Vulnerabilities
-
 187
187‘HIGH RISK’ ZERO DAY LEAVES 200,000 MAGENTO MERCHANTS VULNERABLE
A popular version of the open source Magento ecommerce platform is vulnerable to a zero-day remote code execution vulnerability, putting as many...
-

 169
169Copy-Pasting Sundown Exploit Kit Has Been Offline for More Than a Month
King of copy-paste exploits, the Sundown exploit kit, has been offline since March 8, and this also includes most of its variations,...
-
 239
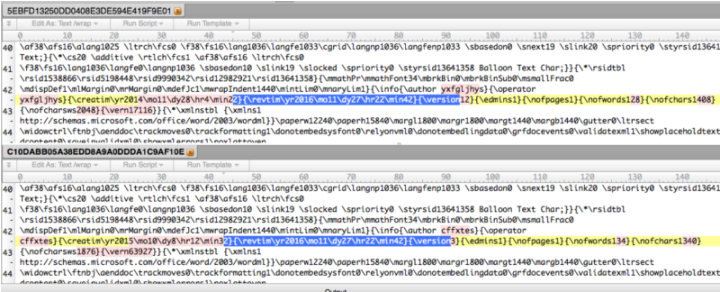
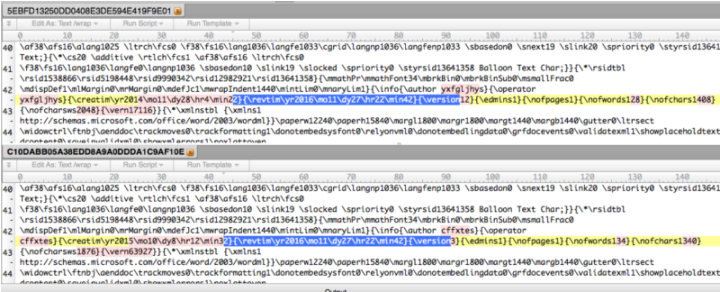
239Microsoft Word 0-day was actively exploited by strange bedfellows
Same exploit used by malware crooks and nation-sponsored hackers targeting Russians. A critical Microsoft Word zero-day that was actively exploited for months...
-

 193
193SAP UPDATES TWO-YEAR-OLD PATCH FOR TREX VULNERABILITY
SAP has issued an updated patch for a code-injection vulnerability affecting the TREX search engine integrated into more than a dozen SAP...
-
 176
176MICROSOFT PATCHES THREE VULNERABILITIES UNDER ATTACK
Microsoft today patched a zero-day Word vulnerability that has been publicly attacked along with deploying fixes for Internet Explorer, Microsoft Edge and...
-

 351
351Adobe Publishes Security Updates for Flash, Reader, Photoshop, and Creative Cloud
Earlier today, Adobe has released security patches for several of its applications, including Adobe Flash Player, Adobe Campaign, Adobe Photoshop CC, the...
-
 94
94RIVERBED PATCHES VULNERABILITIES IN APPLICATION MONITORING PORTAL
Riverbed Technology has patched four serious vulnerabilities in its SteelCentral portal, a centralized application performance monitoring platform. The flaws could allow an...
-

 198
198Longhorn Cyber-Espionage Group Is Actually the CIA
Security researchers from Symantec have tied the CIA hacking tools leaked by WikiLeaks last month to a cyber-espionage group responsible for at...
-

 83
83Epic Fail: TP-Link 3G Router Spews Admin Password via SMS
A particular TP-Link router model will spew out its admin password in cleatext to anyone that sends an SMS message to the...
-
 140
140Critical Office Zero-Day Attacks Detected in the Wild
At McAfee, we have put significant efforts in hunting attacks such as advanced persistent threats and “zero days.” Yesterday, we observed suspicious...
-
 171
171Shadow Brokers Publish the Password for the Rest the Stolen NSA Hacking Tools
The Shadow Brokers (TSB) are back, and they’ve released the password for the rest of the hacking tools they claim to have...
-

 288
288New Zero Day Attack Discovered in MS Word Document Uses to Hack your PC – Still Not yet Patched
[jpshare] MS word Document is on of the main Vector to easily spread the Macro viruses to the Victims. an undisclosed vulnerability has been...
-

 494
494iCloud Mail Phishing Scam Wants to Steal Apple Accounts, Banking Data, Identity
If you follow the steps in the phishing email, you may end up giving attackers a way into stealing your identity. Apple...
-

 192
192Australian Dark Web Hacking Campaign Unmasked Hundreds Globally
The investigation into The Love Zone child pornography site was much larger in scope than previously thought. Last year, Motherboard found Australian...
-

 209
209Ransomware Gang Made Over $100,000 by Exploiting Apache Struts Zero-Day
For more than a month, at least ten groups of attackers have been compromising systems running applications built with Apache Struts and...
-

 251
251Linux-based Tizen OS Is Easily Hackable — Samsung’s Open Source Android Replacement
Short Bytes: There are good chances that you might’ve heard about Samsung’s Android replacement Tizen OS. Recently, an Israeli researcher uncovered 40 zero-days in...
-

 105
105Hackers Empty ATMs by Drilling One Small Hole
Hackers are using a combination of low and high-tech attacks to make ATMS spit out cash, according to Kaspersky researcher Igor Soumenkov,...
-

