Vulnerabilities
-

 4.0K
4.0KBeware: Experts Reveal New Details on Zero-Click Outlook RCE Exploits
Technical details have emerged about two now-patched security flaws in Microsoft Windows that could be chained by threat actors to achieve remote...
-

 3.4K
3.4KNew Security Vulnerabilities Uncovered in pfSense Firewall Software – Patch Now
Multiple security vulnerabilities have been discovered in the open-source Netgate pfSense firewall solution called pfSense that could be chained by an attacker...
-
 2.3K
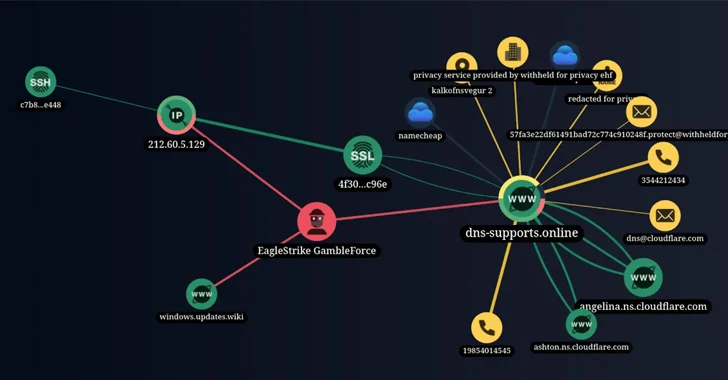
2.3KNew Hacker Group ‘GambleForce’ Tageting APAC Firms Using SQL Injection Attacks
A previously unknown hacker outfit called GambleForce has been attributed to a series of SQL injection attacks against companies primarily in the...
-
 2.7K
2.7KApple Releases Security Updates to Patch Critical iOS and macOS Security Flaws
Apple on Monday released security patches for iOS, iPadOS, macOS, tvOS, watchOS, and Safari web browser to address multiple security flaws, in...
-

 4.5K
4.5KNew Critical RCE Vulnerability Discovered in Apache Struts 2 – Patch Now
Apache has released a security advisory warning of a critical security flaw in the Struts 2 open-source web application framework that could...
-

 356
356Lazarus Group Using Log4j Exploits to Deploy Remote Access Trojans
The notorious North Korea-linked threat actor known as the Lazarus Group has been attributed to a new global campaign that involves the...
-
 1.5K
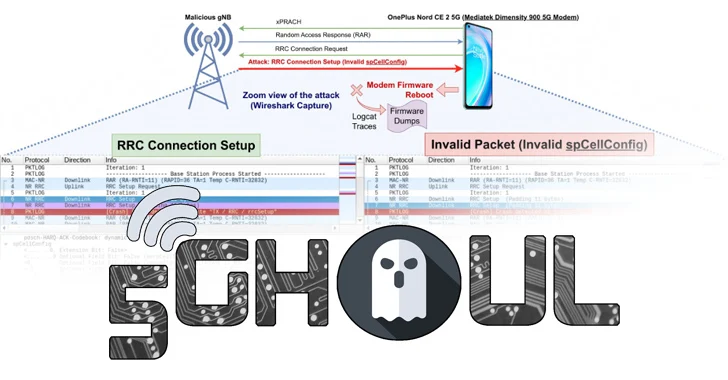
1.5KNew 5G Modem Flaws Affect iOS Devices and Android Models from Major Brands
A collection of security flaws in the firmware implementation of 5G mobile network modems from major chipset vendors such as MediaTek and...
-

 564
564WordPress Releases Update 6.4.2 to Address Critical Remote Attack Vulnerability
WordPress has released version 6.4.2 with a patch for a critical security flaw that could be exploited by threat actors by combining...
-

