How To
-

 4.5K
4.5K5 Robust Cybersecurity Practices for Your Email Marketing Campaigns
If you’re an online business owner that runs email marketing campaigns, you should know that phishing campaigns still prevail to trick your...
-
 3.9K
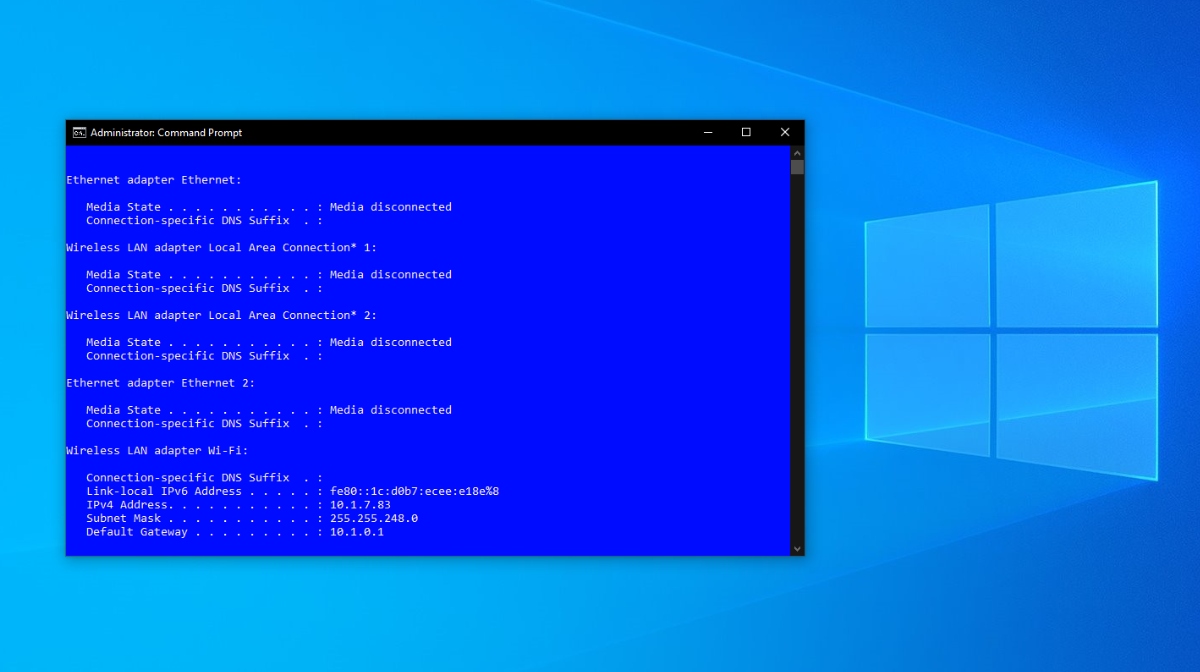
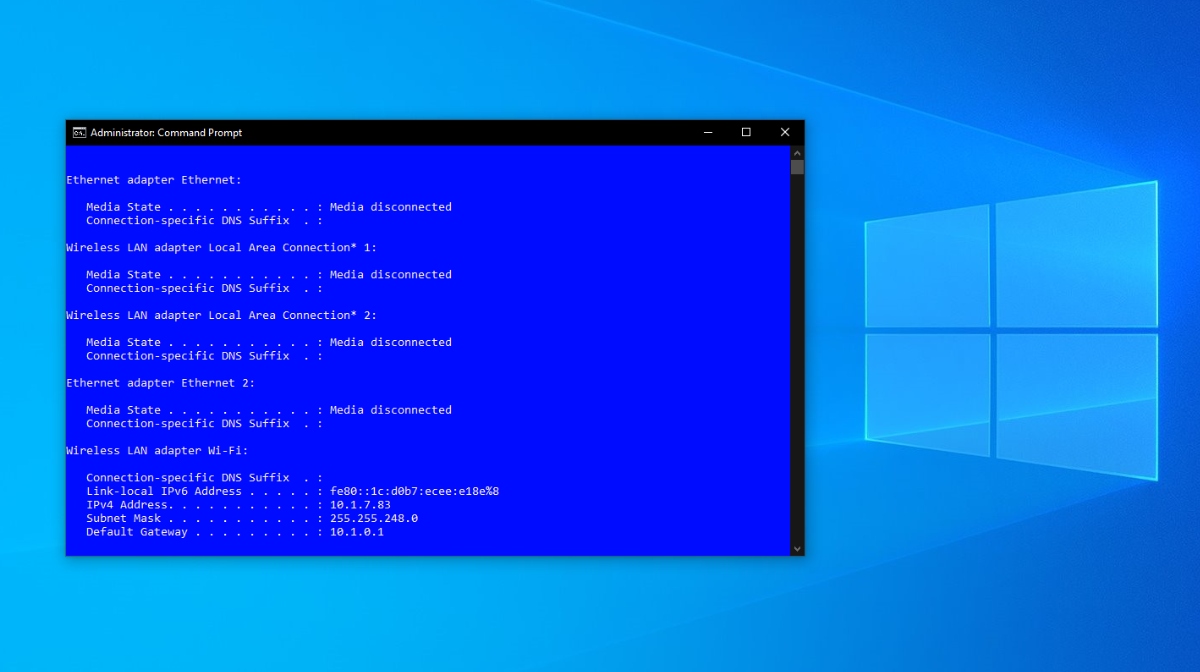
3.9KHow To Enable “Run As Administrator” For A Batch File In Windows 10?
A batch file includes the commands to be executed by Command Prompt in Windows 10 (and older versions). I have already explained...
-

