Incidents
-

 245
245SpyNote Android Trojan Builder Leaked
Our team recently discovered a new Android Trojan called SpyNote which facilitates remote spying. The builder, which creates new versions of the...
-
 192
192QRLJacking — Hacking Technique to Hijack QR Code Based Quick Login System
Do you know that you can access your WeChat, Line and WhatsApp chats on your desktop as well using an entirely different,...
-

 144
144TPB Founder Peter Sunde — “I’ve Been Saying For Years That I Want The Pirate Bay To Shut Down”
Short Bytes: Peter Sunde, co-founder of The Pirate Bay, talked about the decentralization of the torrent ecosystem on TorrentFreak’s audio podcast series...
-

 121
121Another media-stealing app found on Google Play
The HTML Source Code Viewer app by Sunuba Gaming poses as a development tool then steals pictures and videos from mobile devices....
-
 224
224Attack With WPAD Protocol and PAC Files Can Leak HTTPS Traffic
Attackers can collect your HTTPS Web traffic history. Alex Chapman and Paul Stone from Context, a UK cyber security consultancy firm, have discovered...
-

 216
216Keys to Chimera ransomware leaked
When ransomware authors compete on the black market, sometimes victims benefit. This time we got access to private keys of the Chimera...
-

 85
85Hackers steal 1.6 million Clash of Kings forum accounts
The official forum for the popular mobile game Clash of Kings is the latest to fall victim to a cyberattack after a...
-
 89
89Bug hunter downloaded the entire Vine source code
The Indian security expert and bug hunter Avinash has accessed and downloaded the entire Vine source code and it was really easy....
-

 275
275Meet One of the Anonymous Hackers Bombarding ISIS Websites With DDoS Attacks
Softpedia spoke with Rebirth, co-founder of BinarySec. The Anonymous #OpISIS campaign seemed at one point to have slowly died out after the Charlie...
-

 202
2023D printing of a dead man’s fingers allows unlocking his phone
The US federal authorities asked a 3D printing lab to recreate a dead man’s fingers to unlock his smartphone … will it...
-

 181
181Snowden Presents Anti-Spying iPhone Case Attachment
Device was specifically designed for journalists. Infamous NSA whistleblower Edward Snowden and hardware hacker Andrew ‘bunnie’ Huang have presented today at MIT’s Media...
-

 258
258How Apple And Facebook Got KickassTorrents Founder Arrested
Short Bytes: The founder of the world’s largest torrent hosting website KickassTorrents is now behind the bars. The cause of his arrest...
-

 100
100Why It May Be Worth Paying The Ransom In A Ransomware Attack
Australia is being hit hard by ransomware attacks and we’ve heard a lot of security vendors advise against paying the ransom that...
-
 201
201DDoS Attack Takes Down US Congress Website for Three Days
Library of Congress and Copyright Office also affected. The US Congress has just recovered after a three-day-long DDoS attack that has crippled its...
-
 90
90Steem Social Network Hacked, User Funds Stolen, DDoS Attack Followed After
Company promises to refund affected users. Steemit, a relatively small social network, announced last Thursday, on July 14, that an unknown attacker had...
-
 97
97Hacking 3D Printers Is Just Another Way to Destroy Modern Companies
Nothing is safe nowadays, not even 3D printers. A hacker could breach a company’s network, hack into a 3D printer, and alter small...
-

