A malicious Chrome and Edge Browser Extension delivers powerful backdoor to stealing information from the browsers and monitor the victim’s activities.
A downloader that delivers the malware payload that contains Revisit remote administration tool along with a backdoor extension to hijack the infected system.
The two payloads are apparently distributing from a group of Malware authors called Moldova who is delivering this backdoor and RAT via malicious attachments contains spam emails.
Previously Various malware attacks that were targeted to legitimate remote access tools likewise TeamSpy malware that abuses TeamViewer to take over affected systems remotely which is not a new method.
But attacker still abusing the legitimate windows tools and open source tools such as Chrome WebDriver and Microsoft WebDriver.
How Does This Backdoor Works
This malware using various social engineering technique in an email along with an attachment that contains embedded document malicious macro which is heavily obfusticated.
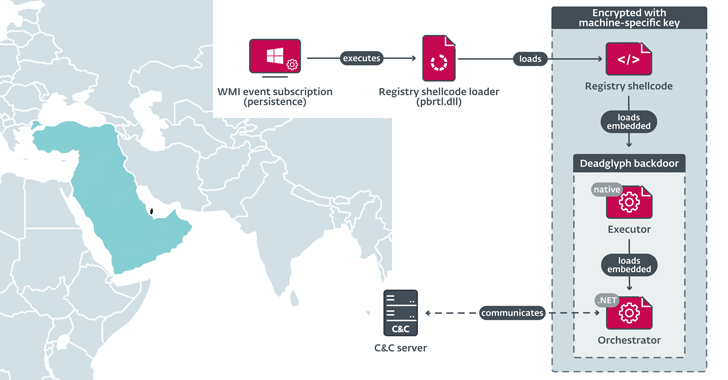
Once the malicious dropper executed a JavaScript file that has packed with ZIP archive which contains two kinds of payloads- one based on Java and another based on NodeJS.

NodeJS payload packed with ZIP archive that contains several files. once the users enable the macro then it executes the node.exe install.js which contains installation script to check the administrator rights and the groups to confirm the user.
later it calls install.vbs to escalate the privilege and add new firewall rules to enable traffic between the remote access tool it will install.
According to Trend Micro, “It establishes persistence by adding shortcut (LNK) files in the Startup folder. install_do.js will also install a browser extension to the system’s browser extension directory and creates a timestamp.dat file.”
 NodeJS extension leads to execute the remote access tool and kill the currently opened web browser via taskkill /IM <filename> then executes a certain revisit 0.63 application which is legitimate and signed remote access tool.
NodeJS extension leads to execute the remote access tool and kill the currently opened web browser via taskkill /IM <filename> then executes a certain revisit 0.63 application which is legitimate and signed remote access tool.
later all the stolen documents are uploaded from remote access tool to the command-and-control (C&C) server. Attackers will now see the machine ID and password, allowing them to connect to the victim’s machine remotely and gain full control over it.
Browser Extension Backdoor
Once the NodeJS and Java modules detect Chrome and Edge Browser open then it will kill the original browser extension and create another one and it will load the malicious extension in the new process.
Later it disables security checks and proceeds to load the malicious extension and the researchers found this malicious extension in Chrome but they confirm that the extension comfortable with Edge.
“This compatibility was a feature introduced by Microsoft last year to help developers port their Chrome extensions to Edge. Selenium is also used to load the extension into Edge.”
The loaded malicious extension designed as a backdoor and it will keep collecting the users opening webpage and URL and send it to the attacker via C&C server.