Malware
-
 182
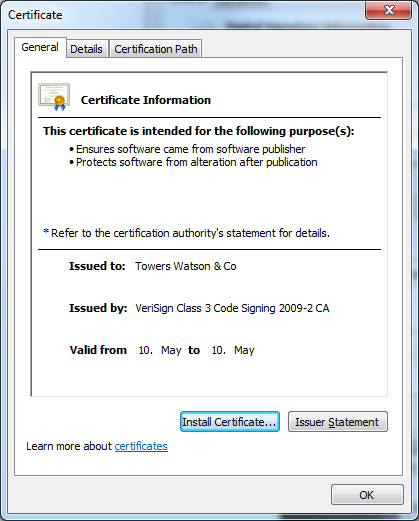
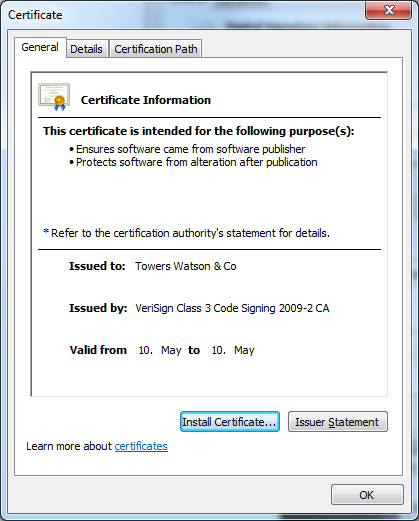
182Towering Qbot Certificates
New stolen digital certificates are used by the multi-purpose backdoor Qbot. The criminals behind the Qbot trojan are certainly not inactive. As...
-

 133
133PDF Trojan Appears on Mac OS X
A new trojan has been released targeting the Macintosh Chinese-language user community. The trojan appears to the user to be a...
-
Android banking malware in the wild
Recently, we’ve noted a steep rise in Android malware and predicted the rise in banking malware, now we see another example in...
-
 133
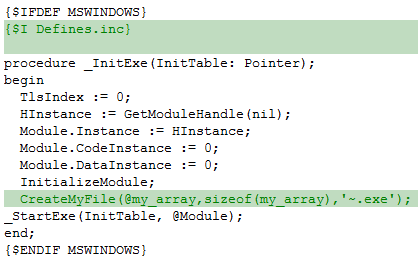
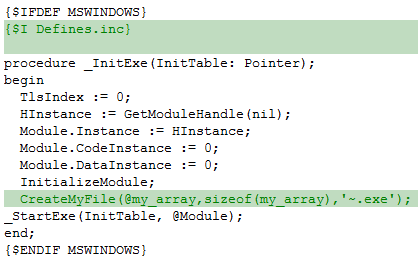
133The Induc Virus is back!
ESET has discovered a new version of the Delphi infector, Win32/Induc. Unlike its predecessors, however, this variant incorporates a seriously malicious payload...
-
 174
174Back to School Qbot, now Digitally Signed
The authors of Win32/Qbot (a.k.a. Qakbot) are back with new variants of this infamous malware, and this time the binaries are digitally...
-
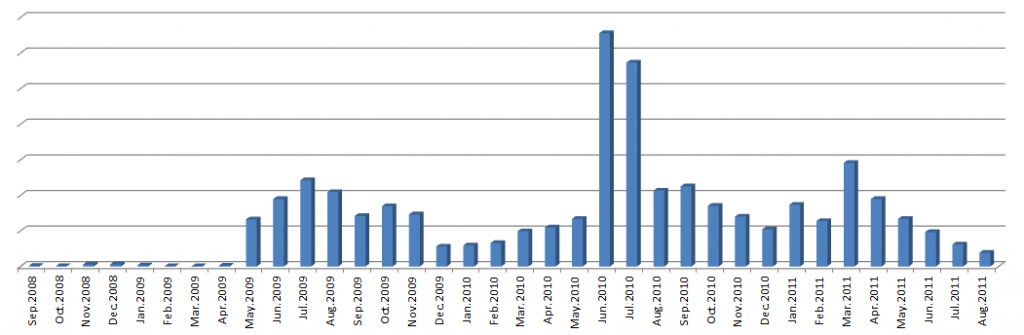
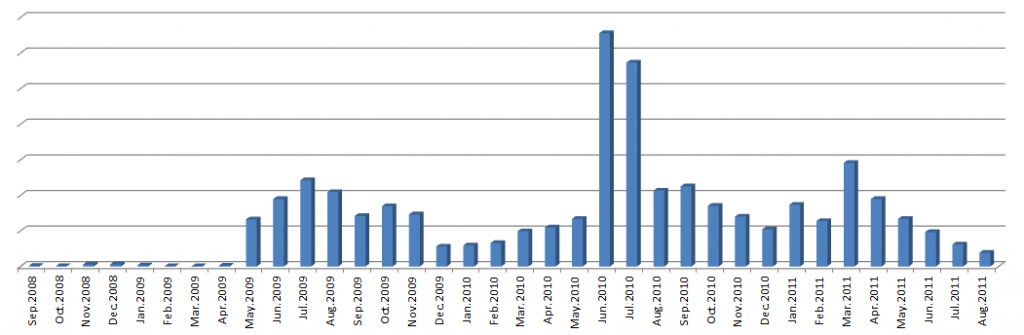
Android financial transactions on the rise – watch for malware
Awhile back we mused that the rapid rise in Android malware would hit its stride near the intersection of widespread mobile financial...
