Infosec
-
 245
245Cybersecurity Myths: Is Mac OS Safer Than Windows?
There seems to be a general belief among the people that Mac OS is safer than Windows. We know many reasons why...
-
 268
268Best Ways to Protect Data From Cyber Attack & Recover Your Deleted Data in Your Personal Computer
Cyber attacks handling and Data Recovery are the most stressful Operation in any of the organization and individual for both Personal and...
-
 223
223Protecting Big Data with Hadoop: A Cyber Security Protection Guide
Big Data analytics is emerging from today’s technology as people are demanding better ways to protect their Big data. Keep reading to...
-
 285
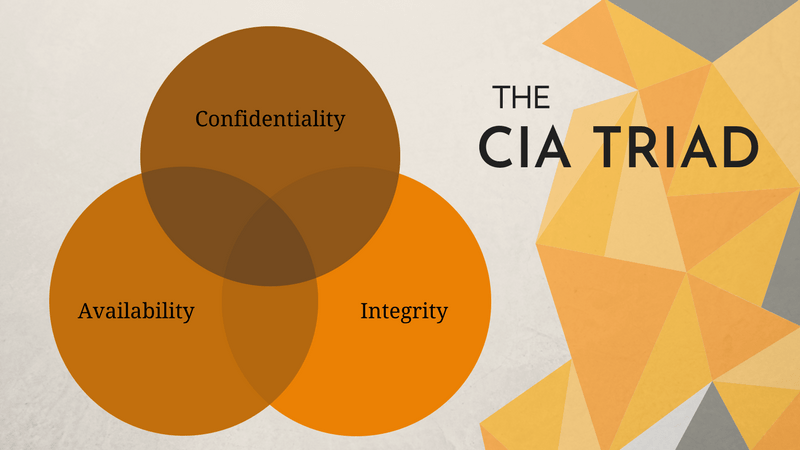
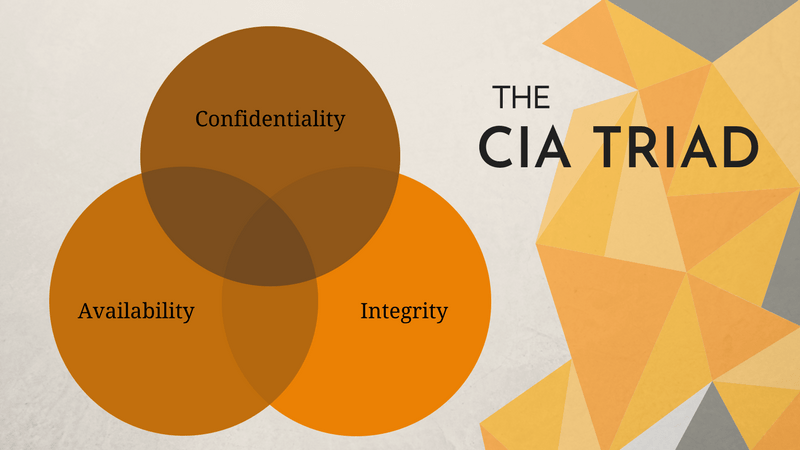
285Most Important Consideration of Confidentiality, Integrity, Availability (CIA Triad) to Avoid Organisational Data Breach
It is not wrong to say that information is power in today’s fast-changing competitive world. The one who has the right information...
-
 302
3022019 Israeli Security Expo Promises to Deliver Solutions to New-Age Threats
The 2019 International HLS & Cyber Expo is all set to be the largest cybersecurity conference and exhibition in Israel. Attracting global...
-

 323
3235 Most Important Things to Consider When Selecting a VPN for Streaming
In this day and age, when people are abandoning traditional cable or satellite television services at a faster rate than ever before,VPN...
-

