Hackers Repository
-

 3.6K
3.6KTencent Blade Team found serious SQLite vulnerability
Recently, the Tencent Blade Team discovered a set of SQLite vulnerabilities called “Magellan 2.0”, allowing hackers to remotely run various malicious programs...
-
 4.9K
4.9K[Blackhat Europe tool] avclassplusplus: Massive Malware Labeling Tool
AVCLASS++: Yet Another Massive Malware Labeling Tool avclassplusplus is an appealing complement to AVCLASS [1], a state-of-the-art malware labeling tool. AVCLASS++ is a...
-
 1.4K
1.4KExploitivator – Automate Metasploit Scanning And Exploitation
This has only been tested on Kali.It depends on the msfrpc module for Python, described in detail here: https://www.trustwave.com/Resources/SpiderLabs-Blog/Scripting-Metasploit-using-MSGRPC/Install the necessary Kali...
-
 4.8K
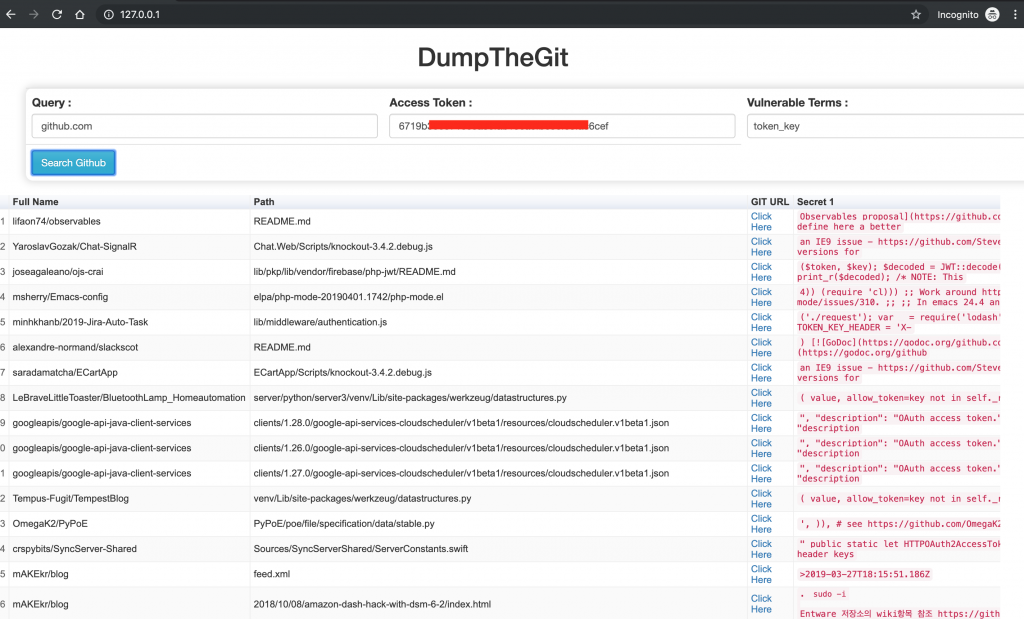
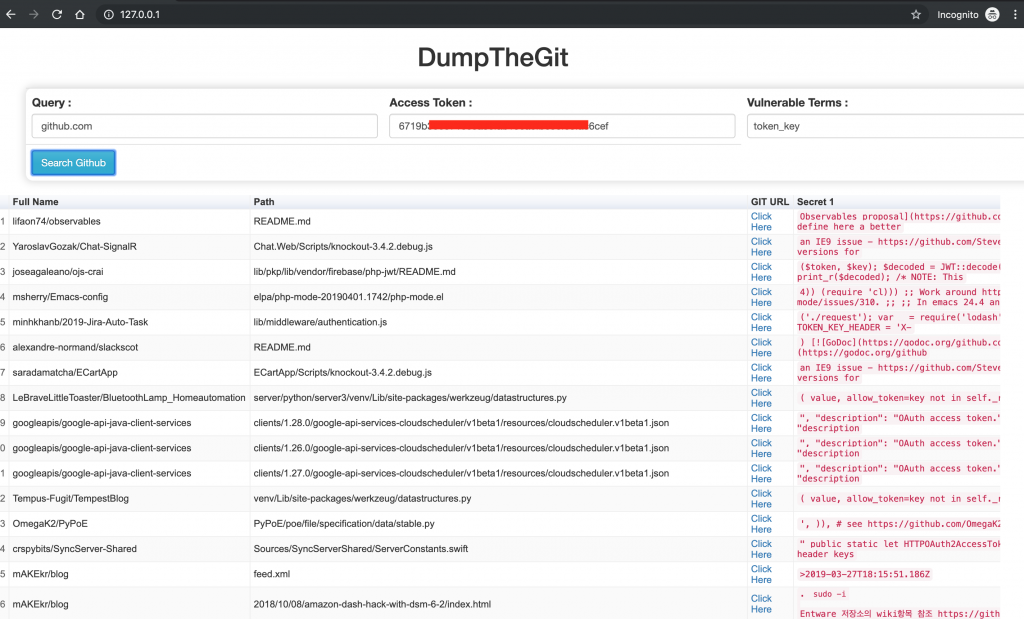
4.8K[Blackhat Europe tool] DumpTheGit: find sensitive information uploaded to the Github repositories
DumpTheGit DumpTheGit searches through public repositories to find sensitive information uploaded to the Github repositories. The tool will flag the matches for...
-

 2.5K
2.5KKaspersky reveals hackers use both Windows 10 and Google Chrome zero-day vulnerabilities to launch attacks
Both Microsoft and Google have released software updates yesterday to fix some security vulnerabilities, including a zero-day vulnerability that has been exploited...
