Hacked
-
 292
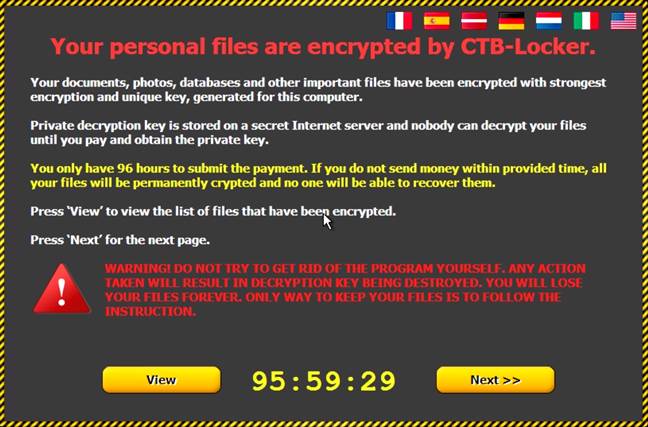
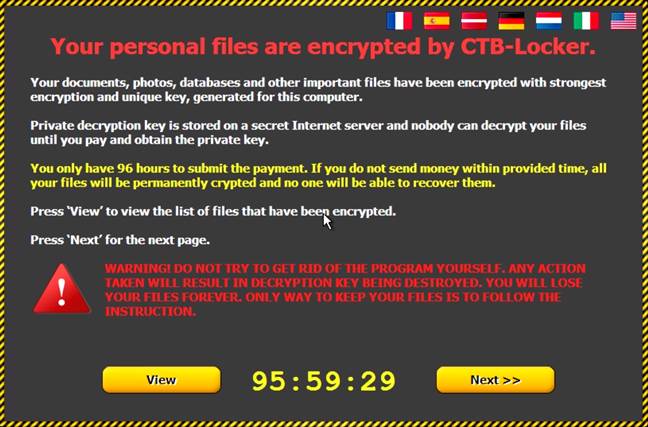
292Beware: A Dangerous Windows 10 Ransomware Scam Is Spreading Online
Short Bytes : A Windows 10 Ransomware scam has been reported by Cisco security blog. This phishing scam sends fake emails that look...
-

 204
204US Decides To Counter-attack Against Chinese Hacking
Short Bytes : As the cyber attacks are getting more and more pervasive, the White House is seeking ways to retaliate against...
-
 329
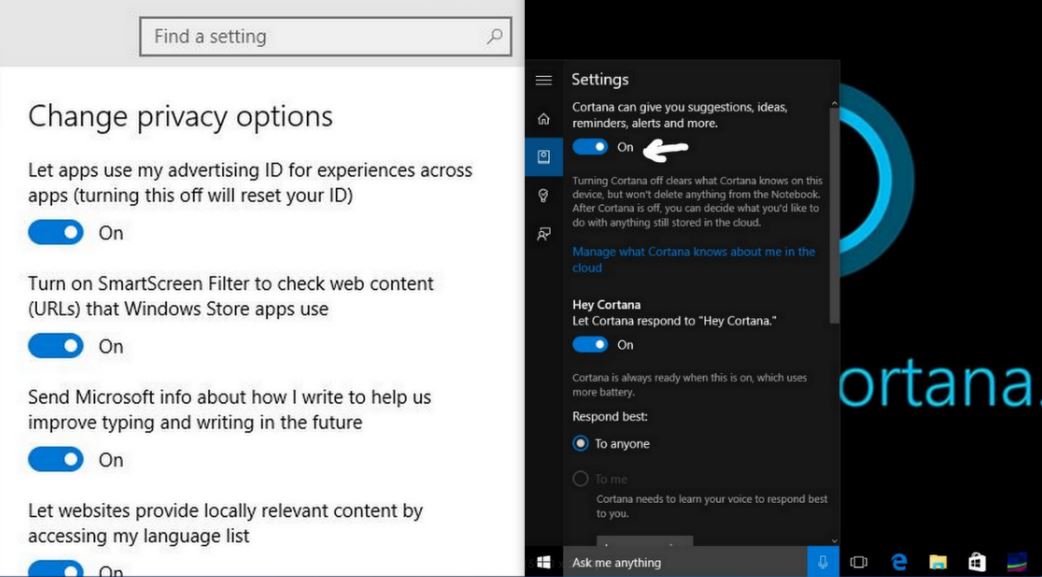
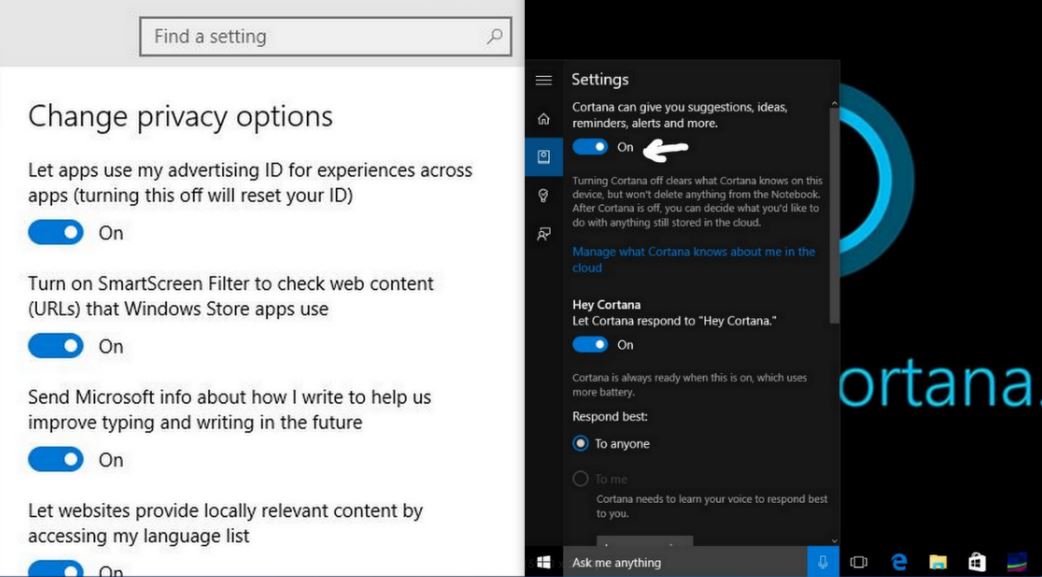
329How to Stop Windows 10 From Spying on You
Short Bytes : Windows 10 is released for all with lots of good features. On the other hand, its privacy policies are...
-

 350
350Top 5 Facebook Scams That You Should Be Aware Of
