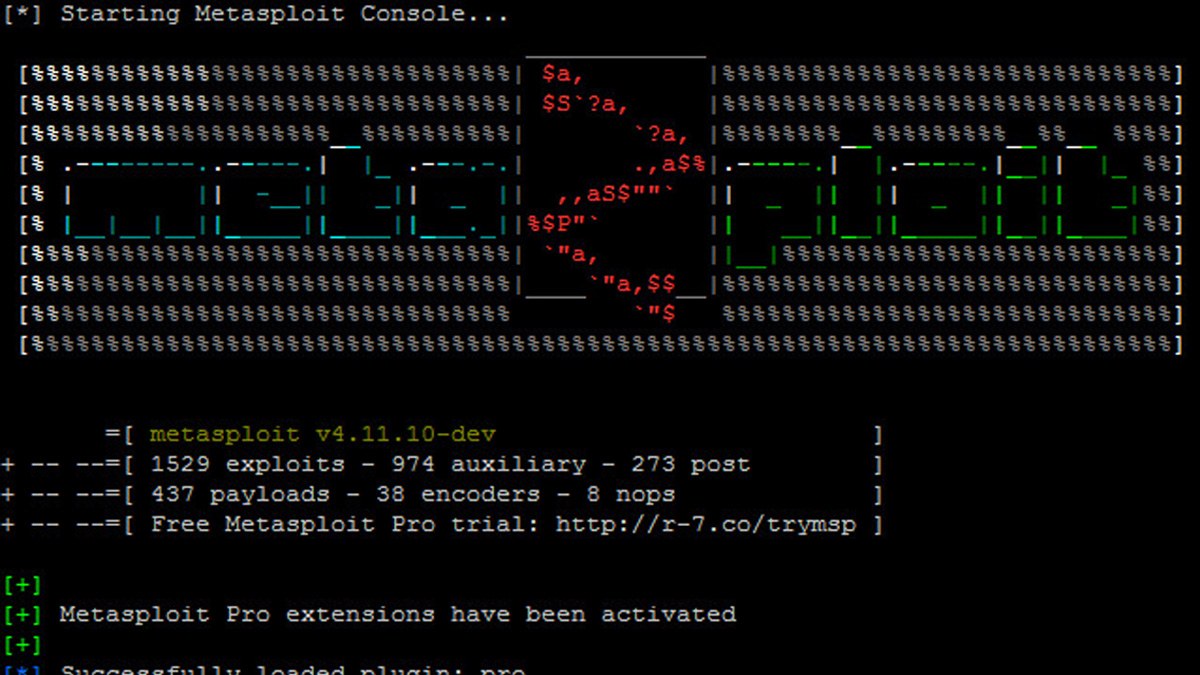
5639 Best Kali Linux Tools For Hacking And Pen-Testing In 2019
Linux-based distros are the most preferred platforms for ethical hacking. Specifically, open source operating systems like Kali Linux Tools and Parrot are...
-

 259
259How to make Microsoft 70-412 exam preparation effective with Prepaway web resource
The Microsoft 70-412 certification exam validates that you have what it takes to configure advanced Windows Server 2012. This test is one...






