Exploitation
-

 357
357Router Exploit Shovel – Automated Application Generation for Stack Overflow Types on Wireless Routers
Router exploit shovel is an automated application generation tool for stack overflow types on wireless routers. The tool implements the key functions...
-
 410
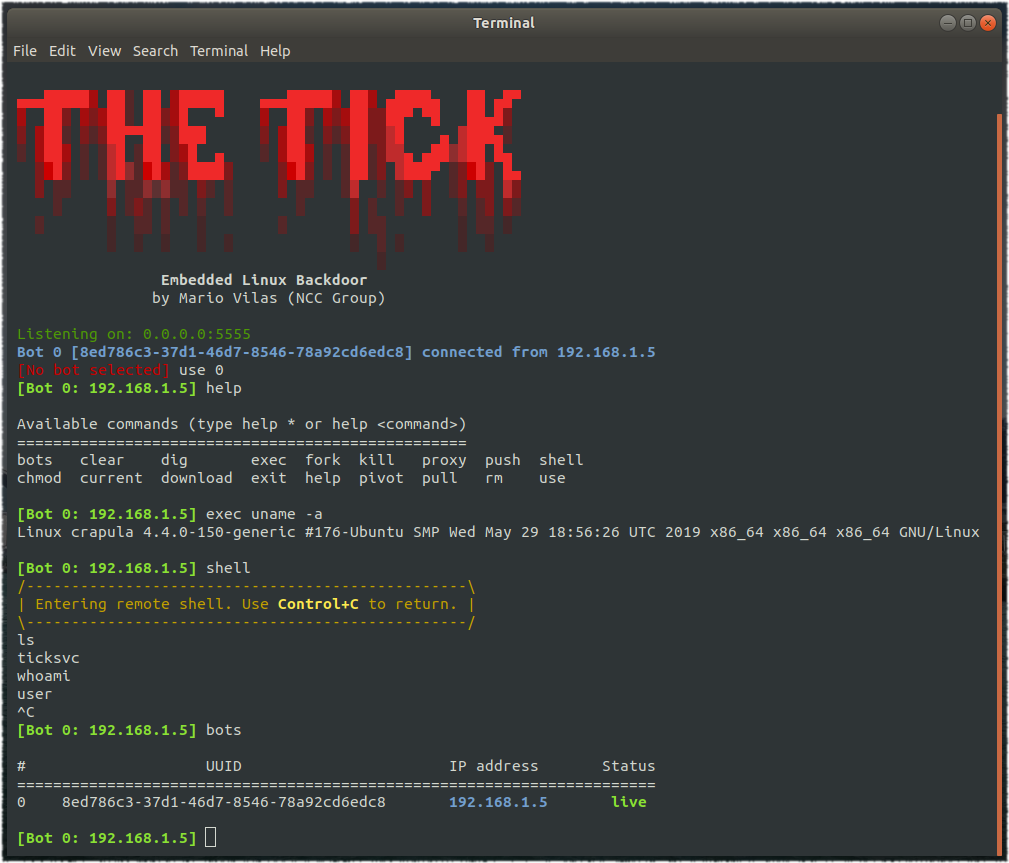
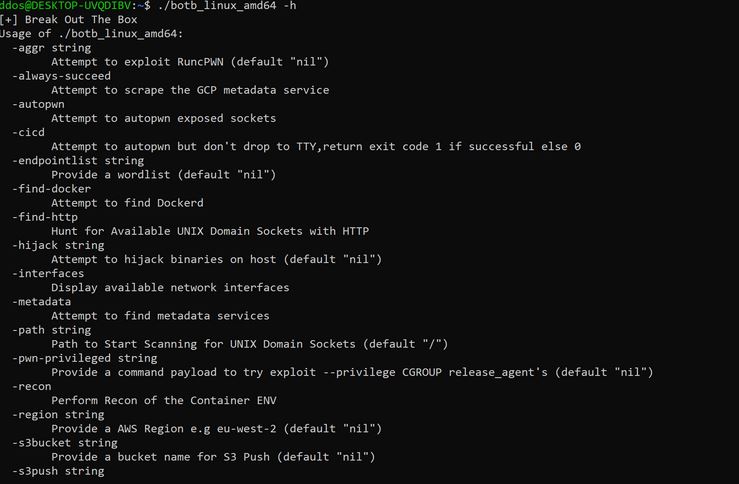
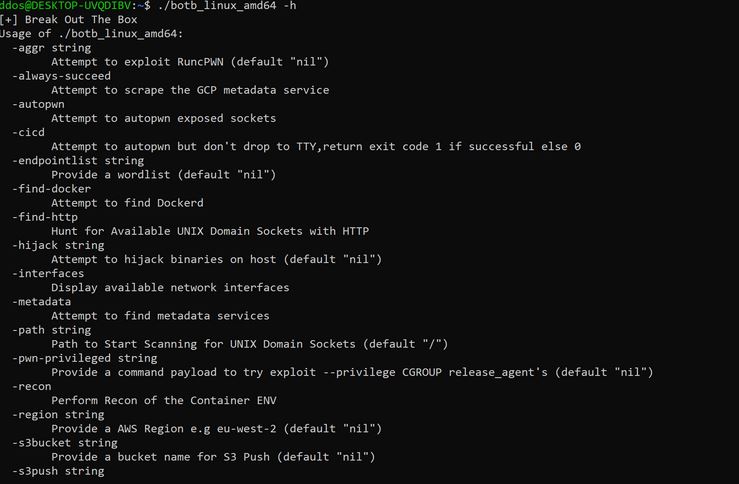
410BotB – A container analysis and exploitation tool for pentesters and engineers.