Short Bytes: Social media sites such as Facebook and their immense user base are prone to scams most of the times. Here’s...
-
 169
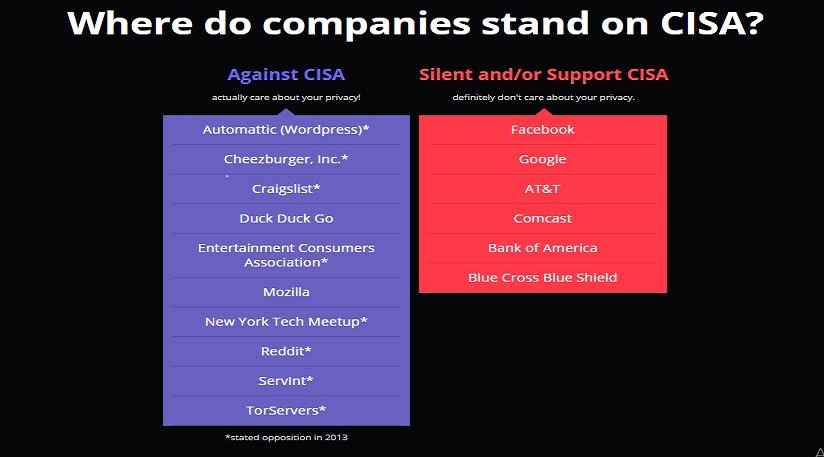
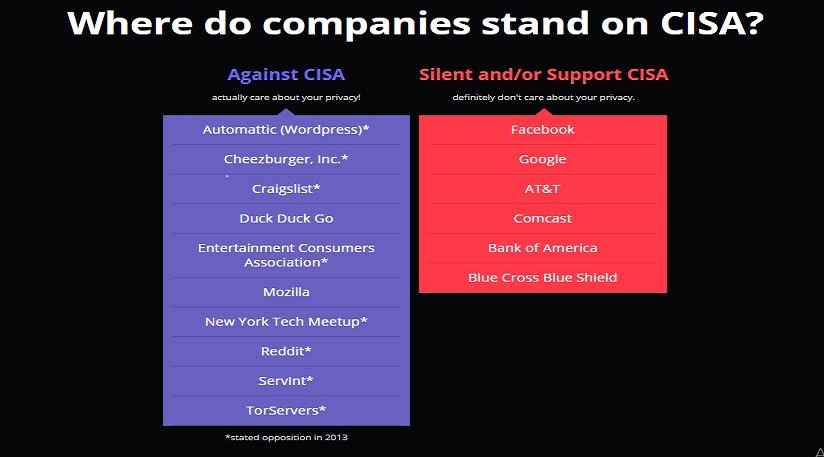
169CISA Bill To Give Your Entire Personal Info To Government
Short Bytes : The recently proposed Cybersecurity Information Sharing Act (CISA) by the government looks like another surveillance law that outrightly gives...
-
 322
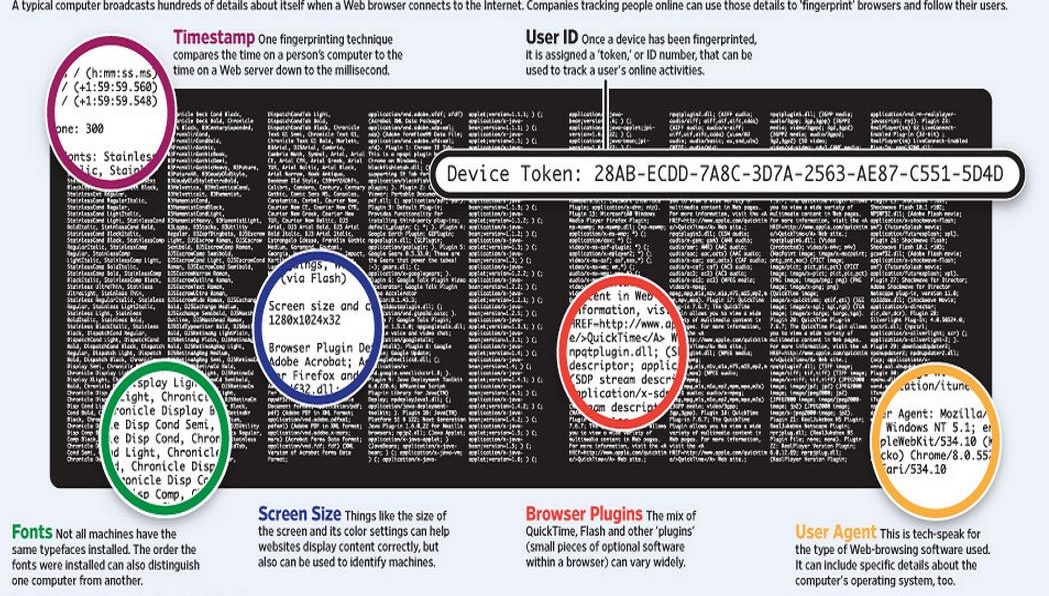
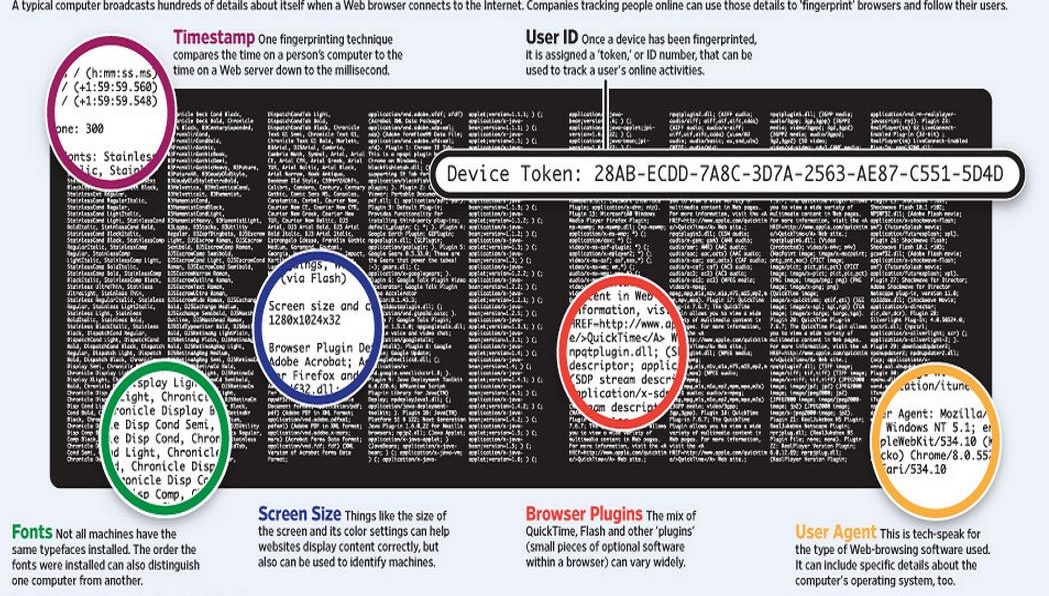
322What is Traffic Fingerprinting and How it is Used to Attack Tor Network
Short Bytes: Traffic fingerprinting is a technique used to sniff the web traffic by analyzing the data packets’ flow pattern- without removing...
-

 165
165Hackers Can Hack Smart Sniper Rifles Running on Linux And Change Its Target
