Hack Tools
-
 4.8K
4.8KFunctrace – A Function Tracer
functrace is a tool that helps to analyze a binary file with dynamic instrumentation using DynamoRIO (http://dynamorio.org/).These are some implemented features (based...
-
 1.2K
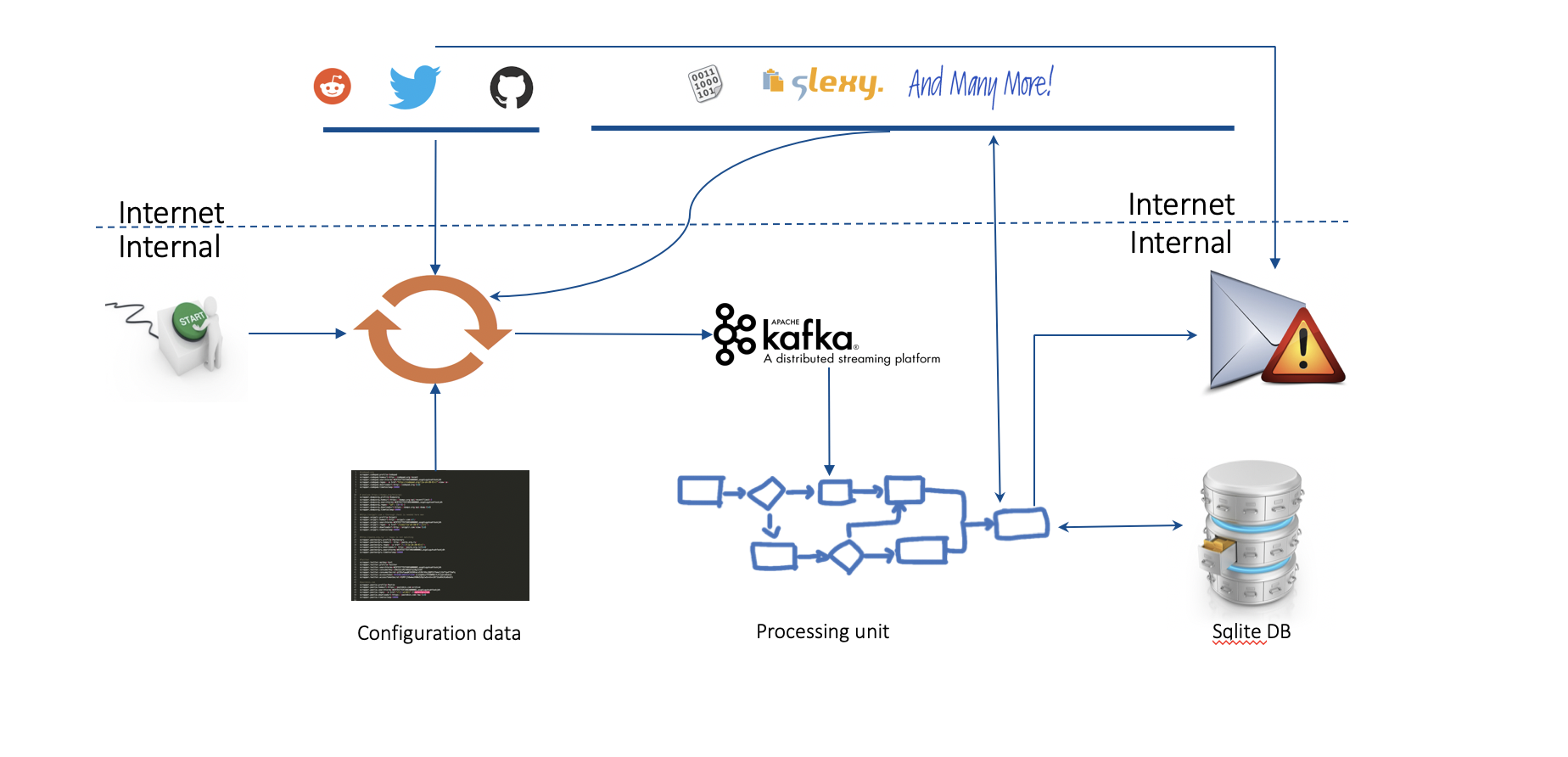
