Security Tools
-
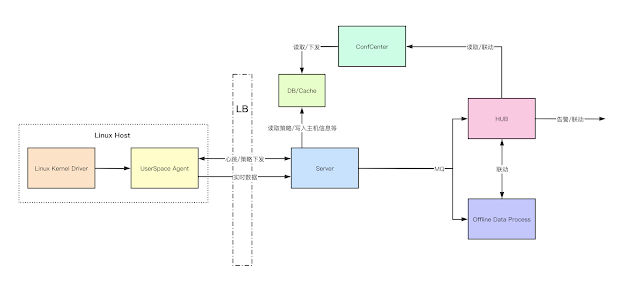
Tylium – Data for Intrusion Detection, Security Analytics and Threat Hunting
These files contain configuration for producing EDR (endpoint detection and response) data in addition to standard system logs. These configurations enable...
-
 373
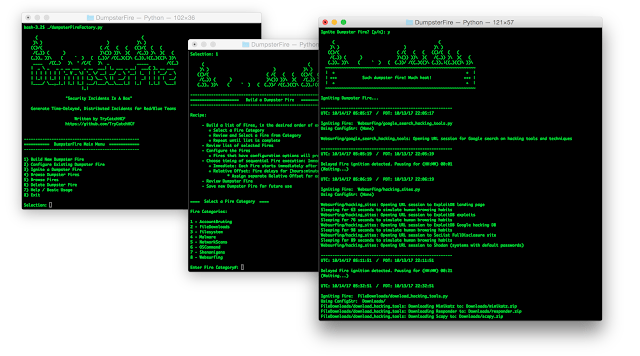
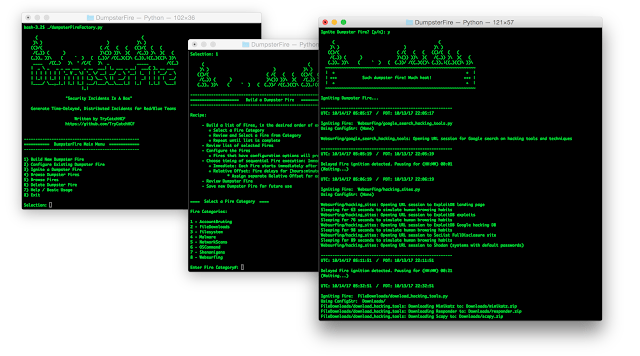
373DumpsterFire – Cross-Platform Tool For Building Security Events
DumpsterFire Toolset – “Security Incidents In A Box!” The DumpsterFire Toolset is a modular, menu-driven, cross-platform tool for building repeatable, time-delayed,...
-
 385
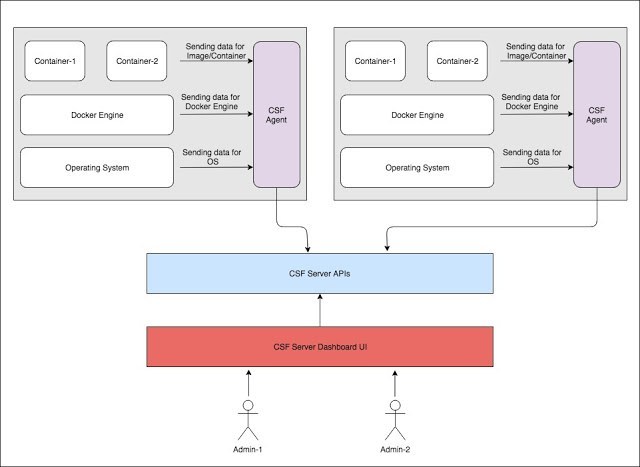
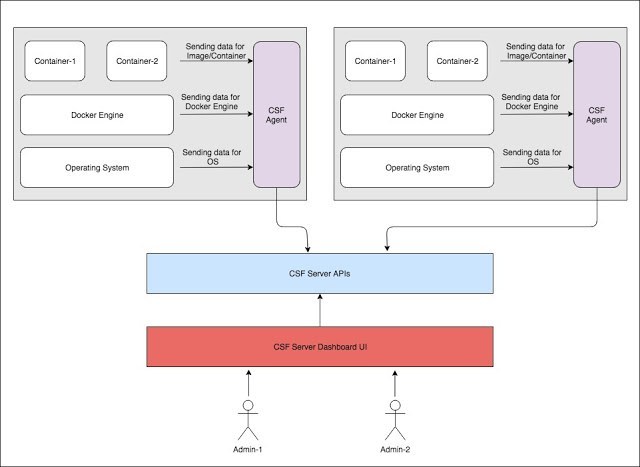
385ArmourBird CSF – Container Security Framework
ArmourBird CSF – Container Security Framework is an extensible, modular, API-first framework build for regular security monitoring of docker installations and...
