Vulnerability Analysis
-
 266
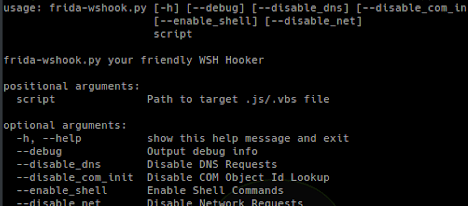
266Frida-Wshook – Script Analysis Tool Based On Frida.re
frida-wshook is an analysis and instrumentation tool which uses frida.re to hook common functions often used by malicious script files which are...
-
 263
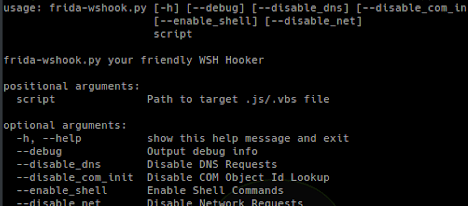
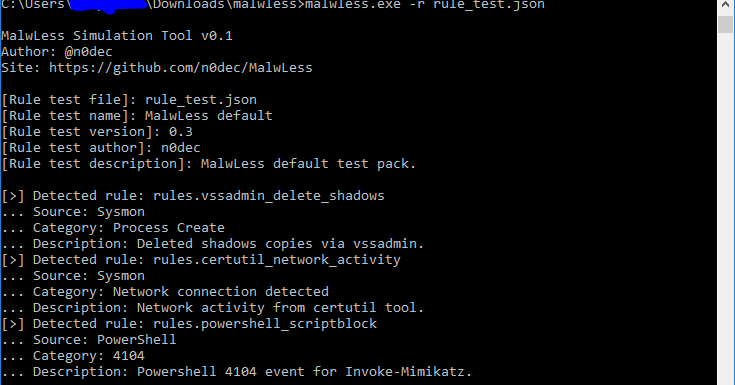
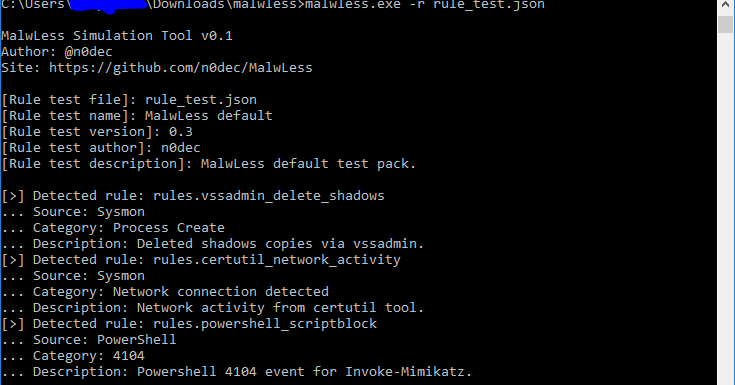
263MalwLess – Test Blue Team Detections Without Running Any Attack
MalwLess is an open source tool that allows you to simulate system compromise or attack behaviours without running processes or PoCs. The...
-

 224
224testssl.sh – Testing TLS/SSL Encryption Anywhere On Any Port
testssl.sh is a free command line tool which checks a server’s service on any port for the support of TLS/SSL ciphers, protocols...
-
 288
288Slither – Static Analyzer For Solidity
Slither is a Solidity static analysis framework written in Python 3. It runs a suite of vulnerability detectors, prints visual information about...
-
 227
227Httplab – Inspect HTTP Requests And Forge Responses
The interactive web server. HTTPLabs let you inspect HTTP requests and forge responses. Install Golang go get github.com/gchaincl/httplab go install github.com/gchaincl/httplab/cmd/httplab Archlinux...