 3.0K
3.0KNew Bluetooth Flaw Let Hackers Take Over Android, Linux, macOS, and iOS Devices
A critical Bluetooth security flaw could be exploited by threat actors to take control of Android, Linux, macOS and iOS devices. Tracked...
-
 955
955Hacking the Human Mind: Exploiting Vulnerabilities in the ‘First Line of Cyber Defense’
Humans are complex beings with consciousness, emotions, and the capacity to act based on thoughts. In the ever-evolving realm of cybersecurity, humans...
-
 3.2K
3.2KNew Stealthy ‘Krasue’ Linux Trojan Targeting Telecom Firms in Thailand
A previously unknown Linux remote access trojan called Krasue has been observed targeting telecom companies in Thailand by threat actors to main...
-

 4.4K
4.4KOver 86,000 Routers at Risk – Is Yours One of Them? Shocking Vulnerabilities in Widely Used OT/IoT Routers
The research Sierra:21 – Living on the Edge” presents an analysis of vulnerabilities found in Sierra Wireless AirLink cellular routers, which are...
-
 4.0K
4.0KNew Report: Unveiling the Threat of Malicious Browser Extensions
Compromising the browser is a high-return target for adversaries. Browser extensions, which are small software modules that are added to the browser...
-

 4.1K
4.1KHackers Exploited ColdFusion Vulnerability to Breach Federal Agency Servers
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned of active exploitation of a high-severity Adobe ColdFusion vulnerability by unidentified threat actors...
-

 2.4K
2.4KQualcomm Releases Details on Chip Vulnerabilities Exploited in Targeted Attacks
Chipmaker Qualcomm has released more information about three high-severity security flaws that it said came under “limited, targeted exploitation” back in October...
-
 5.2K
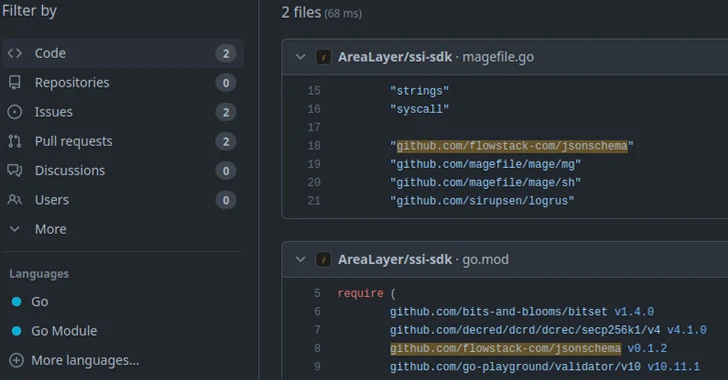
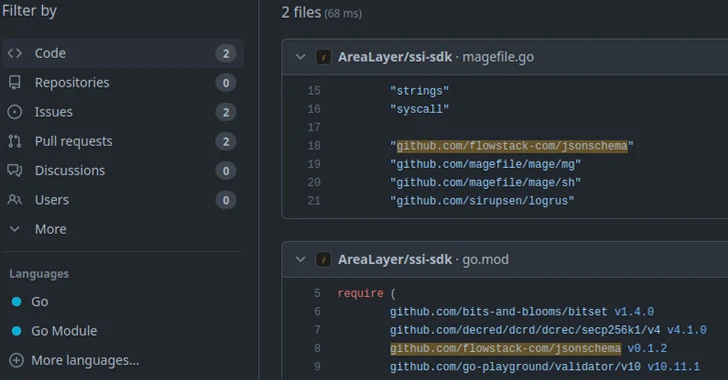
5.2K15,000 Go Module Repositories on GitHub Vulnerable to Repojacking Attack
New research has found that over 15,000 Go module repositories on GitHub are vulnerable to an attack called repojacking. “More than 9,000...
-

