Articles
-

 190
190AWS Certification Training Courses – Get 2019 Bundle @ 96% OFF
With countless web apps and online services launching every day, there is an increasing demand for cloud developers. This exciting niche is...
-
 200
200BEWARE – New ‘Creative’ Phishing Attack You Really Should Pay Attention To
A cybersecurity researcher who last month warned of a creative phishing campaign has now shared details of a new but similar attack...
-

 223
223Severe Flaw Disclosed In StackStorm DevOps Automation Software
A security researcher has discovered a severe vulnerability in the popular, open source event-driven platform StackStorm that could allow remote attackers to...
-

 237
237NSA Releases GHIDRA 9.0 — Free, Powerful Reverse Engineering Tool
The United States’ National Security Agency (NSA) today finally released GHIDRA version 9.0 for free, the agency’s home-grown classified software reverse engineering...
-

 161
161Google Discloses Unpatched ‘High-Severity’ Flaw in Apple macOS Kernel
Cybersecurity researcher at Google’s Project Zero division has publicly disclosed details and proof-of-concept exploit of a high-severity security vulnerability in macOS operating...
-
 270
270Researchers Link ‘Sharpshooter’ Cyber Attacks to North Korean Hackers
Security researchers have finally, with “high confidence,” linked a previously discovered global cyber espionage campaign targeting critical infrastructure around the world to...
-
 169
169Hackers Favorite CoinHive Cryptocurrency Mining Service Shutting Down
Coinhive, a notorious in-browser cryptocurrency mining service popular among cybercriminals, has announced that it will discontinue its services on March 8, 2019....
-
 230
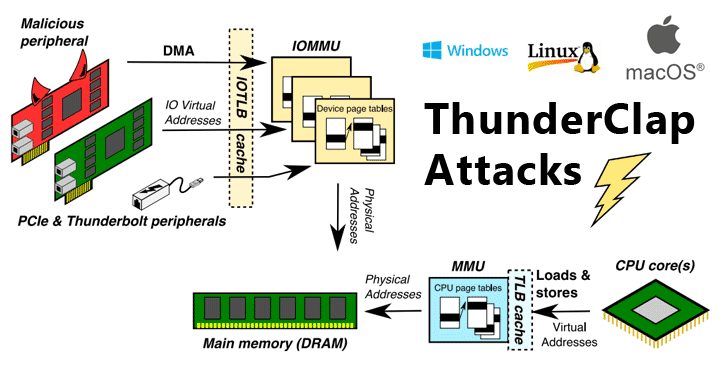
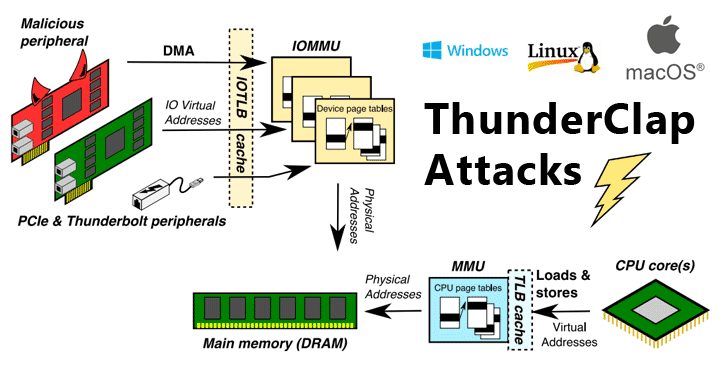
230New Flaws Re-Enable DMA Attacks On Wide Range of Modern Computers
Security researchers have discovered a new class of security vulnerabilities that impacts all major operating systems, including Microsoft Windows, Apple macOS, Linux,...
-
 173
173Severe Flaws in SHAREit Android App Let Hackers Steal Your Files
Security researchers have discovered two high-severity vulnerabilities in the SHAREit Android app that could allow attackers to bypass device authentication mechanism and...
-
 202
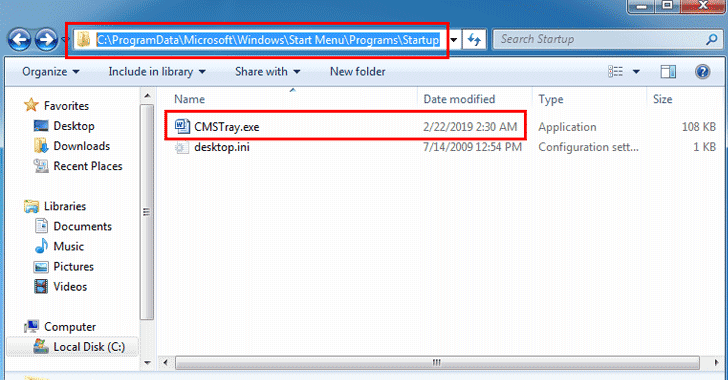
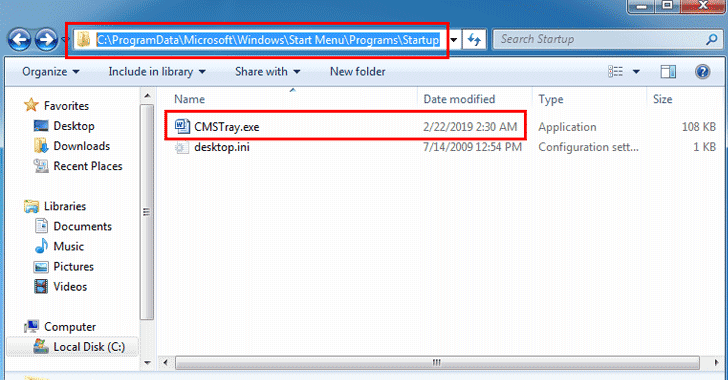
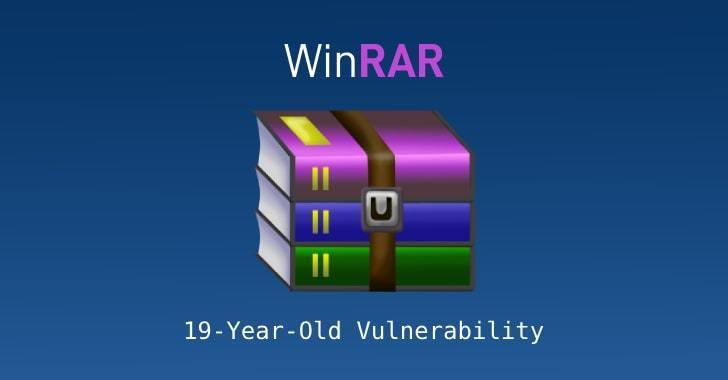
202Latest WinRAR Flaw Being Exploited in the Wild to Hack Windows Computers
It’s not just the critical Drupal vulnerability that is being exploited by in the wild cybercriminals to attack vulnerable websites that have not...
-