 248
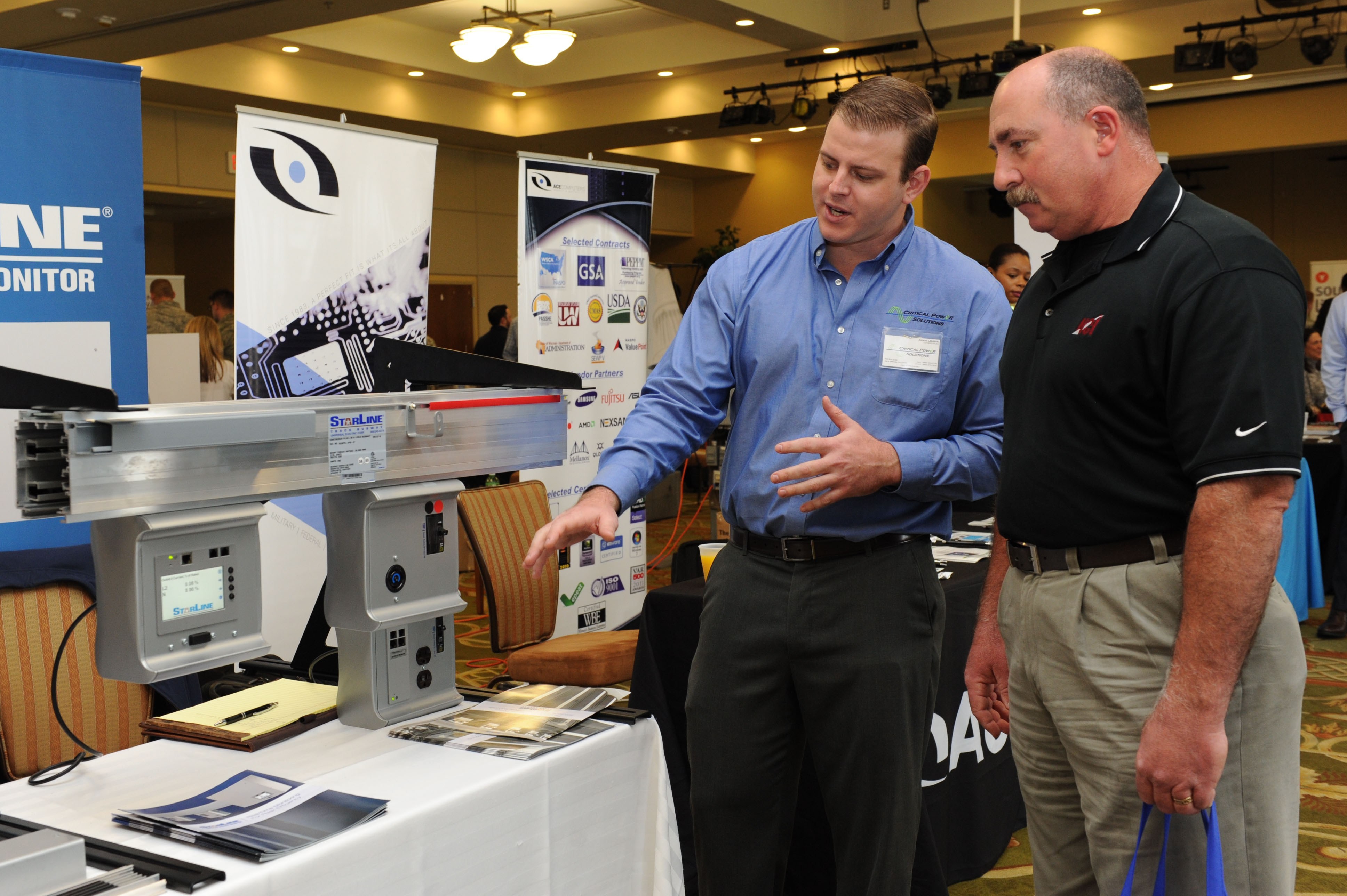
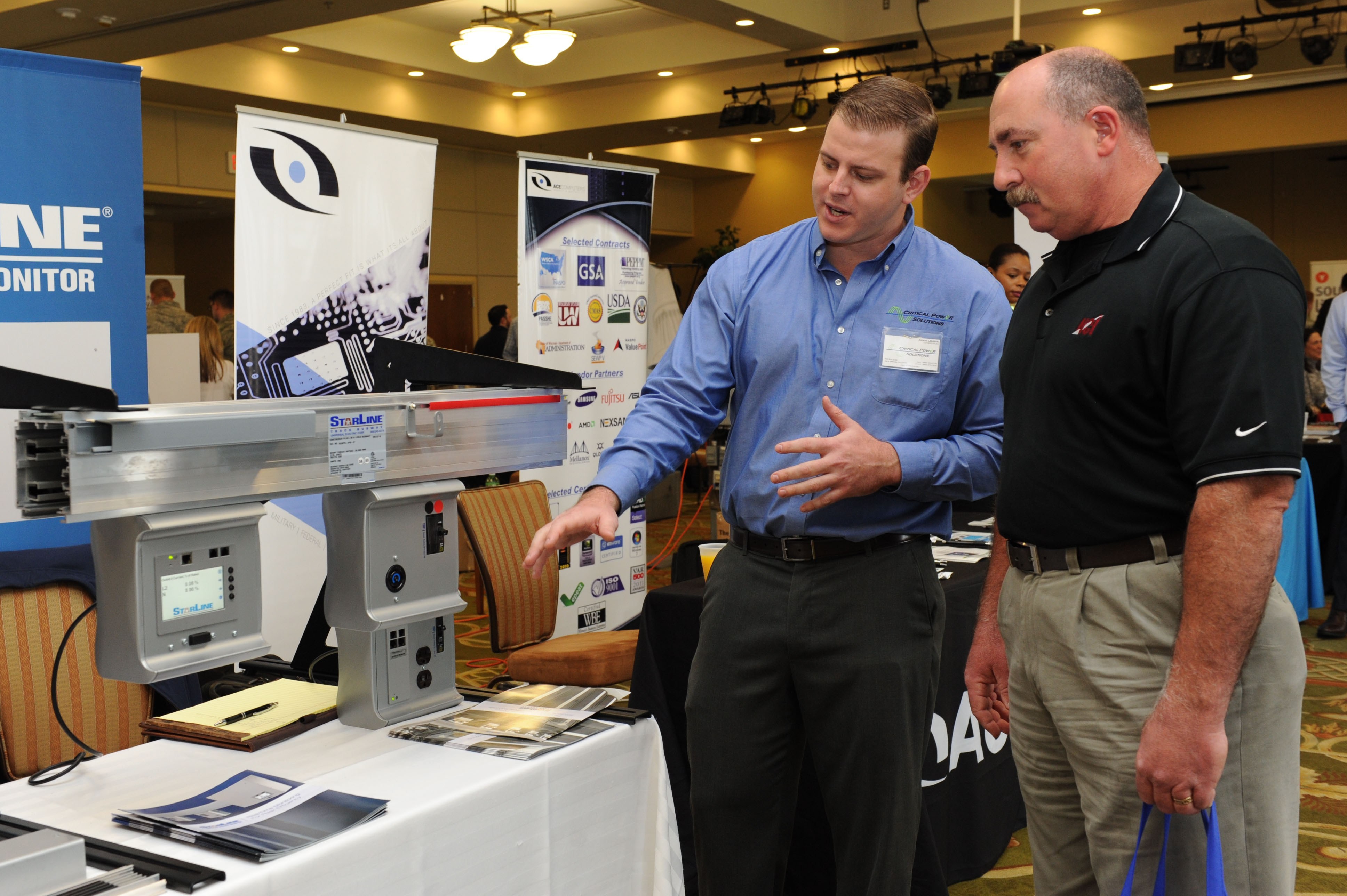
2485 Homeland Security Technologies That Might Be Commercialized
The federal government spends an upwards of $1 billion each year on unclassified cybersecurity research. This fuel a part of Homeland Security...
-