-
 255
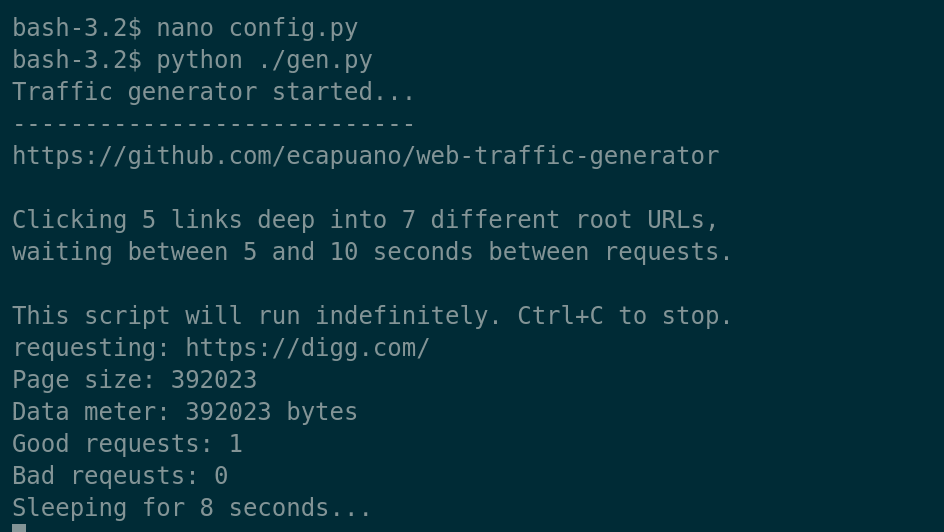
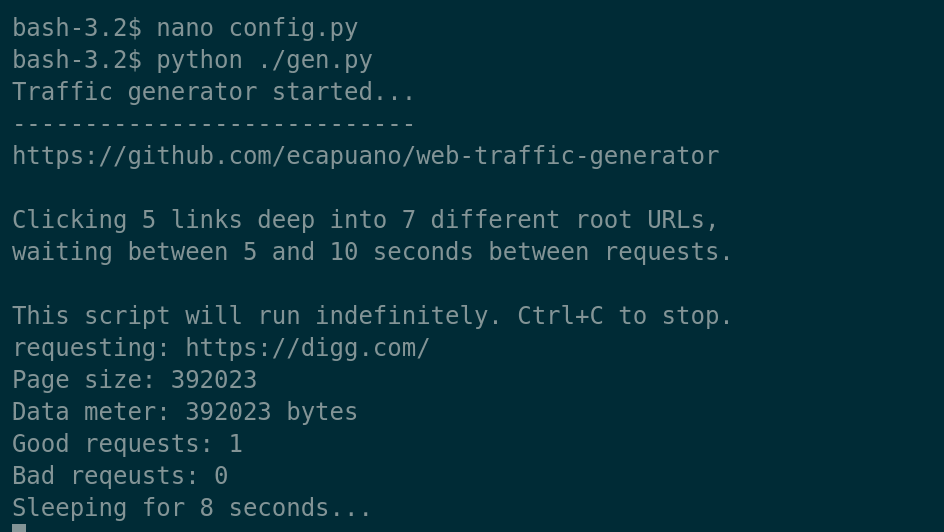
255Web-Traffic-Generator – A Quick And Dirty HTTP/S “Organic” Traffic Generator
Just a simple (poorly written) Python script that aimlessly “browses” the internet by starting at pre-defined rootURLs and randomly “clicking” links on...
-
 252
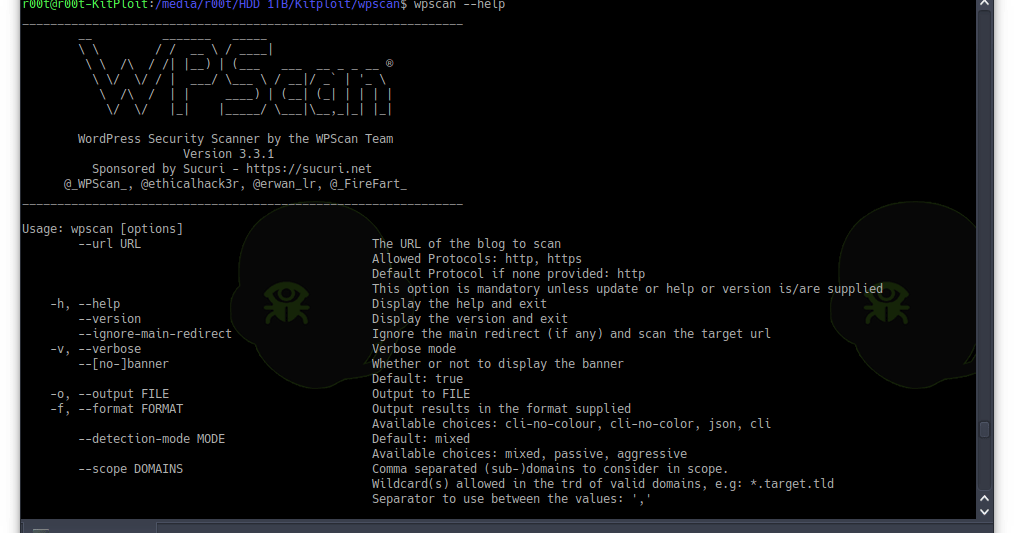
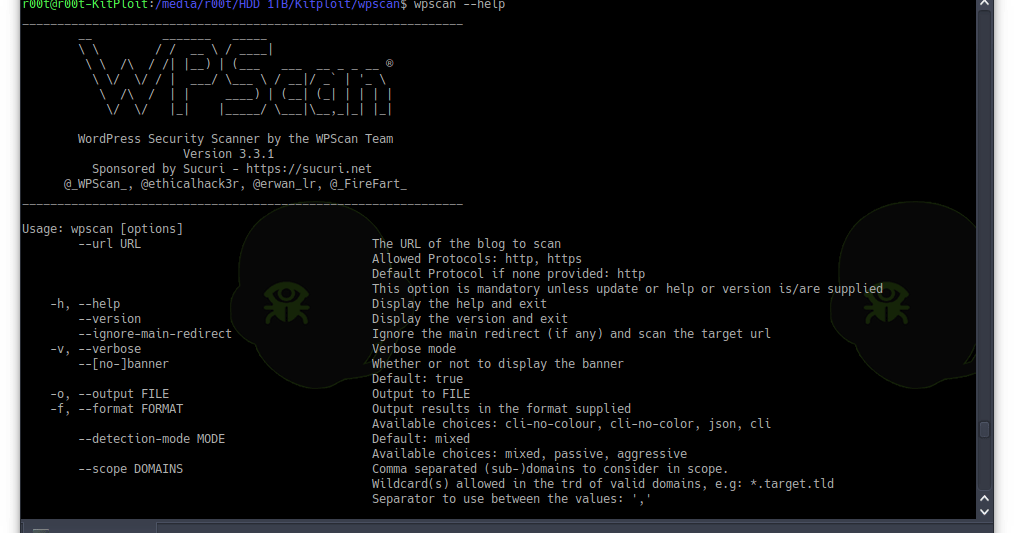
252WPScan v3.3.1 – Black Box WordPress Vulnerability Scanner
WPScan is a free, for non-commercial use, black box WordPress vulnerability scanner written for security professionals and blog maintainers to test the...