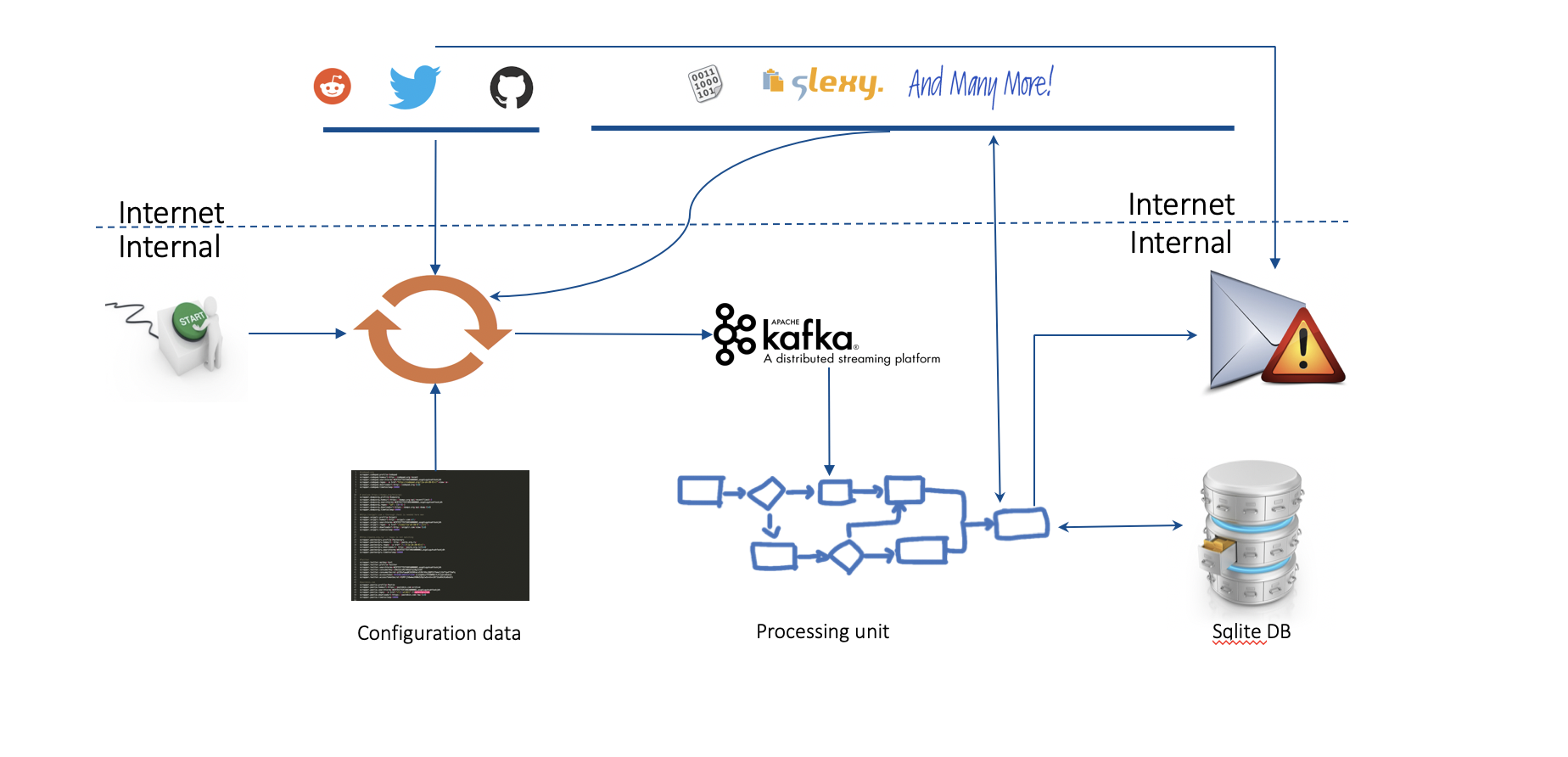
1.2K[BlackHat Europe tool] Real Time Threat Monitoring Tool
Real Time Threat Monitoring Tool V2.0 Monitoring possible threats of your company on the Internet is an impossible task to be achieved...