 3.7K
3.7KStep-by-Step Guide to Creating the Best Web Pages
Everyone knows that your site design and content can be the difference between success and failure, but that doesn’t make it any...
-
 1.4K
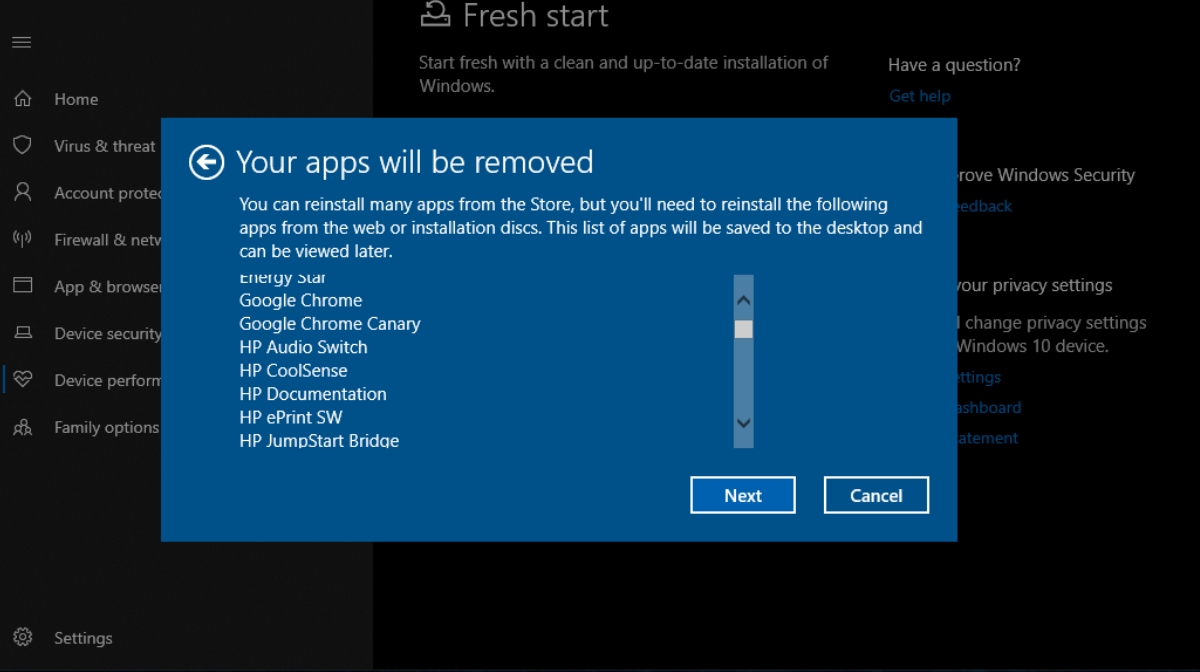
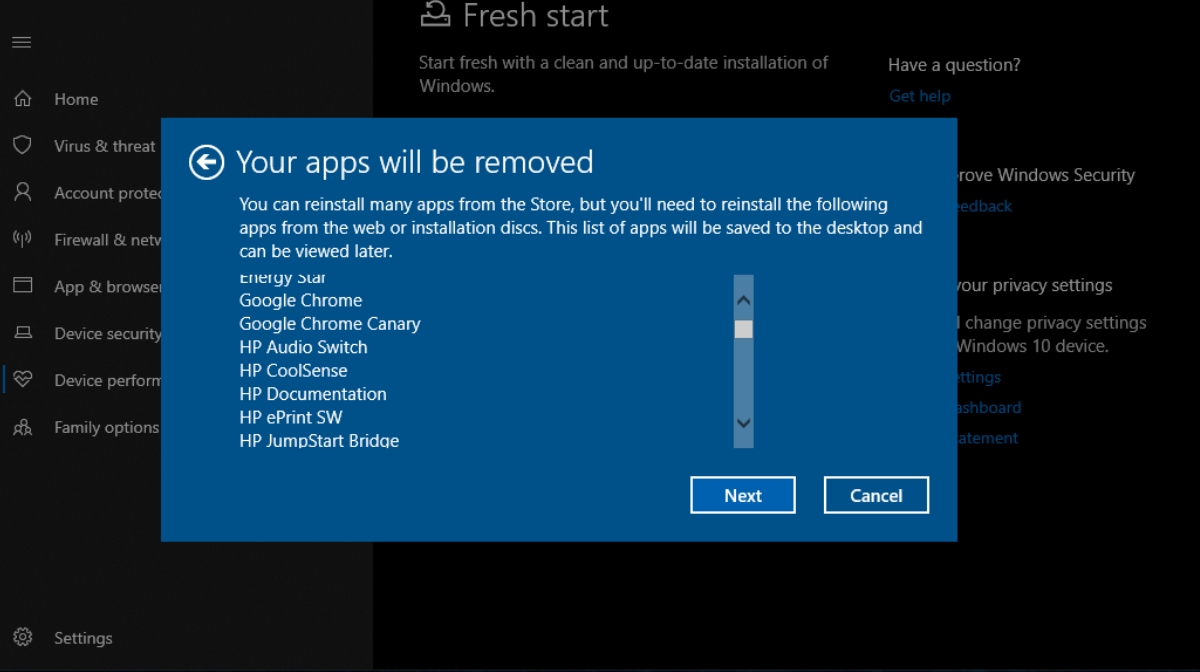
1.4KHow I Removed Bloatware From Windows 10?
Many people who use Windows 10 as their daily driver often try to find ways to remove bloatware from Windows 10 or...
-