-
 431
431Win32/Delf.QCZ:Trust Me, I’m Your Anti‑Virus
Among the many different trojans that spread on Facebook, something popped up recently that caught our particular attention. The threat, detected...
-
 131
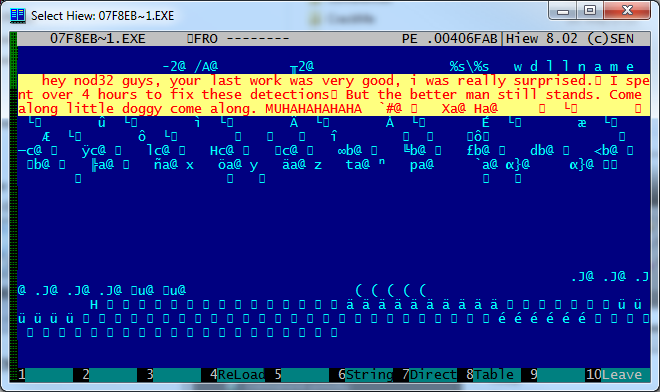
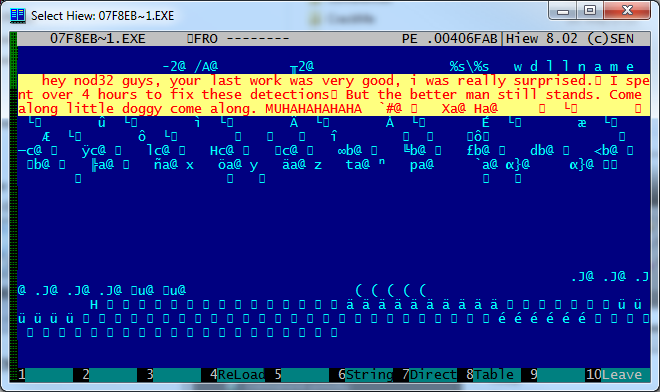
131Come along, little doggy, come along
The most common malware technique for avoiding detection is to create loads of “fresh” variants. Actually, the component that changes so frequently...
-
Manga Management and Malware
...one Yasuhiro Kawaguchi was arrested yesterday on suspicion of "saving a virus on his computer," though the story suggests distribution of malware...
-
 143
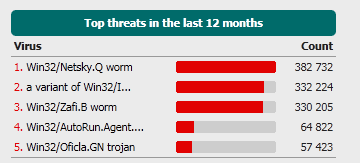
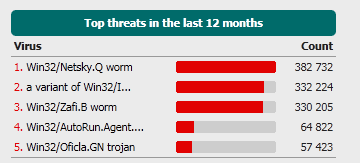
143The more things change, the more they stay the same
It's something of a truism, that 'old viruses never die', and that certainly seems to be the case for some of the...
-
Windows Rootkit Requires Reinstall?
In a ComputerWorld article Gregg Kaiser cites a Microsoft engineer as saying that the trojan that Microsoft calls “Popureb” digs so deeply...
-

 139
139Calling Android Smartphone Zombies
Android Smartphones are under attack again by rogue applications that once installed are reading information from the phone and sending it back...
-
Social engineers don’t care about your OS: and nor should you
Security companies in general and, unfortunately, anti-malware companies in particular, are often accused of ‘hyping’ threats because of a perceived self-interest. However,...