-

 1.1K
1.1KProtect yourself from cyberstalkers
The internet has brought us all closer together than ever before. Never before in our history has mankind been able to communicate...
-

 3.4K
3.4KThe children’s smartwatches exist vulnerability that discloses GPS smartwatches
Security company Rapid7 has disclosed security vulnerabilities in three children’s smartwatches sold on Amazon. These three children’s smartwatches are the GreaSmart, the...
-

 3.6K
3.6KRTTM – Real Time Threat Monitoring Tool
Monitoring possible threats of your company on Internet is an impossible task to be achieved manually. Hence many threats of the company...
-

 1.4K
1.4KHashCobra – Hash Cracking Tool
hashcobra Hash Cracking tool. Usage $ ./hashcobra -H--==[ hashcobra by sepehrdad ]==--usage: hashcobra -o <opr> [options] | [misc]options: -a <alg> - hashing...
-
 4.1K
4.1KIntel CPU voltage can be modified by hackers to steal Intel SGX enclaves
Recently, researchers have discovered that undocumented features in Intel CPUs allow attackers to manipulate Intel CPU voltages in a controlled manner to...
-

 3.2K
3.2KMan Avoids Prison in Darkweb Child Porn Case
A Polish man residing in Ireland was sentenced to three years in prison suspended after he pleaded guilty to possession of hundreds...
