Hackers Repository
-
 3.3K
3.3KGenact – A Nonsense Activity Generator
Pretend to be busy or waiting for your computer when you should actually be doing real work! Impress people with your insane...
-
 1.6K
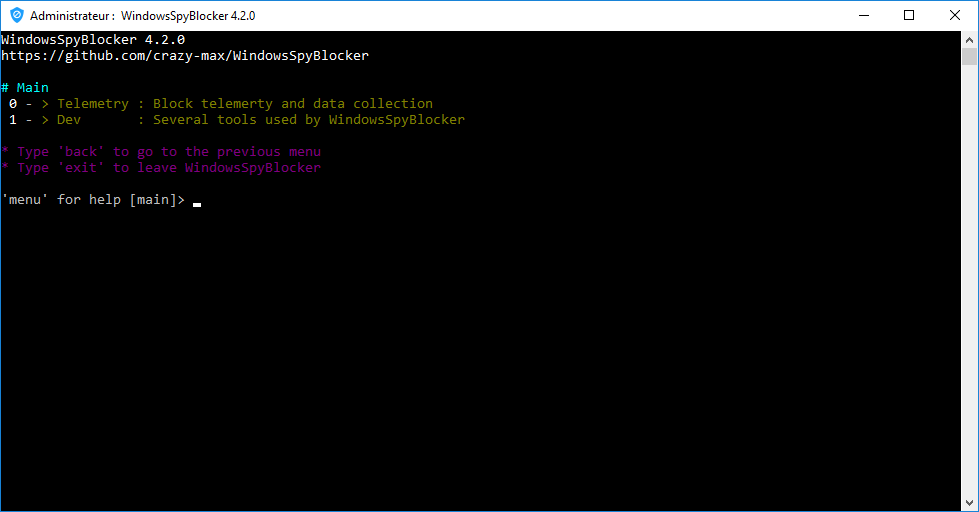
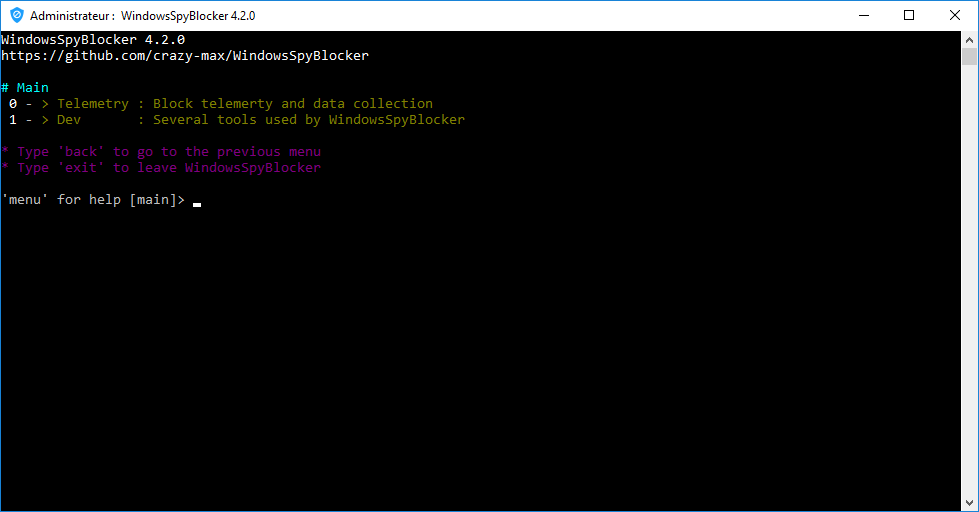
1.6KWindowsSpyBlocker v4.26 releases: Block spying and tracking on Windows
WindowsSpyBlocker is an application written in Go and delivered as a single executable to block spying and tracking on Windows systems. The initial approach of this application...