-

 3.7K
3.7KApk-Mitm – A CLI Application That Prepares Android APK Files For HTTPS Inspection
A CLI application that automatically prepares Android APK files for HTTPS inspection Inspecting a mobile app’s HTTPS traffic using a proxy is...
-
 4.0K
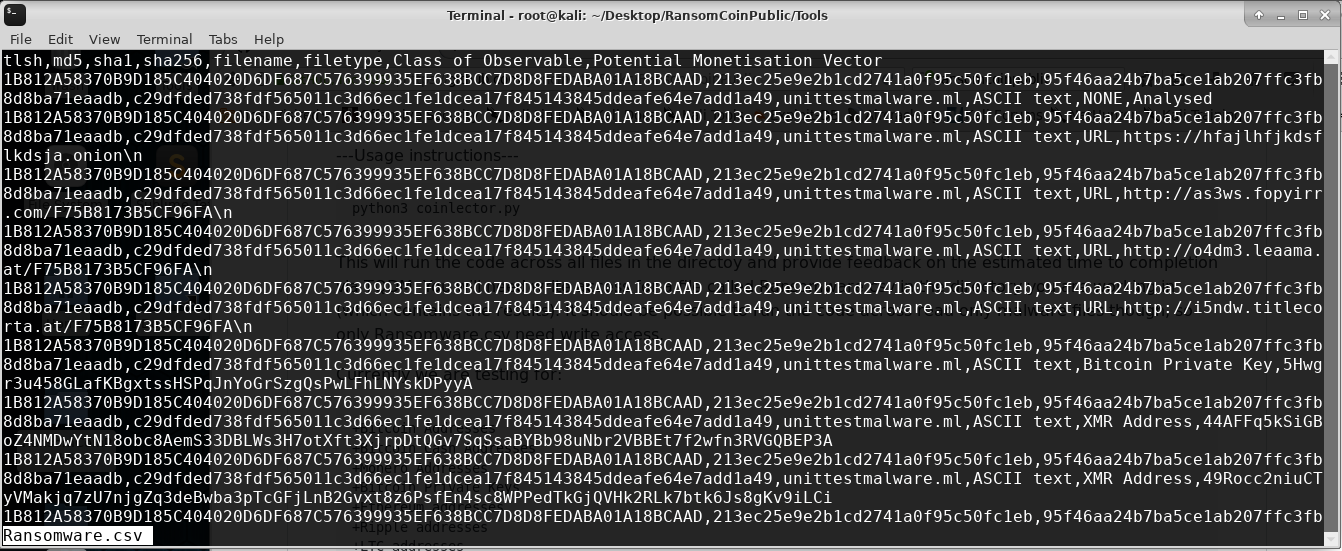
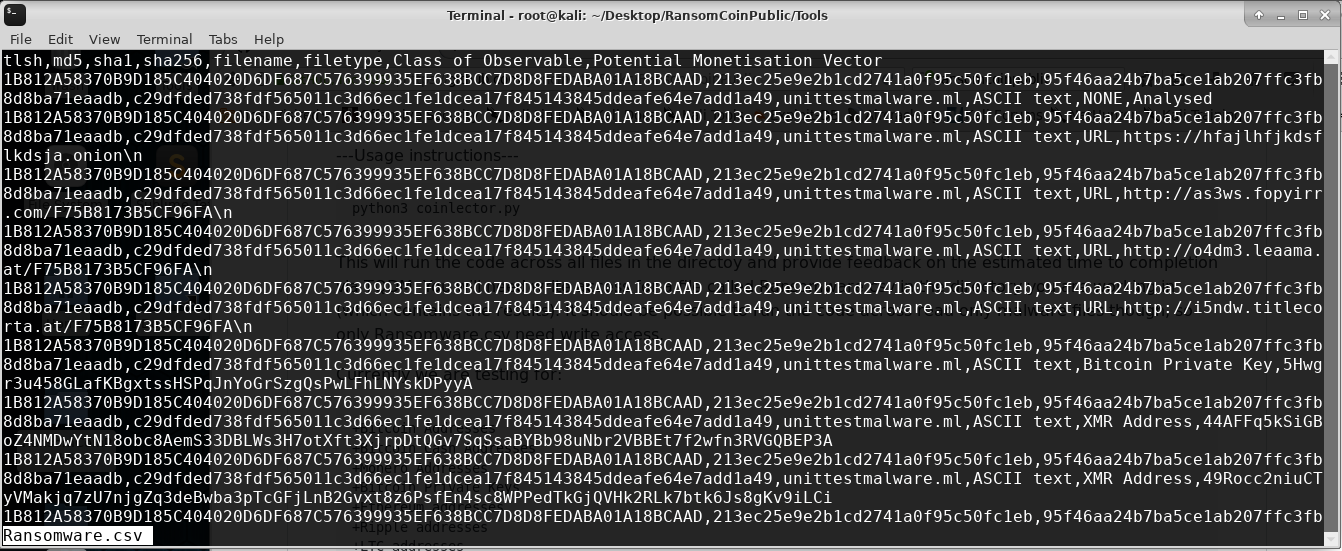
4.0K[Blackhat Europe tool] RansomCoin: extract cryptocoin addresses and other indicators of compromise from binaries
RansomCoin Extracting metadata and hardcoded Indicators of Compromise from ransomware, in a scalable, efficient, way with cuckoo integrations. Ideally, is it run...
