Hack Tools
-
 1.4K
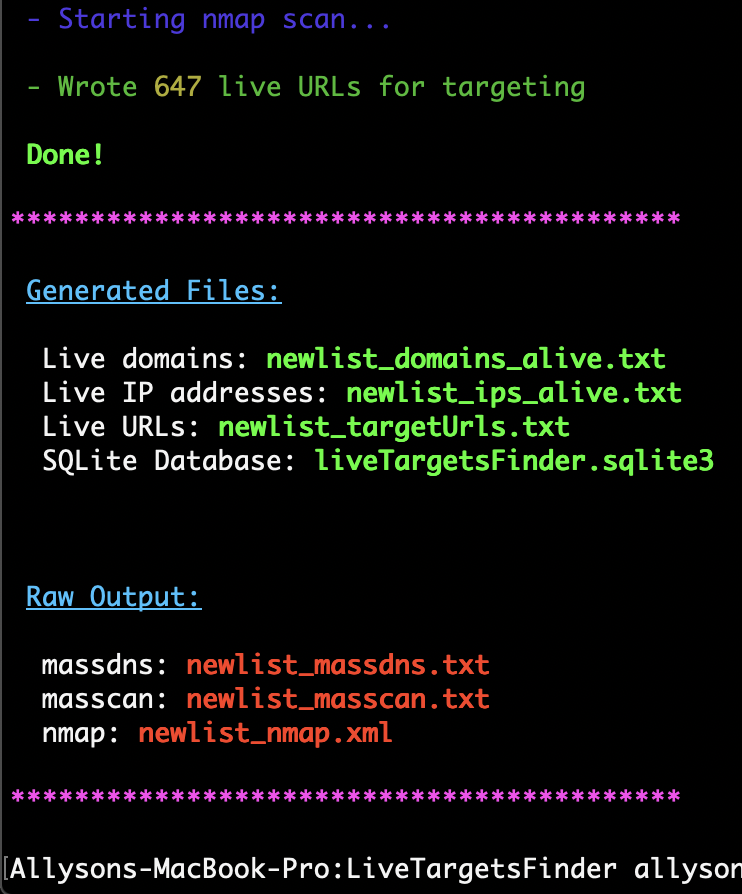
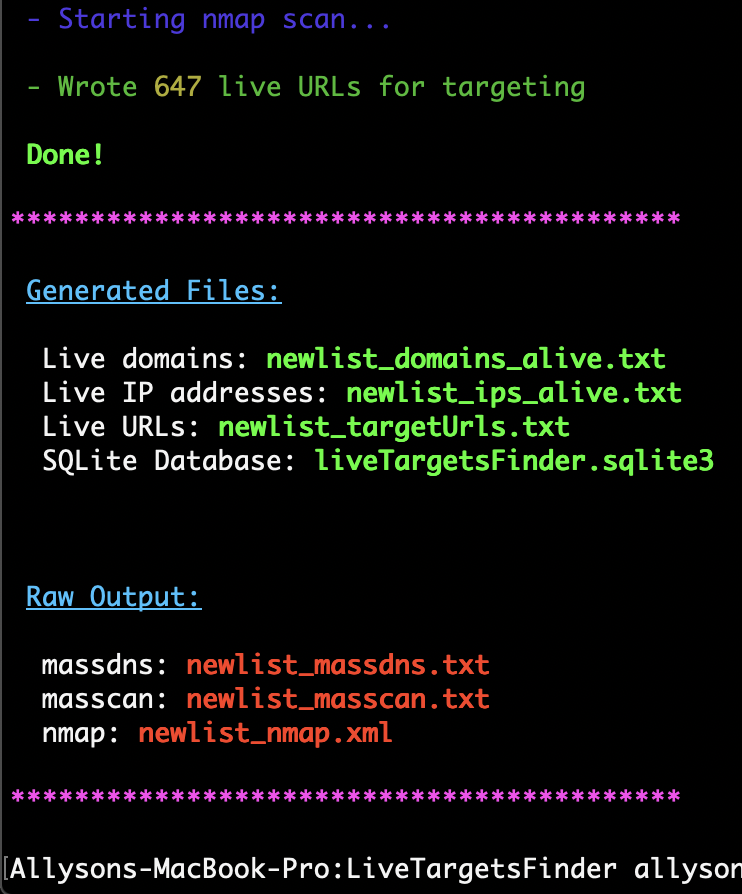
1.4KLiveTargetsFinder: automating the usage of MassDNS, Masscan and nmap to filter out unreachable hosts
LiveTargetsFinder Generates lists of live hosts and URLs for targeting, automating the usage of Massdns, Masscan, and nmap to filter out unreachable...
-
 5.0K
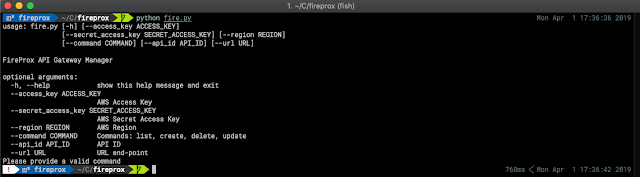
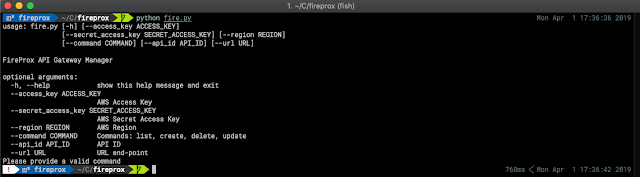
5.0KFireProx – AWS API Gateway Management Tool For Creating On The Fly HTTP Pass-Through Proxies For Unique IP Rotation
Being able to hide or continually rotate the source IP address when making web calls can be difficult or expensive. A number...
-
 2.8K
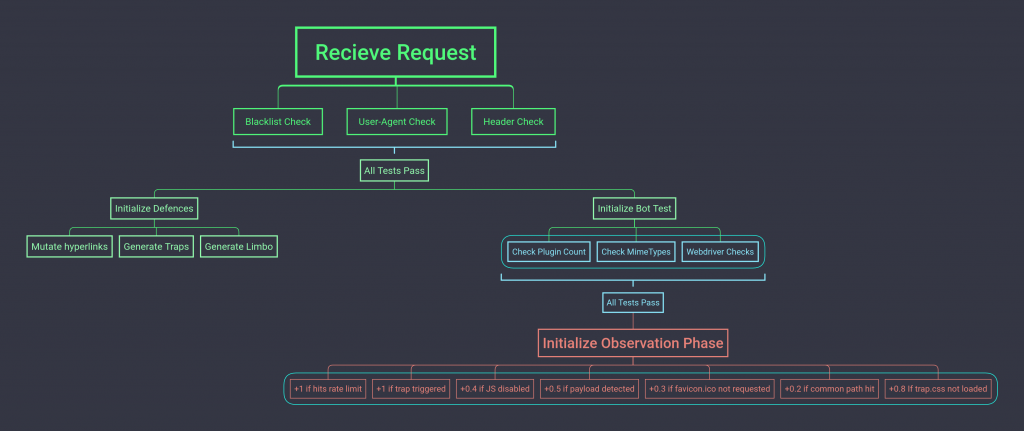
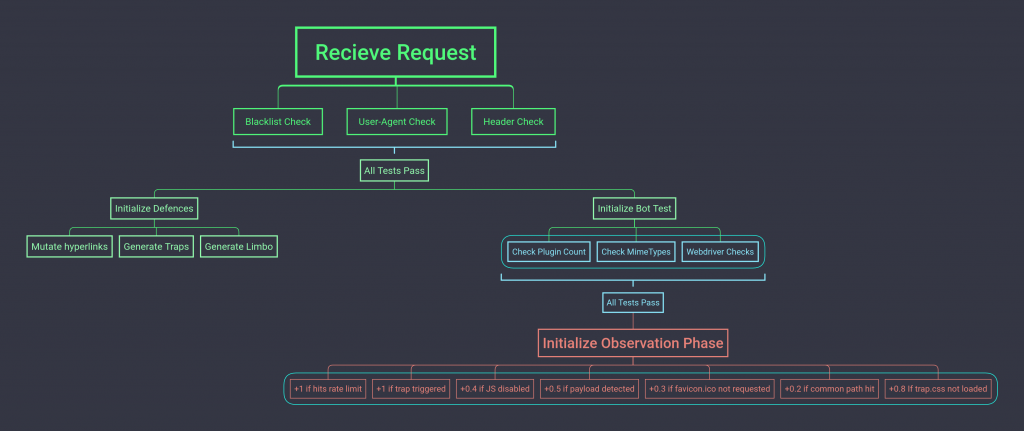
2.8KPredator: Anti-Automation System
Predator – Anti-Automation System Predator is a prototype web application designed to demonstrate anti-crawling, anti-automation & bot detection techniques. It can be...
