Vulnerabilities
-

 250
250Google Forms WordPress Plugin unauthenticated PHP Object injection vulnerability
Introduction The Google Forms WordPress Plugin fetches a published Google Form using a WordPress custom post or shortcode, removes the Google wrapper...
-
 160
160How Your Android’s Pattern Lock Can Be Cracked In Just 5 Attempts
Short Bytes: Pattern lock on Android smartphones is probably the quickest and easiest way to gain access to the device. A group...
-

 189
189Firefox bares teeth, attacks sites that collect personal data
If it wants a password and doesn’t use HTTPS, Mozilla will breathe fire. Shoddy sites will have fewer places to hide with...
-

 163
163AlphaBay Dark Web marketplace hacked, private messages leaked
Over 200,000 messages were compromised due to a security flaw. One of the largest trading posts on the Dark Web, AlphaBay, has...
-

 162
162China cracks down on ‘unauthorized’ VPNs
The censorship state wants to enforce government control over software which can circumvent China’s Great Firewall. The Chinese government has launched a...
-

 202
202PHP Melody 2.7 – Multiple Vulnerabilities
What’s interesting when I come across a new piece of software is how the initial impressions change after reading the code. If...
-

 166
166Discovered Critical Bug allowed to Delete any Videos from Facebook
Security researcher Dan Melamed came across the vulnerability in June 2016. The bug is some ways similar to a vulnerability discovered by...
-
 192
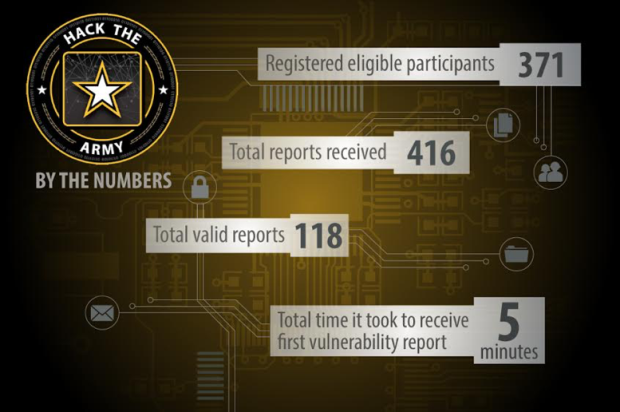
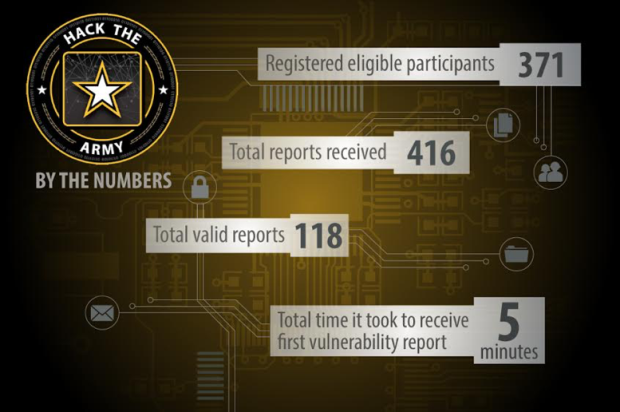
192Expert Hacks Internal DoD Network via Army Website
The Defense Digital Services (DDS) group is tasked with pioneering private sector solutions to solve some of the Department of Defense’s most...
-
 77
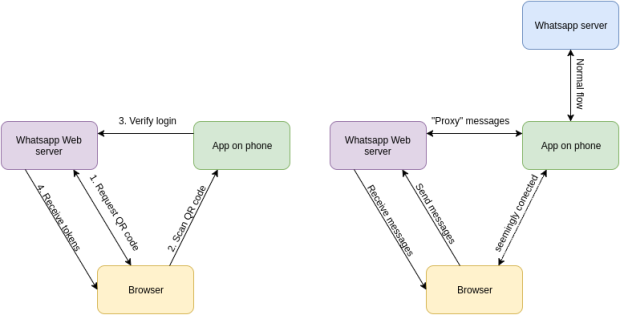
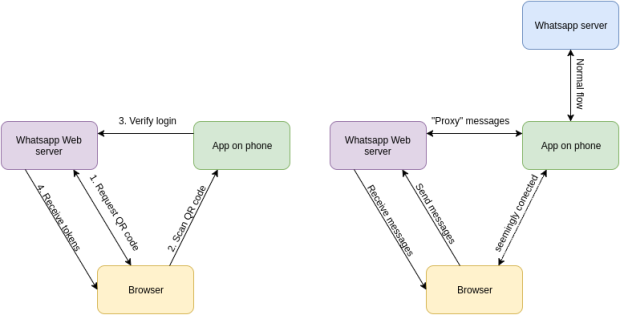
77HIJACKING WHATSAPP ACCOUNTS USING WHATSAPP WEB
Whatsapp accounts are based on phone numbers. This means your phone number is your username and it’s also used for authentication. While...
-
 209
209Android Trojan Hijacks Google Play Store, Covertly Downloads or Purchases Apps
Security researchers have discovered a new Android trojan named Skyfin that can infiltrate the local Play Store Android app and download or...
-
 195
195DOCKER PATCHES CONTAINER ESCAPE VULNERABILITY
Docker has patched a privilege escalation vulnerability (CVE-2016-9962) that could lead to container escapes, allowing a hacker to affect operations of a...
-

 240
240Secret tokens found hard-coded in hundreds of Android apps
In some cases, the hard-coded secrets could allow an attacker to steal or delete data. A security research firm has found hundreds...
-

 147
147Hackers demonstrate how to hack Samsung SmartCam
Researchers Exploitee.rs discovered a flaw in Samsung SmartCam IP cameras that could be exploited to execute commands and hijack vulnerable devices. Samsung...
-
 146
146This phishing email uses an unexpected trick to infect PCs with keylogger malware
Rather than using macros, this malware uses Visual Basic Script to avoid detection. Cybercriminals are targeting a US major financial services provider...
-
 117
117Insidious phishing attack leverages on fake attachments to steal Gmail credentials
Cybercriminals are adopting specially crafted URLs to trick users into entering their Gmail credentials in a new sophisticated phishing campaign. Security experts...
-

 137
137Stealing passwords from McDonald’s users
By abusing an insecure cryptographic storage vulnerability (link) and a reflected server cross-site-scripting vulnerability (link) it is possible to steal and decrypt...
-

 211
211Intelligence report claims the Kremlin has cracked Telegram service
A raw intelligence document published last week claims Russian cyber experts have cracked Telegram messaging service to spy on opponents. A raw intelligence...
-

 227
227Internet Archive Launches Chrome Extension That Replaces 404 Pages With Archived Copies
The Internet Archive has launched on Friday a Chrome extension that will detect “Page not found” and other web errors and replace...
-

 197
197WordPress 4.7.1 released, patches eight vulnerabilities and 62 bugs
According to the release notes the latest version of WordPress 4.7.1 addresses eight security vulnerabilities and other 62 bugs. Wednesday the latest...
-

 88
88Hacker Steals 900 GB of Cellebrite Data
The hackers have been hacked. Motherboard has obtained 900 GB of data related to Cellebrite, one of the most popular companies in...
-

 88
88Adobe, Microsoft Push Critical Security Fixes
Adobe and Microsoft on Tuesday each released security updates for software installed on hundreds of millions of devices. Adobe issued an update...