-
 253
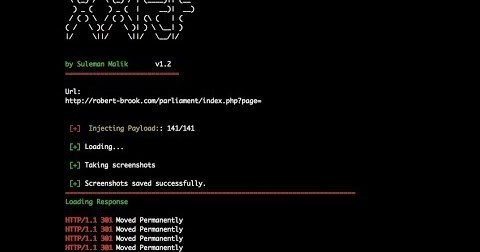
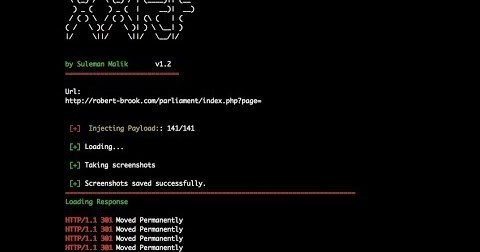
253XXRF Shots – Tool to Test SSRF Vulnerabilities
What is SSRF vulnerability? Server Side Request Forgery (SSRF) is a type of vulnerability class where attacker sends crafted request from a...
-
 243
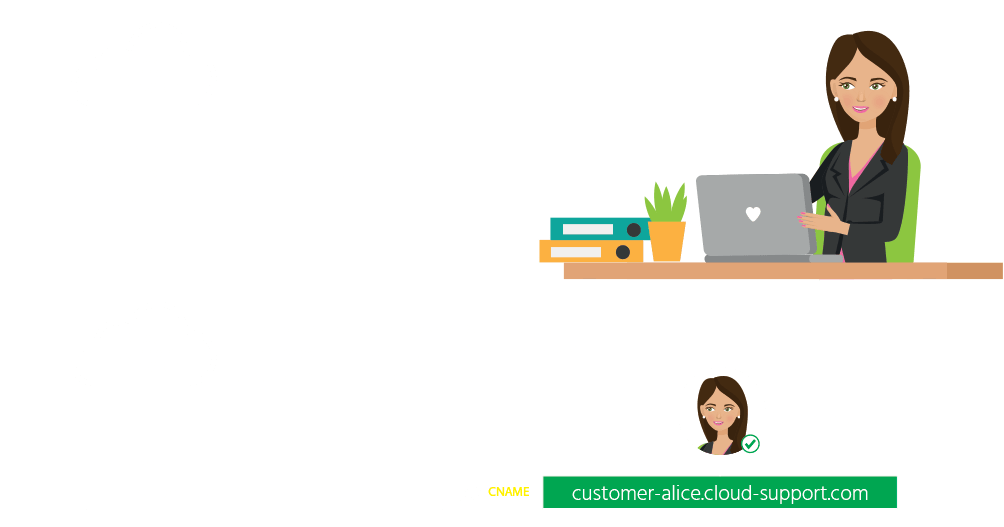
243Scan your exposure to domain and subdomain hijacking over 10’s of cloud providers
Domain Hijacking is a well-known security issue that can be carried in many different ways. In addition to social engineering or unauthorized...