BOtB (Break out the Box) is a container analysis and exploitation tool designed to be used by pentesters and engineers while also...
-
 528
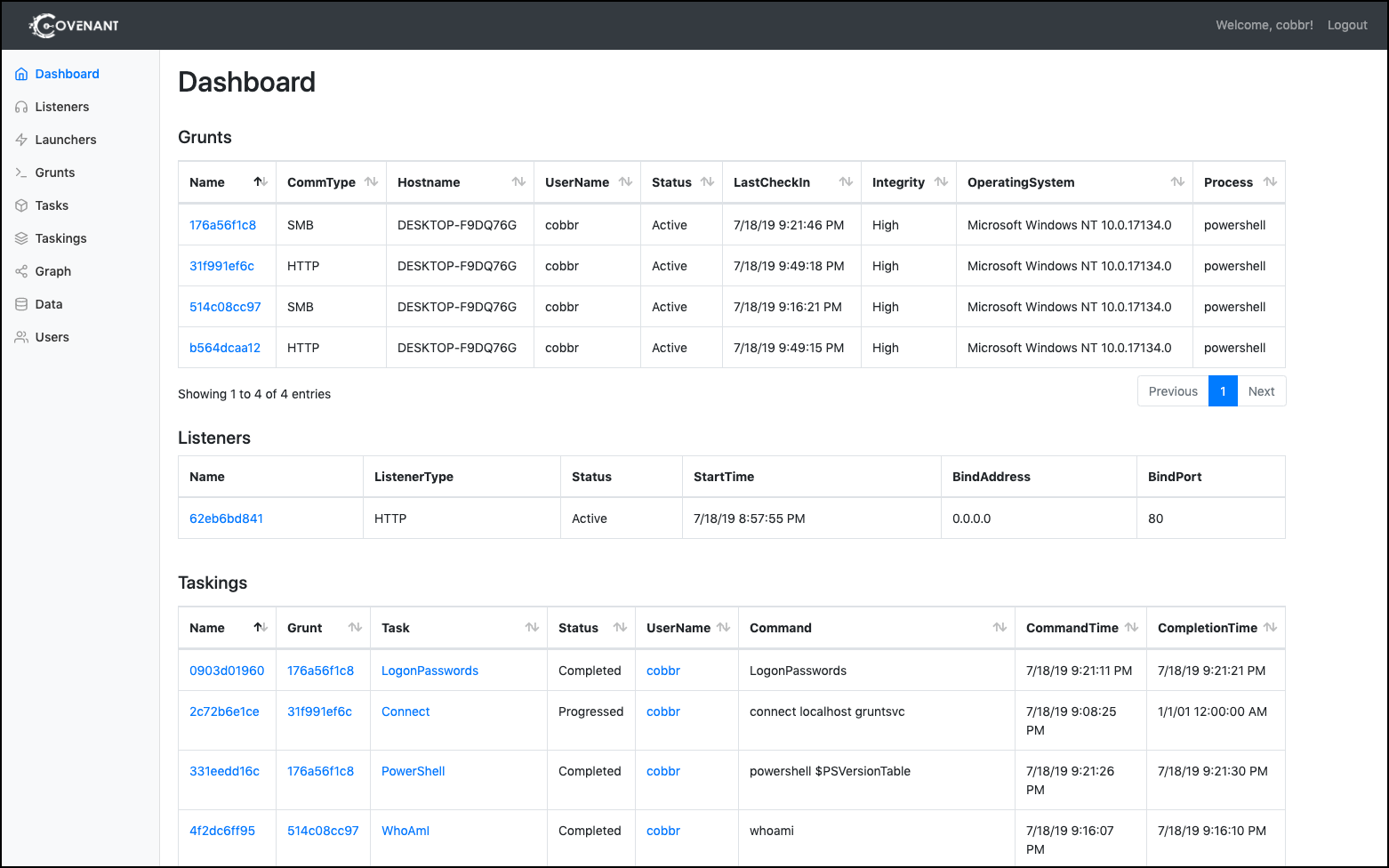
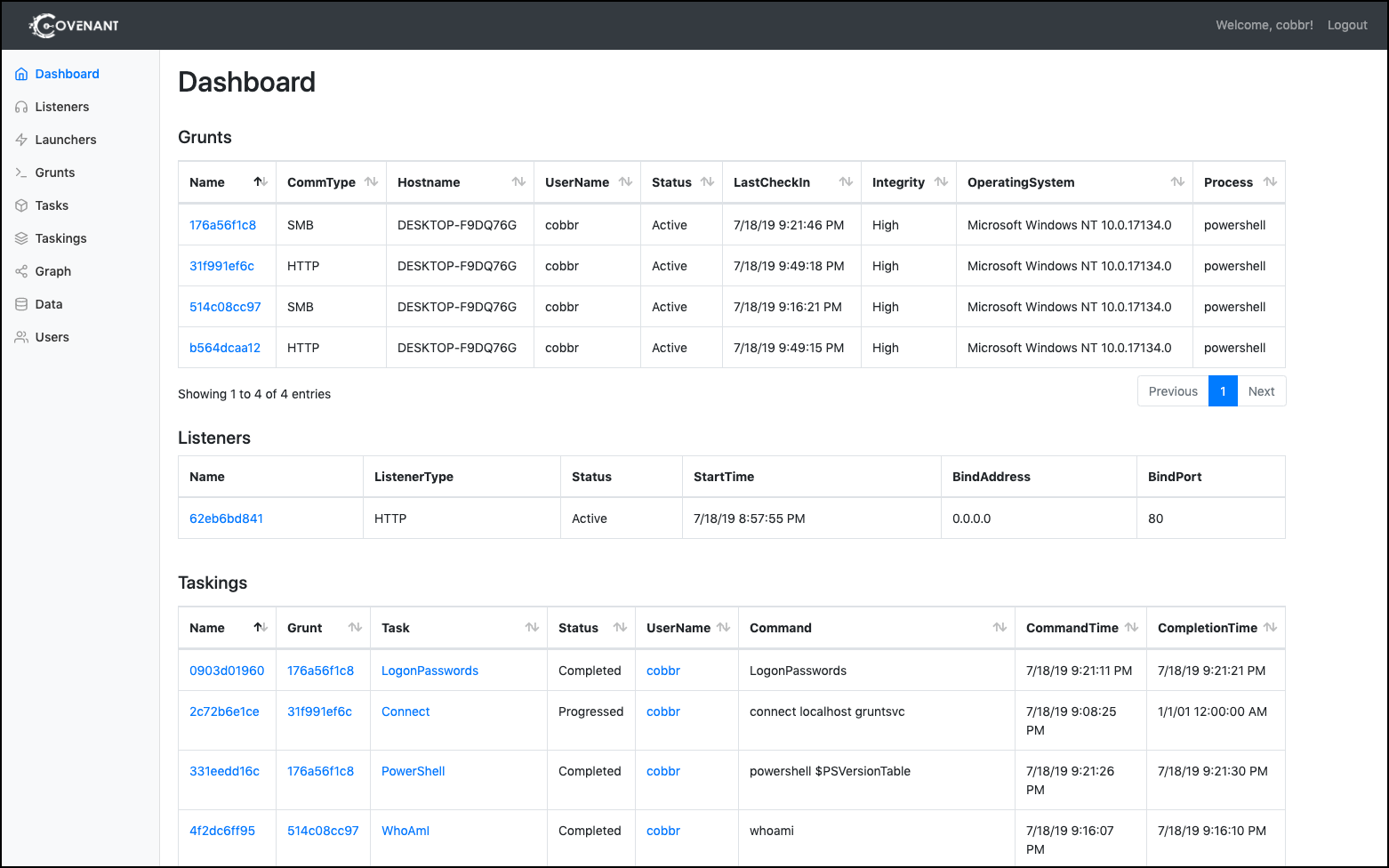
528Covenant – Offensive .NET Collaborative C&C Platform for Red Teamers.
Covenant is a .NET command and control framework that aims to highlight the attack surface of .NET, make the use of offensive...