-
 3.0K
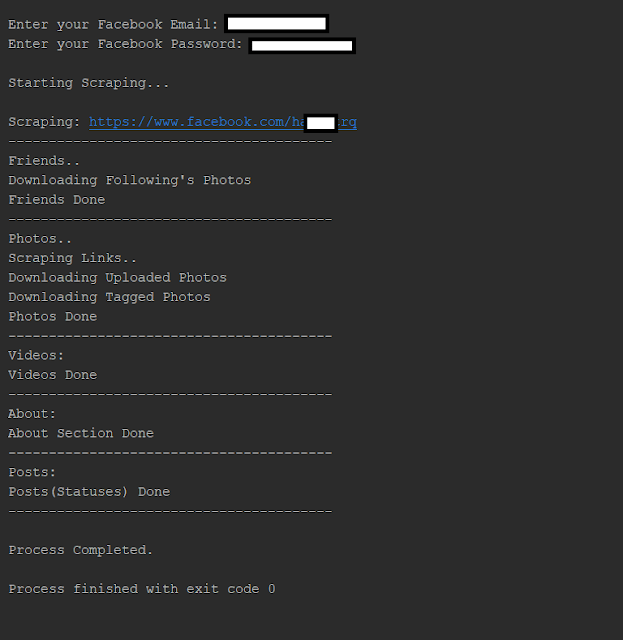
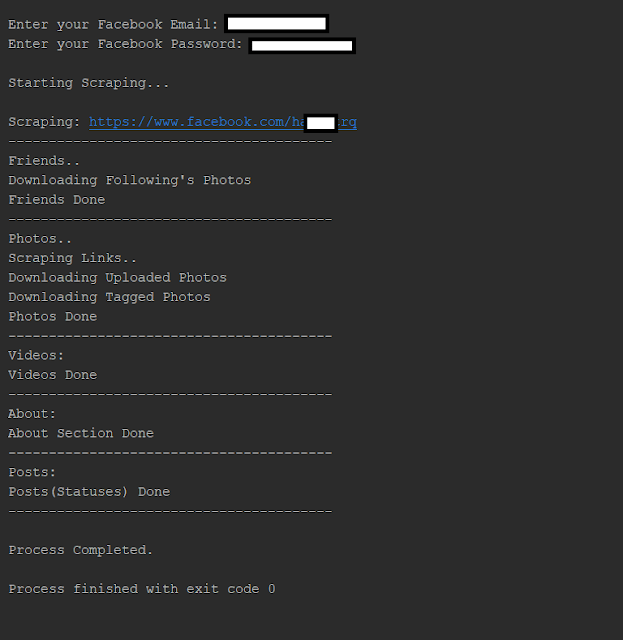
3.0KUltimate Facebook Scraper – A Bot Which Scrapes Almost Everything About A Facebook User’S Profile Including All Public Posts/Statuses Available On The User’S Timeline, Uploaded Photos, Tagged Photos, Videos, Friends List And Their Profile Photos
Tooling that automates your social media interactions to collect posts, photos, videos, friends, followers and much more on Facebook. FeaturesA bot which...
-

 450
450Consumer VPN Safety Tips To Consider
Given that we are almost always connected to the Internet on a daily basis, cybersecurity is a growing concern among all of...
-
 2.9K
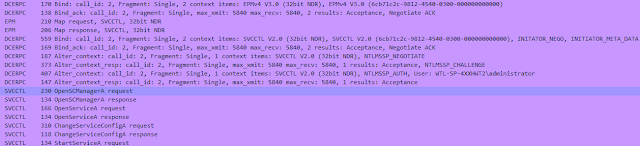
2.9KSCShell – Fileless Lateral Movement Tool That Relies On ChangeServiceConfigA To Run Command
Fileless lateral movement tool that relies on ChangeServiceConfigA to run command. The beauty of this tool is that it doesn’t perform authentication...
-
 2.7K
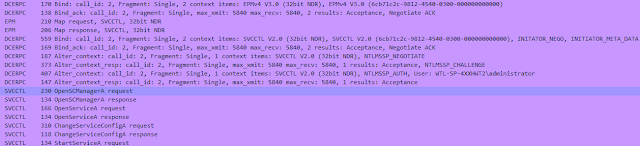
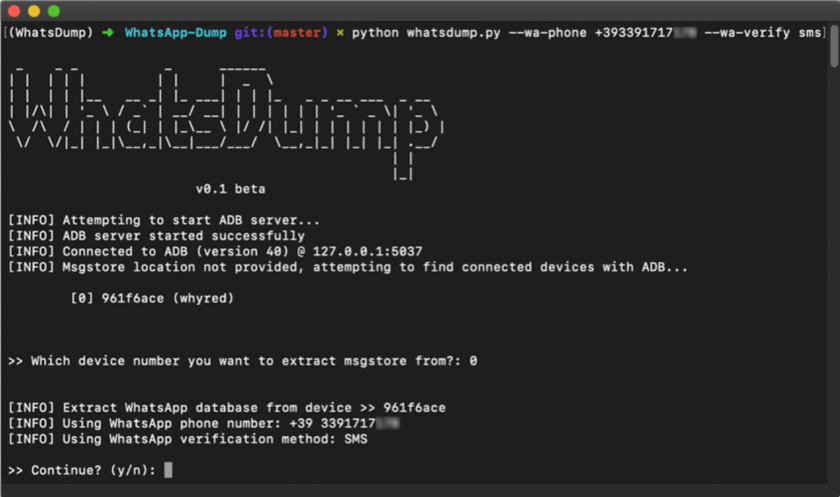
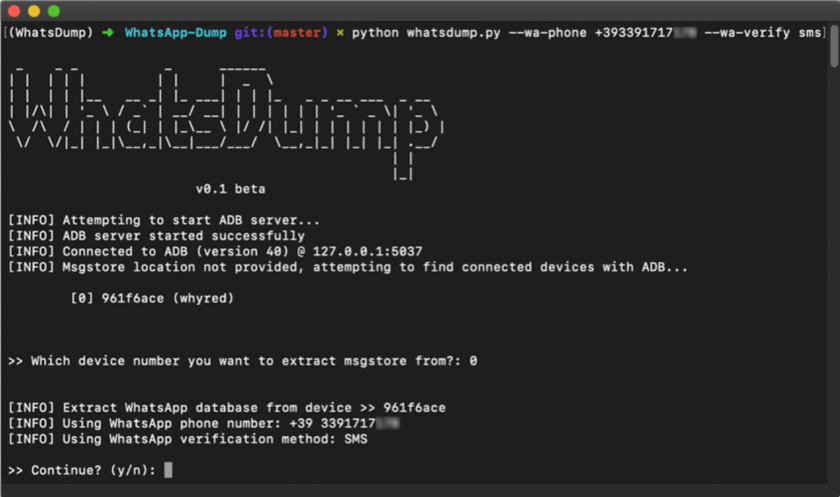
2.7KWhatsDump: Extract WhatsApp private key from any non-rooted Android device
WhatsDump Extract WhatsApp private key from any Android device (Android 7+ supported). This tool spawns a clean Android 6 emulator and attempts...