Images: Wired Short Bytes : Security researchers have found a way to hack the Tracking Point sniper rifles. These “smart” snipers run...
-

 279
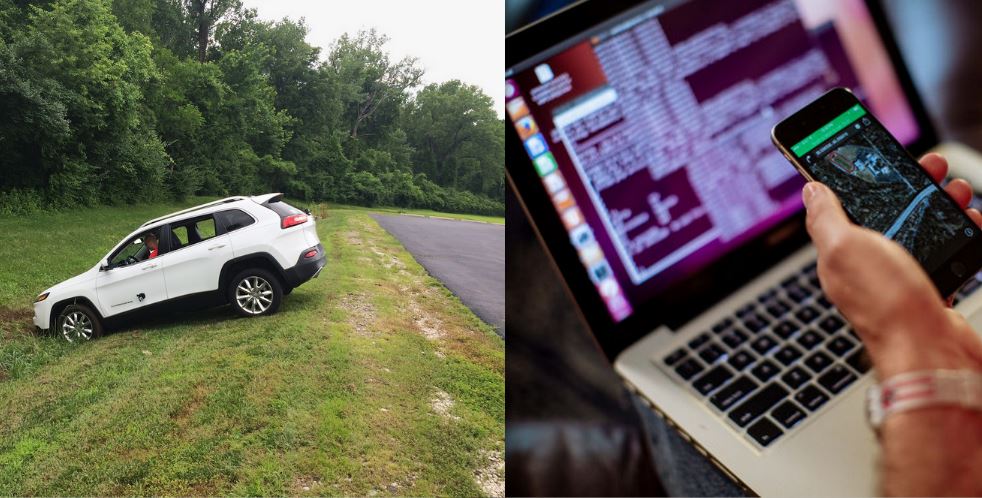
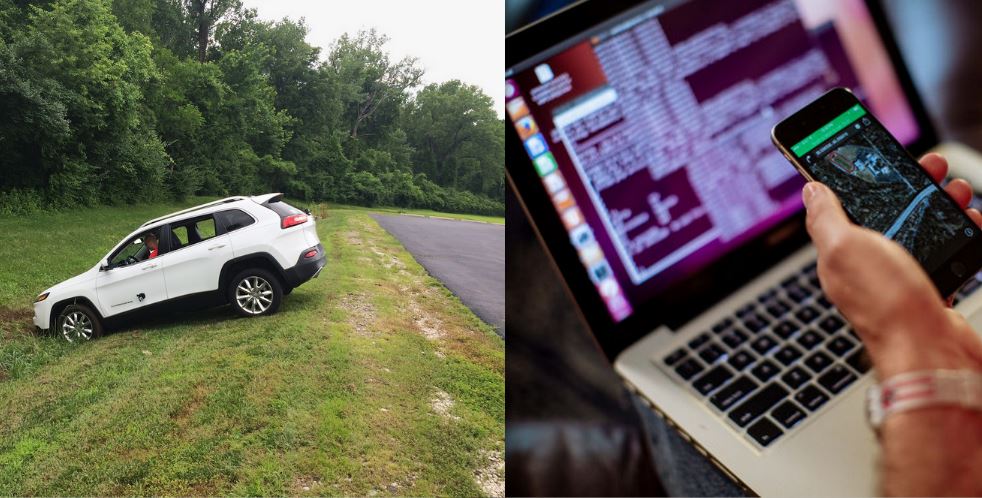
279Experts Explain The Car Hack Process – How to Hack a Car
Short Bytes : The recent Fiat Chrysler car hack exposed the vulnerabilities and the extent to which insecure IoT can be dangerous....
-

 184
1845 Best Free Android Antivirus Apps of 2015
Short Bytes : Your smartphone is at the equal risk of getting infected by malware as is your computer. Hers’s a list...
-
 335
335U.S. Government Wants to Send Edward Snowden to Prison, Rejects Pardon Request
(Credit: Reuters/Bobby Yip) Short Bytes : The White House has rejected a petition with more than 167,000 signatures to pardon whistleblower Edward...