-

 532
532Hacktronian – All In One Hacking Tool For Linux & Android
Pentesing Tools That All Hacker Needs, Hacktronian is an all in one hacking toolkit. HACKTRONIAN Menu : Information Gathering Password Attacks Wireless...
-
 266
266Theo – Ethereum Recon and Exploitation Tool
Theo aims to be an exploitation framework and a blockchain recon and interaction tool. Features: Automatic smart contract scanning which generates a...
-
 525
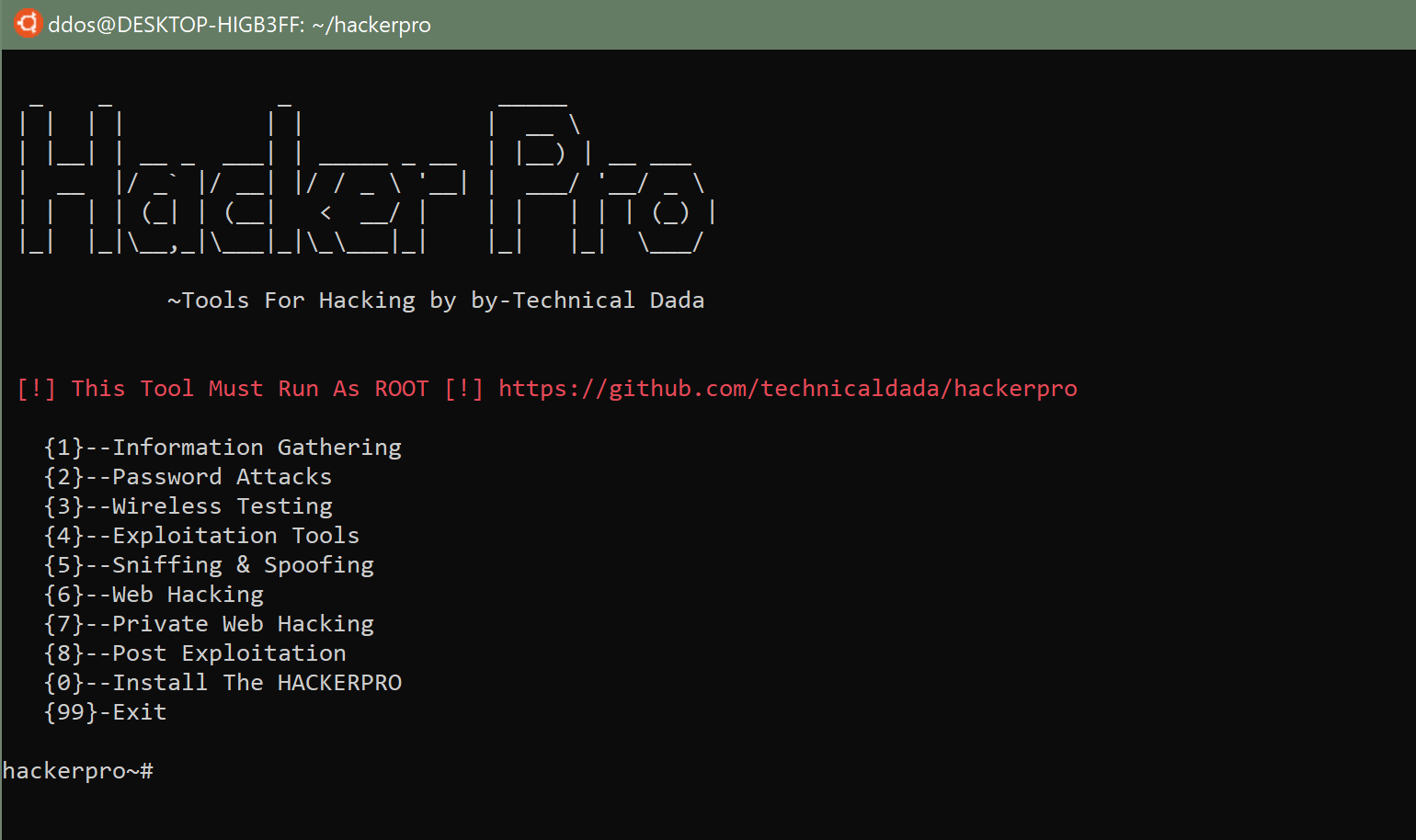
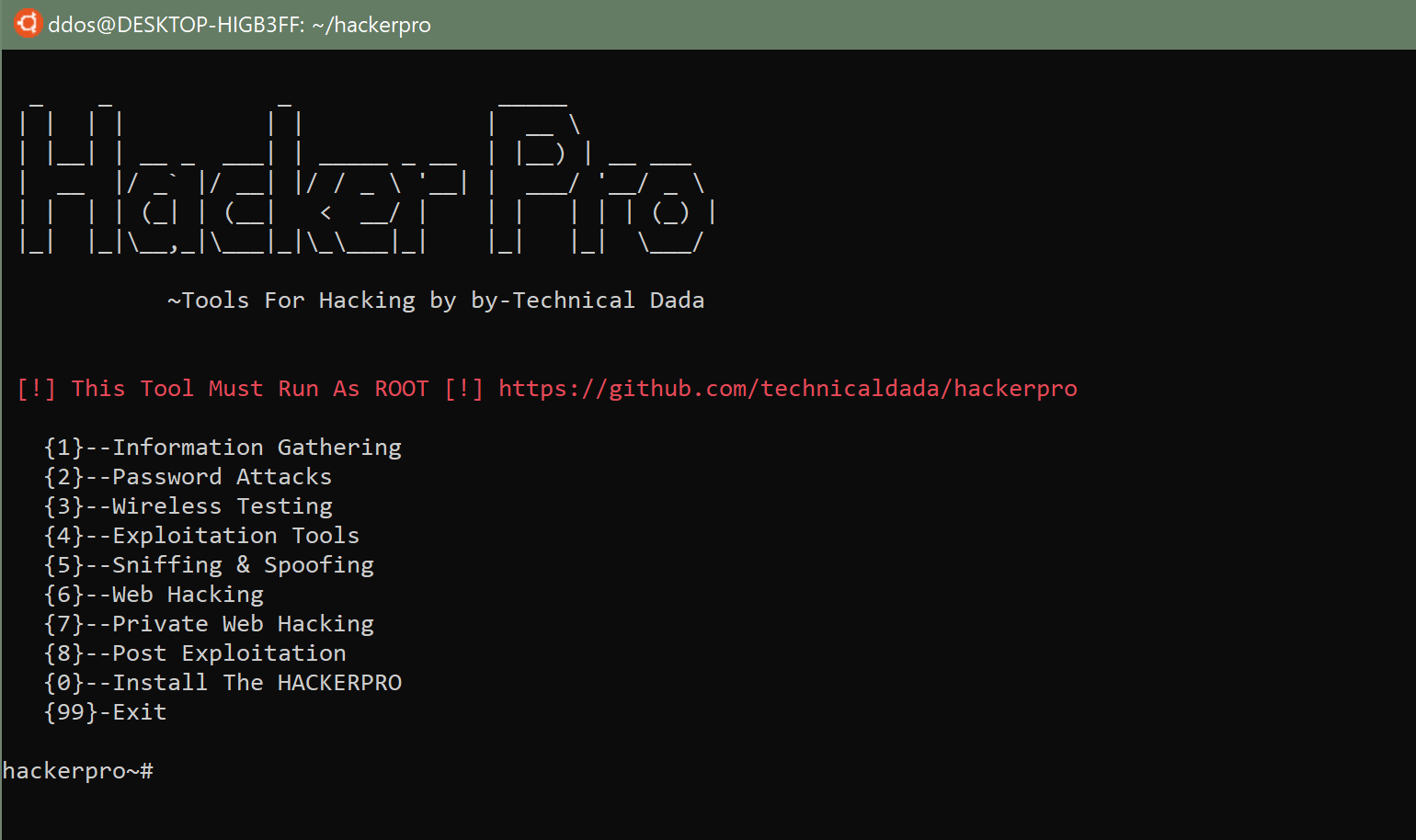
525HackerPro: All in One Hacking Tool for Linux & Android
All in One Hacking Tool for Linux & Android (Termux). HACKERPRO Menu : Information Gathering Password Attacks Wireless Testing Exploitation Tools Sniffing...
