Password
-

 277
277Who goes there? Identity and multiple authentication factors
Correct identification of an individual using a computer or service is important because it represents the accountability of the person identified. If...
-

 102
102Twitter makes two factor the authentication process du jour
Following the examples of Google, Facebook, Yahoo and DropBox, Twitter is reportedly ready to roll out a two factor sign in process...
-

 320
320Linux/SSHDoor.A Backdoored SSH daemon that steals passwords
In his summary of New Year predictions by security researchers here at ESET, Stephen Cobb pointed to expanded efforts by malware authors...
-

 95
95Ninety per cent of passwords are vulnerable to hacking, says report
According to the Deloitte Technology Trends 2013 report more than 90 per cent of user-generated passwords are weak and vulnerable to hacking,...
-

 146
146Securing Your Holiday Tech Gifts, Part 1: Windows PC Guide
[UPDATE #1: (21 Dec 2012, 5:30PM) ESET Researcher Cameron Camp has just published the second part of this series on securing your...
-
 118
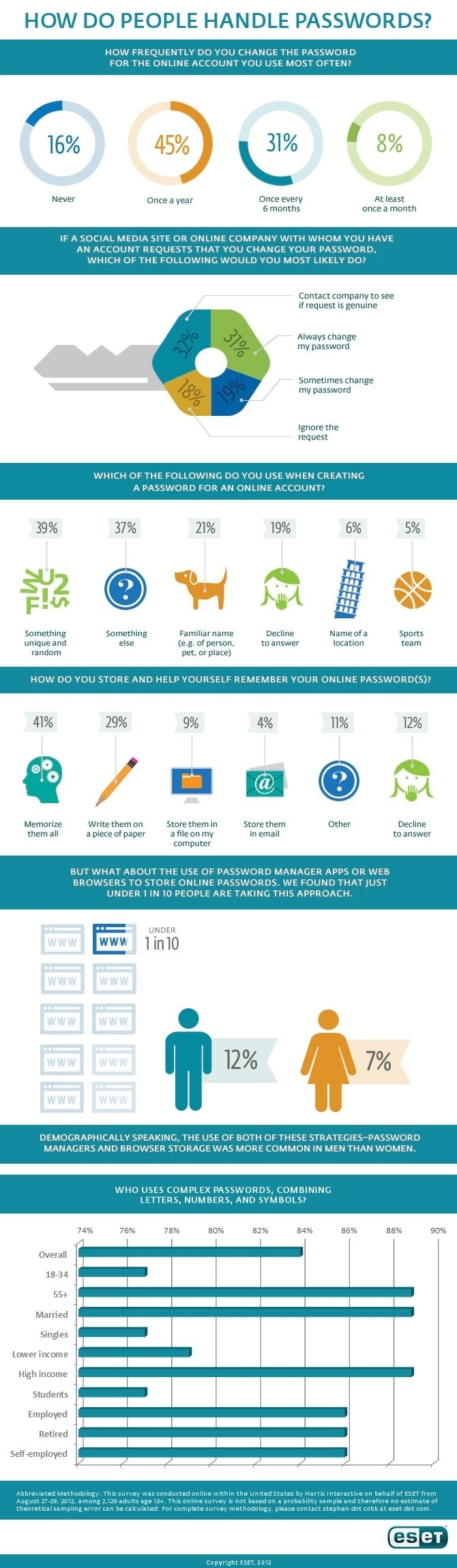
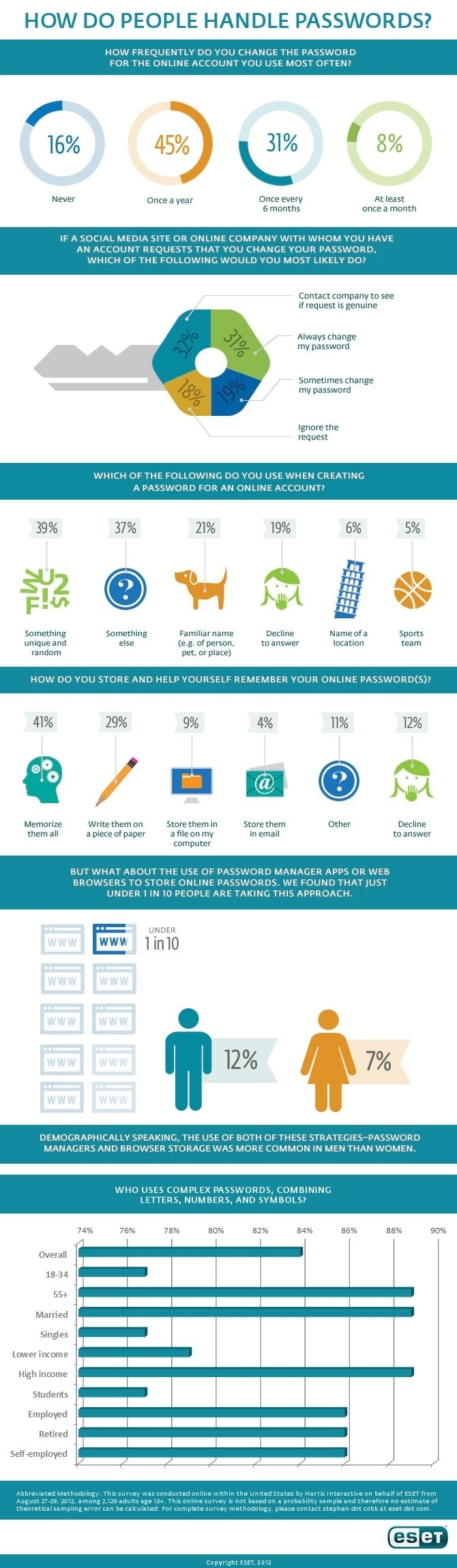
118Password handling: challenges, costs, and current behavior (now with infographic)
Online passwords are a pain, and not just when you have to type them to access your online bank account or shop...
-
 445
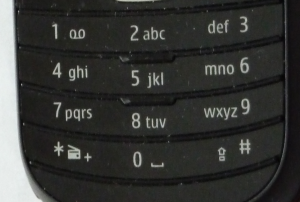
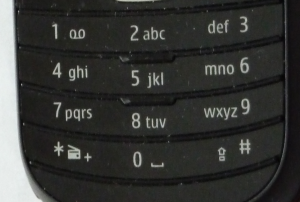
445Choosing a non‑obvious PIN
There is very little research data on PIN prevalence available, so analysis of a new dataset of 4-digit passcodes can't be ignored.
-