-
 4.5K
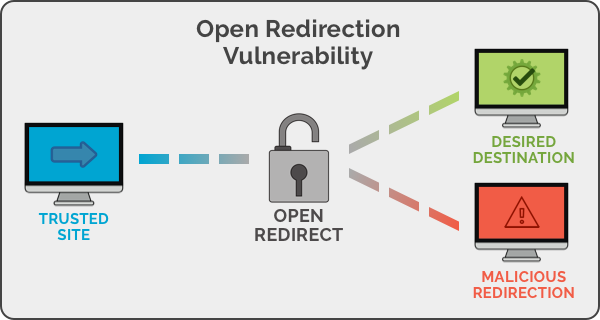
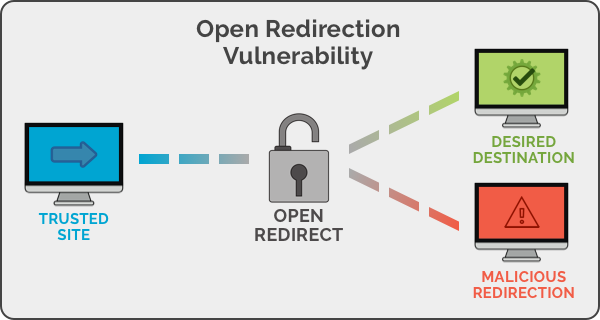
4.5KOpen Redirect Payload List
Unvalidated redirects and forwards are possible when a web application accepts untrusted input that could cause the web application to redirect the...
-
 4.2K
4.2KWhat is the CyberSec Feature?
With each passing year, cybersecurity concerns increase in terms of the number of threats and their severity. Hackers can and will cause...