-
 2.5K
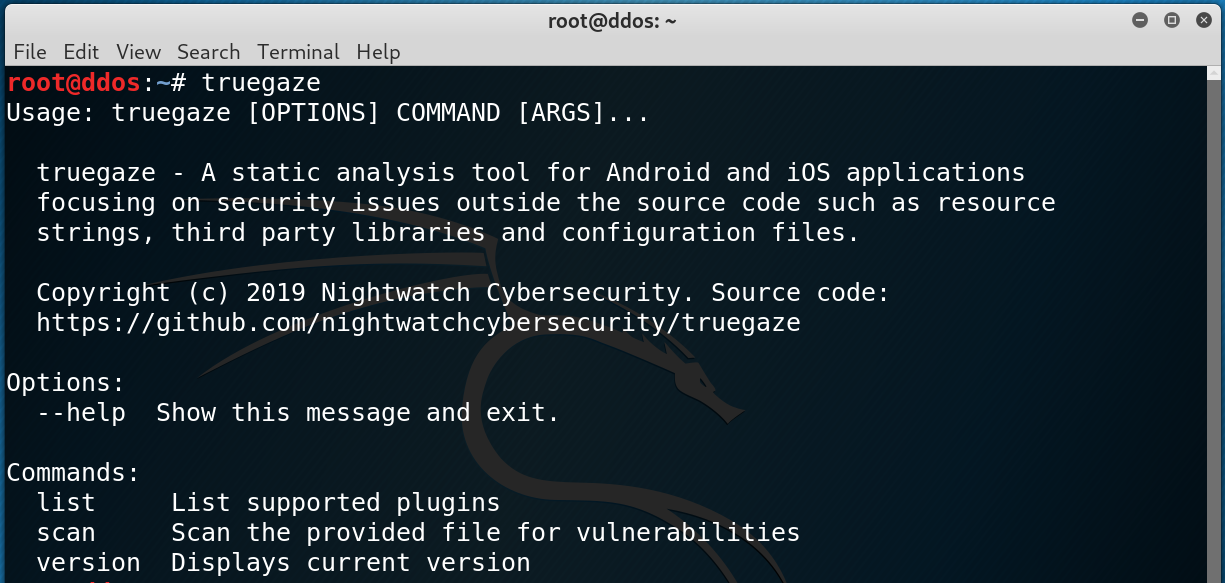
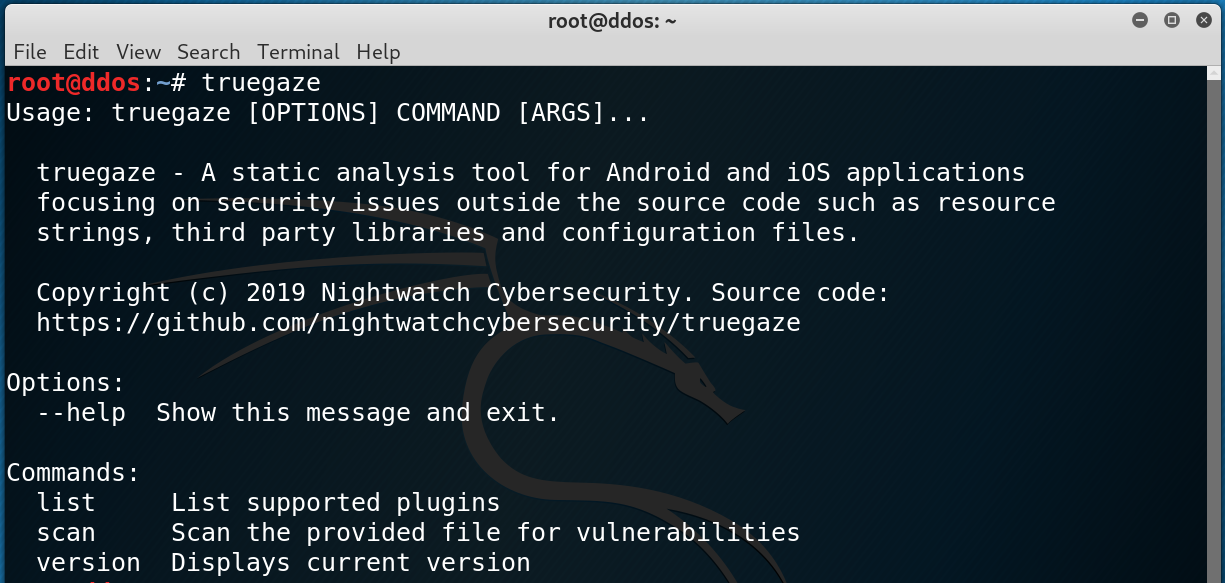
2.5Ktruegaze v0.1.5 releases: Static analysis tool for Android/iOS apps focusing on security issues
truegaze A static analysis tool for Android and iOS applications focusing on security issues outside the source code such as resource strings,...
