Incidents
-

 82
82Operator of Online Payment Company Indicted for Stealing From Customers
Crook stole $22 million via online payments company. Gareth David Long, 37, a British man living in Las Vegas, USA, was indicted by...
-

 75
75Imgur’s Video to GIF Feature Abused to Send Spam and Shut Down the Service
Researchers earned $2,000 for his discovery. Imgur’s staff have closed a critical security issue that allowed attackers to use its service to send...
-

 162
162This Chrome Extension is stealing bitcoins from users
BitcoinWisdom Ads Remover extension for Chrome is reportedly stealing bitcoins from users. Bitstamp, a bitcoin exchange portal based in Slovenia, has issued a warning...
-

 169
169Typos stopped hackers stealing $1bn from Federal Reserve Bangladesh account
Hackers who allegedly infiltrated the Federal Reserve Bangladesh’s account were attempting to steal almost $1 billion, but typos thwarted the plan. This...
-

 203
203The majority of CCTV cameras can be easily hacked
Your CCTV camera might make you feel physically safer, but after reading this article, it will sure make you feel virtually vulnerable....
-
 104
104One of the greatest art heists of our time was actually a data hack
The story behind the Nefertiti Hack just got a lot stranger. But is it a hoax? Last month, two artists grabbed headlines across...
-

 153
153Phishers are creating YouTube channels to document their attacks
Phishing attacks have linked back to YouTube channels where phishers explain their attacks and promote their tools while looking for buyers. Symantec...
-

 81
81Internet-Connected Trucks Can Be Tracked and Hacked, Researcher Finds
Insecure configurations expose car telematics to hacking. Industrial vehicles like trailer trucks, delivery vans, or buses that have an Internet connection, can be...
-
 185
185Operation Transparent Tribe targets Indian diplomats and military
ProofPoint uncovered a new cyber espionage campaign dubbed Operation Transparent Tribe targeting Indian diplomatic and military entities. A new cyber espionage campaign...
-

 173
173New attack steals secret crypto keys from Android and iOS phones
Researcher-devised exploit threatens Bitcoin wallets and other high-value assets. Researchers have devised an attack on Android and iOS devices that successfully steals cryptographic...
-

 170
170US DoD invites a restricted number of hackers to Hack the Pentagon
Hack the Pentagon – DoD would invite outside hackers to test the cybersecurity of some public US Defense Department resources as part...
-

 123
12333 percent of all HTTPS websites open to DROWN attack
Security experts presented the DROWN attack that exploits a new critical security vulnerability affecting the OpenSSL. Security experts have discovered a new...
-

 286
286Payroll data leaked for current, former Snapchat employees
Incident occurred after employee responded to e-mail phish scam. In a blog post on Sunday, Snapchat executives revealed that the payroll data of...
-

 144
144Discover how many ways there were to hack your Apple TV
Apple has patched more than 60 vulnerabilities affecting the Apple TV, including flaws that can lead to arbitrary code execution and information...
-

 147
147Group Behind the Sony Hack Is More Dangerous Than Previously Thought
Researchers blow the lid on one of the most dangerous and well-organized cyber-espionage groups around. Only after four different cyber-security firms teamed...
-
 270
270Anonymous hacked the France’s Ministry of Defense portal CIMD (Centre d’Identification des Materiels de la Defense)
Anonymous hacked the CIMD portal managed by the France’s Ministry of Defense to protest against French foreign arms trade operations. The Anonymous...
-

 86
86HTTP GZIP Leaks Data on the General Location of Tor Websites
Some Tor servers may leak timezone info via gzipped files. Jose Carlos Norte, developer for the eyeOS virtual desktop project, has discovered an...
-

 288
288Anonymous took down several government websites of Saudi Arabia
Anonymous launched a series of cyber attacks against government websites of Saudi Arabia to protest the execution of 47 people, including Mr....
-

 100
100NSA Data Center effect : This state experiences 300,000,000 hacking attacks a day
Utah state computer systems experiences 300 million hacking attacks a day due to NSA data center in the state. 300,00,000 hacking attempts in...
-
 85
85Man admits he stole nude celebrity pics from Apple and Gmail accounts
Phishing scheme gained illegal access to accounts storing 161 nude images. An Oregon man has admitted he tricked hundreds of people into divulging...
-
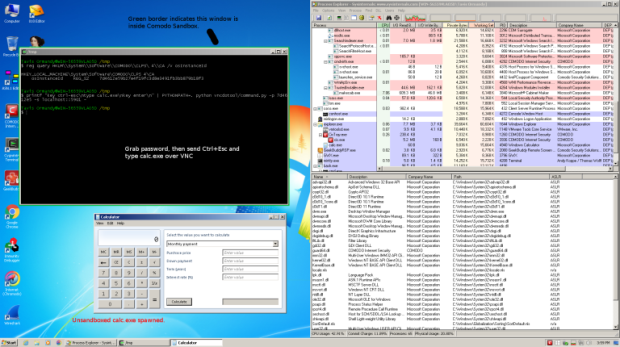
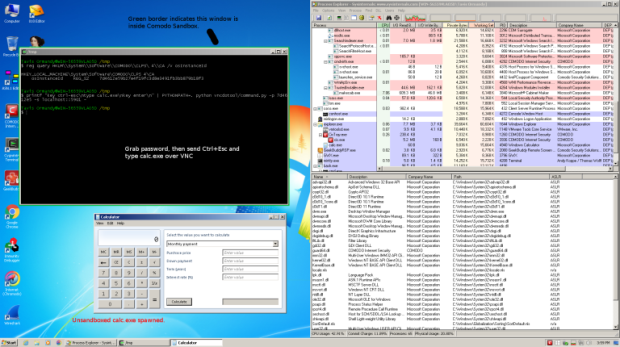 109
109Comodo Internet Security opened your PC to attackers
Comodo Internet Security, in the default configuration, installs an application called GeekBuddy that also installs a VNC server enabled by default. The hackers...