 260
260Bad password choices: don’t miss the point
Phish, Phowl, and Passwords I spend a lot of time defending educational as opposed to purely technical solutions to security. Not that...
-

 116
116Authentication attacks: Apple, Amazon, iCloud, Google, anything with a password
Sharing details of the hack that “wiped his life” has earned Mat Honan a place in the annals of information system security;...
-
 101
101Password Party Weekend? Millions exposed now include Phandroid, Nvidia, me
Changing the passwords on your online accounts might not sound like a fun weekend activity, but that’s what I did last weekend....
-

 127
127Passwords of Plenty*: what 442773 leaked Yahoo! accounts can tell us
If a service leaks your credentials, your options are limited, but changing all your passwords to something harder to guess/break is never...
-
Passwords and PINs: the worst choices
It's important to know the worst password choices, but also the worst choices for numeric passcodes.
-
 103
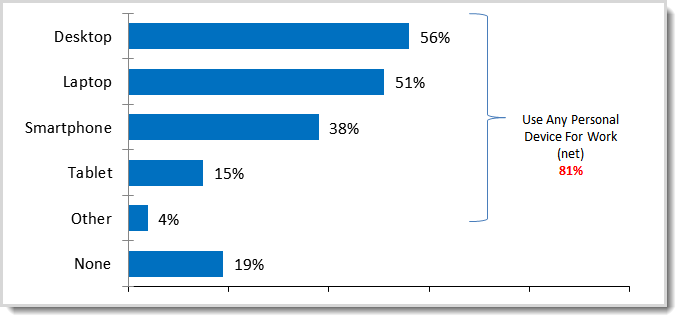
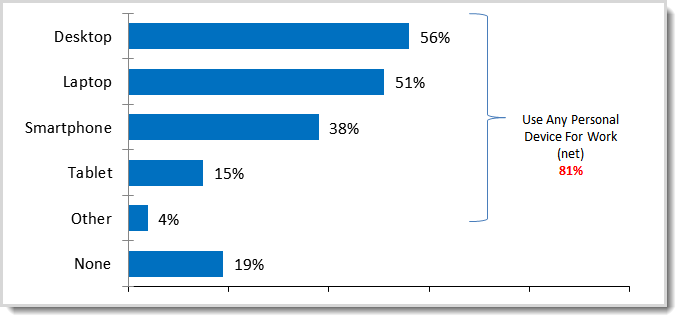
103The BYOD security challenge: How scary is the iPad, tablet, smartphone surge?
Employee use of personally-owned computing devices for work-related purposes–known as Bring Your Own Device or BYOD–is not a new trend and security...
-

 395
395Password management for non‑obvious accounts
A continuation on: Time to check your DNS settings? After 7 March 2012, lots of people potentially can be hit as their...
-
Passwords, Stratfor, and Newton’s 3rd Law of Motion
Dazzlepod is saying ... if your account name comes up, change your current password ... why not assume that your account is...
-
Much Ado About Facebook
The Reuters news agency reported earlier today a sudden increase in violent and pornographic images and videos on Facebook. A quick review...
-
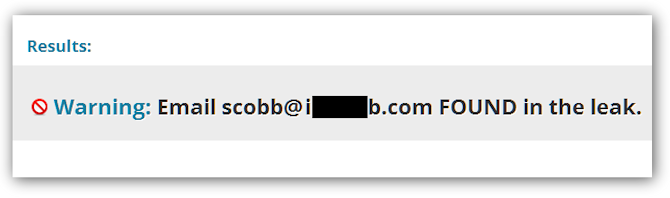
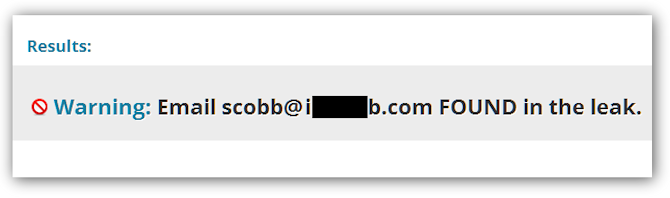
Stolen password checking: a question of trust
How do you know a service is legitimate and safe? We all have to trust by proxy sometimes, but it just doesn't...
-
Where there’s smoke, there’s FireWire
Forensic software developer PassWare announced a new version of its eponymous software forensics kit on Tuesday. Already several news sources are writing...
-
 209
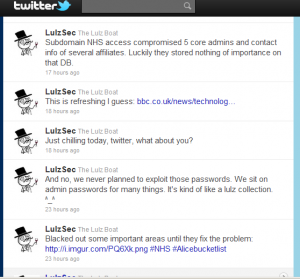
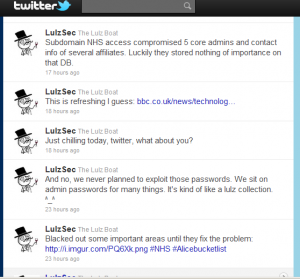
209LulzSec lulls the NHS: not such bad lads?
...on the Twitter account owned by LulzSec that they had turned their attention to the NHS. Curiously enough, they seem to have...
-
A Nice Pair of Breaches
...here's a blog in stark contrast to Urban Schrott's blog about good password practice in Ireland ... Troy Hunt ran an analysis...
-

 136
136No chocolates for my passwords please!
Greetings Dear Reader, We have published guidance material previously on passwords and passphrases, some are blogs and some are lengthier depending on...