-
 295
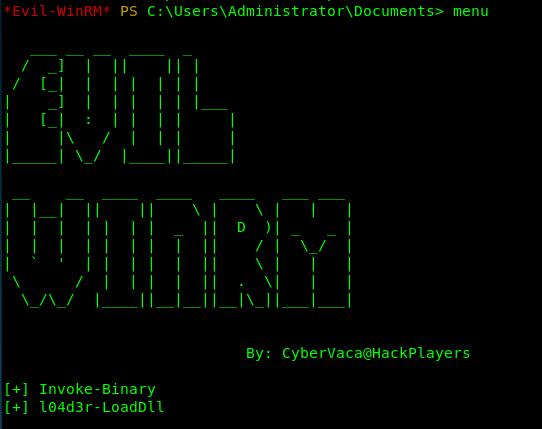
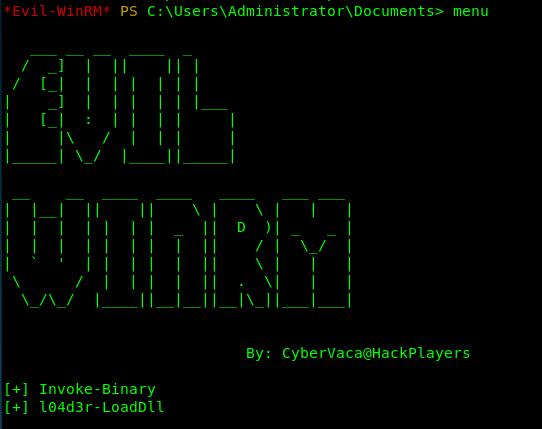
295EvilWinRM – The Ultimate WinRM Shell for Pentesting
WinRM (Windows Remote Management) is the Microsoft implementation of WS-Management Protocol. A standard SOAP based protocol that allows hardware and operating systems...
-
 333
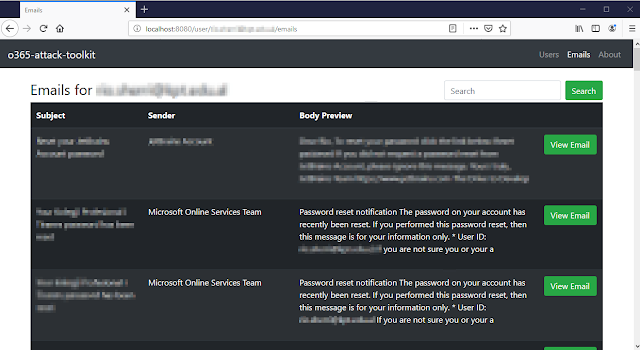
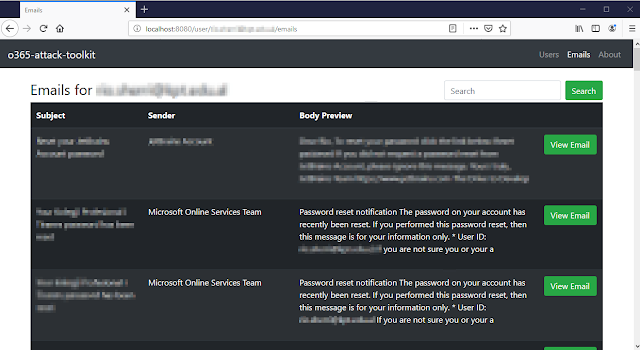
333O365 Attack Toolkit – A Toolkit to Attack Office365
o365-attack-toolkit allows operators to perform an OAuth phishing attack and later on use the Microsoft Graph API to extract interesting information. Some...
