Infosec
-
 281
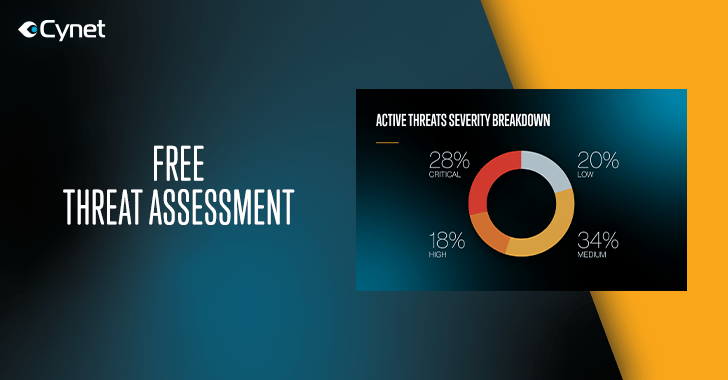
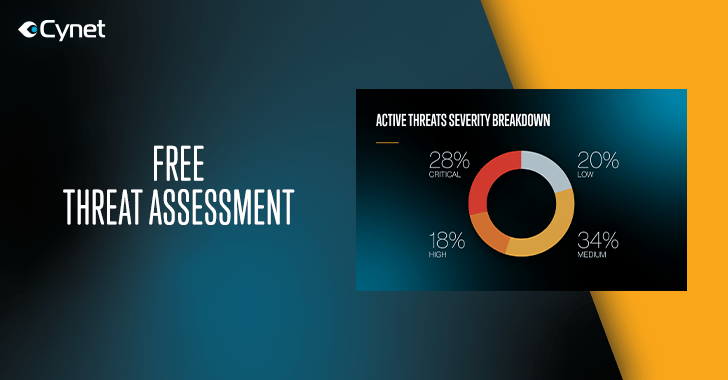
281Cynet Offers a Free Threat Assessment for Mid-Sized and Large Organizations – Take a Free Ride Now
Visibility into an environment attack surface is the fundamental cornerstone to sound security decision making. However, the standard process of 3rd party...
-

 298
298Conference Call Security Checklist – Best Practices in On-Call Security
When you’re hosting a conference call there’s usually a handful of things you’re worried about, the integral part in the Conference Call...
-
 193
193AI Can Help You Sleep Better But What about Security Concerns?
Have you ever wondered where that mid-afternoon crash comes from? Most of us experience it, and it makes for a miserable day...
-
 334
334Malicious Payload Evasion Techniques with Advanced Exploitation Frameworks
Sophisticated threats are Evolving with much more advanced capabilities and giving more pain for analysis even evade the advanced security software such...
-

 267
267Top 10 Best Proxy Server 2019 & Important Methods to Prevent Yourself From Hackers
Best Proxy Server has been used in enormous cases where some personal data or information have been misused illegally against an entity...
-
 400
400Advanced ATM Penetration Testing Methods
ATM Penetration testing, Hackers have found different approaches to hack into the ATM machines. Programmers are not restricting themselves to physical assaults,...
-

 242
242Operating Systems can be Detected using Ping Command
Operating Systems can be detected using Ping Command, Ping is a computer network administration software utility, which used to find the Availability...
-

 435
435TOP 11 Deep Web Search Engine Alternative for Google and Bing 2019
Deep Web Search Engine is an alternative search engine when we need to search something, then Google or Bing will the first...
-
 171
171Why You Should Not Use Pirated Software
If you do not have the money to immediately afford the piece of software you would like, there is a big temptation...
-

 179
179How Does Worlds Highly Secured Google Network Works ? Google’s Effort & Dedication
Google always Maintain the Extremely strong Cyber Security Culture for Data Security, Network Security, Cloud Security and Physical security. Google’s this extreme...
-
 310
310Information Security Risks With Vendors/3rd Parties – How Does it Matter for Banking & Financial Service Lines?
Information Security Risks assisted Business models for banking & financial services(BFS) institutions have evolved from being a monolithic banking entity to multi-tiered...
-

