Mobile Security
-

 120
120Fake iPhone charger can hack iOS in under 60 seconds
A fake iPhone charger could be used to bypass the defenses of Apple's smartphone, three researchers from Georgia Tech have claimed. In...
-

 125
125Cybercrime a growing concern for businesses, security spending up at 40% of UK firms
Fears of cybercrime have become a major concern for many businesses - with security spending rising at four out of ten firms,...
-

 134
134Gartner indicates shift to mobile computing happening faster than expected
According to a survey by technology industry analysts Gartner, the adoption of mobile devices is happening even faster than expected.
-
 131
131Rogue developers hiding Android malware in apps on Google Play
Respected security blogger Brian Krebs reports that an “explosion in Android malware” is being fuelled by a growing market for hijacked of...
-

 147
147FinSpy and FinFisher spy on you via your cellphone and PC, for good or evil?
We read that “FinFisher spyware made by U.K.-based Gamma Group can take control of a range of mobile devices, including Apple Inc.’s...
-
 229
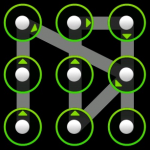
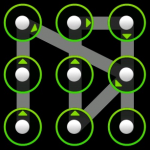
229The security of unlocking an Android based device, the future is near?
In a recent survey of people in America who use their smartphone for work, less than a third said they employ the...
-

 172
172New Year’s resolutions for securing your new tablet
Okay, you got the wrapping paper off the new tablet hotness, fired it up and now cannot put it down. But what...
-
Mobile Devices Favor Malware and Phishing
A while back a malicious program called DroidDream was found on the Google Marketplace. The thing about DroidDream is that it exploited...
-

 139
139Google Android and Really Bad Math
Yesterday I blogged about a security company that found a high percentage of apps for the iPhone and for the Android were...
-
Are You As Smart As Your Phone?
According to Cell-news.com, in 2007 over 850,000 Brits flushed their cell phones down the toilet. I’m sorry to report that there isn’t...
-
Mobile Malware
SC Magazine recently reported a malicious application in Google’s Android online market store http://www.scmagazineus.com/malicious-apps-found-in-googles-android-online-store/article/161001/. Due to the highly open nature of Android...
-
Got ICE?
ICE stands for “In Case of Emergency”. The idea is that you put ICE in front of the contact(s) on your phone...
-
Fly By Wireless
No, nothing to do with drive-by downloads… Our colleagues in Europe came up with a nice idea: an article on the dangers...