-
 388
388Linux Exploit Suggester – Linux Privilege Escalation Auditing Tool – Kali Linux 2018.1
Often during the penetration test engagement the security analyst faces the problem of identifying privilege escalation attack vectors on tested Linux machine(s)....
-
 225
225XVNA – Extreme Vulnerable Node Application
XVNA is an extreme vulnerable node application coded in Nodejs(Expressjs)/MongoDB that helps security enthusiasts to learn application security. it’s not counseled to...
-
 221
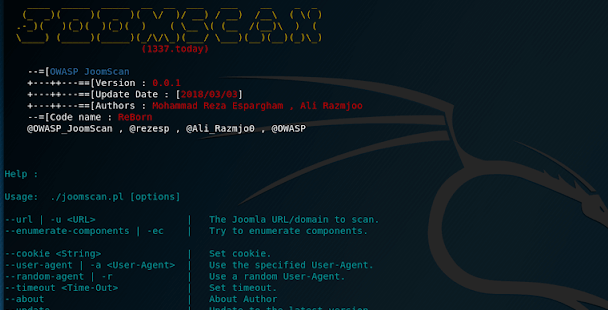
221JoomScan 0.0.5 – OWASP Joomla Vulnerability Scanner Project
OWASP JoomScan (short for [Joom]la Vulnerability [Scan]ner) is an opensource project in perl programming language to detect Joomla CMS vulnerabilities and analysis them. WHY OWASP JOOMSCAN ? If...
-
 162
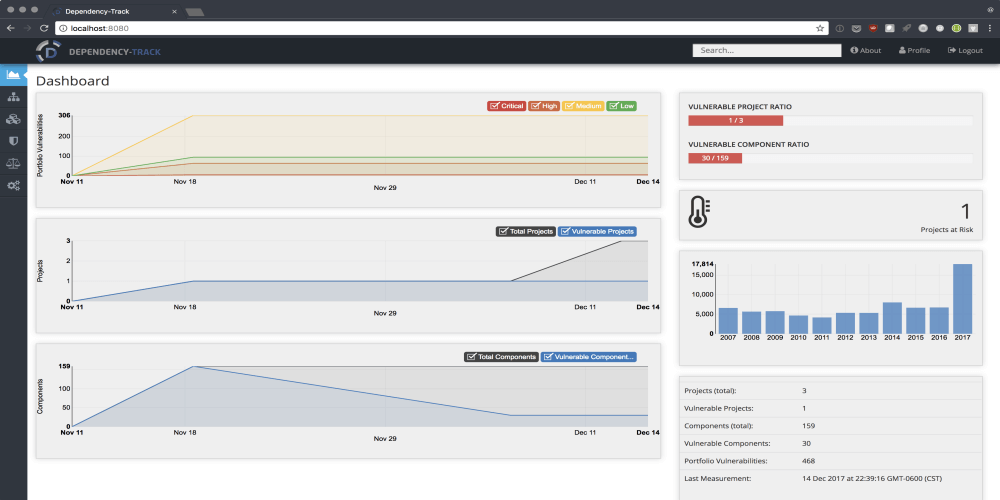
162Dependency-Track – Intelligent Software Composition Analysis Platform
Modern applications leverage the availability of existing components for use as building blocks in application development. By using existing components, organizations can...