-
 369
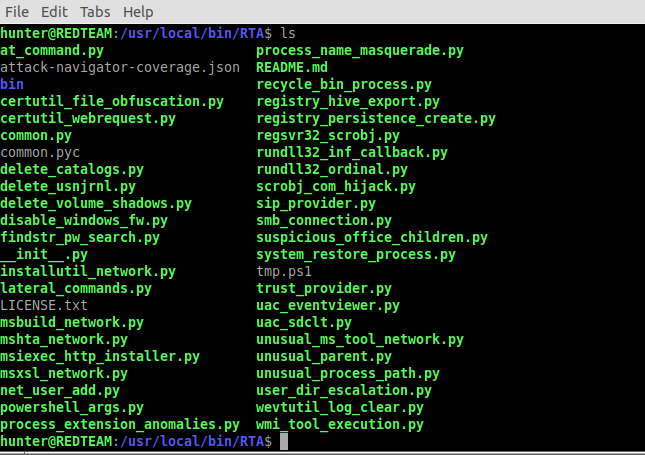
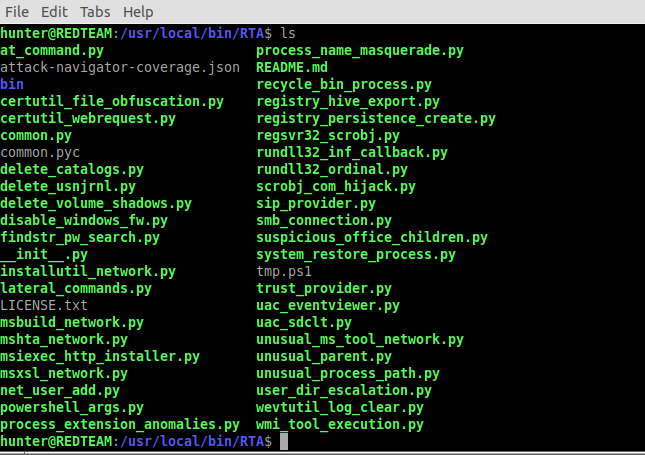
369Endgame Red Team Automation (RTA) Framework
Red Team Automation (RTA) provides a framework of scripts designed to allow blue teams to test their detection capabilities against malicious tradecraft,...
-
 362
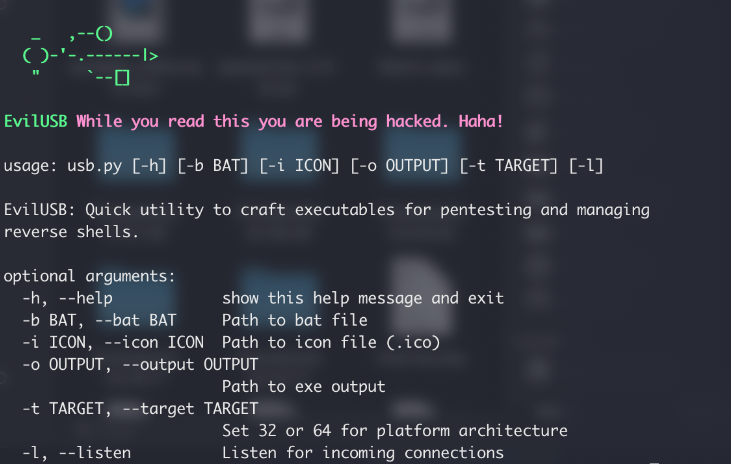
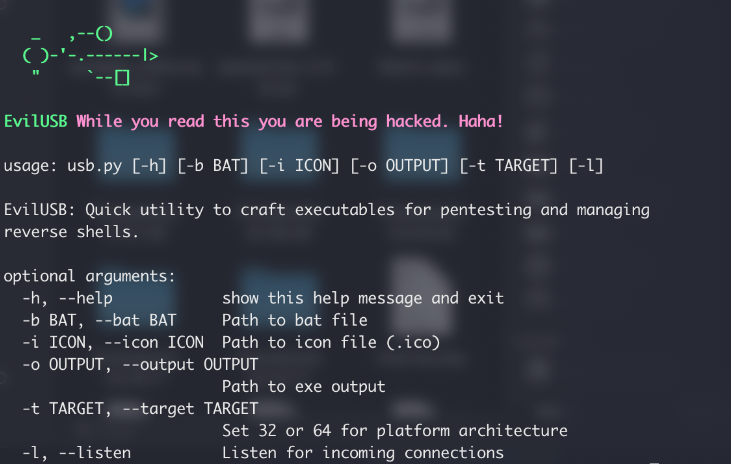
362EvilUSB – Quick Utility to Craft Executables for Pentesting & Managing Reverse Shells
Quick utility to craft executables for pentesting and managing reverse shells. Instructions Requires Python 3.5 or above. usage: usb.py [-h] [-b BAT]...
