Articles
-
 203
203jQuery hacked: Site was hit, but not the library
The official blog of jQuery—most popular JavaScript library used by millions of websites—has been hacked by some unknown hackers, using the pseudonym...
-

 194
194Ethereum phishing attack that earns $15K in two hours
Wesley Neelen (security researcher) has received a phishing email that seems to be from the legal online Ethereum wallet site Myetherwallet.com. Cybercriminals...
-
Entire Europe is being affected by the BadRabbit Ransomware
According to various cybersecurity firms, the growing virus is dubbed “BadRabbit” and is a form of ransomware that bolts down machines and...
-
Pixel 2 XL Displays are burning up already
News reported the issue, revealing a picture of a Pixel 2 XL with some fierce image remembrance around the navigation bar. Shortly...
-

 237
237Intel and Lenovo are trying to build UAF and U2F authentication into their devices
81 percent of data breaks last year involved weak, default or stolen passwords, and phishing attacks have advanced 65 percent year-on-year. Protecting...
-
 245
245DUHK (Don’t Use Hard-coded Keys) Attack Recovers Encryption Keys & Reveals VPN Connections
DUHK (Don’t Use Hard-coded Keys) is a new crypto implementation attack that could enable attackers to obtain secret keys that secure VPN...
-

 212
212Four Darknet Markets Simultaneously Go Offline
In an astonishing hit to the Darknet, four of it’s most popular marketplaces all went down at the same time. Marketplaces involved...
-

 186
186Russia Fights to Keep Founder of BTC-e from Extradition to United States
In a tale as old as time, the United States and Russia are at it again. Alexander Vinnik, the founder of a...
-
DNS over TLS is being developed for the next Android Update
DNS over TLS is a protocol where DNS inquiries will be encrypted to the equivalent level as HTTPS and therefore a DNS...
-
The Value of Bitcoin has surpassed $6000 for the first time
The cryptocurrency hit an all-time high of $6,147.07 just a time after forcing through the $6,000 mark, according to data from application...
-
 200
200Machine Learning Software created by Google is replicating itself
Now, Google has declared that AutoML has defeated the human AI engineers at their own game by setting machine-learning software that’s more...
-

 191
191A New IoT Botnet Threatens to Take Down the Internet
Just a year after Mirai—biggest IoT-based malware that caused vast Internet outages by launching massive DDoS attacks—completed its first anniversary, security researchers...
-
Your School can now check your Browser History according to the new Rules by Denmark Government
The motion seeks to make it more stressful for students to cheat in exams. As a section of the new rules, schools...
-
Another Vulnerability is found in Intel Management Engine which allows execution of Code with no Digital Fingerprint
Taking advantage of Intel ME technology, within which attackers can execute unsigned code on the target machine. This leads to a full...
-

 212
212Cyber Attack Kept Secret from Public by Microsoft for Years
Not the first news of this nature but it was very recently discovered that Microsoft suffered a cyber attack from a group...
-

 202
202Google Advanced Protection is for high-profile hacking targets
Many internet giants offer security measures like two-factor authentication (which you should really use) to keep your account safe from hackers. But...
-

 160
160Google is thinking about adding support to stop cryptocurrency miners on websites
Studies on the topic of in-browser miners have been going on the Chromium project’s bug tracker since mid-September when Coinhive, the first...
-