-
 2.7K
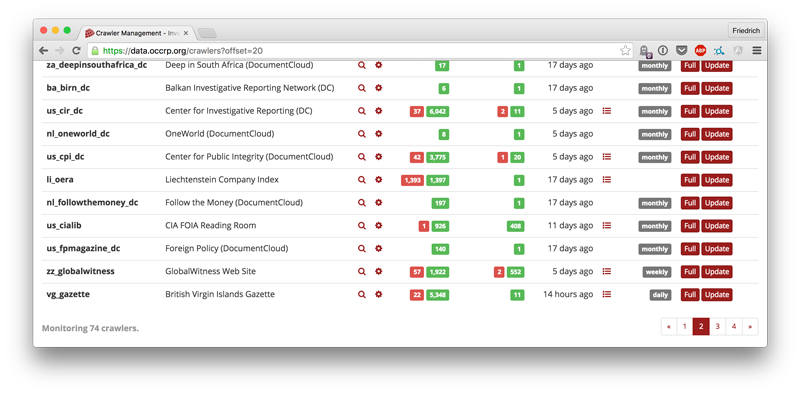
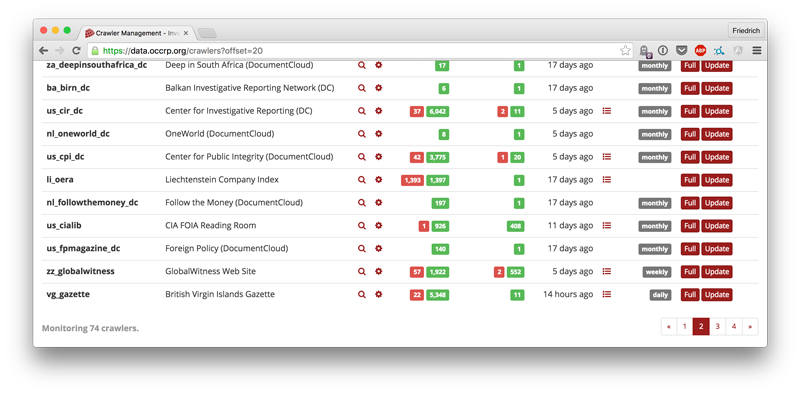
2.7Kaleph v3.4.2 releases: find the people and companies you look for
Aleph is a tool for indexing large amounts of both documents (PDF, Word, HTML) and structured (CSV, XLS, SQL) data for easy browsing...
-

 4.7K
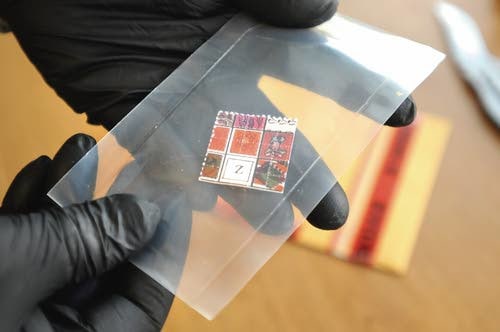
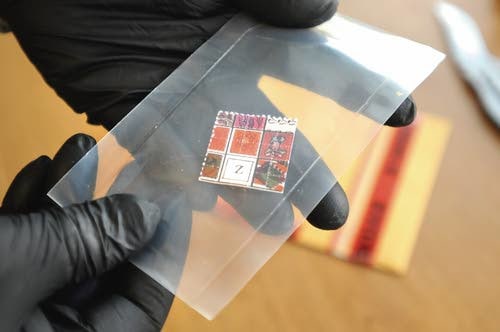
4.7KGeorgia Man Admits Running Darkweb Drug Trafficking Ring
A Georgia man admitted his role as the ringleader of a large-scale drug trafficking operation responsible for producing and distributing up to...