 164
164Hackers Actively Exploiting Latest Drupal RCE Flaw Published Last Week
Cybercriminals have actively started exploiting an already patched security vulnerability in the wild to install cryptocurrency miners on vulnerable Drupal websites that...
-
 200
200Android Gets FIDO2 Certification—Now Supports Secure Passwordless Logins
Great news. If you have already installed the latest update of Google Play Services released earlier today, and your Android device is...
-
 182
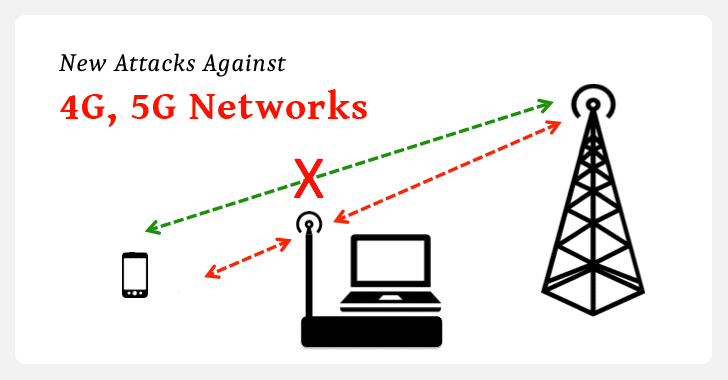
182New Attacks Against 4G, 5G Mobile Networks Re-Enable IMSI Catchers
At NDSS Symposium 2019, a group of university researchers yesterday revealed newly discovered cellular network vulnerabilities that impact both 4G and 5G...
-
 407
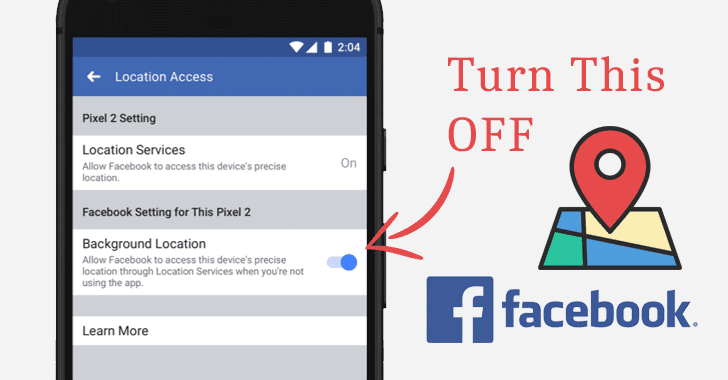
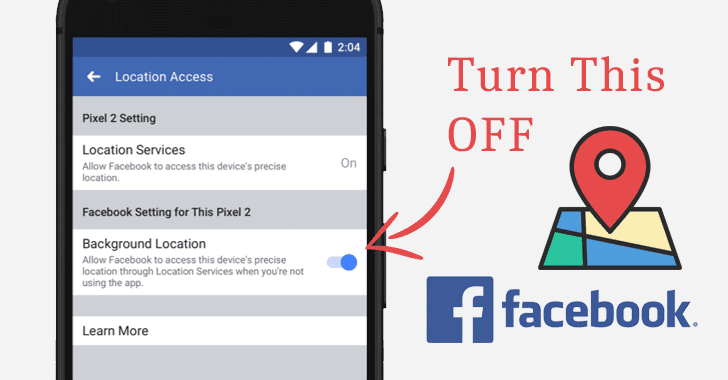
407How to Stop Facebook App From Tracking Your Location In the Background
Every app installed on your smartphone with permission to access location service “can” continually collect your real-time location secretly, even in the...
-