-
 5.1K
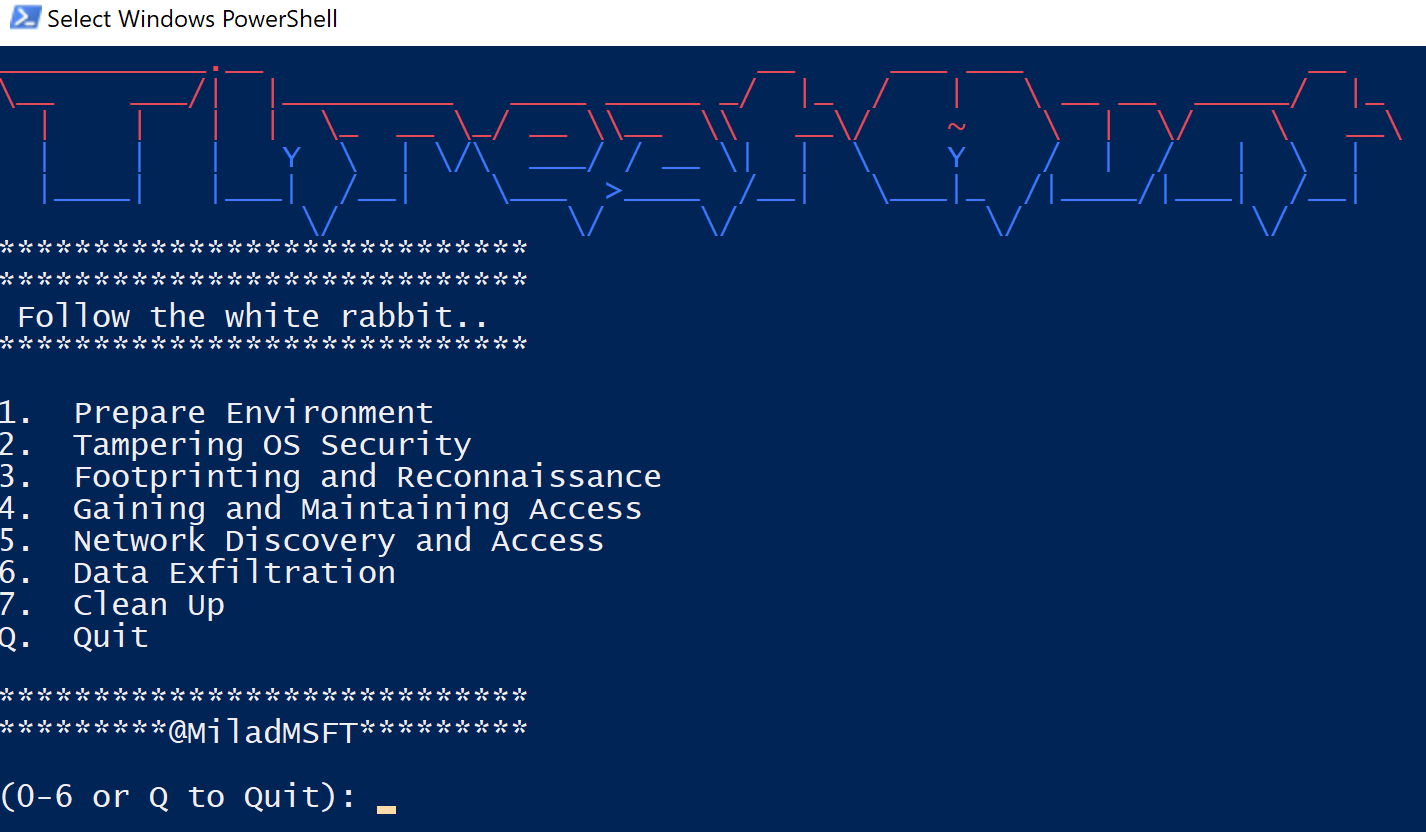
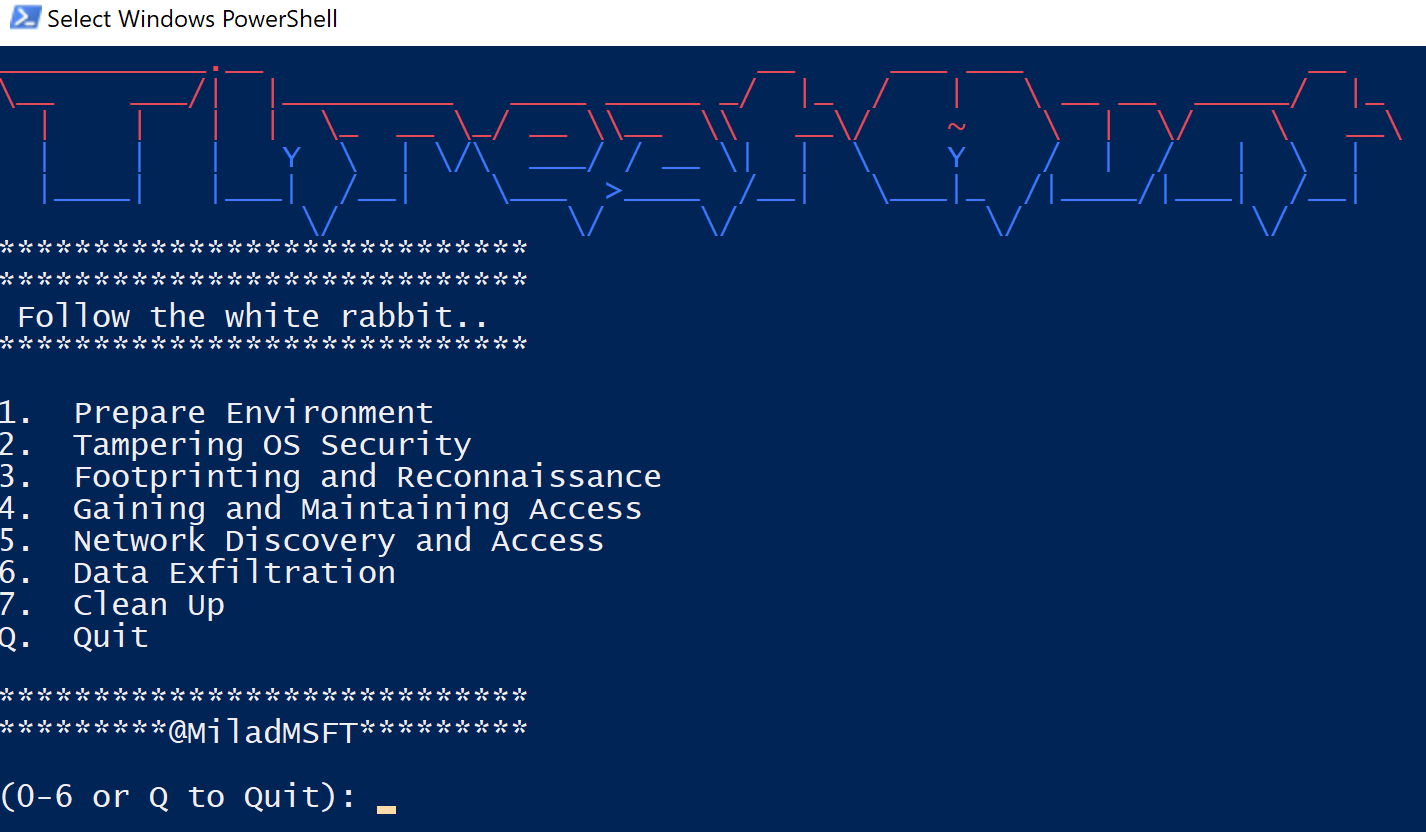
5.1KThreatHunt: PowerShell repository to train your threat hunting skills
ThreatHunt is a simple PowerShell repository that allows you to train your threat hunting skills. ThreatHunt allows you to simulate a variety...
-
 3.9K
3.9KReconPi – Set Up Your Raspberry Pi To Perform Basic Recon Scans
ReconPi – A lightweight recon tool that performs extensive reconnaissance with the latest tools using a Raspberry Pi.Start using that Raspberry Pi...
-
 742
742CAINE 11 – GNU/Linux Live Distribution For Digital Forensics Project, Windows Side Forensics And Incident Response
CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project. Currently, the project manager is Nanni Bassetti...
