Infosec
-

 251
251Most Important Cyber Attack Techniques that often used by Hackers
The cyber attack occurs on a daily basis, and these can range from attacks on tech giants to individuals falling foul to...
-
 266
266What is Single Sign-on (SSO) ? – Solution to Ensure Your Company Data Security
Single Sign-on is a method of authentication process that helps to log in multiple application using single login credentials. Security is enhanced...
-

 218
218One-Way vs Two-Way Syncing: What’s the Difference?
Do you know that you can synchronize files between your devices? You can access your files from virtually anywhere, whether you’re offline...
-
 546
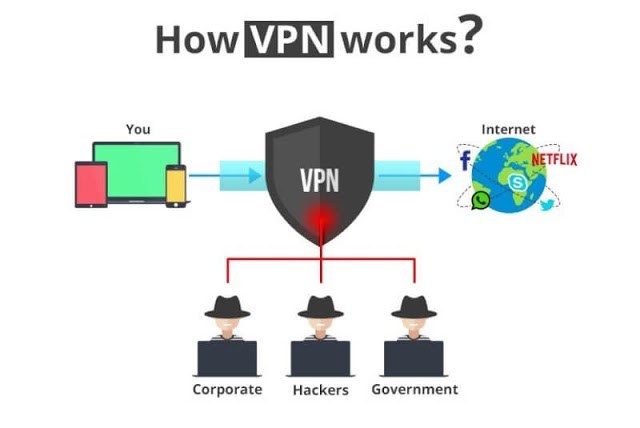
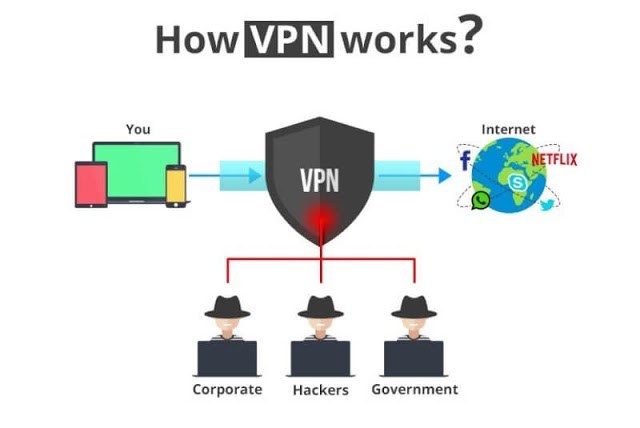
546Virtual Private Network: What is it and Why is it So Important To Protect Your Privacy?
Computers and the Internet have become one of the main means of transmitting and processing information. Most of the information on the...
-
 250
250The Benefits of VoIP Home Phones – Avoid Hackers to Tap Your Phone calls
VoIP phone, or voice over Internet Protocol phones, are telephones that transmit and receive calls through the IP network such as the...
-

 300
300Top 500 Most Important XSS Script Cheat Sheet for Web Application Penetration Testing
XSS is a very commonly exploited vulnerability type which is very widely spread and easily detectable. Here we are going to see...
-

 354
354Most Important Computer Forensics Tools for Hackers and Security Professionals
Computer Forensics tools are more often used by security industries to test the vulnerabilities in network and applications by collecting the evidence...
-

 224
224Protect Yourself from Phishing attempts, Malware & ads Trackers Using Surfshark VPN’s CleanWeb
Nowadays all our activities highly depend on the Internet that includes shopping financial services, communication, entertainment and number of other services. The...
-

 352
352Intrusion Detection System (IDS) and Its Detailed Working Function – SOC/SIEM
Detection Methods An IDS can only detect an attack. It cannot prevent attacks. In contrast, an IPS prevents attacks by detecting them...
-

 287
287Hacking vs Spying: How Puzzling it is to Find the Hackers in Cyber World
The cyber world is a weird world and cell phones have added a new dimension to it. You can’t judge your friends...
-