-

 460
460ScoutSuite – Multi-Cloud Security Auditing Tool
Scout Suite is an open source multi-cloud security-auditing tool, which enables security posture assessment of cloud environments. Using the APIs exposed...
-
 345
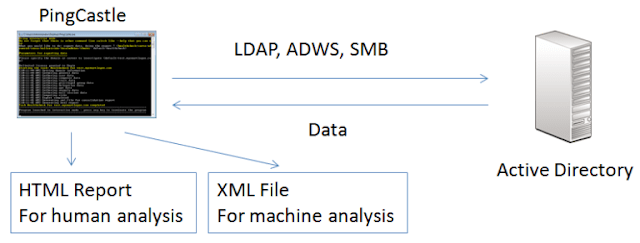
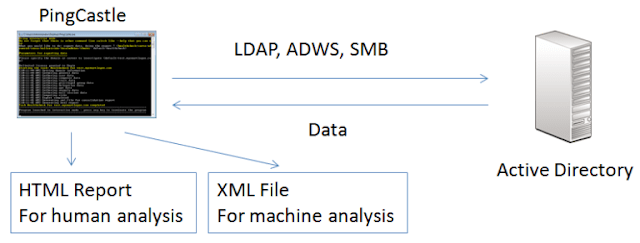
345PingCastle – Get Active Directory Security
The risk level regarding Active Directory security has changed. Several vulnerabilities have been made popular with tools like mimikatz or sites...
-
 276
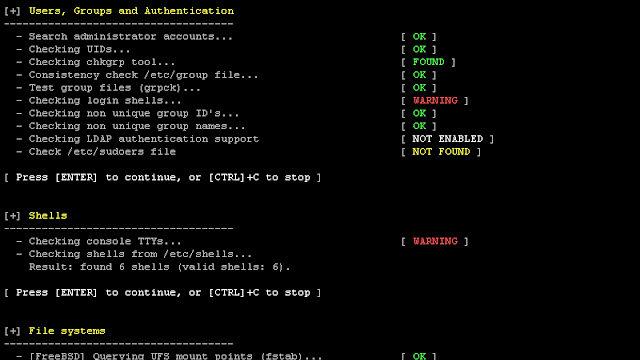
276Lynis 2.7.3 – Security Auditing Tool for Unix/Linux Systems
We are excited to announce this major release of auditing tool Lynis. Several big changes have been made to core functions of...
-
 398
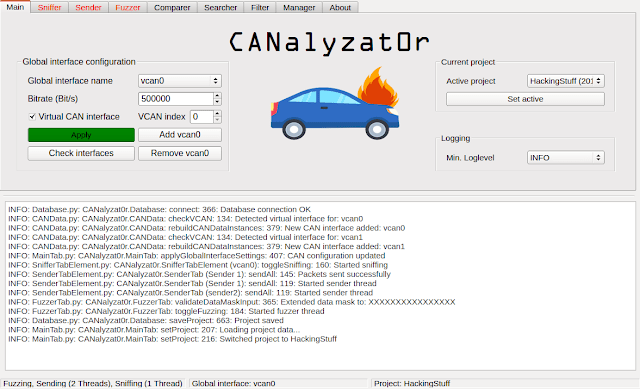
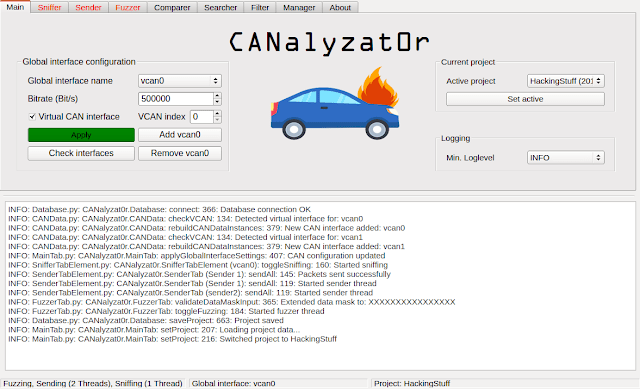
398CANalyzat0r – Security Analysis Toolkit For Proprietary Car Protocols
This software project is a result of a Bachelor’s thesis created at SCHUTZWERK in collaboration with Aalen University by Philipp Schmied.Please refer...