-
 4.1K
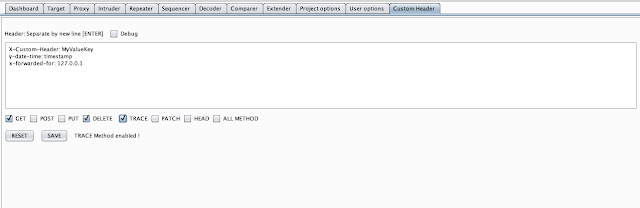
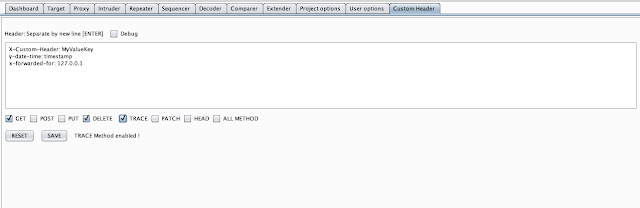
4.1KCustom Header – Automatic Add New Header To Entire BurpSuite HTTP Requests
This Burp Suite extension allows you to customize header with put a new header into HTTP REQUEST BurpSuite (Scanner, Intruder, Repeater, Proxy...
-
 3.1K
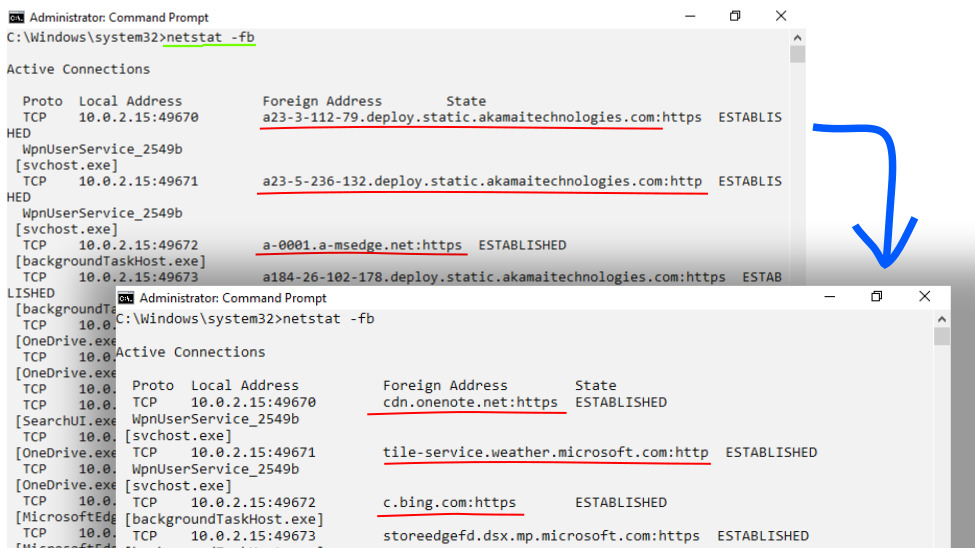
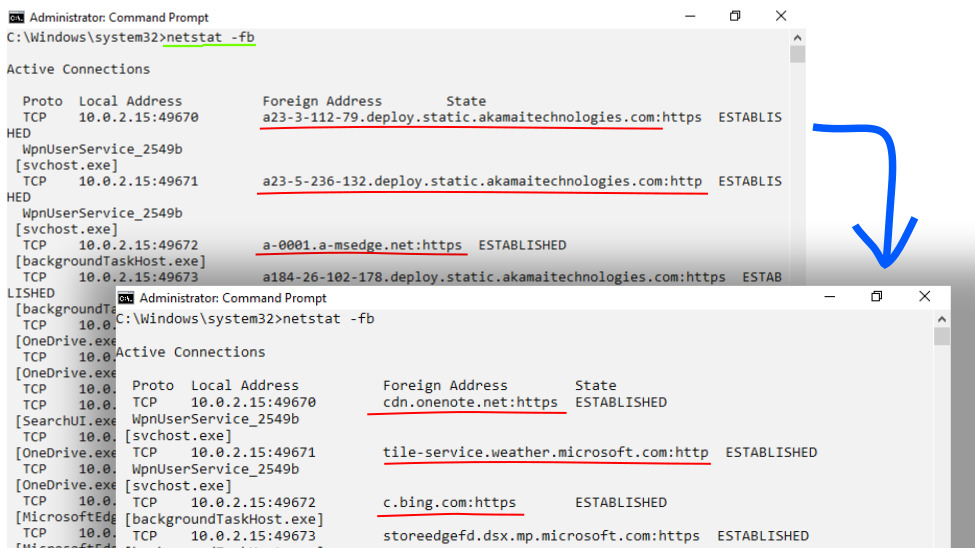
3.1KPR-DNSd: Passive-Recursive DNS daemon
PR-DNSd Passive-Recursive DNS daemon. What does it do? Use cases run as localhost DNS service, to fix your netstat/tcpview/lsof, etc. output...
-

 4.5K
4.5KDdoor – Cross Platform Backdoor Using Dns Txt Records
Cross-platform backdoor using dns txt records. What is ddor?ddor is a cross platform light weight backdoor that uses txt records to execute...