-

 1.7K
1.7KAntiDisposmail – Detecting Disposable Email Addresses
Antbot.pw provides a free, open API endpoint for checking a domain or email address against a frequently-updated list of disposable domains. CORS...
-
 2.4K
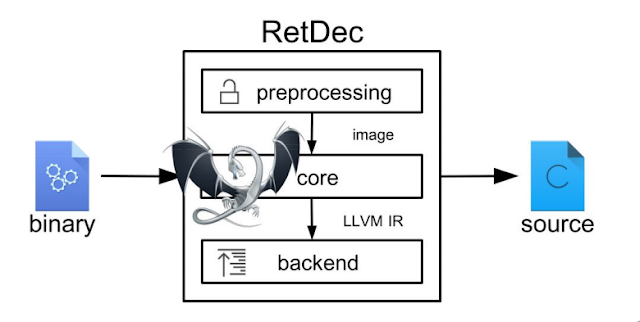
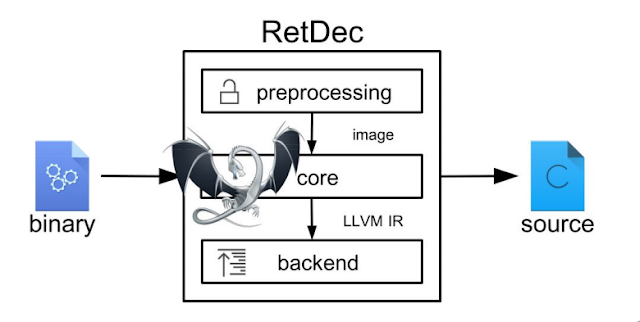
2.4KRetDec – A Retargetable Machine-Code Decompiler Based On LLVM
RetDec is a retargetable machine-code decompiler based on LLVM.The decompiler is not limited to any particular target architecture, operating system, or executable...
-

 2.1K
2.1KSeeker v1.2.1 – Accurately Locate Smartphones Using Social Engineering
Concept behind Seeker is simple, just like we host phishing pages to get credentials why not host a fake page that requests...
-
 3.4K
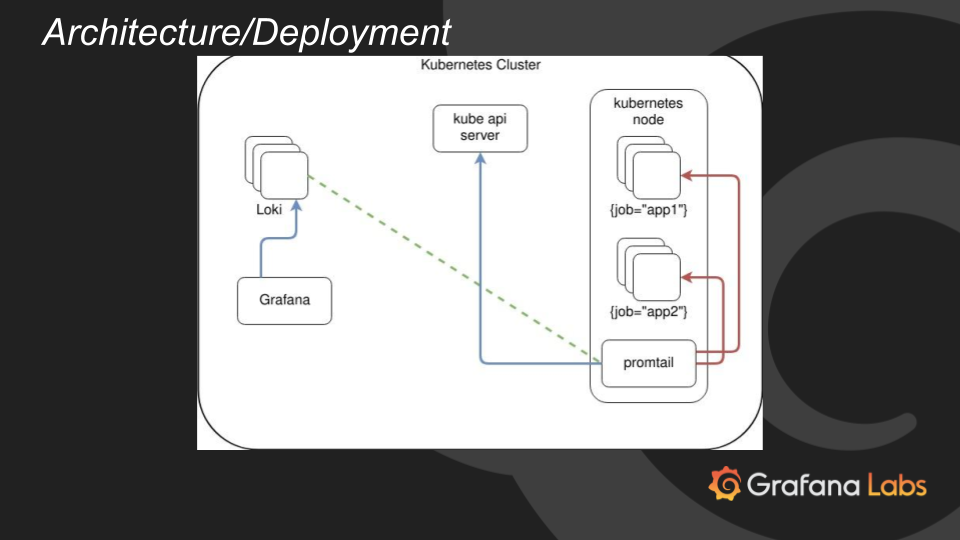
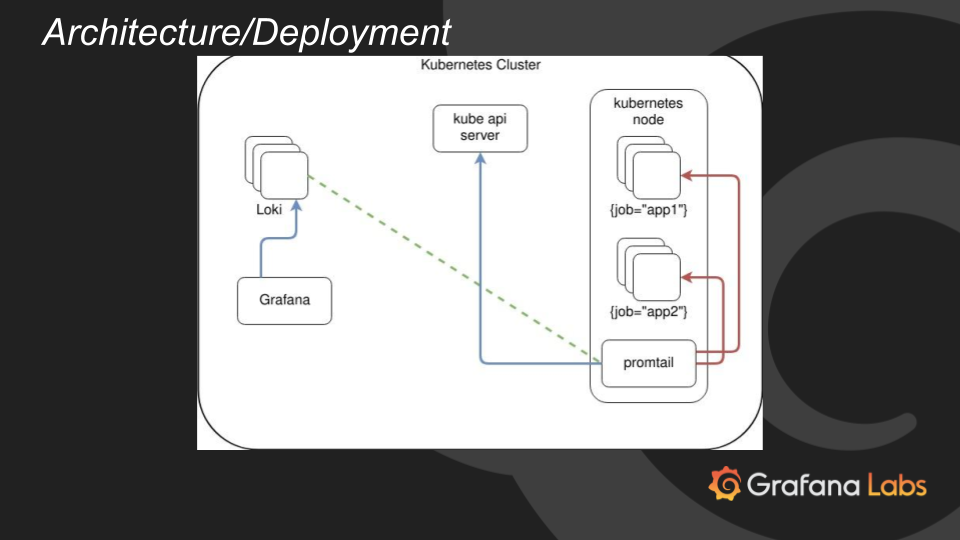
3.4KLoki v1.1 releases: horizontally-scalable, highly-available, multi-tenant log aggregation system