-
 288
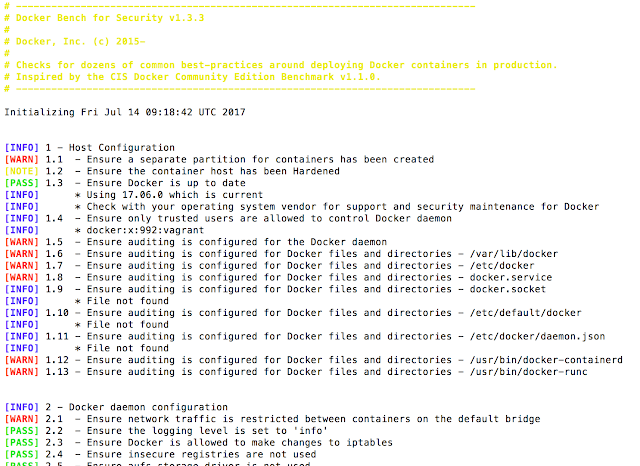
288The Docker Bench For Security – A Script That Checks For Dozens Of Common Best-Practices Around Deploying Docker Containers In Production
The Docker Bench for Security is a script that checks for dozens of common best-practices around deploying Docker containers in production. The...
-
 289
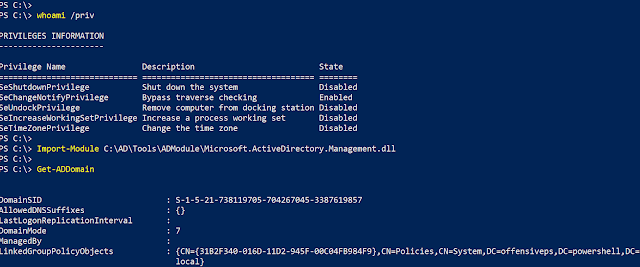
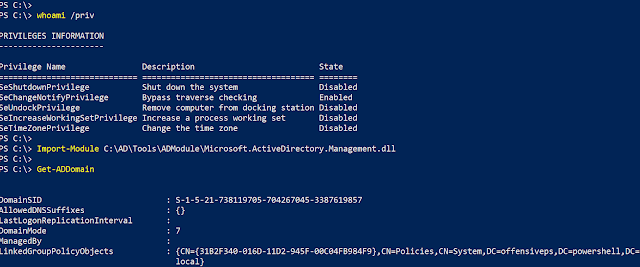
289ADModule – Microsoft Signed ActiveDirectory PowerShell Module
Microsoft signed DLL for the ActiveDirectory PowerShell module Just a backup for the Microsoft’s ActiveDirectory PowerShell module from Server 2016 with RSAT...
-

 270
270Python-Nubia – A Command-Line And Interactive Shell Framework
Nubia is a lightweight framework for building command-line applications with Python. It was originally designed for the “logdevice interactive shell (aka. ldshell)”...
-
 348
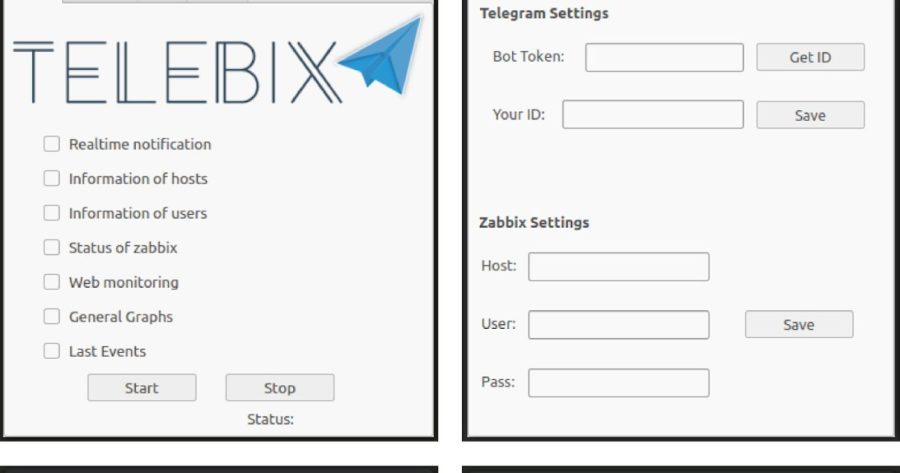
348Telebix – An Application That Communicates With A Bot On The Telegram To Receive Commands And Send Information From An Infrastructure Monitored By Zabbix
Telebix is an application that communicates with a Bot on the Telegram to receive commands and send information from an infrastructure monitored...