 260
2605 Steps How To Protect Your Company Infrastructure From Insider Threats
While most people worry about threats from hackers trying to breach their security from the outside, it’s just as, if not more,...
-
 351
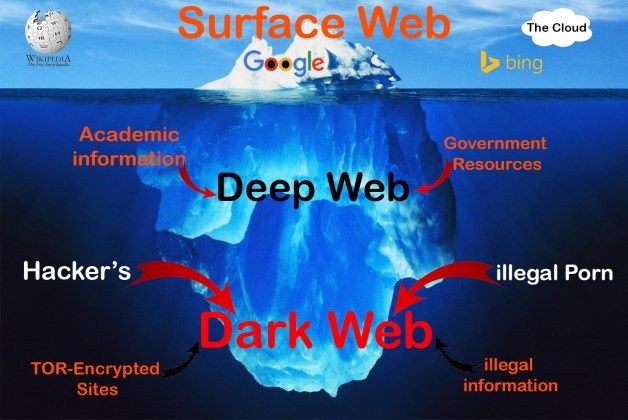
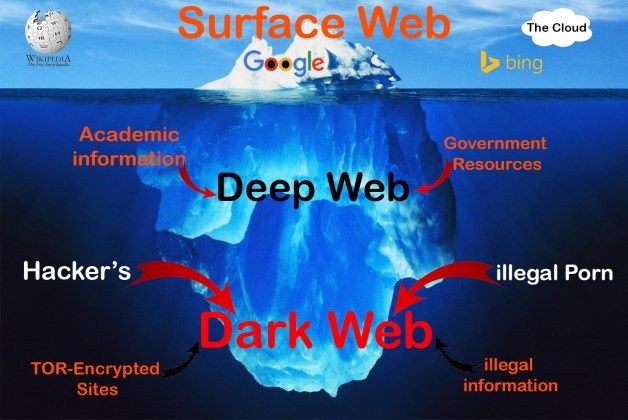
351How To Access Dark Web Anonymously and know its Secretive and Mysterious Activities
What is Deep Web The deep web, invisible web, or hidden web are parts of the World Wide Web whose contents are...
-
 228
2283 Ways to Protect Your Financial Information Online
One of the biggest fears when it comes to our precious finances is that they might be taken from us when we...
-

 238
238Insider Threat Detection Software: Protecting Against the Insider Threat – What You Should Know
Insider Threat is one of the dangerous threat actors for many organization and keeping your business protected from outside threats is hard...
-

 269
269Pentesting with Killcast Tool to Manipulate Chromecast Devices in Your Network
Recently HackerGiraffe and j3ws3r hijacked more than 70,000 Chromecasts to make people aware about the security risks of devices exposed to internet...
-

 256
256Simple & Important Ways to Protect your Business from Cyber Attacks
A vital role of the internet in completing various tasks, such as selling online goods, transferring funds is worth considering. With its...
-
 371
371TOR and VPN Anonymous Enough for Dark Web
Dark web is the World Wide Web content that exists on darknets, overlay systems which use public Internet yet we must particular...
-