-
 3.0K
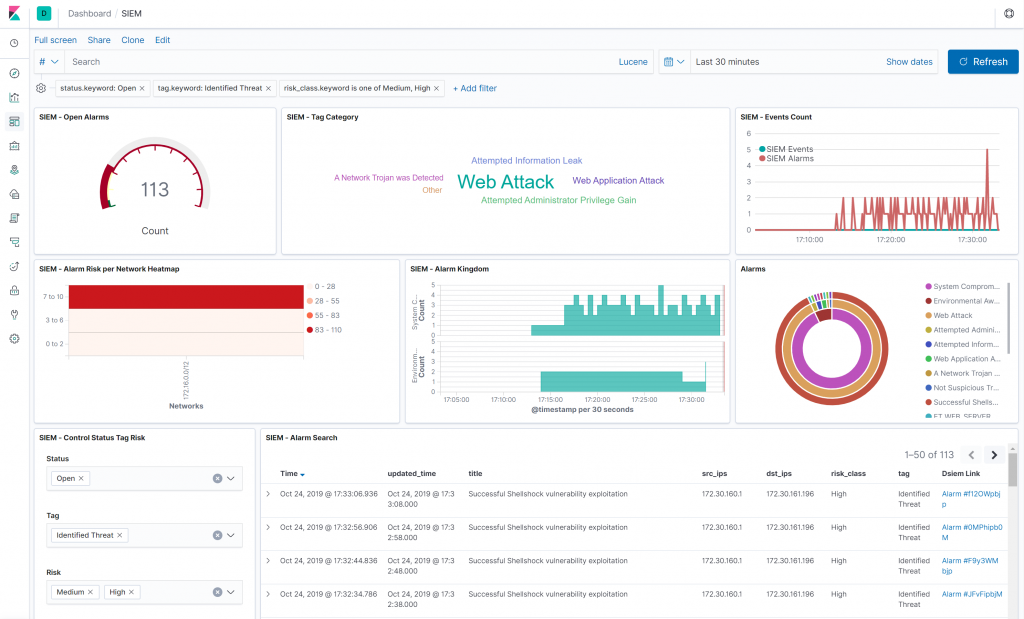
3.0K[Blackhat Europe tool] dsiem: Security event correlation engine for ELK stack
Dsiem Dsiem is a security event correlation engine for ELK stack, allowing the platform to be used as a dedicated and full-featured SIEM system. Dsiem...
-
 4.3K
4.3KNgrev – Tool For Reverse Engineering Of Angular Applications
Graphical tool for reverse engineering of Angular projects. It allows you to navigate in the structure of your application and observe the...
-

 2.3K
2.3KHull Man Sentenced for Reselling Drugs from the Darkweb
A young man from Hull, United Kingdom was sentenced to 3 years in prison for selling ecstasy and ketamine sourced from the...