-
 4.2K
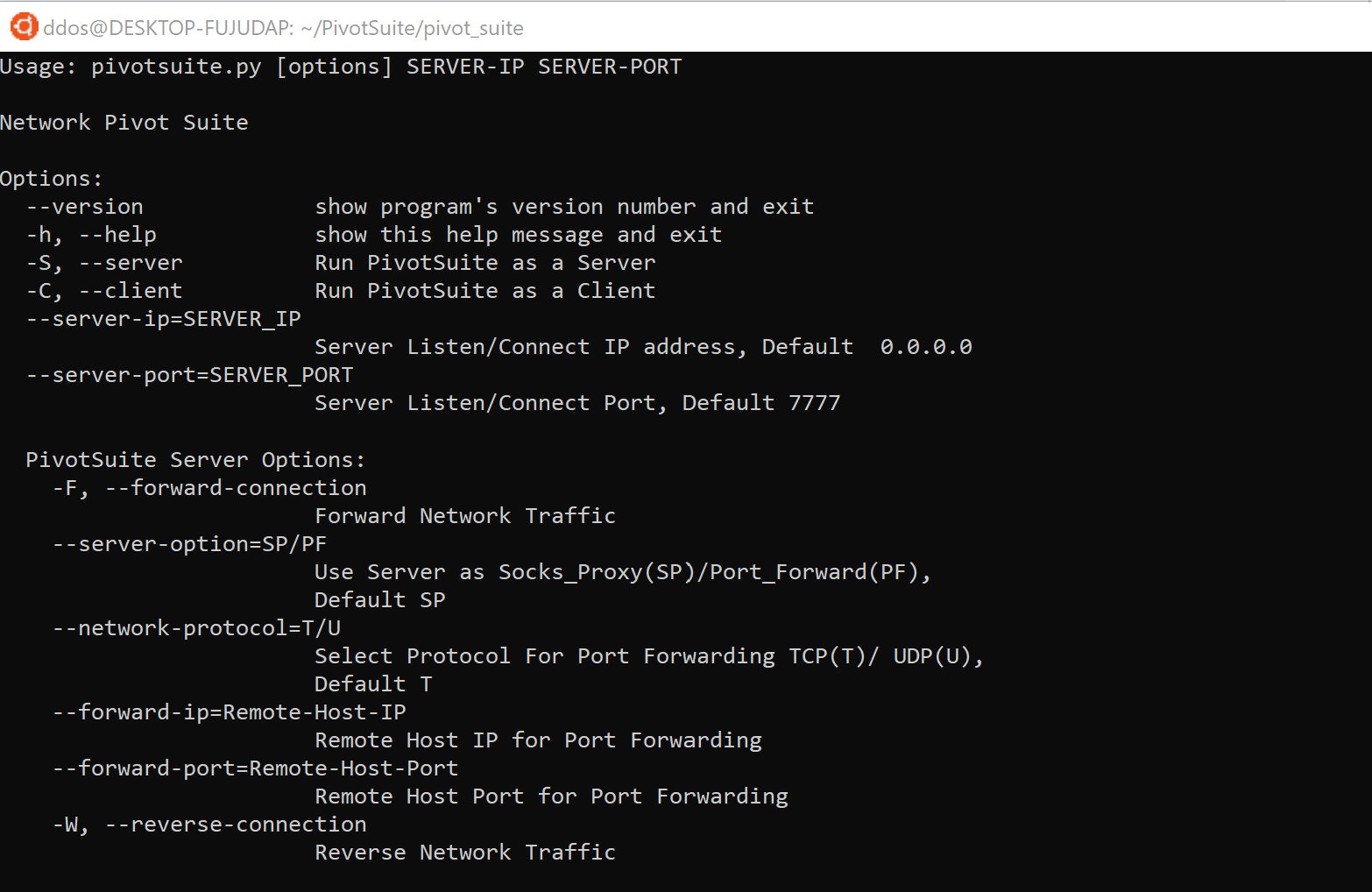
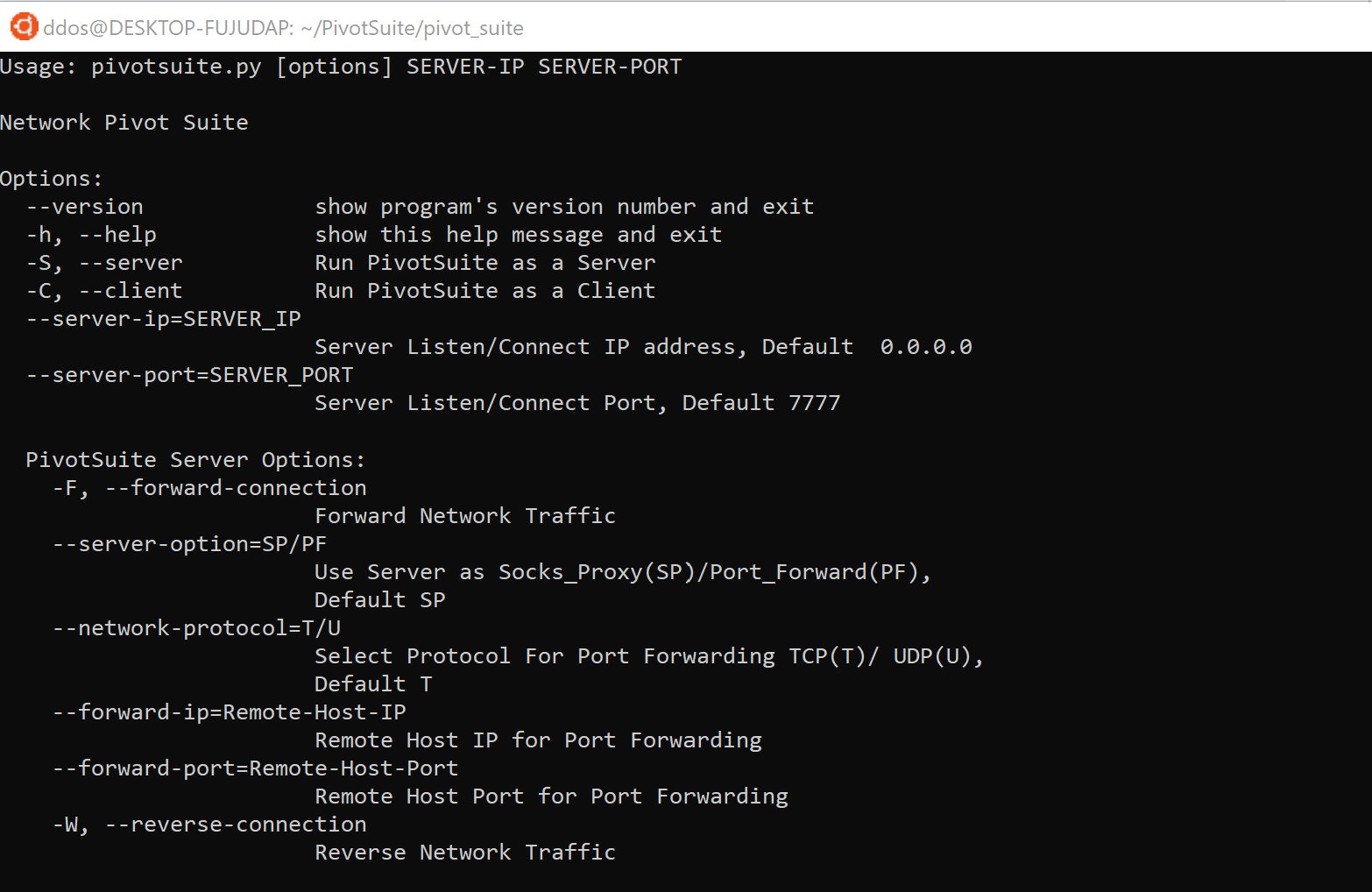
4.2KPivotSuite: A Network Pivoting Toolkit
PivotSuite PivotSuite: Hack The Hidden Network – A Network Pivoting Toolkit It is a portable, platform-independent and powerful network pivoting toolkit, Which...