-
 254
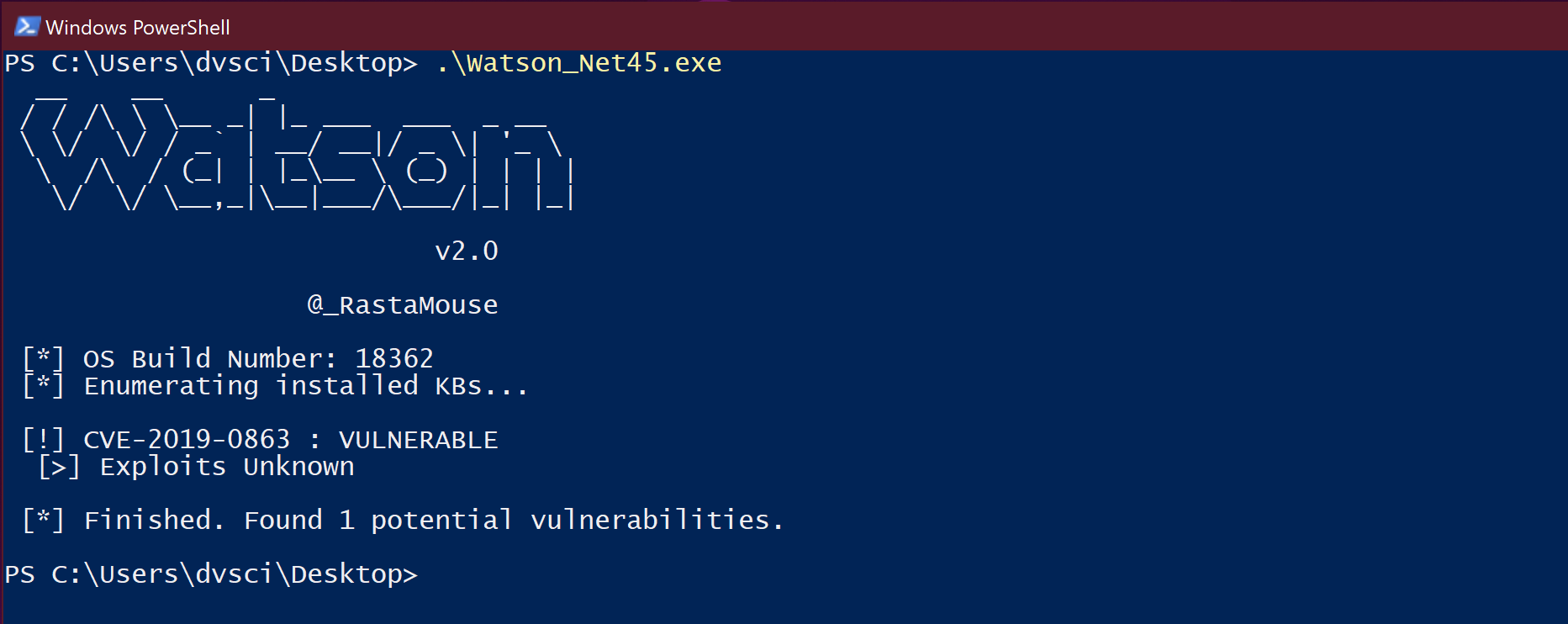
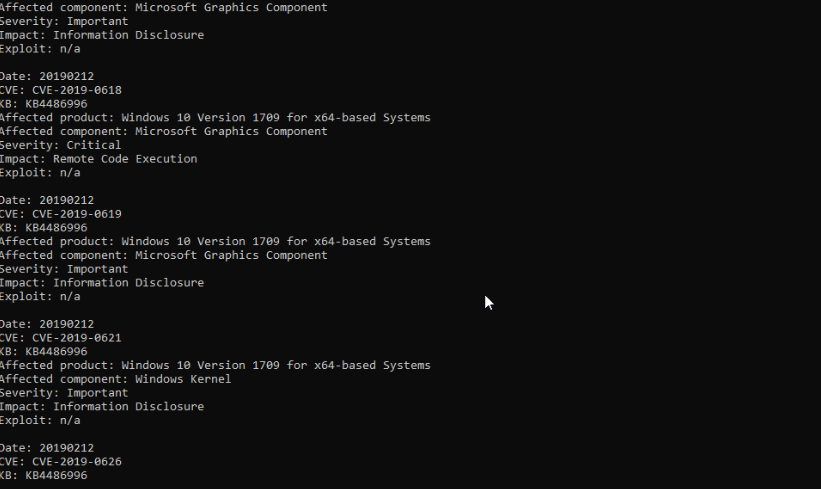
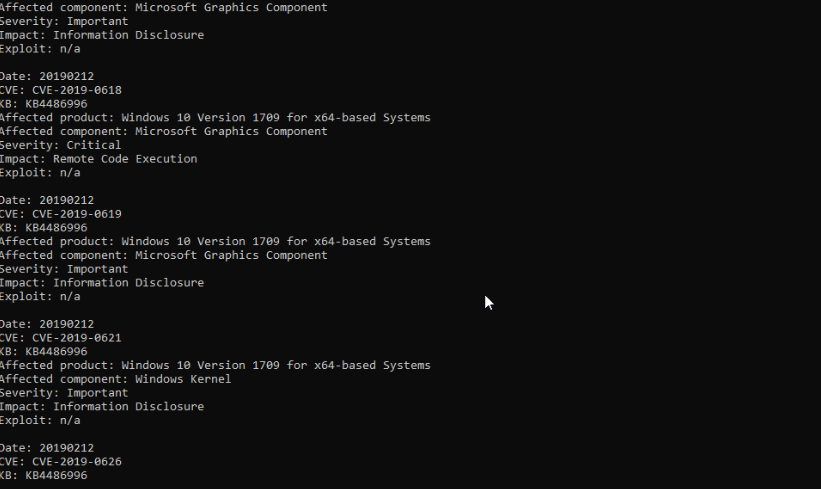
254WES-NG: Windows Exploit Suggestor
WES-NG is a tool based on the output of Windows’ systeminfo utility which provides the list of vulnerabilities the OS is vulnerable...
-
 318
318PRET – Hacking Printer Command Languages
PRET is a new tool for printer security testing developed in the scope of a Master’s Thesis at Ruhr University Bochum. It...