Loki: like Prometheus, but for logs. Loki is a horizontally-scalable, highly-available, multi-tenant log aggregation system inspired by Prometheus. It is designed to be...
-

 3.5K
3.5KCORStest – A Simple CORS Misconfiguration Scanner
A simple CORS misconfiguration scannerBased on the research of James KettleCORStest is a quick & dirty Python 2 tool to find Cross-Origin...
-

 4.5K
4.5Kad-password-protection: password protection for Active Directory
Lithnet Password Protection for Active Directory (LPP) enhances the options available to an organization wanting to ensure that all their Active Directory...
-
 4.0K
4.0KSharpHide – Tool To Create Hidden Registry Keys
Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null terminated) registry key. This...
-
 2.3K
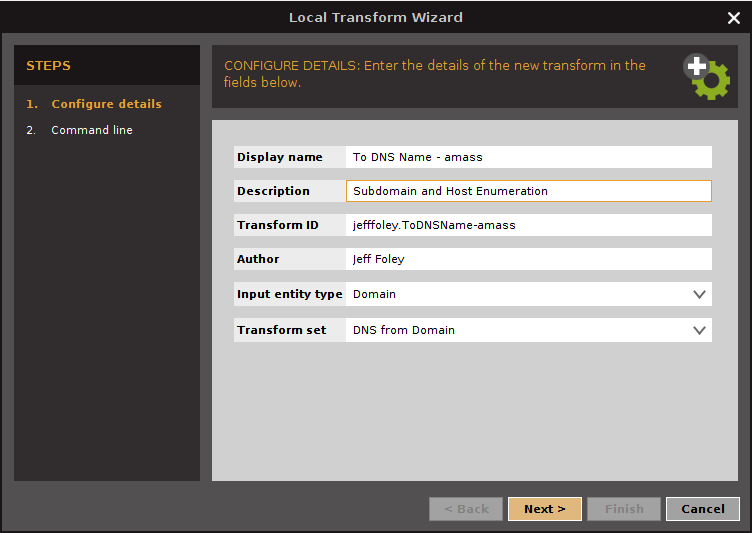
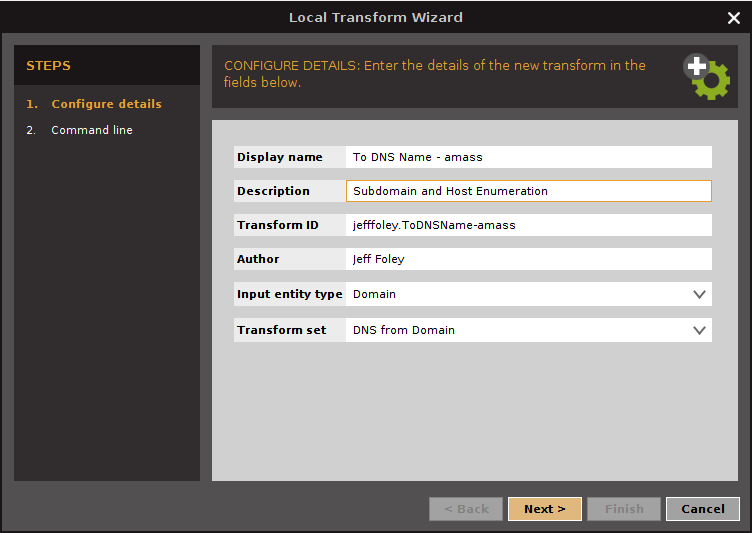
2.3Kamass v3.4.1 releases: In-depth subdomain enumeration written in Go
