Infosec
-

 407
407Shodan and Censys: Finding Hidden Parts On the Internet With Special Search Engines
Our digital lives connect massive things with the Internet. Starting with Smartphones, Wi-Fi routers, Surveillance Camera, Smart TV, SCADA networks and leading...
-

 431
4313 Reasons why SAAS Business need to Concentrate on website Security
Businesses that are growing are always trying to expand in all departments and to do that they need a website that portrays...
-
 256
256Zero-Day Attack Prevention: A Fundamental Pillar of Security
Preventing zero-day attack, one of a developer’s worst nightmares. In this guide, we’ll tackle the A to Zs of these attacks. Keeping...
-

 405
405Organization Cyber Disaster Recovery Plan Checklist
Calamity occurrence in any area, arising from natural or man-made causes, or by accident or negligence which results in substantial loss of...
-

 335
335How to Make a Dedicated Development Center with Cyber Security Principles
Are you looking for a team that can help find cyber attacks and issues in your network and eliminates them? Learn how...
-
 576
576Most Important Security Tools and Resources For Security Researcher and Malware Analyst
Security Professionals always need to learn many tools, techniques, and concepts to analyze sophisticated Threats and current cyber attacks. Hex Editors HxD...
-

 483
483Key Elements and Important Steps to General Data Protection Regulation (GDPR)
The General Data Protection Regulation (GDPR) applied on 25 May 2018, this new law applies to all companies that collect and process data...
-

 258
258Radio Tech Used to Hack Everything From Airplanes to Defibrillators
Earlier this year an experienced team of researchers at Northeastern University’s Khoury College of Computer Sciences in Boston proved that an airliner’s complex radio-navigation...
-

 303
303A Perfect Way to Start and Strengthen Your Cyber Security Career
Breaking into a cybersecurity career is no different than any other career path or profession. In fact, in some ways, we’d even...
-
 368
368Surprising Differences between TLS and SSL Protocol
TLS is simply a successor of SSL 3.0, TLS is a protocol which provides Data encryption and Integrity between communication channels. SSL...
-

 424
42410 Important Components of PCI Compliance Checklist for Protecting the Customers Payment Card Data
Customers are looking for services and products that they believe are suitable for them. At the same time, these people expect safer...
-
 356
356Securing your Linux Virtual Private Server | Top 5 Ways To Implement Better Server Security
Linux VPS servers are nowadays widely using cloud platform that has its own security futures compare to other most of its competitors. Storing...
-

 428
428DNS Security: How to Reduce the Risk of a DNS Attack
Domain Name System or DNS is one of the foundational elements of the entire internet; however, unless you specialize in networking, you...
-
 305
3055 Methods to Secure Your Company’s Data from Cybercriminals
Your data is a big part of your company. There are a hundred ways to immediately lose all of them and that...
-

 305
305Employees Actively Seeking Ways to Bypass Corporate Security Protocols in 95 % of Enterprises
Nowadays cyber incidents activities such as data theft, insider threat, malware attack most are significant security risks and some it caused by the...
-

 266
266Most Important Checklist for Security Leakage Before Initiating Data Migration in Your Organization
Security leakage is a great concern when it comes to data migration. It not only hampers organizational reputation but can jeopardize the...
-

 252
252What Security Checklist Do You Need to Pay Attention When Choosing Web Hosting
If you own a website, security is one of the factors you can’t mess around with. Choosing a plan that doesn’t offer...
-
 431
431New Google Dorks List Collection for SQL Injection – SQL Dorks 2019
Google helps you with Google Dorks to find Vulnerable Websites that Indexed in Google Search Results. Here is the latest collection of...
-

 354
354OWASP Top 10 Proactive Security Controls For Software Developers to Build Secure Software
Proactive Controls for Software developers describing the more critical areas that software developers must focus to develop a secure application. The OWASP...
-
 234
2345 Significant Reasons Why You Should Use a VPN for Your Business
VPN or virtual private network is a way to connect various networks using the internet. It uses security protocols which allows authenticity...
-
 275
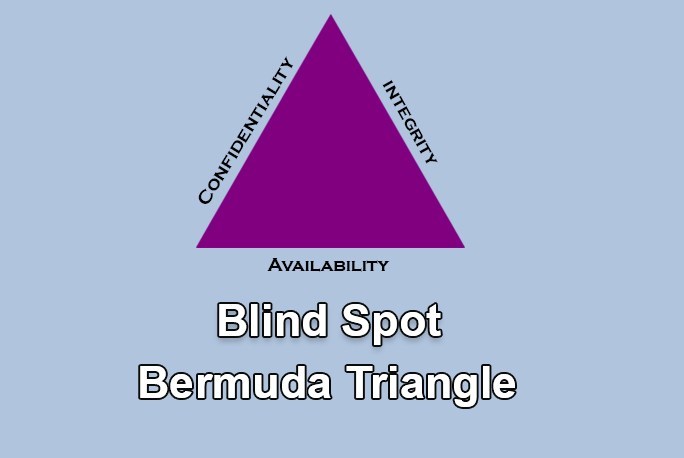
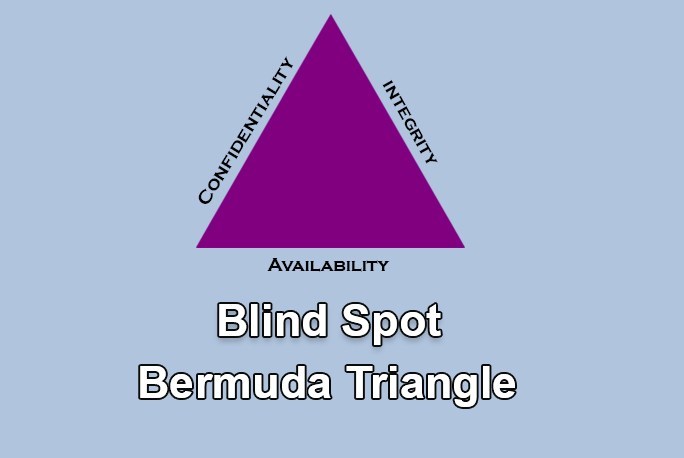
275CIA Triangle – Most Important Security Challenge with Organisation Insider Threats
Inspection in detail is available for Packet’s behaviour, but unfortunately, there is no possibility or means to inspect a person’s Intention. (...