 316
316Cybersecurity in Trading and Forex: What You Need to Know
While cyber attacks occur almost daily in the world, sometimes with catastrophic results, we do not hear about successful attempts of disrupting...
-

 273
2734 Anti Drone Technologies That Can Neutralize Rogue Drones
civilians all over the globe. Go to any beautiful beach destination and you will find people flying drones in a bid to...
-
 486
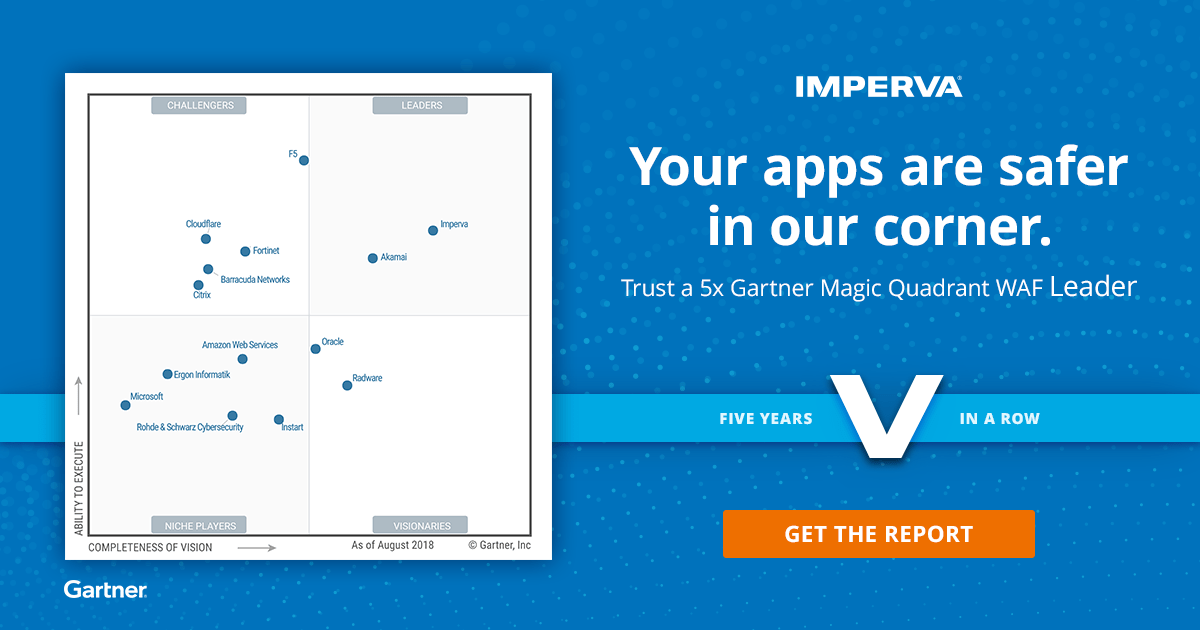
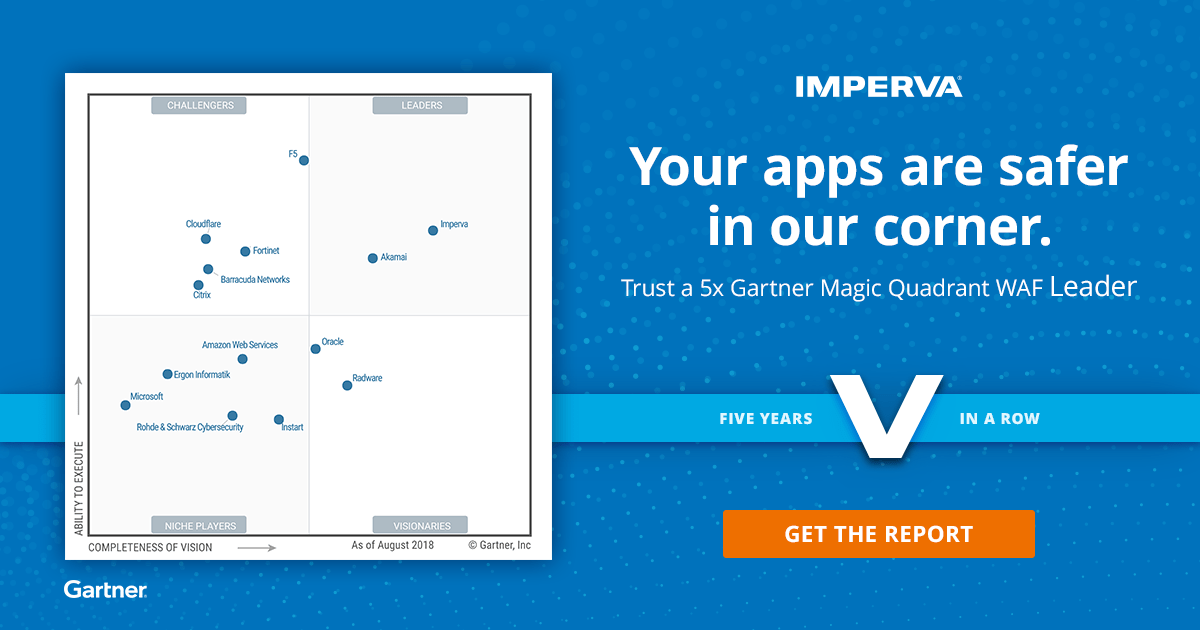
486Gartner Released Magic Quadrant for Web Application Firewalls – Imperva WAF Selected as a #1 Best WAF
Currently Web Application Firewall performing a major role in Web application protection since the web applications are primary targets for cybercriminals and...
-