-
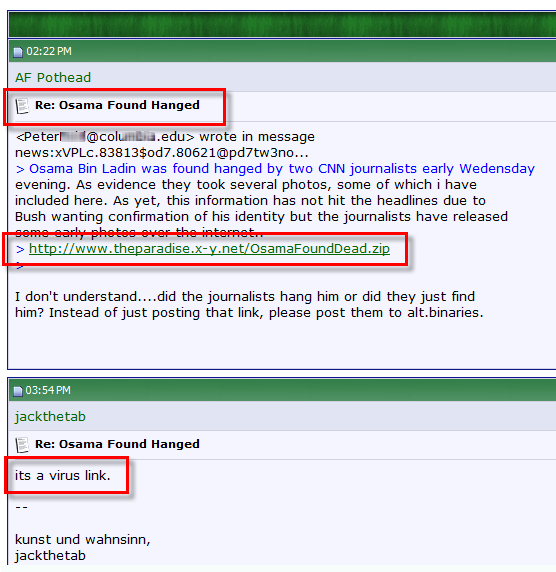
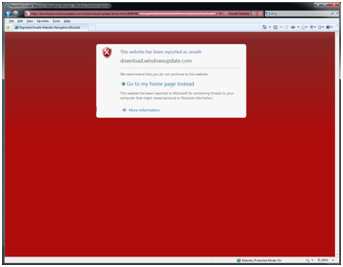
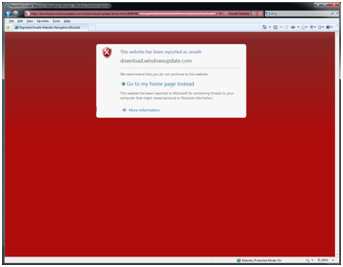
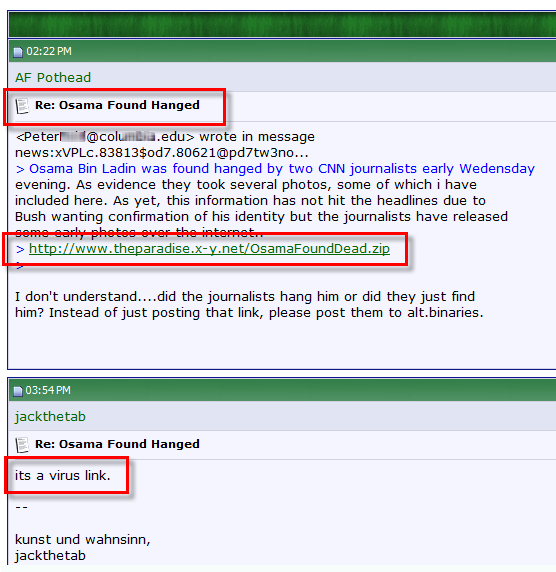 148
148Osama Bin Laden dead, malware is alive
Yesterday the U.S. president, Barak Obama, held a conference at the White House to announce that the leader of Al Qaeda, Osama...
-
Anatomy of a Biting Bunny – The Infected Microsoft Catalog Update
Aryeh Goretsky posted a blog about a trojan program in a Microsoft catalog update. I thought it might be a little interesting...
-
 130
130Trojan in Microsoft Update Catalog – A Bunny Bites Back
UPDATE #1 Randy Abrams has posted a follow-up article, Anatomy of a Biting Bunny – The Infected Microsoft Catalog Update with additional information...
-
What are Heuristics?
It is generally well-understood that antimalware programs—the software which detects computer viruses, worms, trojan horses and other threats to your system—work by...
-
Stuxnet: Cyberwarfare’s Universal Adaptor?
Now that cyberwarfare is out of the bottle, will anyone agree to not use it? In the summer of 1945 in New...
-
Open Source Malware Fingerprinting – Free Tool
In my ever-widening circle of anti-cybercrime methodology this particular approach to attribution of the criminals looting the free world makes me particularly...
-
Aryeh’s Mousing Memoirs
“Written in the form of a personal retrospective, this paper compares the earliest days of PC computer viruses with today’s threats, as...
-
Stock Manipulation Botnets Gain Ground
The attacks from cybercriminals are now occurring in the online stock and equity trading world. Instead of simply emptying out compromised brokerage...