-
 2.5K
2.5KSplunk Attack Range – A Tool That Allows You To Create Vulnerable Instrumented Local Or Cloud Environments To Simulate Attacks Against And Collect The Data Into Splunk
The Attack Range solves two main challenges in development of detections. First, it allows the user to quickly build a small lab...
-
 4.9K
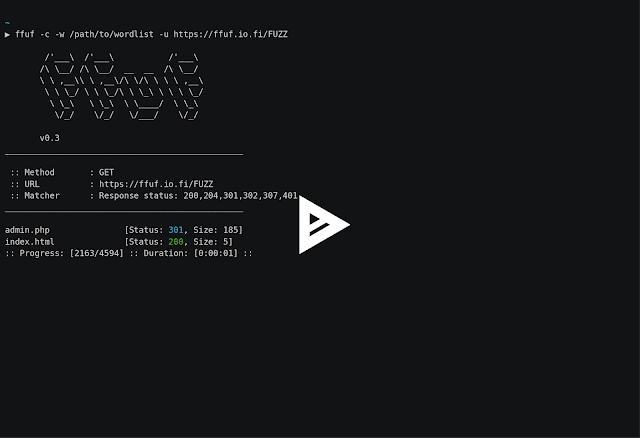
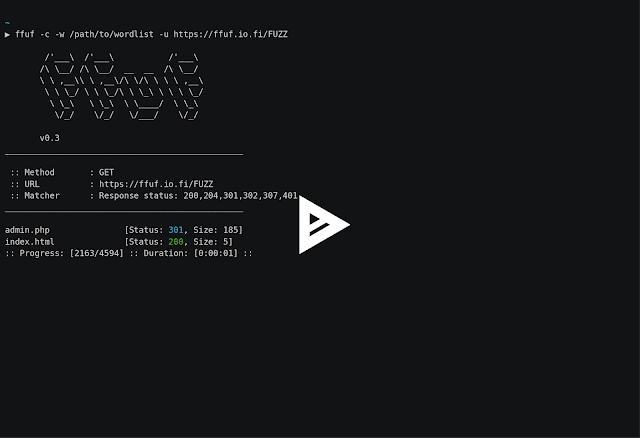
4.9KFfuf – Fast Web Fuzzer Written In Go