The OWASP Amass tool suite obtains subdomain names by scraping data sources, recursive brute forcing, crawling web archives, permuting/altering names and reverse...
-
 1.0K
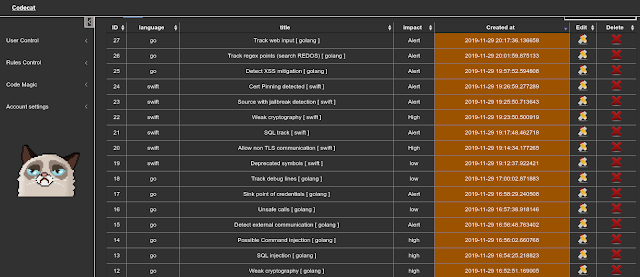
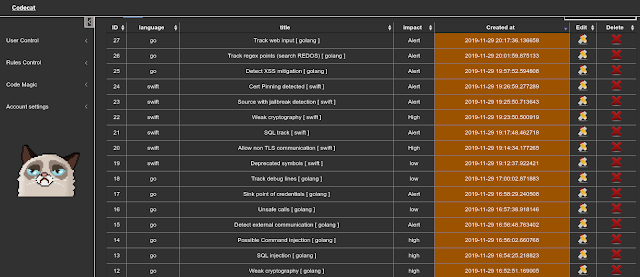
1.0KCodecat – Tool To Help In Manual Analysis In Codereview
CodeCat is a open source tool to help you in codereview, to find/track sinks and this points follow regex rules…How too install,...
-
 3.4K
3.4K“Cybersecurity: The Beginner’s Guide ($29.99 Value) FREE For a Limited Time”
Cybersecurity: The Beginner’s Guide It’s not a secret that there is a huge talent gap in the cybersecurity industry. Everyone is talking...
-

 2.7K
2.7KLinuxCheck – Linux Information Collection Script
A small linux information collection script is mainly used for emergency response. It can be used under Debian or Centos.Features CPU TOP10,...