 123
123Google and Apple Issue Security Updates for Critical Broadcom WiFi Vulnerabilities
Owners of Android and iOS devices should pay special attention to security updates released by Google and Apple on Monday, as they...
-
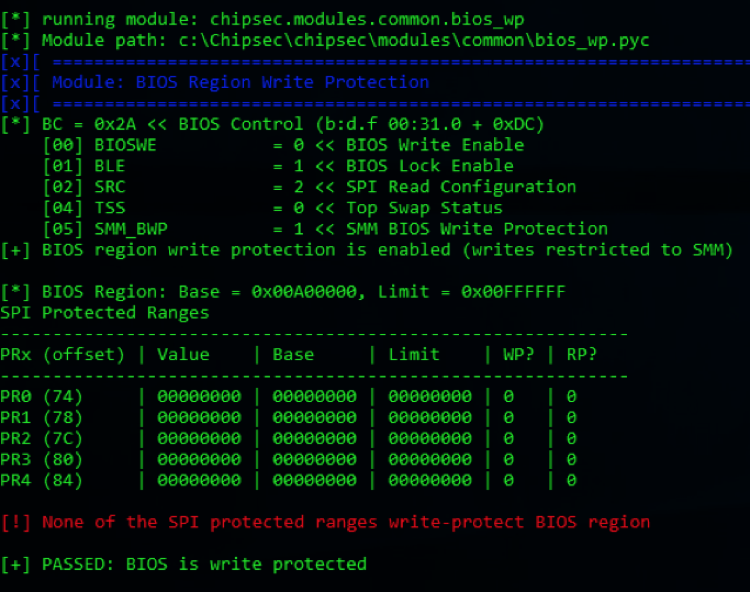
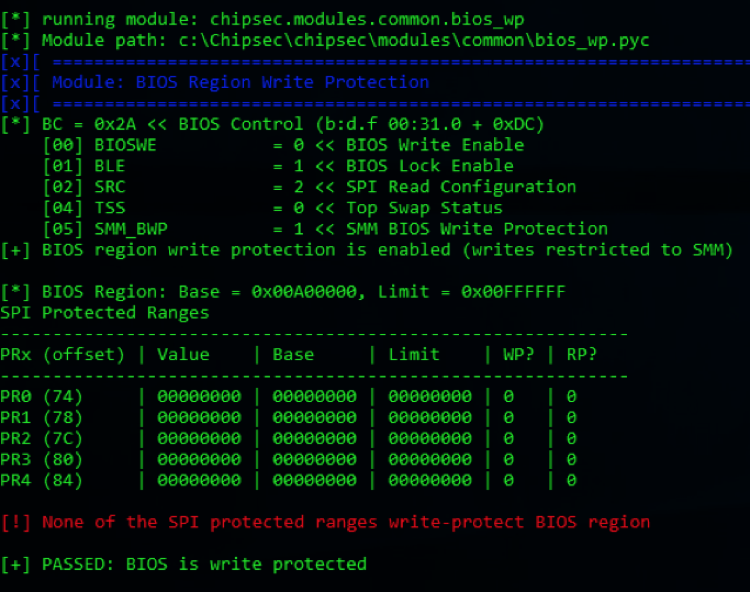 196
196UEFI Vulnerabilities allow to fully compromise Gigabyte Mini PCs
Experts at Cylance disclosed two UEFI flaws that can be exploited by attackers to install a backdoor on some Gigabyte BRIX mini...
-

 132
132Hackers Can Easily Hijack This Dildo Camera and Livestream the Inside of Your Vagina
The Internet of Shit gets up close and personal. If you’re using an internet-connected vibrator equipped with a camera that allows you...
-
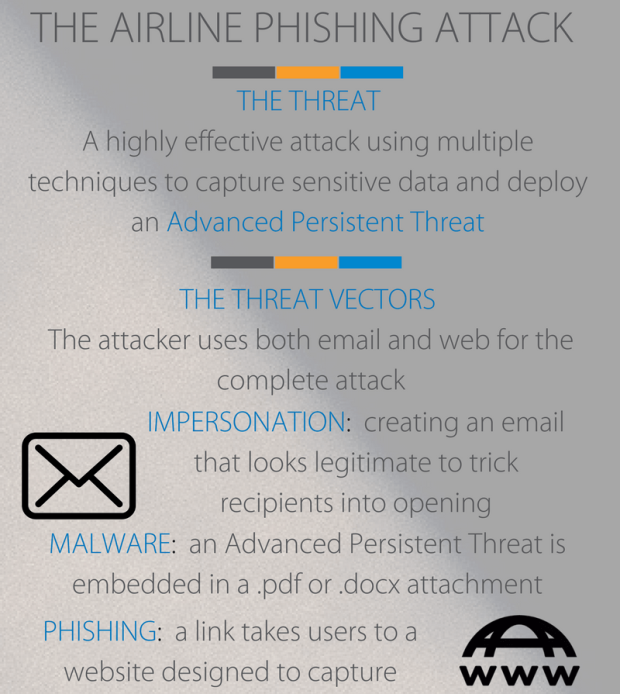
 177
177Phishing campaigns target airline consumers seeking business credentials
A series of phishing campaigns is targeting airline consumers with messages crafted to trick victims into handing over personal or business credentials....