 5.0K
5.0KMicrosoft Warns of Kremlin-Backed APT28 Exploiting Critical Outlook Vulnerability
Microsoft on Monday said it detected Kremlin-backed nation-state activity exploiting a now-patched critical security flaw in its Outlook email service to gain...
-
 4.7K
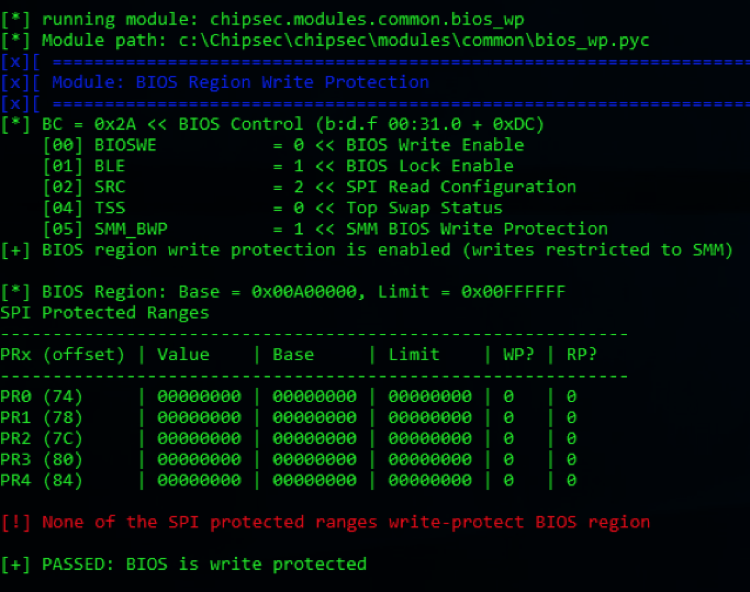
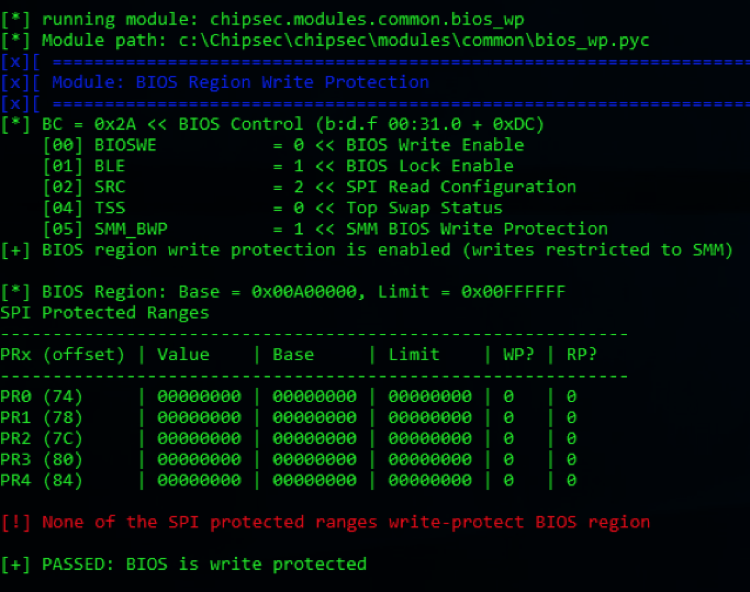
4.7KInside LogoFAIL: The UEFI Firmware Flaw Compromising Millions of Devices
In the ever-evolving landscape of cybersecurity, a new threat has emerged, casting a long shadow over the integrity of computer systems worldwide....
-

 3.7K
3.7KNew P2PInfect Botnet MIPS Variant Targeting Routers and IoT Devices
Cybersecurity researchers have discovered a new variant of an emerging botnet called P2PInfect that’s capable of targeting routers and IoT devices. The...
-
 2.4K
2.4KCACTUS Ransomware Exploits Qlik Sense Vulnerabilities in Targeted Attacks
A CACTUS ransomware campaign has been observed exploiting recently disclosed security flaws in a cloud analytics and business intelligence platform called Qlik...
-

 1.6K
1.6KGoTitan Botnet Spotted Exploiting Recent Apache ActiveMQ Vulnerability
The recently disclosed critical security flaw impacting Apache ActiveMQ is being actively exploited by threat actors to distribute a new Go-based botnet...