-
 186
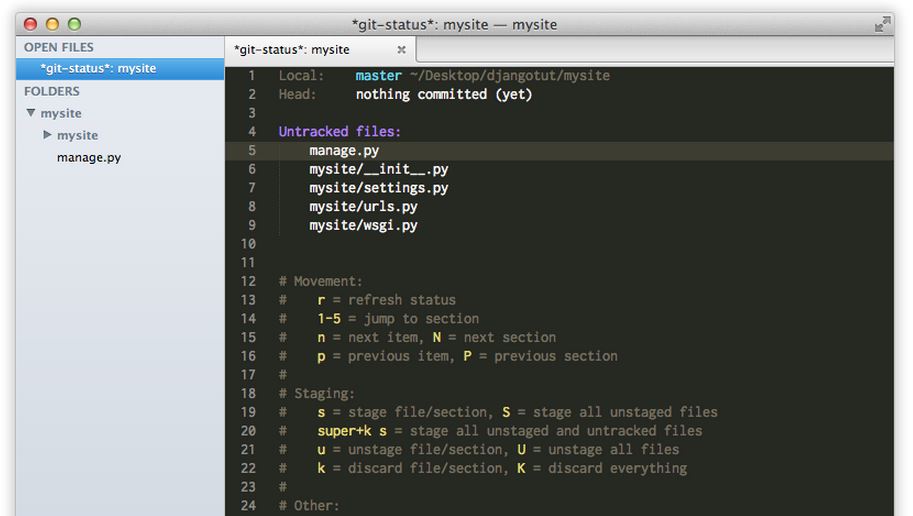
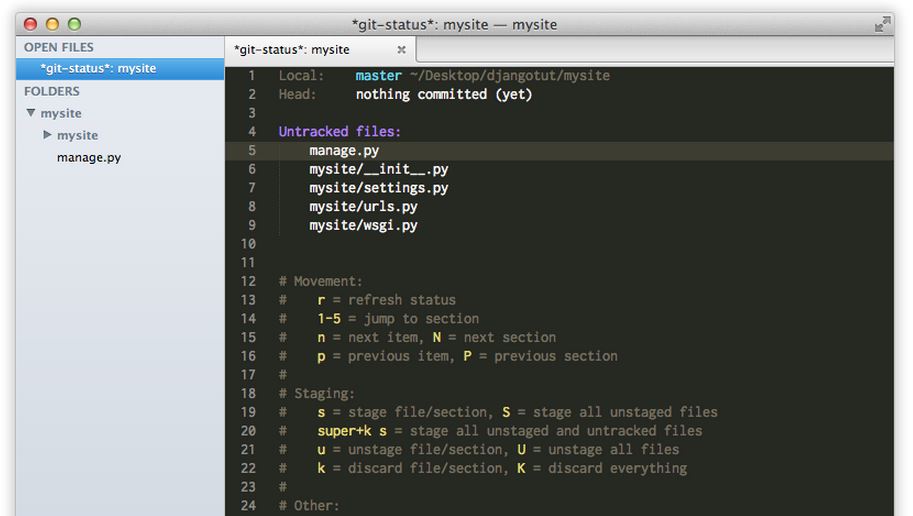
186One in Every 600 Websites Has .git Exposed, How to Check Yours and Hide It
Recently, I read about an innocent mistake committed often by web developers and thought it’d be nice to share it on fossBytes....
-

 279
279Google Tells You How To Stay Safe Online
When most of your Facebook timeline is flooded with news like cyber threats and security, how cyber criminals steal your money, and...
-

 187
187500 Million Devices at Risk Due to Leaked “Easy to Use” RCSAndroid Malware
The massive data breach at the Hacking Team has resulted in tons of revelations regarding different kinds of spyware and the potential security...
-
 317
317Movie Studios Repeatedly Report Their Own 127.0.0.1 Localhost for Piracy