-
 1.5K
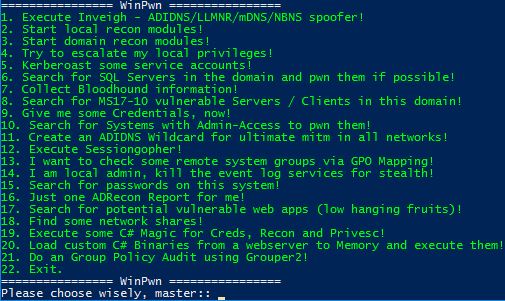
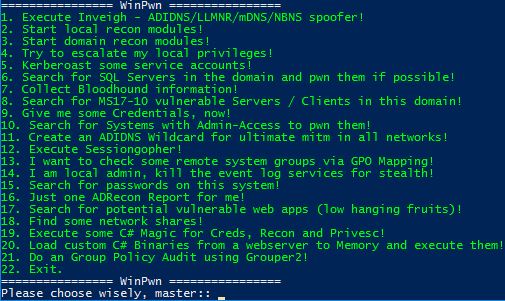
1.5KWinPwn – Automation For Internal Windows Penetrationtest / AD-Security
In many past internal penetration tests I often had problems with the existing Powershell Recon / Exploitation scripts due to missing proxy...
-
 1.5K
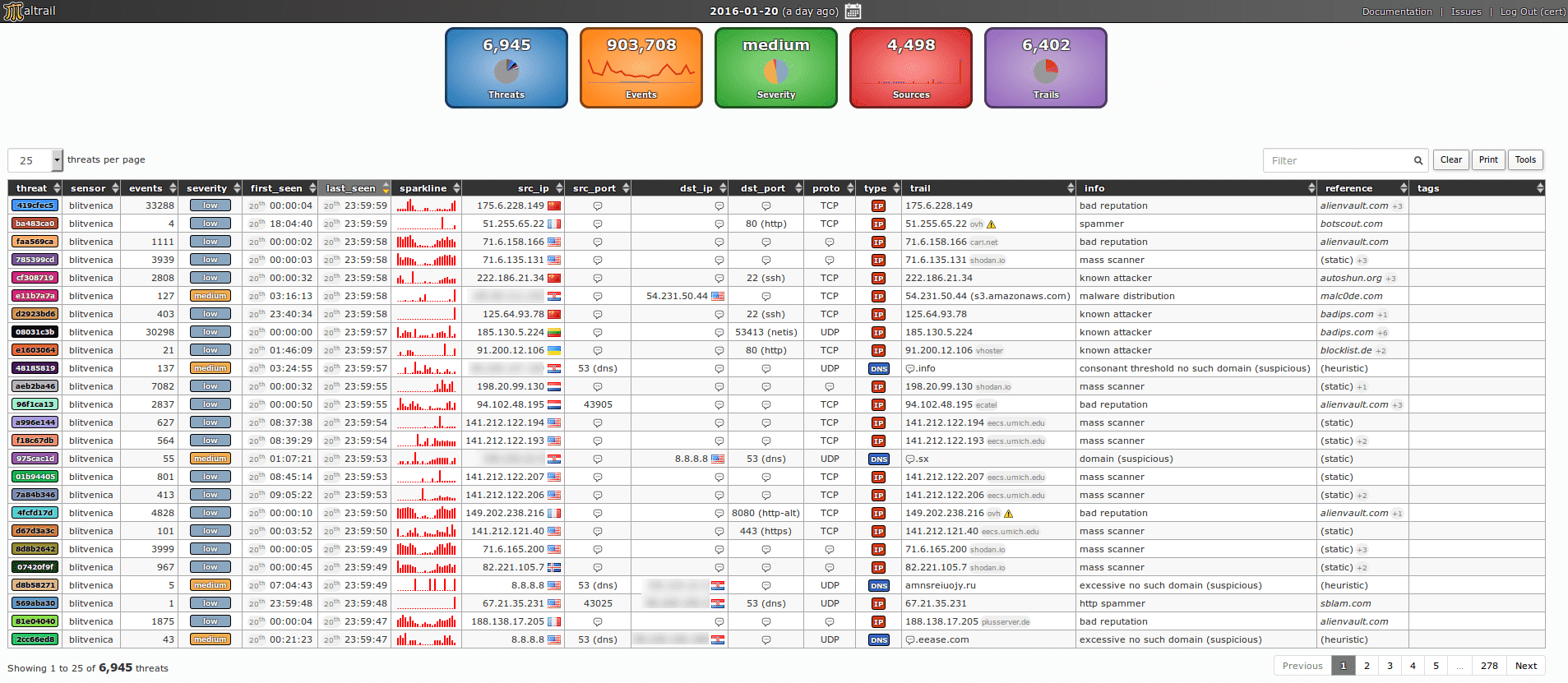
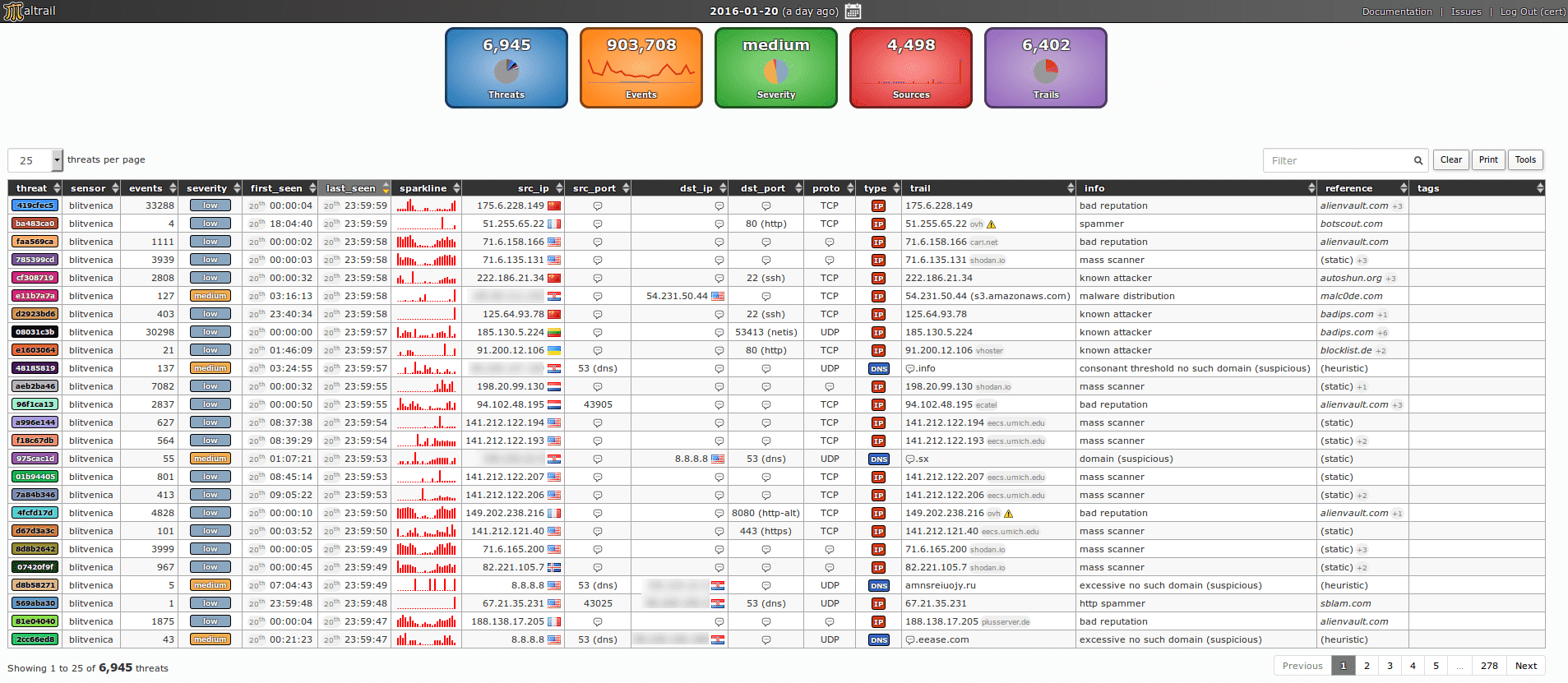
1.5Kmaltrail v0.16.69 releases: Malicious traffic detection system
Maltrail is a malicious traffic detection system, utilizing publicly available (black)lists containing malicious and/or generally suspicious trails, along with static trails compiled from...