-
 316
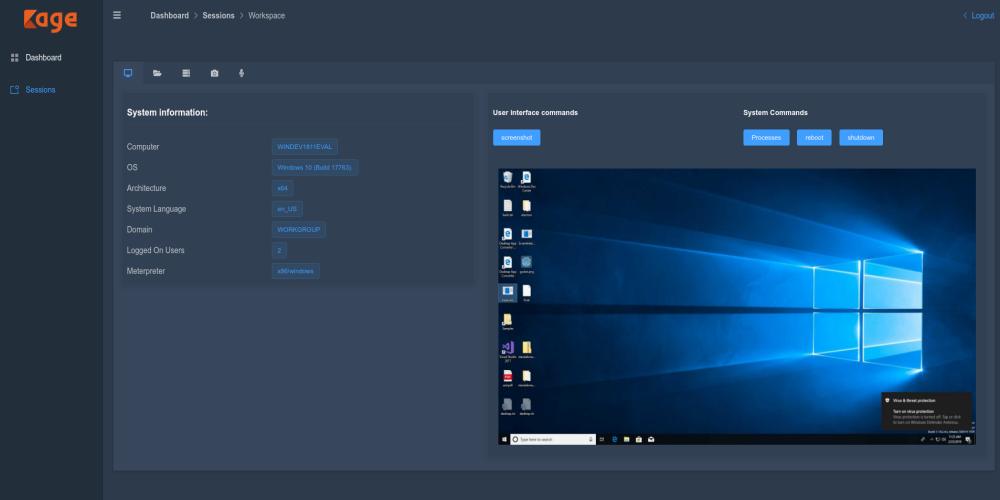
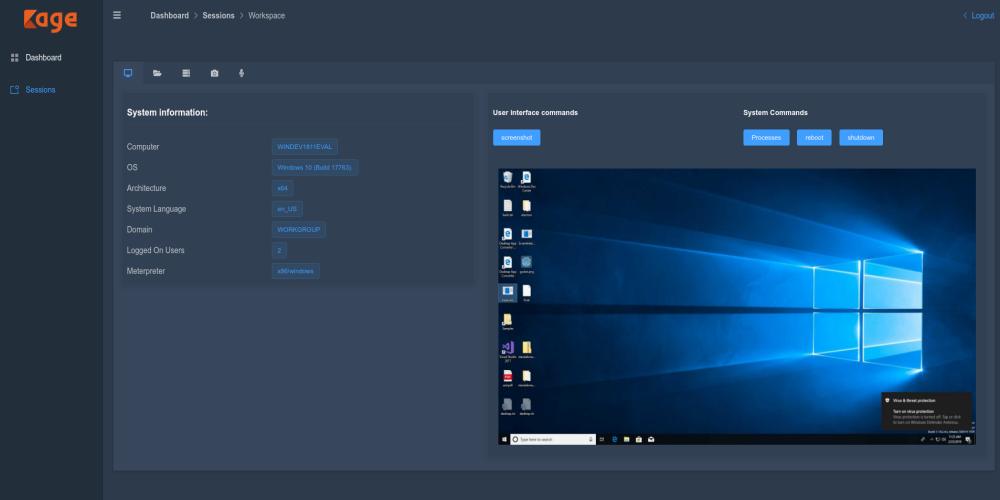
316Graphical User Interface for Metasploit Meterpreter and Session Handler: Kage
Kage (ka-geh) is a tool inspired by AhMyth designed for Metasploit RPC Server to interact with meterpreter sessions and generate payloads. For...
-
 287
287Arecibo – Endpoint for Out-of-Band Exfiltration
In the process of identifying and exploiting vulnerabilities, it is sometimes necessary to resort to Out of Band (OOB) techniques in order...
-
 280
280SILENTTRINITY – A Post-Exploitation Agent Powered By Python, IronPython, C#/.NET
A post-exploitation agent powered by Python, IronPython, C#/.NET. Requirements Server requires Python >= 3.7 SILENTTRINITY C# implant requires .NET >= 4.5 How...
-
 211
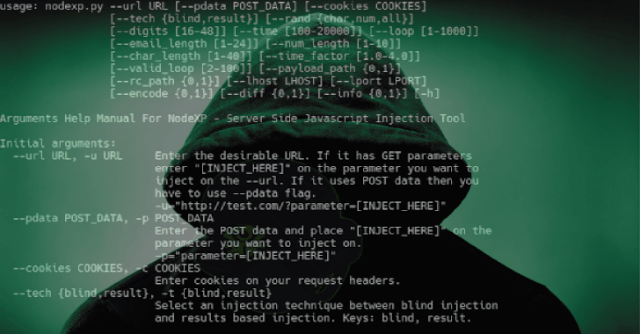
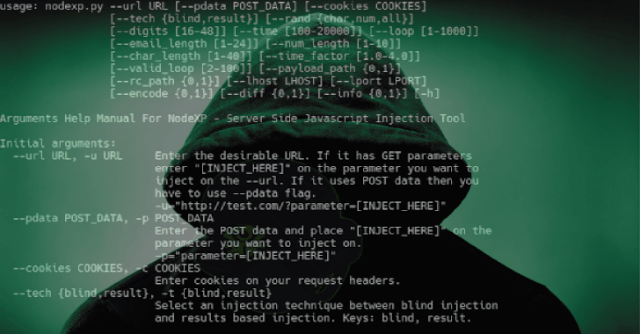
211Nodexp – A Server Side Javascript Injection Tool
NodeXP is an intergrated tool, written in Python 2.7, capable of detecting possible vulnerabilities on Node.js services as well as exploiting them...
-
 283
283SharpSploit – A .NET Post-Exploitation Library Written in C#
SharpSploit is a .NET post-exploitation library written in C# that aims to highlight the attack surface of .NET and make the use...