 173
173According to Research: 25% of the Federal Government Mails are Fraud
Agari supports email fraud on behalf of larger than 400 federal websites, including the real sites of the departments of Health and...
-
 241
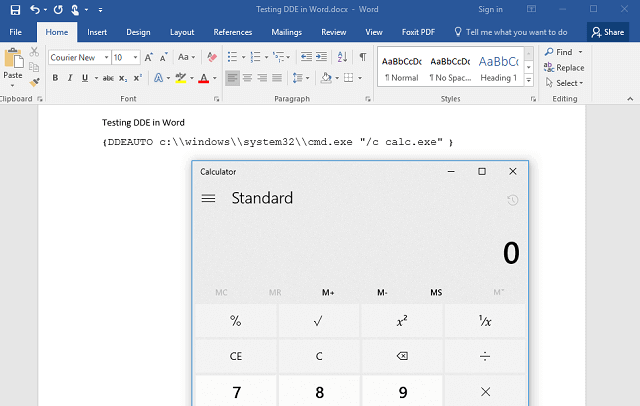
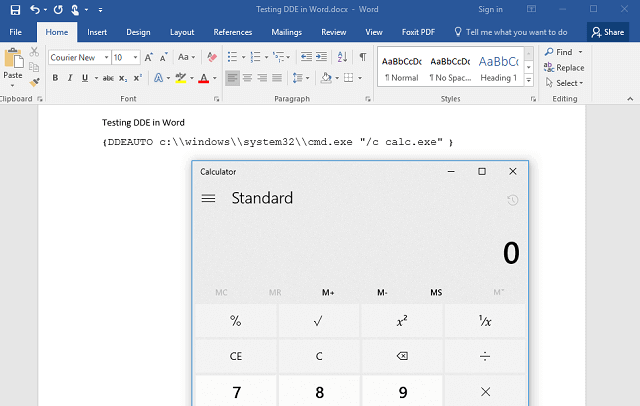
241Unpatched Microsoft Word DDE Exploit Being Used In Malware Attacks
A newly discovered unpatched attacking method that exploits a built-in feature of Microsoft Office is currently being used in various widespread malware...
-
 267
267Proof of Concept Code for WPA2 Krack Attack has been released
Security researchers have discovered several key management vulnerabilities in the core of Wi-Fi Protected Access II (WPA2) protocol that could allow an...
-
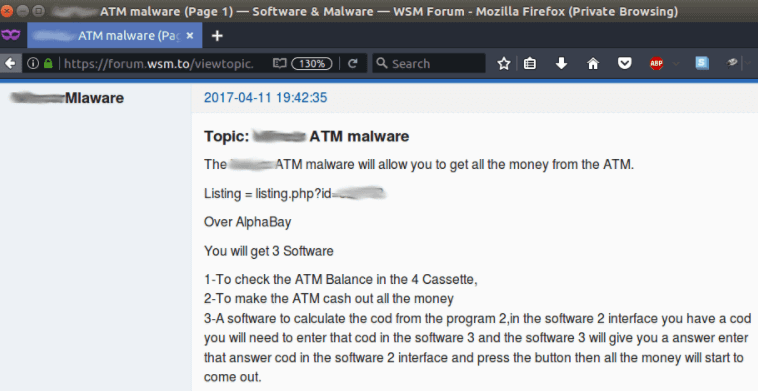
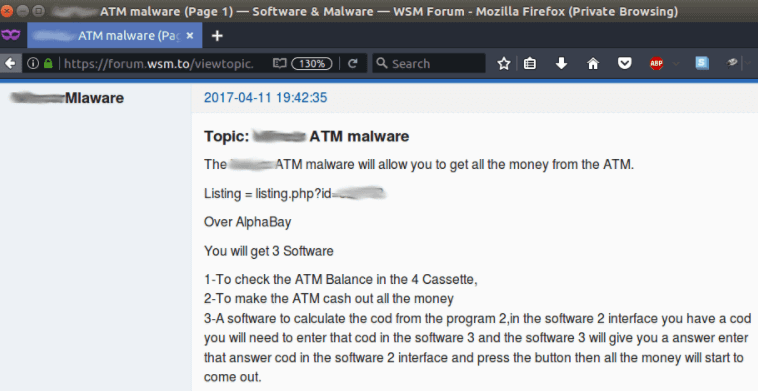 253
253ATM malware is being sold on Dark Web market that can make ATMs drain available cash
In May 2017, Kaspersky security researchers have noticed a forum post advertising ATM (Automated teller machine) malware that was targeting specific vendor...