-
 2.2K
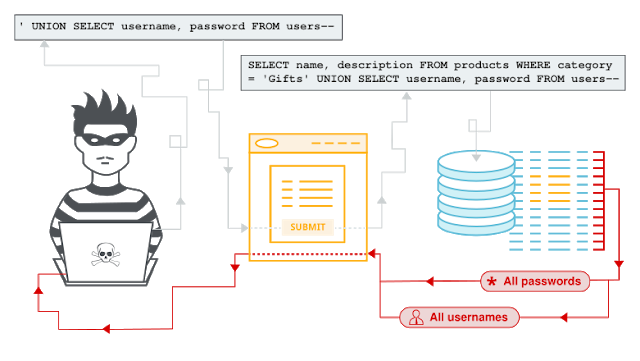
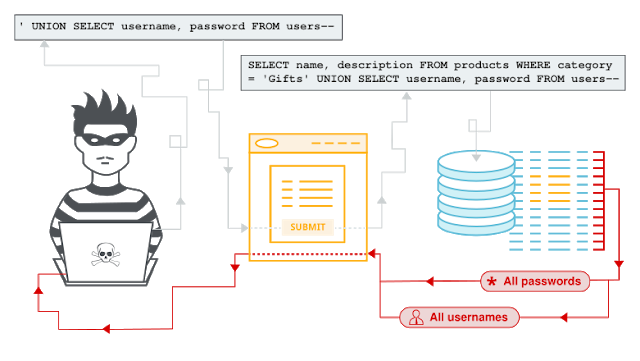
2.2KSQL Injection Payload List
SQL InjectionIn this section, we’ll explain what SQL injection is, describe some common examples, explain how to find and exploit various kinds...
-

 3.0K
3.0KWhat Is Meant By Anti Theft Devices
According to the Insurance Bureau of Canada, car theft is a major problem that is occurring all across the world and costs...
-
 706
706Andor – Blind SQL Injection Tool With Golang
Blind SQL Injection Tool with Golang.UsageDownload andor.go and go to the folder where the file andor.go located. And type this to command...
-
 1.6K
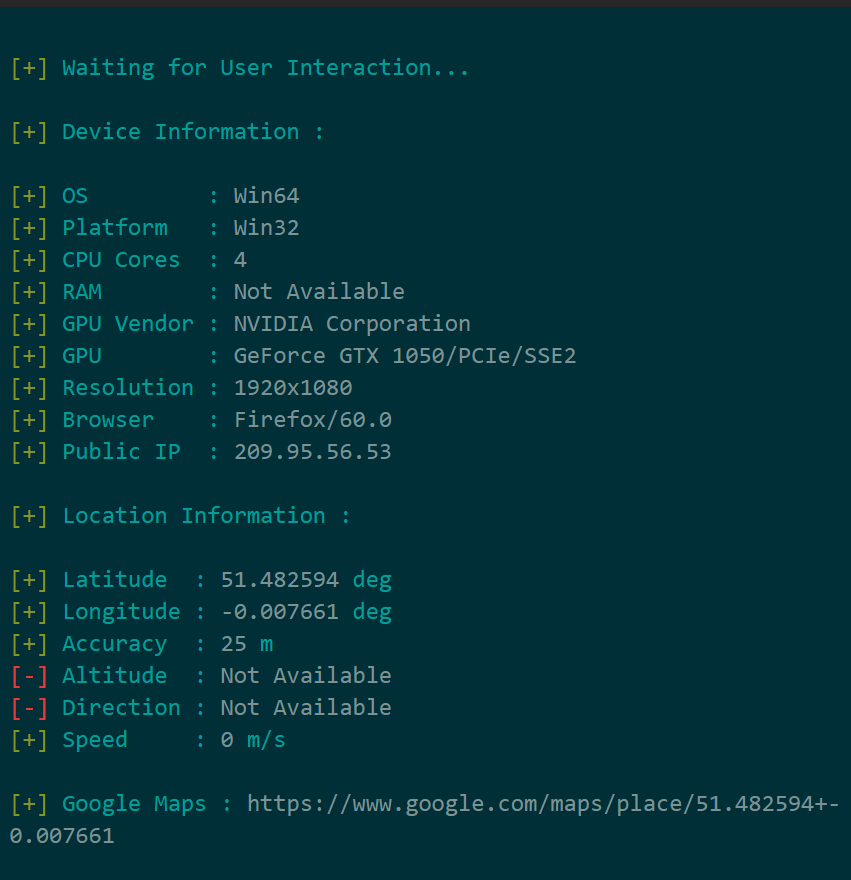
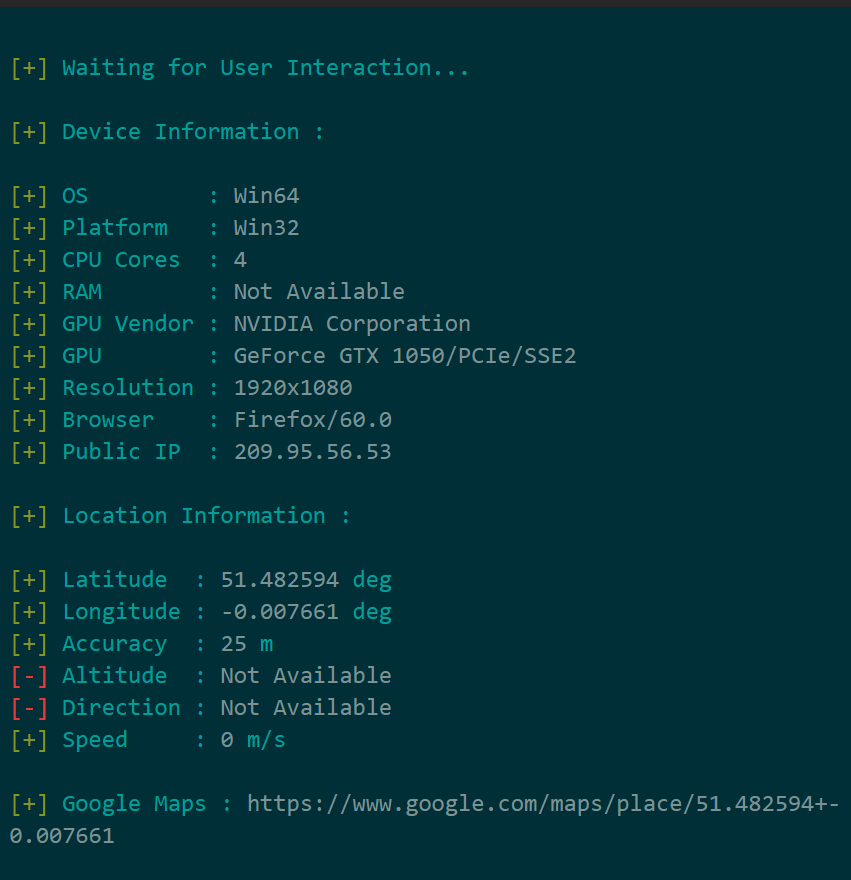
1.6Kseeker v1.1.9 releases: Find GeoLocation with High Accuracy
Seeker Introduction Seeker utilizes HTML5, Javascript, JQuery and PHP to grab Device Information and GeoLocation with High Accuracy. Seeker Hosts a fake website on Apache Server and uses Ngrok to generate an...