-
 661
661pylane: python vm injector with debug tools, based on gdb
pylane Pylane is a python vm injector with debug tools, based on gdb and ptrace. It uses gdb to trace python process,...
-
 4.8K
4.8KFunctrace – A Function Tracer
functrace is a tool that helps to analyze a binary file with dynamic instrumentation using DynamoRIO (http://dynamorio.org/).These are some implemented features (based...
-
 1.2K
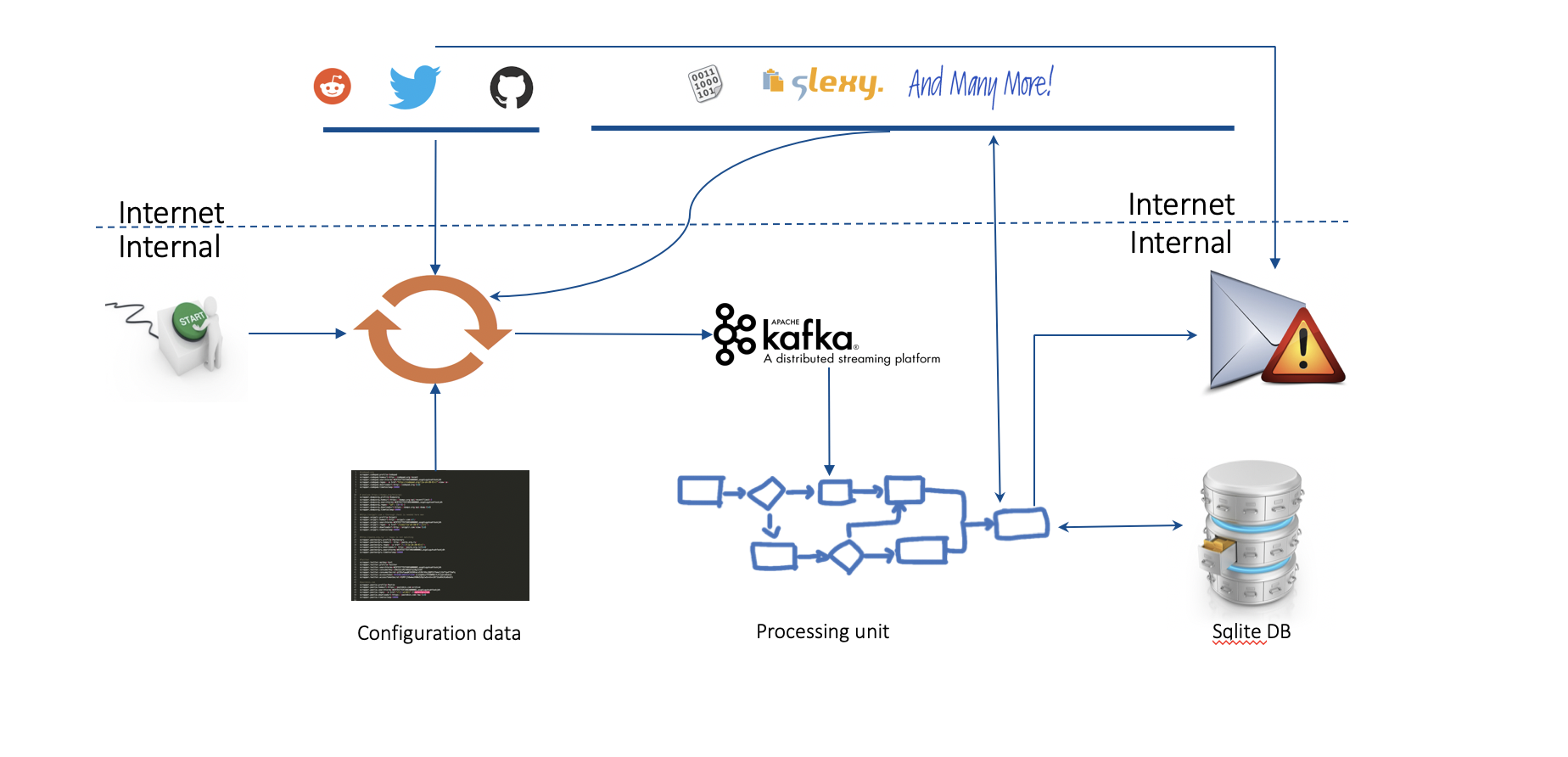
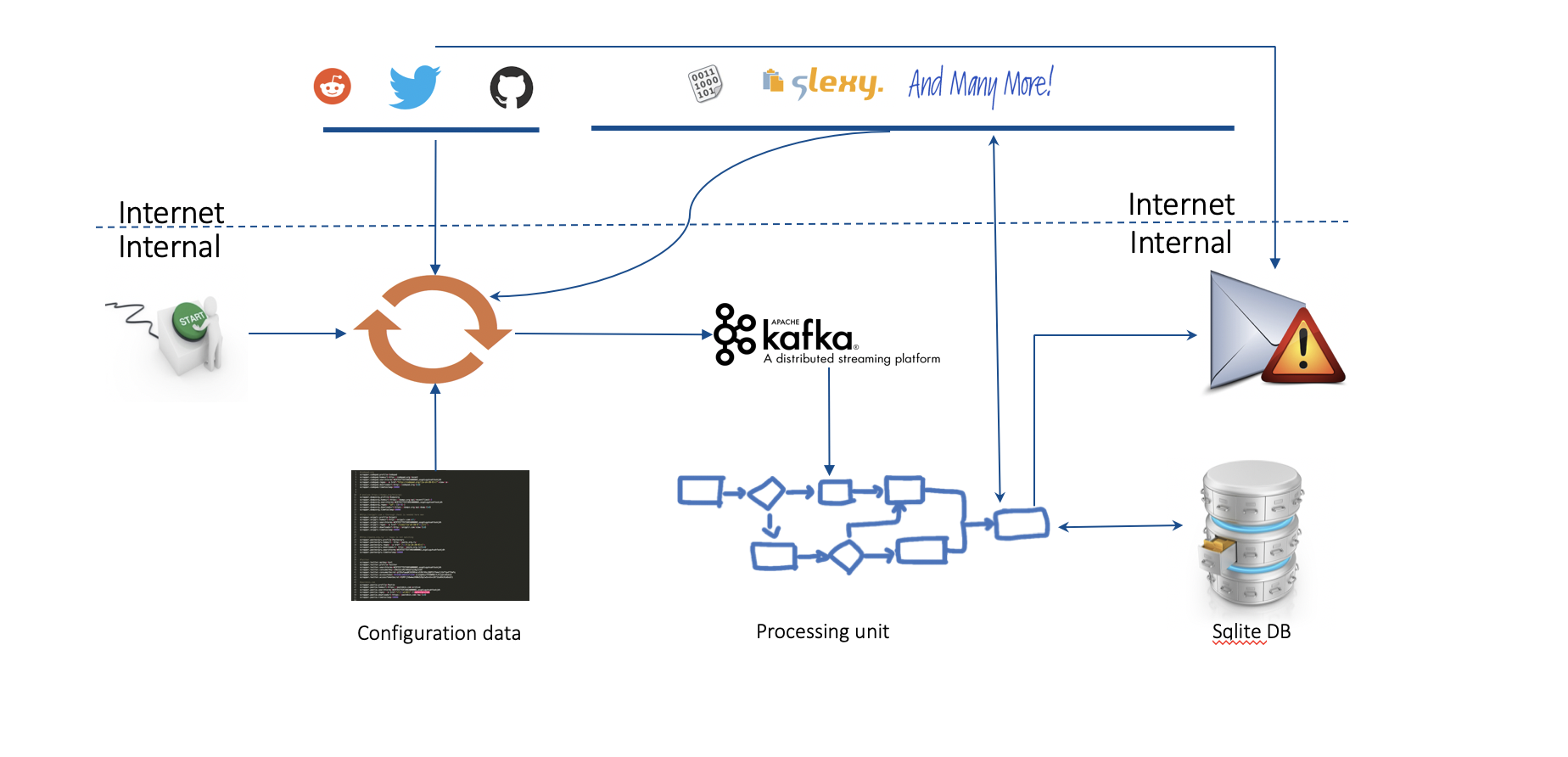
1.2K[BlackHat Europe tool] Real Time Threat Monitoring Tool
Real Time Threat Monitoring Tool V2.0 Monitoring possible threats of your company on the Internet is an impossible task to be achieved...
-
 3.3K
3.3KRed Hat Enterprise Linux 7 and CentOS 7 receive critical kernel security update
Red Hat and CentOS have announced the availability of important kernel security updates for their Red Hat Enterprise Linux 7 and CentOS...
-

 3.7K
3.7KApk-Mitm – A CLI Application That Prepares Android APK Files For HTTPS Inspection
A CLI application that automatically prepares Android APK files for HTTPS inspection Inspecting a mobile app’s HTTPS traffic using a proxy is...
-

 613
613Two Sentenced to Prison for Liverpool Darkweb Drug Operation
Two were sentenced prison for running a “major darkweb dug operation” out of their Liverpool home. According to evidence revealed in court,...
