Vulnerabilities
-

 318
318Uncooperative Russian ISP Prevents Cisco from Shutting Down Cybercriminal Gang
Russian ISP Eurobyte fails to answer Cisco’s emails, allows malvertising campaign to go on undisturbed. Cisco’s Talos research team has managed to identify...
-
 149
149GM embraces white-hat hackers with public vulnerability disclosure program
First major automaker (aside from Tesla) to issue guidelines promising not to sue researchers. On January 5, General Motors quietly flipped the...
-

 184
184Drupal Update Process Flawed by Multiple Bugs, Attackers Can Take Over Sites
IOActive’s Fernando Arnaboldi has sounded the alarm on three major flaws in Drupal’s update process that may allow attackers to poison Drupal...
-

 213
213Severe Silent Circle Blackphone vulnerability lets hackers take over
The security-focused smartphone contained vulnerabilities which allow hackers to control the device’s modem and call functions. Researchers have revealed a severe vulnerability in...
-

 194
194Zerodium Offers $100K for Adobe Flash Heap Isolation Bypasses
Despite calls to eliminate Adobe Flash Player, researchers inside and outside the vendor continue to invest in and build mitigations against modern...
-

 107
107CVE-2015-8562 – 16,000 Daily Attacks on vulnerable Joomla servers
Experts at Symantec discovered that hackers quickly take advantage of CVE-2015-8562 remote code execution to compromise Joomla servers. Joomla recently patched the CVE-2015-8562...
-

 120
120Patch now! Flash-exploitin’ PC-hijackin’ attack spotted in the wild by Huawei bods
Adobe squeezes out one last batch of security fixes for 2015. Adobe has issued new versions of Flash to patch a load...
-

 160
160Quantum cryptography ‘is vulnerable to attack’
Quantum cryptography, considered to be one of the most complex and unbreakable methods of encryption, has been found to be vulnerable to...
-
 194
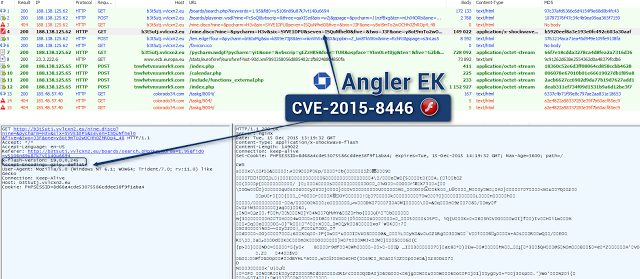
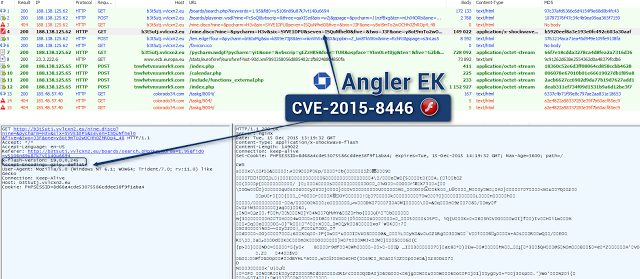
194Angler exploit kit includes the code of a recent Flash flaw
A security researcher discovered a new variant of the Angler exploit kit that includes the exploit code for a recently patched Adobe...
-
 246
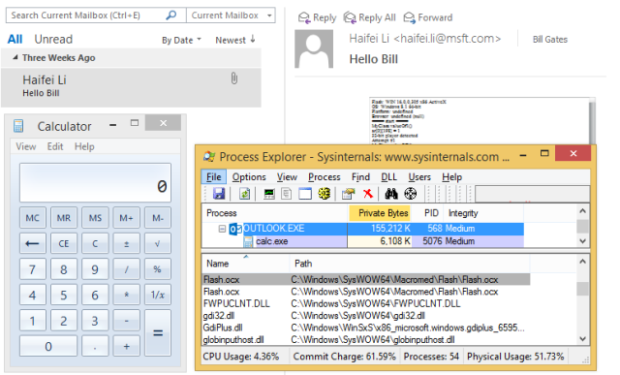
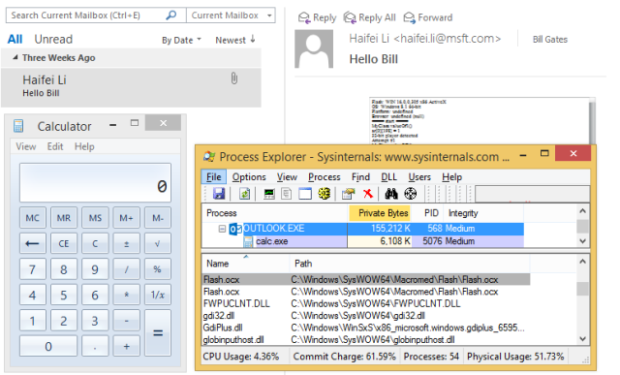
246Outlook “letterbomb” exploit could auto-open attacks in e-mail
Fixed by Microsoft’s latest patches, bug could be “enterprise killer,” says researcher. One of a heaping collection of critical bug fixes pushed...
-
 113
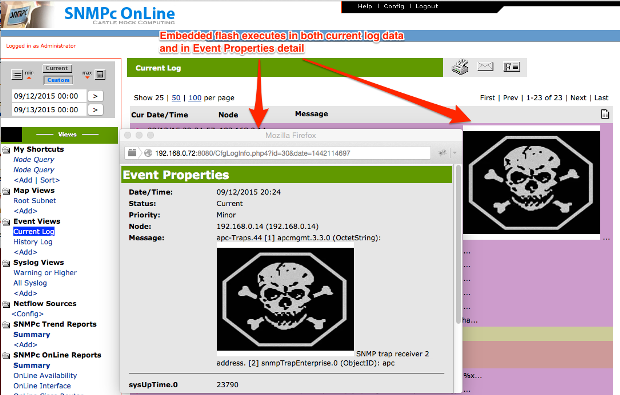
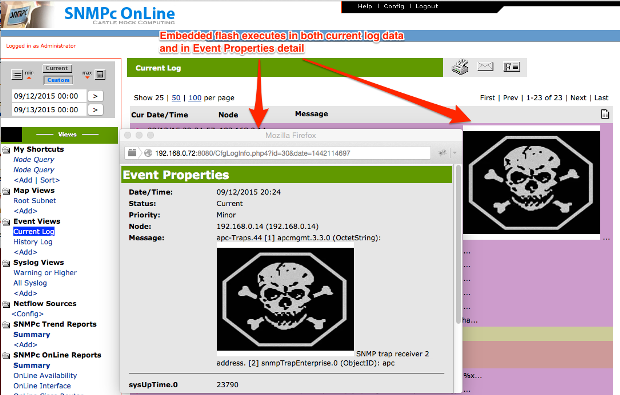
113Four Network Management Systems Vulnerable to SQLi and XSS Attacks
Today, Rapid7 is disclosing several vulnerabilities affecting several Network Management System (NMS) products. These issues were discovered by Deral Heiland of Rapid7...
-