-

 1.4K
1.4KDetectionLab – Vagrant And Packer Scripts To Build A Lab Environment Complete With Security Tooling And Logging Best Practices
DetectionLab is tested weekly on Saturdays via a scheduled CircleCI workflow to ensure that builds are passing. PurposeThis lab has been designed...
-
 401
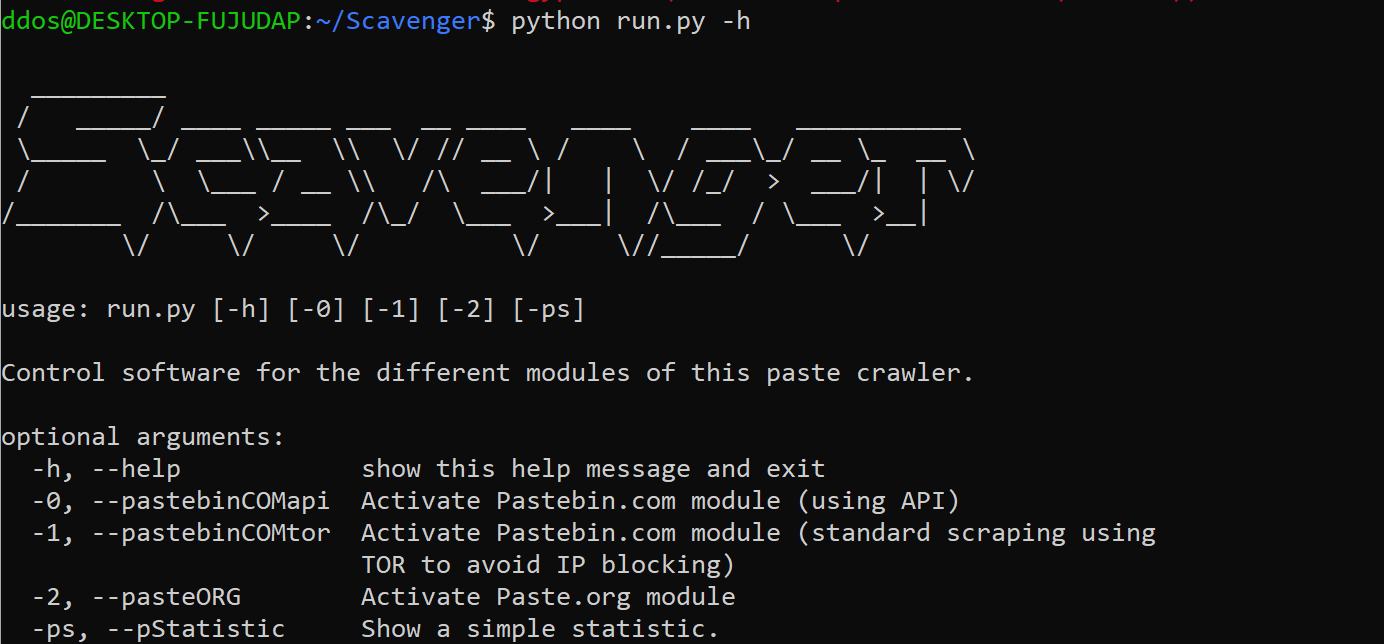
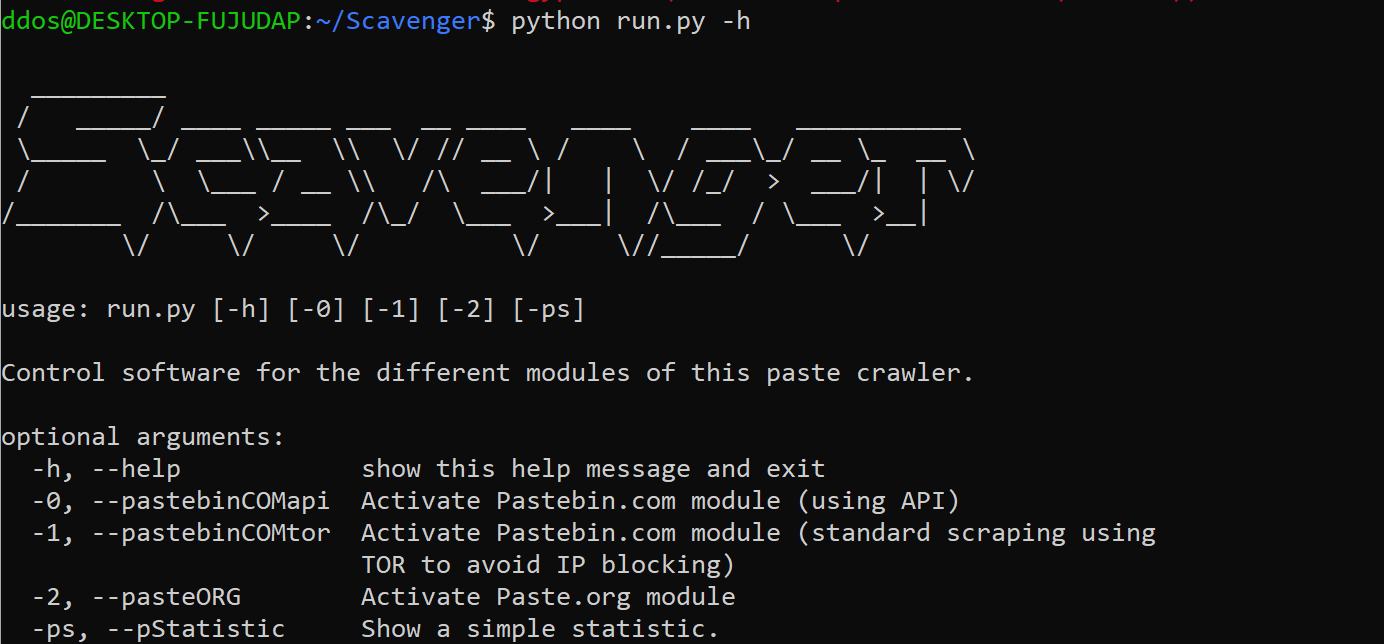
401Scavenger: searching for credential leaks on different paste sites
Scavenger Just the code of my OSINT bot searching for sensitive data leaks on different paste sites. Search terms: credentials private RSA...
-

 4.5K
4.5KRedPeanut – A Small RAT Developed In .Net Core 2 And Its Agent In .Net 3.5/4.0
[*] RedPeanut is a small RAT developed in .Net Core 2 and its agent in .Net 3.5 / 4.0. RedPeanut code execution...