-
 237
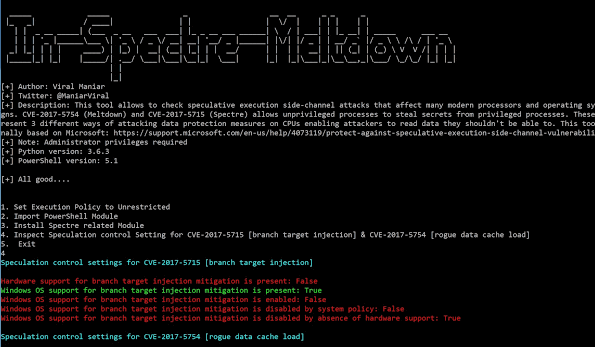
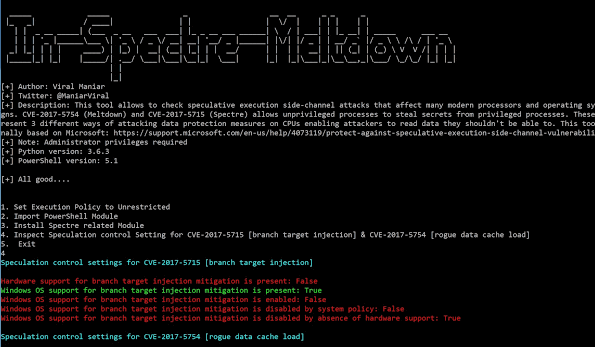
237In-Spectre-Meltdown – Tool to identify Meltdown & Spectre Vulnerabilities in processors
This tool allows to check speculative execution side-channel attacks that affect many modern processors and operating systems designs. CVE-2017-5754 (Meltdown) and CVE-2017-5715...
-

 265
265Wapiti 3.0.0 – The Web-Application Vulnerability Scanner
Wapiti allows you to audit the security of your websites or web applications. It performs “black-box” scans (it does not study the...
-
 237
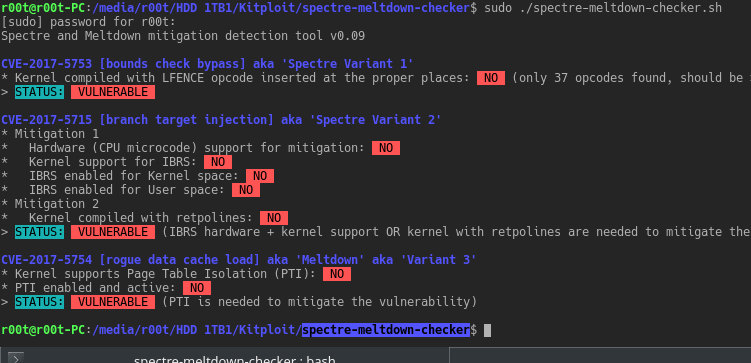
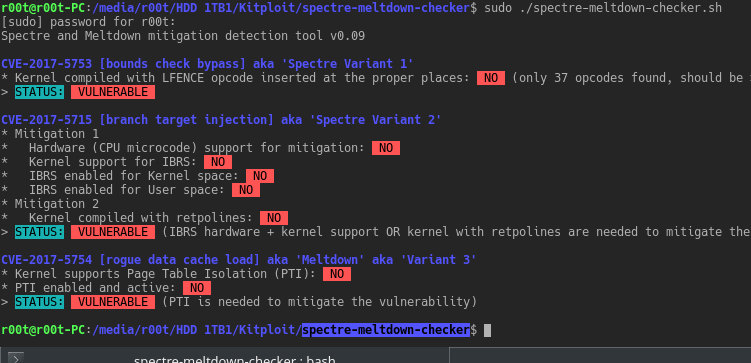
237Spectre-Meltdown-Checker – Spectre & Meltdown Vulnerability/Mitigation Checker For Linux
A simple shell script to tell if your Linux installation is vulnerable against the 3 “speculative execution” CVEs: CVE-2017-5753 bounds check bypass...
-

 193
193Meltdown Exploit Proof of Concept
Speculative optimizations execute code in a non-secure manner leaving data traces in microarchitecture such as cache. Refer to the paper by Lipp...
-

 365
365WhatWaf – Detect And Bypass Web Application Firewalls And Protection Systems
WhatWaf is an advanced firewall detection tool who’s goal is to give you the idea of “There’s a WAF?”. WhatWaf works by...