 189
189Hacking Virtual Reality – Researchers Exploit Popular Bigscreen VR App
A team of cybersecurity researchers from the University of New Haven yesterday released a video demonstrating how vulnerabilities that most programmers often...
-

 166
166Another Critical Flaw in Drupal Discovered — Update Your Site ASAP!
Developers of Drupal—a popular open-source content management system software that powers millions of websites—have released the latest version of their software to...
-

 166
166Almost Half A Million Delhi Citizens’ Personal Data Exposed Online
Exclusive — A security researcher has identified an unsecured server that was leaking detailed personal details of nearly half a million Indian...
-
 170
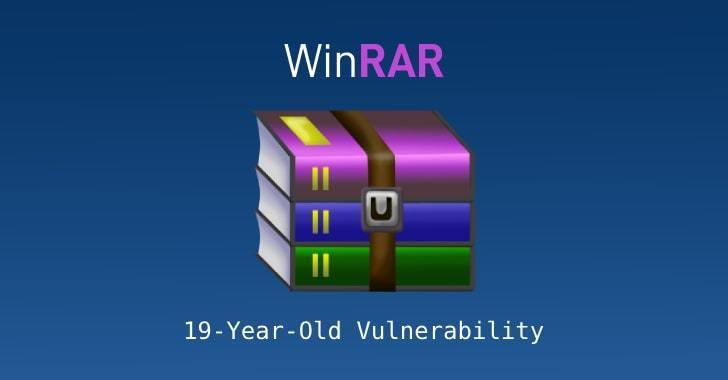
170Critical WinRAR Flaw Affects All Versions Released In Last 19 Years
Beware Windows users… a new dangerous remote code execution vulnerability has been discovered in the WinRAR software, affecting hundreds of millions of...
-

 160
160Critical Flaw Uncovered In WordPress That Remained Unpatched for 6 Years
Exclusive — If you have not updated your website to the latest WordPress version 5.0.3, it’s a brilliant idea to upgrade the...
-
 169
169Learn How XDR Can Take Breach Protection Beyond Endpoint Security
How do you know whether an attacker has infiltrated your network? Can you really rely on an Endpoint Detection and Response (EDR)...
-
 158
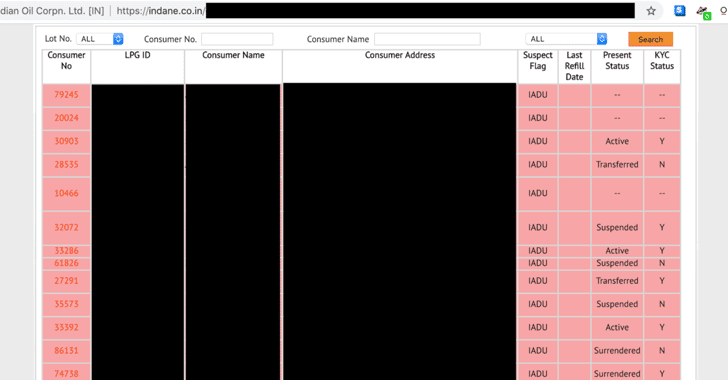
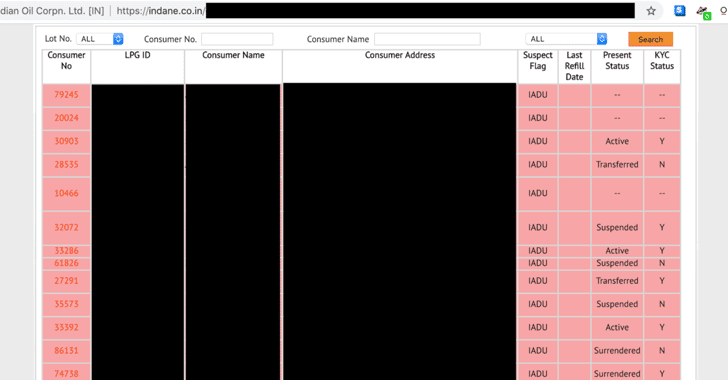
158LPG Gas Company Leaked Details, Aadhaar Numbers of 6.7 Million Indian Customers
Why would someone bother to hack a so-called “ultra-secure encrypted database that is being protected behind 13 feet high and 5 feet...