-
 3.5K
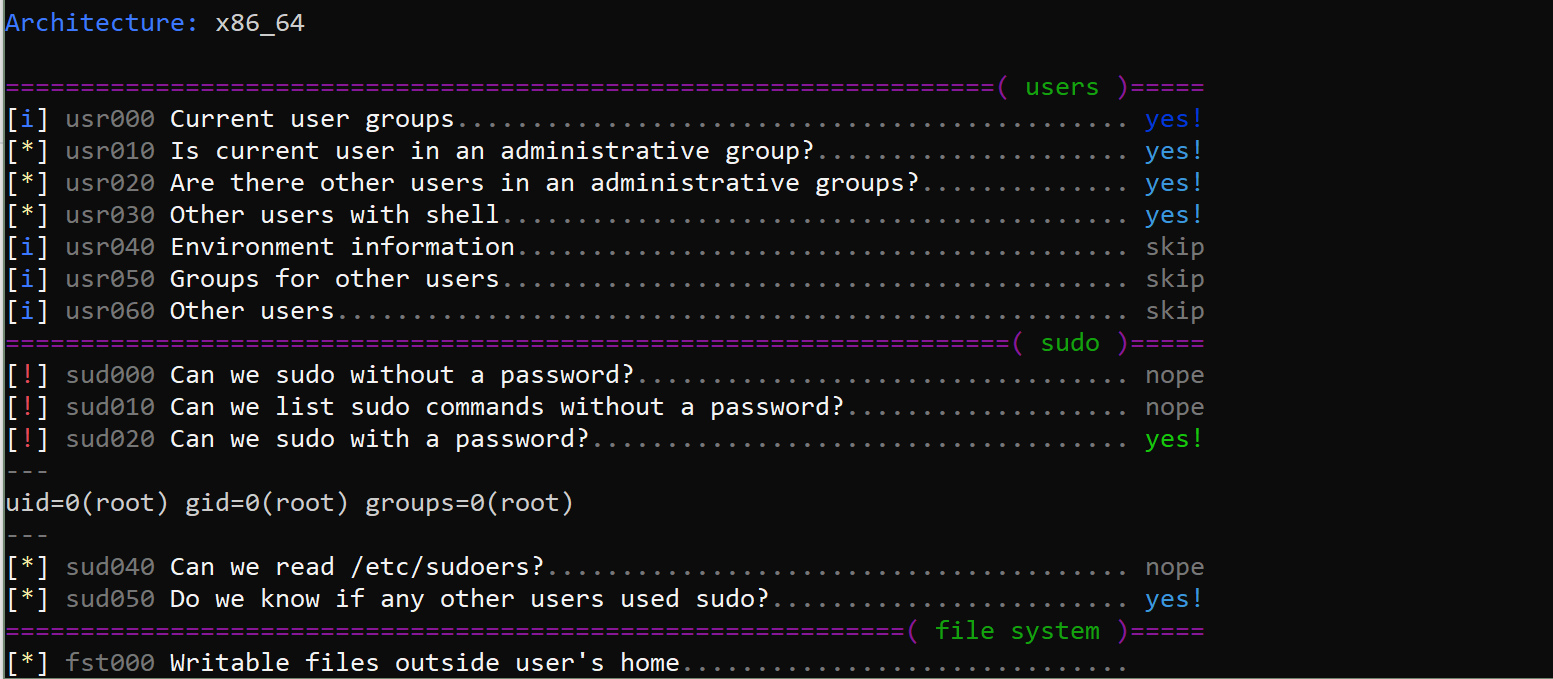
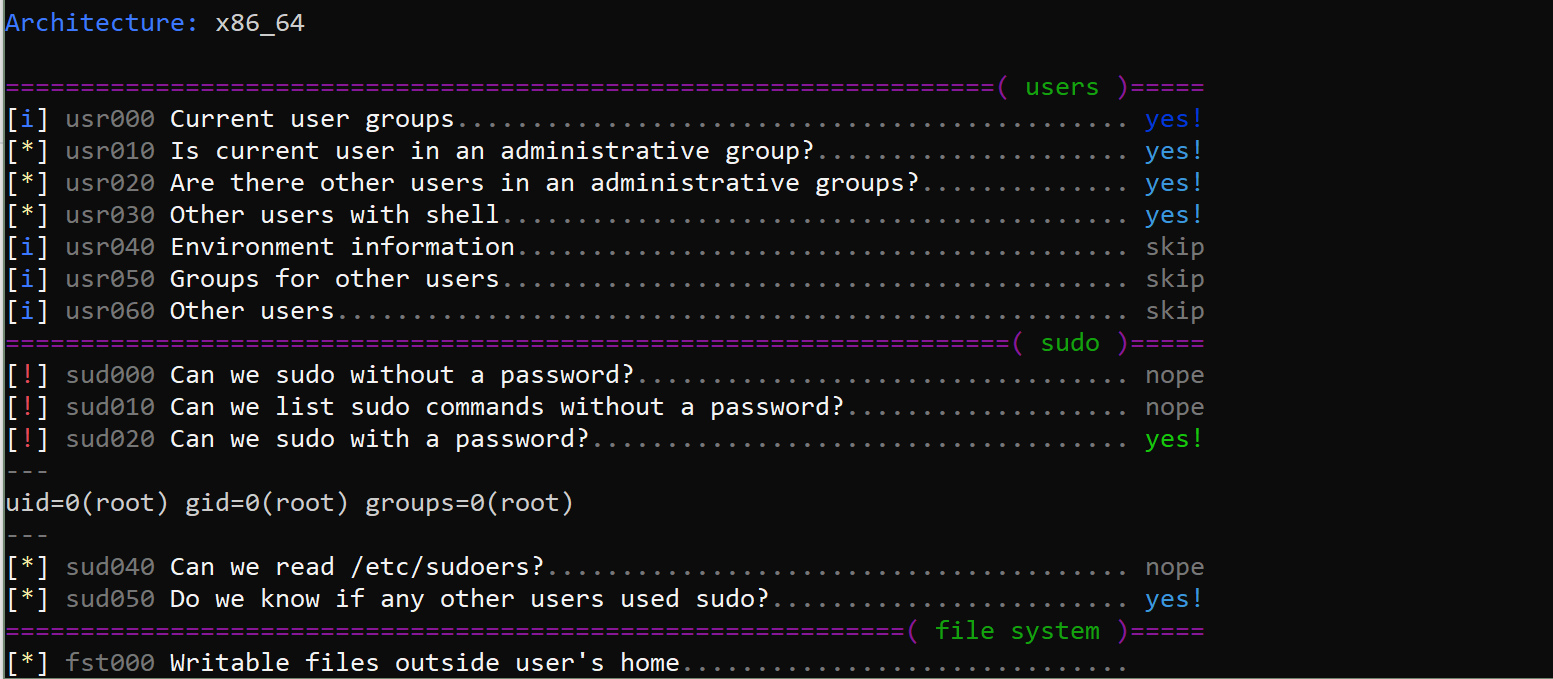
3.5Klinux-smart-enumeration v1.9 releases: Linux enumeration tools for pentesting and CTFs
linux-smart-enumeration Linux enumeration tools for pentesting and CTFs This project was inspired by LinEnum and uses many of its tests. Unlike LinEnum, lse tries...