-

 241
241PatrOwl – Open Source, Free And Scalable Security Operations Orchestration Platform
PatrOwl is a scalable, free and open-source solution for orchestrating Security Operations. PatrowlManager is the Front-end application for managing the assets, reviewing...
-

 260
260Nameles – Open Source Entropy Based Invalid Traffic Detection And Pre-Bid Filtering
Nameles provides an easy to deploy, scalable IVT detection and filtering solution that is proven to detect at a high level of...
-
 261
261EKFiddle v.0.8.2 – A Framework Based On The Fiddler Web Debugger To Study Exploit Kits, Malvertising And Malicious Traffic In General
A framework based on the Fiddler web debugger to study Exploit Kits, malvertising and malicious traffic in general. Installation Download and install...
-
 242
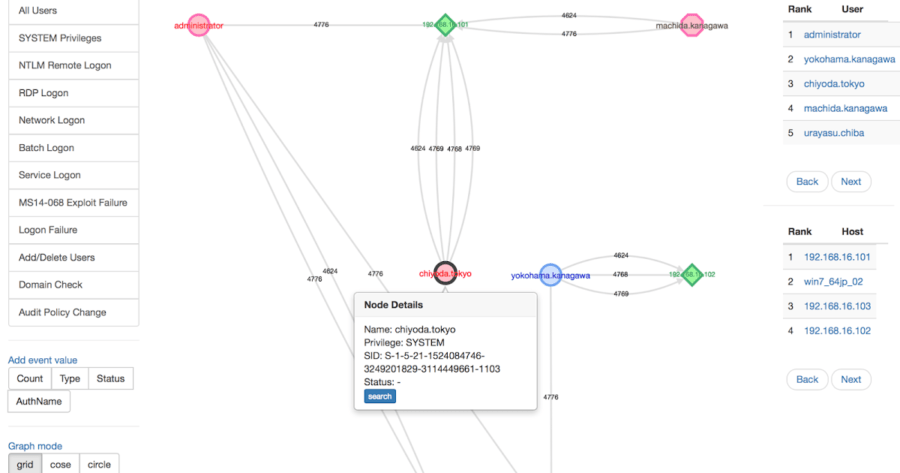
242LogonTracer – Investigate Malicious Windows Logon By Visualizing And Analyzing Windows Event Log
Investigate malicious logon by visualizing and analyzing Windows active directory event logs. Concept LogonTracer associates a host name (or an IP address)...
-

 225
225GlobaLeaks – The Open-Source Whistleblowing Software
GlobaLeaks is open-source / free software intended to enable secure and anonymous whistleblowing initiatives developed by the Hermes Center for Transparency and...
-
 348
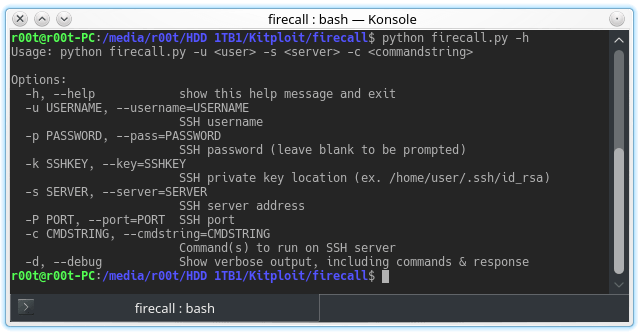
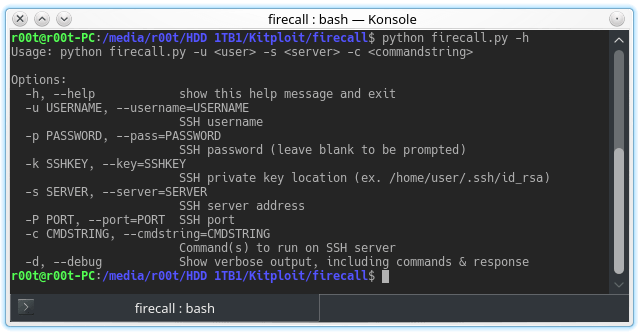
348Firecall – Automate SSH Communication With Firewalls, Switches, Etc.
Automate SSH communication with firewalls, switches, etc. Description These scripts are designed to automate sending commands to a Cisco ASA firewall. The...