-
 2.1K
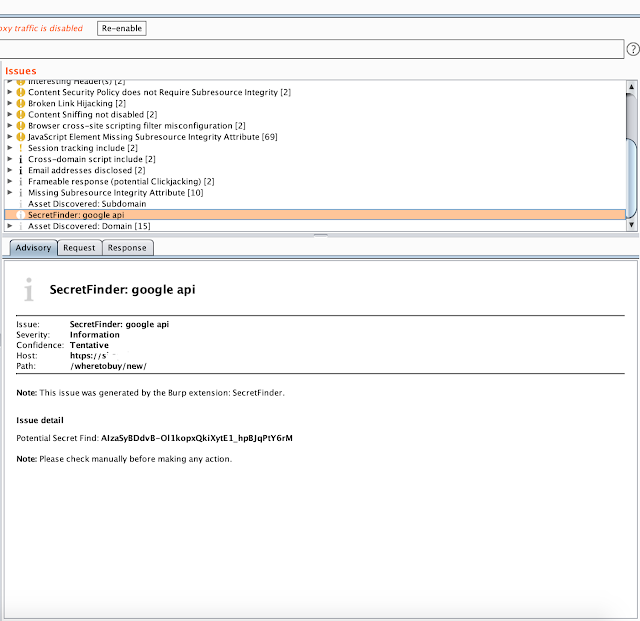
2.1KBurp Suite Secret Finder – Burp Suite Extension To Discover Apikeys/Tokens From HTTP Response
Burp Suite extension to discover a apikey/tokens from HTTP response. Install download SecretFinder wget https://raw.githubusercontent.com/m4ll0k/BurpSuite-Secret_Finder/master/SecretFinder.pyorgit clone https://github.com/m4ll0k/BurpSuite-Secret_Finder.git now open Burp > Extender...
-

 2.7K
2.7KaSYNcrone – A SYN Flood DDoS Tool
aSYNcrone is a SYN Flood DDoS Attack Tool!Usage: git clone https://github.com/fatih4842/aSYNcrone.gitcd aSYNcronegcc aSYNcrone.c -o aSYNcrone./aSYNcrone <source IP> <source port> <destination IP> <destination...
-
 908
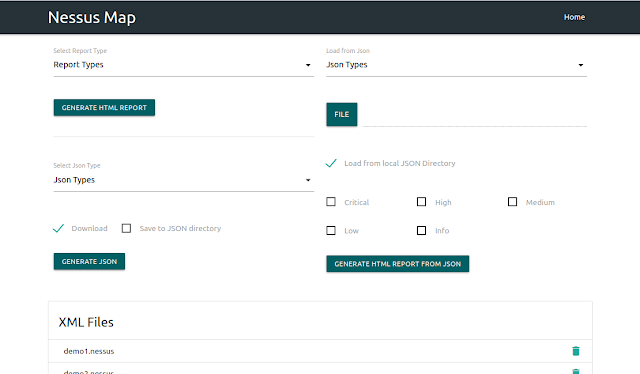
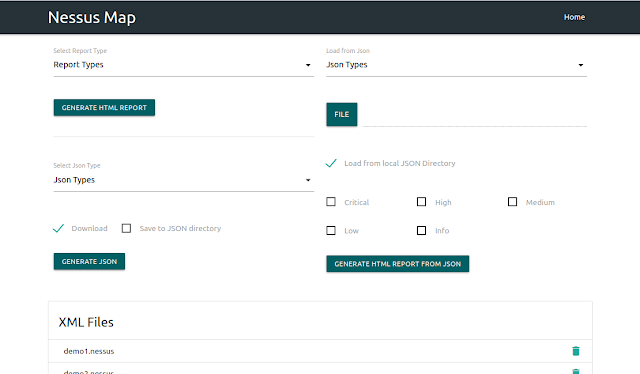
908Nessus Map – Parse .Nessus File(S) And Shows Output In Interactive UI
Nessus XML Praser Requirements Python3 Django Tested on Ubuntu 18.04 What it does Vulnerability based parsing Service based parsing Host bases parsing...
-

 3.7K
3.7KSooty – The SOC Analysts All-In-One CLI Tool To Automate And Speed Up Workflow
Sooty is a tool developed with the task of aiding SOC analysts with automating part of their workflow. One of the goals...