A fast web fuzzer written in Go.Heavily inspired by the great projects gobuster and wfuzz. Features Fast! Allows fuzzing of HTTP header...
-

 800
800Multi critical security vulnerabilities were fixed on December Patch Tuesday
On December 11, 2019, Microsoft and Adobe released the December security update. The types of vulnerabilities addressed include out-of-bounds reads and write,...
-
 5.6K
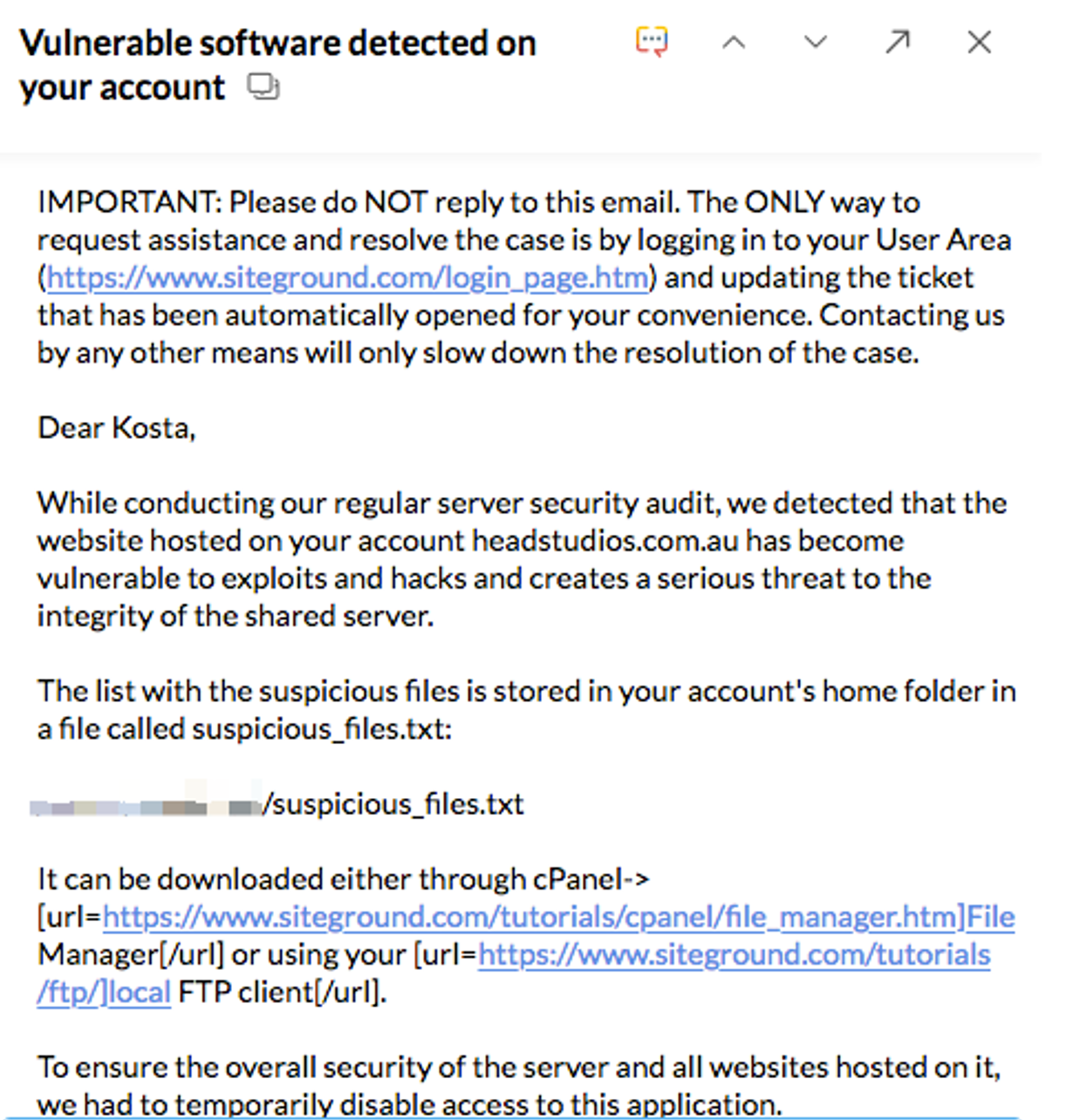
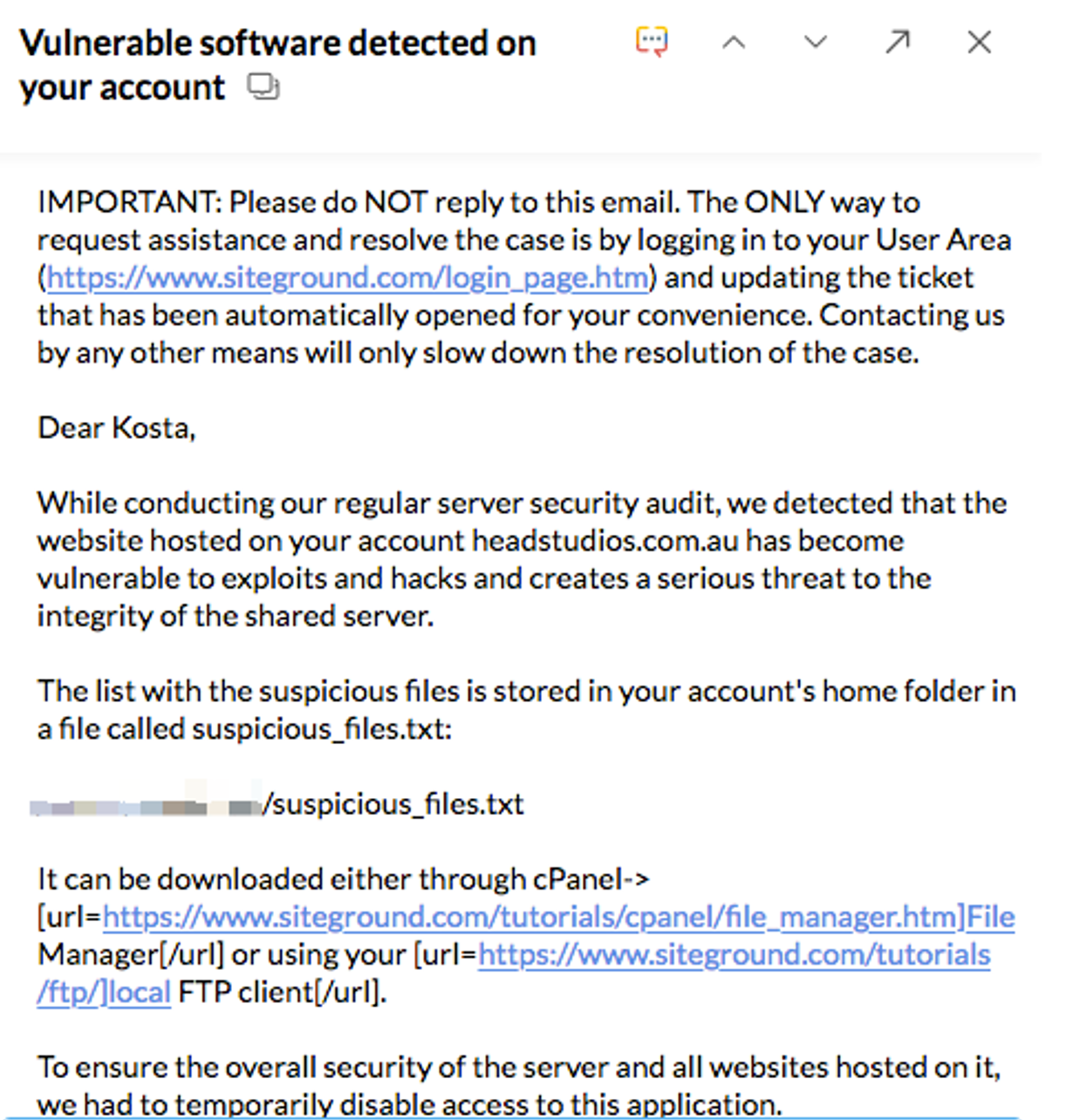
5.6KTHE HORROR EMAIL: WHEN SITEGROUND DECIDED TO SHUT DOWN MY ENTIRE SITE DUE TO 20 LINES OF MALWARE CODE – AND THE 3 THINGS I LEARNED
When comparing the difference of a shared server to a private server configuration one thing that people never consider is the fact...
-
 2.1K
2.1KAlphabay Vendor “DailyFix” Ordered to Forfeit 64 Bitcoins
A 35-year-old man from Northern Portugal was sentenced to 76 months in prison for dark web drug trafficking and money laundering. The...