 88
88Hackers Steal Data from Polish Defence Ministry and Ask for $50,000 Ransom
Some of the data looks legit, some looked fake. A group of hackers who call themselves “Pravyy Sector” [Right Sector] are extorting...
-
 149
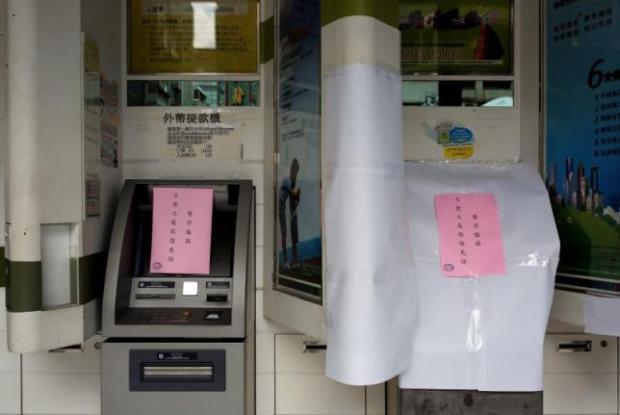
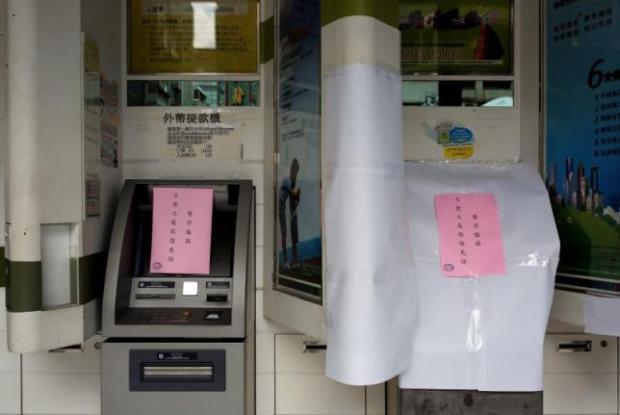
149Russians and Malware Involved in $2 Million ATM Heist in Taiwan
ATM transactions suspended in Taiwan for two days. Taiwan’s top eight banks have suspended operations on 900 ATMs after crooks stole NT$70 million...
-
 84
84Now it’s easy to see if leaked passwords work on other sites
Freely available tool follows the release of more than 642 million account credentials. Over the past few months, a cluster of megabreaches...
-
 157
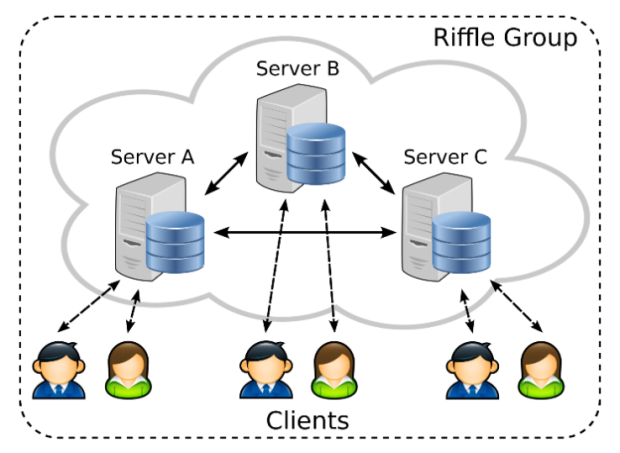
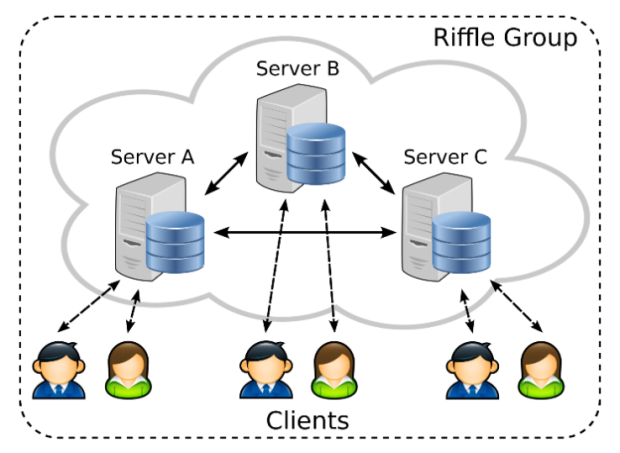
157MIT’s anonymous online communications protocol Riffle could beat Tor at its own game
Tor has been the go-to for anonymous communication online for years now — and that has made it one of the juiciest...
-
 217
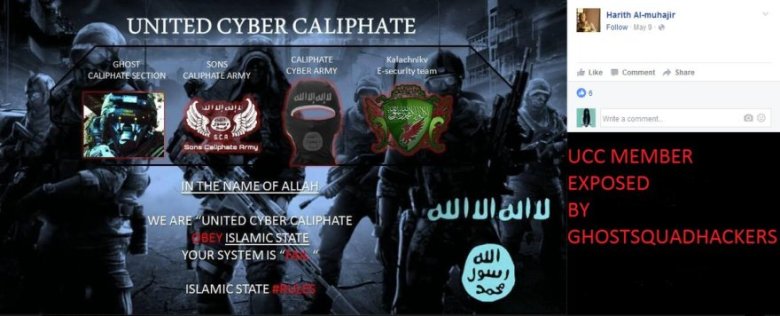
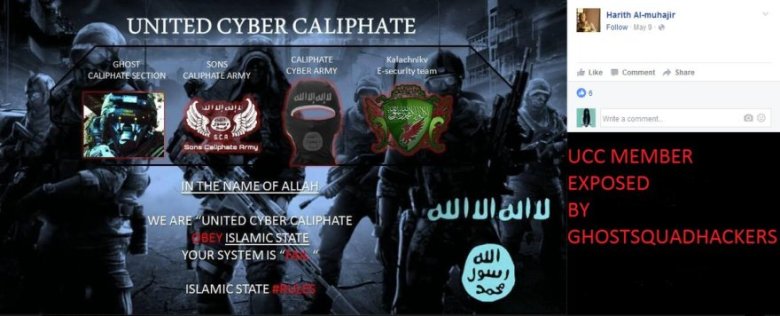
217Ghost Squad hackers dox United Cyber Caliphate including Mauritania Attacker
Hacktivists from Ghost Squad Hacker group made revealed the identities of hackers affiliated with the ISIS cyber army called United Cyber Caliphate....