 309
309Privacy Policy – Sensitive Information that Collected by Websites and Mobile Applications
A privacy policy is a statement that discloses some of the ways a party gathers, uses, discloses, and manages a customer or client’s data....
-
 294
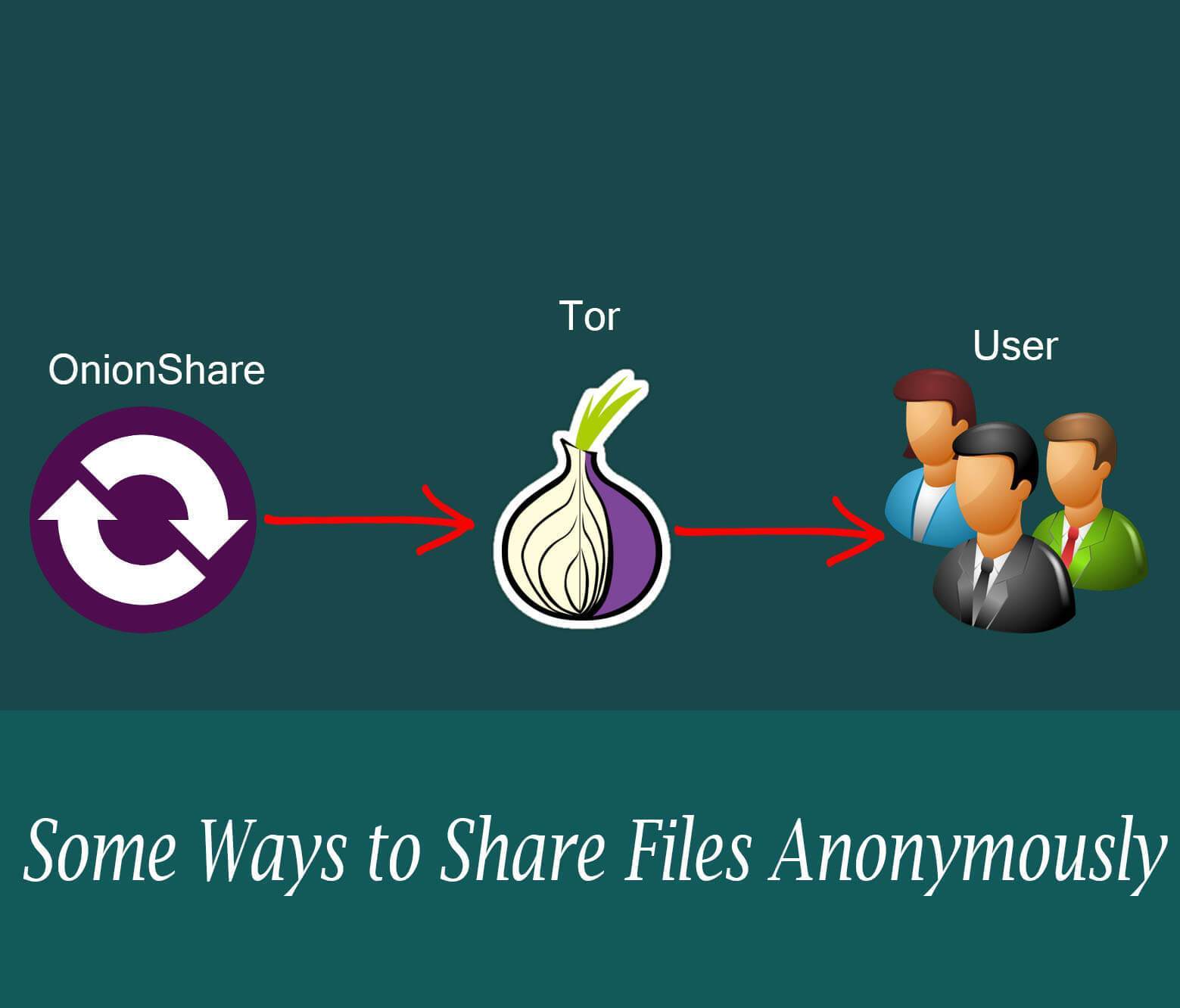
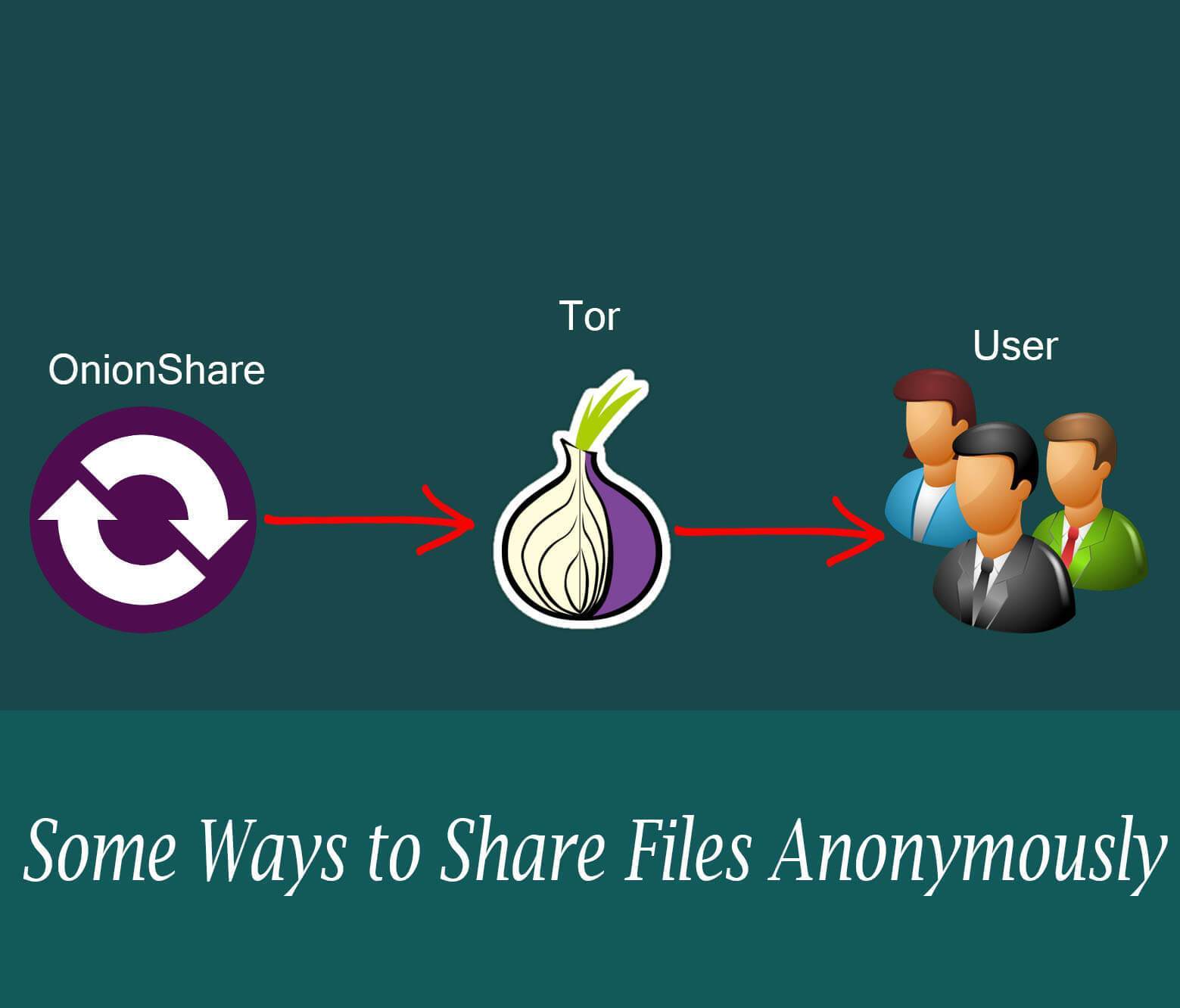
294Share Your Files Anonymously Using TOR and Onion Share
There is a bunch of reasons why people may look to share records anonymously, with the principal that rings a bell being...
-
 285
285Beware – Dangerous IoT Attacks Leads Some One to Hack and Control Your Car
The Internet of Things (IoT), responsible for connecting unthinkable things, now offers the possibility of connecting vehicles to the internet. With this,...