-
 4.0K
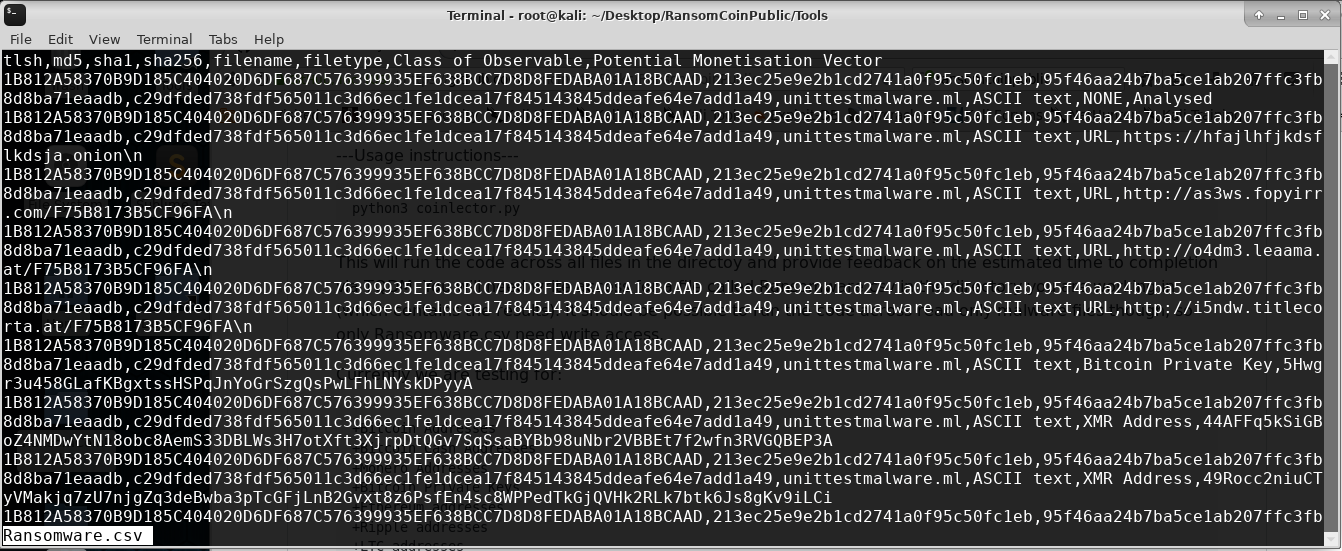
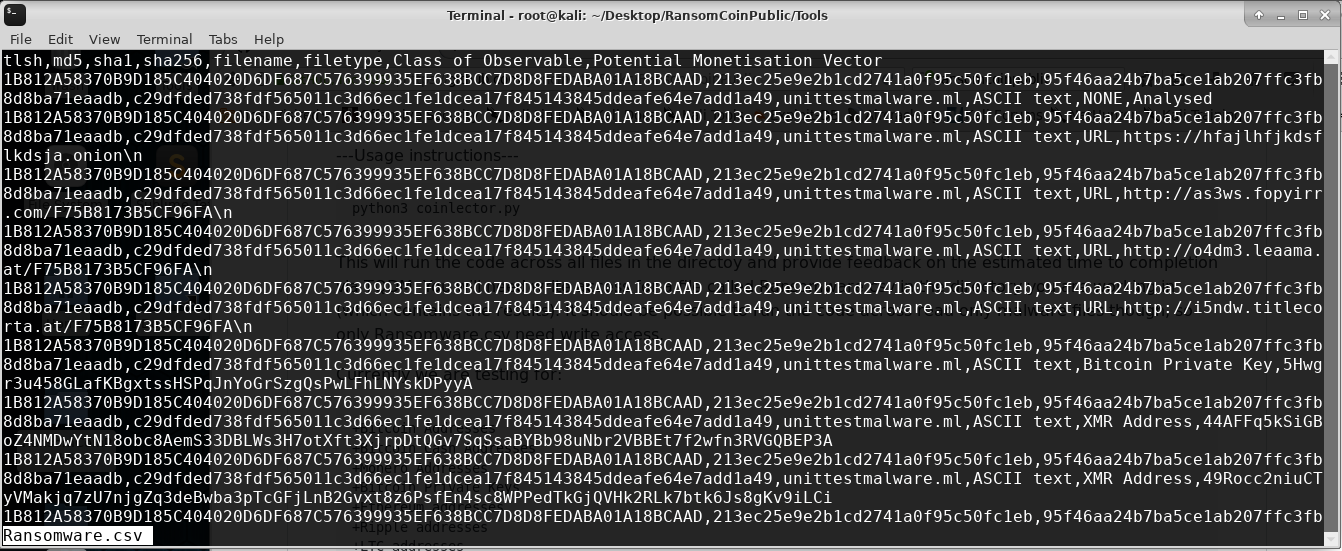
4.0K[Blackhat Europe tool] RansomCoin: extract cryptocoin addresses and other indicators of compromise from binaries
RansomCoin Extracting metadata and hardcoded Indicators of Compromise from ransomware, in a scalable, efficient, way with cuckoo integrations. Ideally, is it run...