 3.1K
3.1KHow To Take Screenshot On Snapchat Without Them Knowing?
We all know how popular and important the photo-sharing app Snapchat has become in our lives. Not sharing a snap while we...
-

 1.5K
1.5K5 Insider Threat Solutions You Should Follow in 2019
There are five main pillars of organization security that every successful business needs to adhere to: Protect your important assets Create a...
-

 1.4K
1.4KHow To Stop Someone From Spying On Your Cell Phone
People have the right to privacy on their mobile phones. However, with the increase of malicious hackers and the use of third-party...
-

 4.1K
4.1KHow To Download WhatsApp Status Video And Photos?
Ever since the concept of disappearing stories arrived on WhatsApp, the photo-sharing app’s popularity has grown further. It is a mandatory task...
-
 3.9K
3.9KData Breaches That Occurred in 2019 and How Cybersecurity Frameworks Can Work To Prevent Them
Data breaches are expensive. A company that suffers a data breach will spend about $4 million to recover lost information and shore...
-
 2.1K
2.1KHow to decrypt your data from Hakbit & Jigsaw ransomware for free
The cyber security firm Emisoft has released decrypter for Hakbit and Jigsaw ransomware that would unlock your files for free. One day...
-

 3.0K
3.0KKey features and best practices to look out for when purchasing a laptop
Cybersecurity is no longer a term, reserved only for the super paranoid nerds and/or conspiracy theorists. With hackers getting increasingly creative and...
-

 980
980Mini-Guide to Bug Bounty Hunting
My roommate, who has been in the IT niche for around 6 years, has recently started doing bug bounty (s). It was...
-
Should Students Have Homework?
People have been arguing over this subject for a couple of decades, but a unified opinion has not been formed yet. Some...
-

 2.6K
2.6KHow To Use ‘Mi Share’ For Cross-Device File Sharing In MIUI 11?
As much as people like to count the advantages of buying an Android device over an iPhone, they have to admit one...
-

 3.6K
3.6KA Review Of Yodot Recovery Software For Windows And Mac
While SD cards provide a wonderful means to store photos, videos, and other data, they need careful handling since they are prone...
-

 1.7K
1.7KSix Tips to Safely Shop Online During Black Friday and Cyber Monday 2019
The Thanksgiving weekend is just right around the corner. While some would still associate the upcoming holiday as time to be spent...
-

 3.2K
3.2KThe Cyber Essentials Checklist: How Accreditation Can Help Executives Grow Their Business
Since the dawn of the computer era, entrepreneurs and hackers have been in a constant race to outwork each other. While there...
-

 1.4K
1.4K3 ways an attacker may compromise a phone without the victims knowledge
We carry our mobile phones everywhere with us. These devices store our personal information. If this data falls into the wrong hands,...
-

 4.9K
4.9KHow to Remove Ads in Any Xiaomi/Redmi Device 2019 | 100% Working
Back in September, Xiaomi introduced a disable ad feature in the last beta version of MIUI 10. As the name suggests, the...
-

 4.2K
4.2KHow To Unlock Bootloader On Xiaomi Devices Using “Mi Unlock” Tool?
In order to root your smartphone or install a custom ROM, one of the first conditions that should be fulfilled is unlocking...
-

 2.1K
2.1KYour Ultimate Antivirus Software Guide
Android is the most widely used operating system. It is written in Java, C, C++, XML, Assembly Language, Python, Shell script and...