-
 1.4K
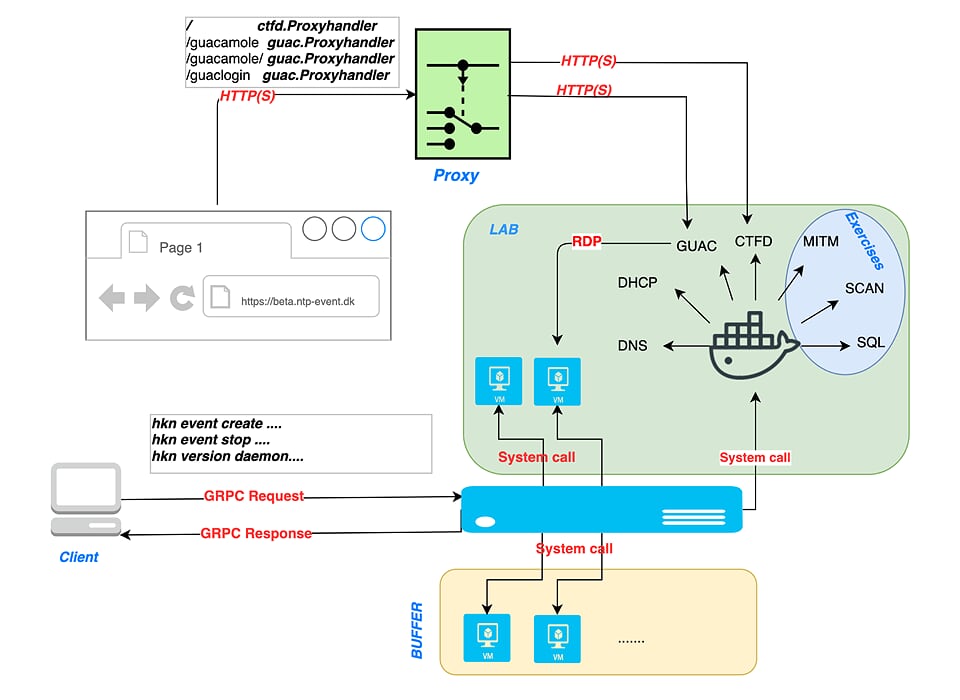
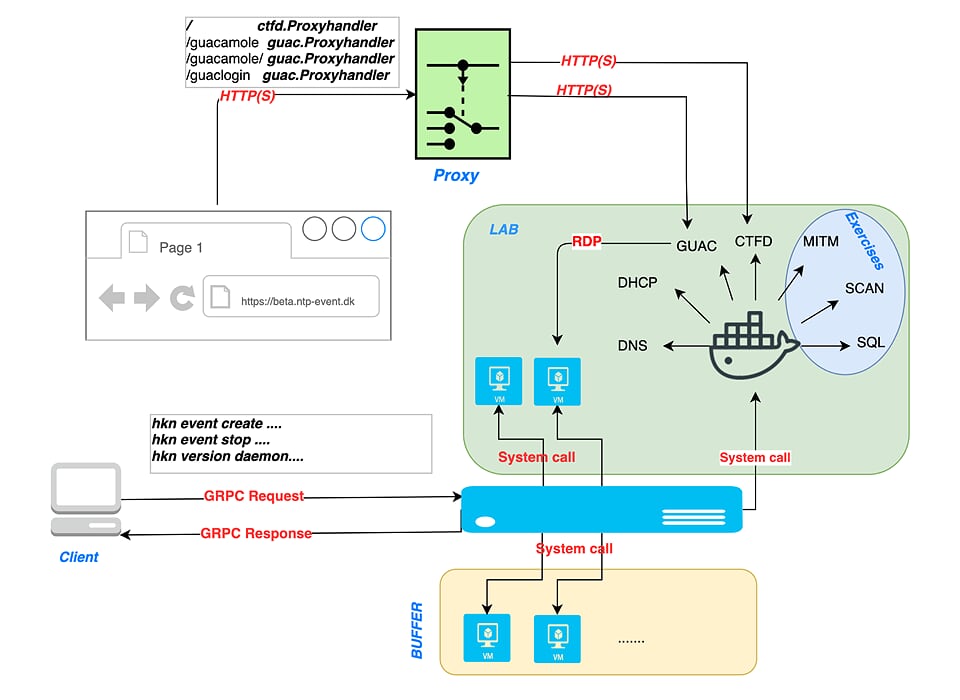
1.4K[Blackhat Europe tool] haaukins: Automated Virtualization Platform for Security Education
Haaukins Haaukins is a highly accessible and automated virtualization platform for security education, it has three main components (Docker, Virtualbox, and Golang),...
-

 791
791Fileintel – A Modular Python Application To Pull Intelligence About Malicious Files
This is a tool used to collect various intelligence sources for a given file. Fileintel is written in a modular fashion so...