 220
220Secure Cloud Migration Guide – Technical and Business Considerations
Cloud migration is the process of moving applications into the public and private cloud infrastructure to achieve cloud’s agility, resiliency and scalability drive business...
-
Patching The Vulnerabilities in Government Systems: Inside the New DHS Mandate
Software vulnerabilities and the need for patching have become a fact of life in the modern world. Everyone loves the capabilities provided...
-
What Could Blockchain Technology Do for Cybersecurity?
Blockchain Technology and the evolution of the digital world has led to a sizeable outbreak of sophisticated cyber attacks, with attackers continually...
-

 295
295CyberGhost VPN – The Best VPN to Protect Your Privacy Online with No Log Policy
A VPN, short for Virtual Private Network, protects you from threats on public networks, and it can also shield you wherever you...
-
 255
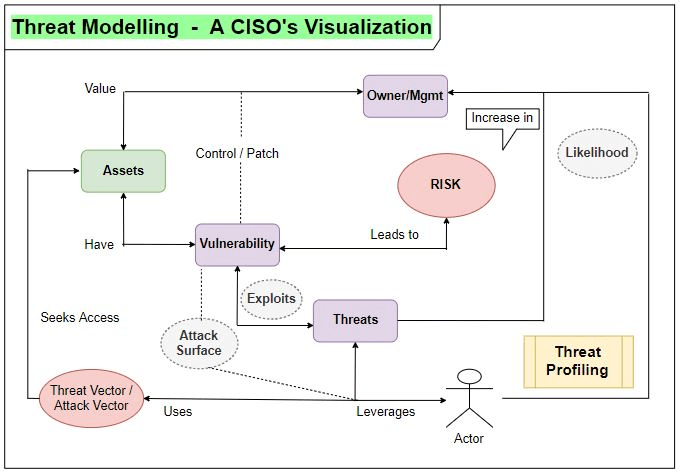
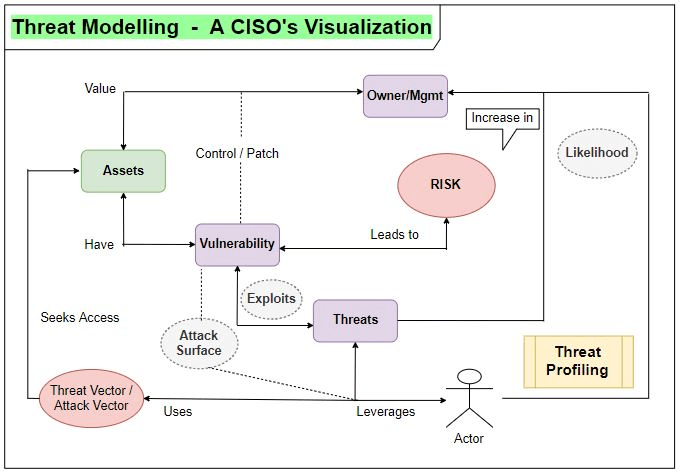
255Cyber Security is Not an Easy Game for CISO – It’s an Absolute End Game!
Let’s breakdown the little pieces and the critical dots to connect in the perspective of a CISO and a point-of-view from CyberSpace....
-

 305
305Is this website Safe : How to Check Website Safety to Avoid Cyber Threats Online
is this website safe ? In this digital world, Check website safety is most important concern since there are countless malicious websites...
-
 367
367Python for Data Science – Most Important Contribution of Data Science in Cybersecurity
Python for Data Science is one of the essential parts for those who all are willing to focus on Data science. There...
-

 250
250Most Important Data Protection Policies to Keeping Your Personal, Official, Financial Data Safe
The recent compromise of Facebook privacy has caused ripples of fear as to whether any data can be safe. Yes. You can...
-
 338
338Secure File Storage with Virtual Private Server (VPS)- A Detailed Guide
Storing data in the cloud such as Virtual Private Server (VPS) is a very important thing nowadays to secure the sensitive files...
-

 294
294FLASHMINGO – Free Threat Intelligence Tool for Malware Analysts’ to Analyse Flash Exploits
FireEye released a Free automated analysis tool FLASHMINGO, which enables malware analysts to detect suspicious flash samples and to investigate them. The...
-

 250
250Most Important Protection Approach to Prevent From Cyber Attack Via Internet at Work
As a normal Internet user, you have the sensible hope that your correspondences and transaction are private and secure in Internet security...