-
 237
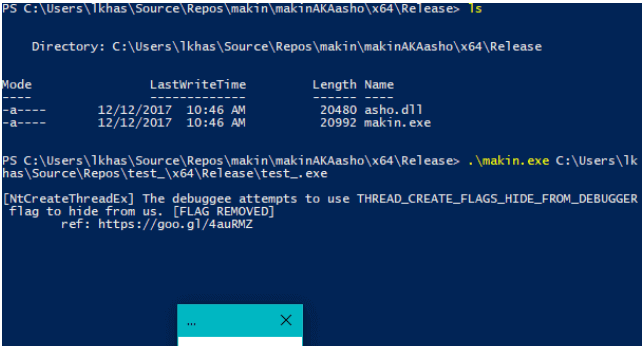
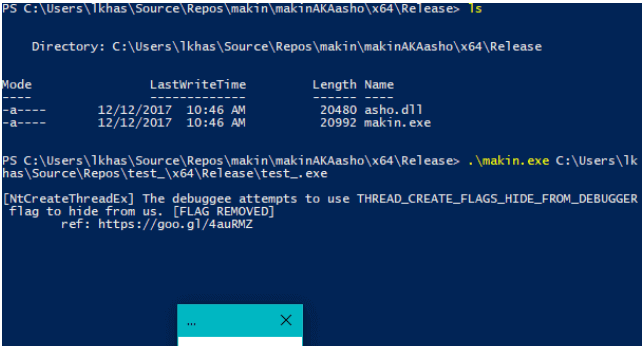
237Makin – Reveal Anti-Debugging Tricks
makin is to make initial malware assessment little bit easier, It helps to reveal a debugger detection techniques used by a sample. Supports...
-
 260
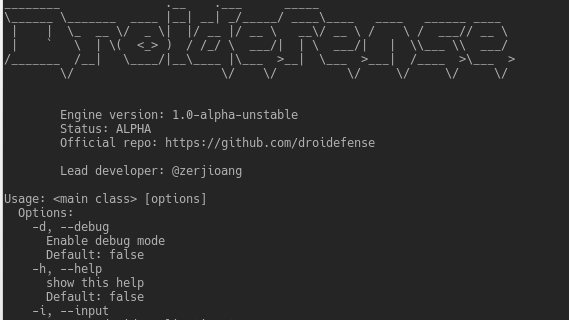
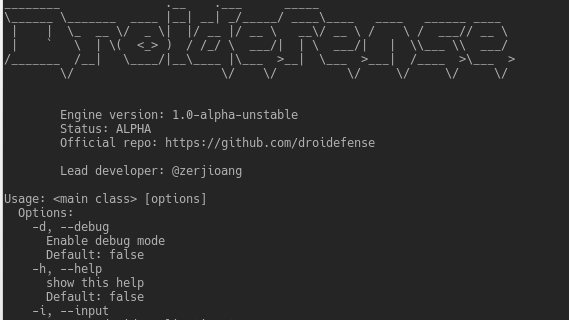
260Droidefense – Advance Android Malware Analysis Framework
Droidefense (originally named atom: analysis through observation machine)* is the codename for android apps/malware analysis/reversing tool. It was built focused on security...
-
 247
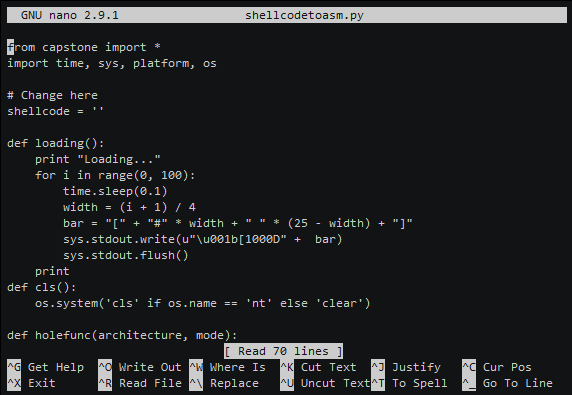
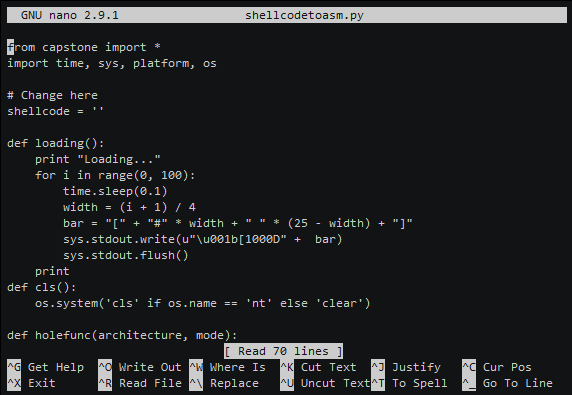
247ShellcodeToAssembly – Transform your Shellcode to Assembly (ARM, ARM64, MIPS, PPC, X86)
Transform your Shellcode to Assembly (ARM, ARM64, MIPS, PPC, X86) Replace in shellcodetoasm.py with your shellcode. shellcode = '' Installation git clone https://github.com/blacknbunny/ShellcodeToAssembly.git...