 172
172Best Way to Accelerate and Secure Your Website From Top Common Web Threats
Web Applications Security becomes essential as more and more data gets stored in web applications. Web Security assessment is a wide-ranging process...
-

 368
368Best Way to Find the Stolen Android Phones with the Help of Google
One of the most devastating feelings in the world is your phone being stolen. In the past, there was no phone tracker,...
-

 324
324Most Important Cybersecurity Consideration to Secure Your Company’s Integrity
When it comes to cybersecurity then no any business would be able to ignore it! In fact, if we consider the reports...
-

 199
199Most Important Cybersecurity Risk Mitigating for Connected Vehicles
Staying connected when managing or owning a fleet is crucial. It is the only way to have real-time data and the monitoring...
-
 290
290Mega vs Dropbox : Most Important Cyber security Consideration in the Cloud
Mega vs Dropbox, If history is something to learn from, then we know there is not enough cybersecurity to protect us 100%...
-

 183
183Best Ways to Protect & Tracking Children’s Online Activities Using iPhone Keylogger
So you have decided to monitor someone’s activity via the iPhone. Well, you’re not alone. Fortunately, humanity has already invented software and...
-
 170
170Investing in Fraud Detection Software – Is It Worth the Expense?
Businesses are constantly trying to find better ways to fight fraud but one question many are left asking is ‘is fraud detection...
-
 359
359Globally Gas Stations are Extremely Vulnerable to Internet of Things (“IoT”) Cyber Attacks
2018 begins with the rise of the Internet of Things (” IoT “) which is based on the existence of an interconnection...
-

 352
352Most Important Consideration for Industrial Control System(ICS) Cyber Defense
It is Extremely challenging task to identify and successfully deploy an absolutely innovative and never-seen-before defense solution for Industrial Control System (ICS)....
-

 425
425The Cyber Risk of Online Gambling websites – Are Casinos Safe?
For online Gambling house, data protection is not only an obligation but also a necessary measure to retain customers and earn more business. After...
-

 294
294Why Using a VPS to Host your Own VPN is Safer than Using a VPN Service
VPN is basically a private network through which you can connect to the Internet. It makes your web traffic pass through encrypted...