The torrent pirates that keep hurting the million-dollar movie studios by uploading the data using their torrent clients are their biggest enemies...
-
 222
222How To Self Destruct Email With Dmail
Admit it, you have wanted this for a long time. There must have been instances when you regretted sending an email with...
-
 334
334HORNET: Tor-like Anonymity Network With Superfast Speeds
The Deep Web is a place that is hidden from the ordinary world because the browsers used to access the Deep Web, continuously encrypt...
-
 324
324Edward Snowden Tells How to Build an Internet Focused on Privacy
When someone like Edward Snowden, tells you how to make an internet focused on privacy and user welfare, you listen, and you...
-
 281
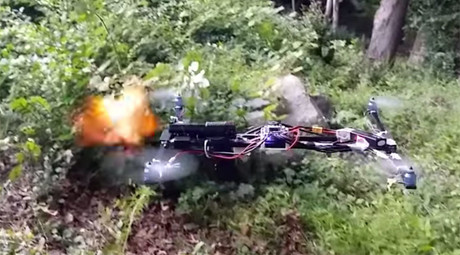
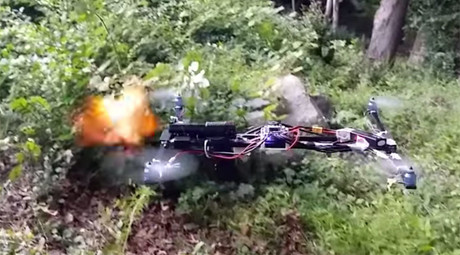
281Gun Firing Drone Appears Legal, FAA Still Investigating
Remember the Drone Gun? The quadcopter hovering in the woods of Clinton, Connecticut and firing rounds of shots and completely legal...
-
 189
189Hackers Remotely Hacked This Car Running at 70mph on Highway
As our vehicles become smarter and more dependent on computers, the risk of a car hack automatically increases. Articles titled how to...
-
 194
194Download this Critical Windows Update Now, Flaw Allows Hackers to Control Entire System
A newly discovered vulnerability can allow hackers to remotely execute codes and take over your entire system. A user could be tricked...
-

 187
187Instagram Can Totally Hijack Your Account And Give To Some Celebrity
How cool would it be if somehow your parents were Pitt’s and ended up to name you Brad, or a simple Messi...