-
 4.4K
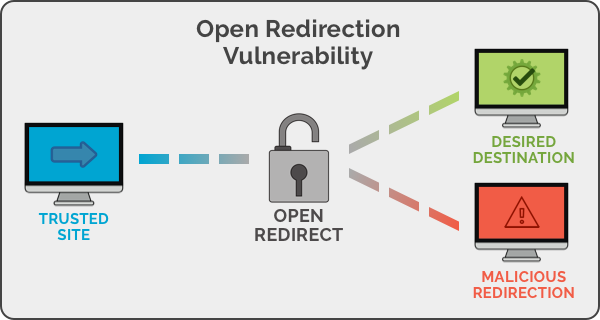
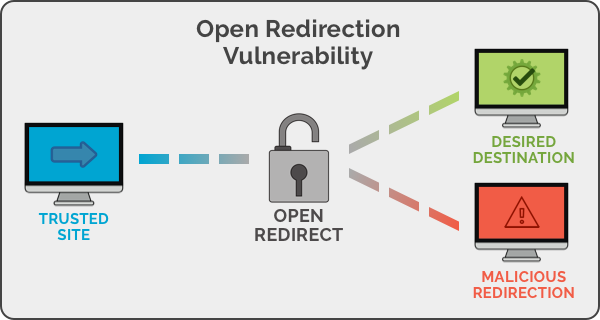
4.4KOpen Redirect Payload List
Unvalidated redirects and forwards are possible when a web application accepts untrusted input that could cause the web application to redirect the...
-
 4.2K
4.2KWhat is the CyberSec Feature?
With each passing year, cybersecurity concerns increase in terms of the number of threats and their severity. Hackers can and will cause...
-

 1.7K
1.7KAntiDisposmail – Detecting Disposable Email Addresses
Antbot.pw provides a free, open API endpoint for checking a domain or email address against a frequently-updated list of disposable domains. CORS...
-

 4.9K
4.9KCustoms Busted a Darkweb Drug Ring in the Czech Republic
Law enforcement in the Czech Republic arrested five individuals for running an international drug trafficking ring out of Brno. The group allegedly...
-
 2.4K
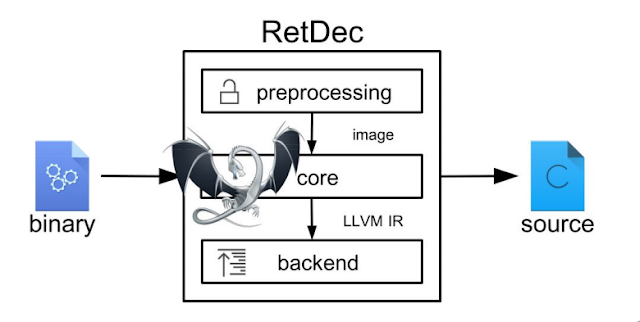
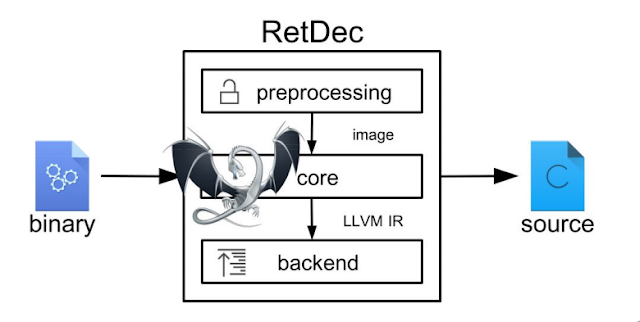
2.4KRetDec – A Retargetable Machine-Code Decompiler Based On LLVM
RetDec is a retargetable machine-code decompiler based on LLVM.The decompiler is not limited to any particular target architecture, operating system, or executable...
-

 2.1K
2.1KSeeker v1.2.1 – Accurately Locate Smartphones Using Social Engineering
Concept behind Seeker is simple, just like we host phishing pages to get credentials why not host a fake page that requests...