 225
225Hackers actively exploit critical vulnerability in sites running Joomla
Wave of attacks grows. Researchers advise sites to install just-released patch. Attackers are actively exploiting a critical remote command-execution vulnerability that has...
-

 164
164‘Fairly bad core bug’ crushed in Linux 4.4-rc5
Linus Torvalds says almost no-one ‘actually ever hit the problem’, or will code at Xmas. Linux Lord Linus Torvalds says the fourth...
-

 226
226Hackers add exploit kit to article asking ‘Is cyber crime out of control?’
Net menaces show warped sense of humour in attack onGrauniad story. Hackers have hosed an article published by The Guardian using the...
-

 103
103Steam tightens trading security amid 77,000 monthly account hijackings
Traded items will be “held” for days unless you have two-factor security. Account theft is a common and longstanding problem for all...
-

 178
178Kaspersky, McAfee, and AVG all vulnerable to major flaw
Researchers watch the watchmen. Some of the biggest names in the security software business have been compromised by a serious flaw that...
-

 163
163Apple Patches 50 Vulnerabilities Across iOS, OS X, Safari
Apple has piled on the patches already released by Adobe and Microsoft today, and pushed out updates for iOS, OS X, Apple...
-

 138
138Google patches critical vulnerabilities in Android
The flaws can be exploited remotely through emails, Web pages, MMS and rogue apps. Google has released a new batch of security fixes...
-

 123
123Java Deserialization Vulnerability Found in More Java Libraries
Initial issues trickle down to other Java toolkits.Exactly a month ago, we were reporting on an issue that exposed many Java applications...
-
 225
2253-Year-Old Vulnerability Affects Millions of Smart TVs, Phones, and Routers
Trend Micro reports that 6.1 million devices are affected.A 3-year-old bug in the Portable SDK for UPnP Devices, also called libupnp, is...
-
 276
276ElasticZombie Botnet – Exploiting Elasticsearch Vulnerabilities
With the rise of inexpensive Virtual Servers and popular services that install insecurely by default, coupled with some juicy vulnerabilities, like CVE-2015-5377...






