What do you mean by social engineering?
Social engineering is the art of manipulating users of a computing system into revealing confidential information. The term can also include activities such as exploiting human kindness, greed and curiosity. To gain access to restricted access buildings or getting the users to installing backdoor software.
HERE,
This is the first stage, learn as much as he can about the intended victim. The information taken from company web sites, and sometimes by talking to the users of the target system.
- Plan Attack: The attackers outline how he/she intends to execute the attack
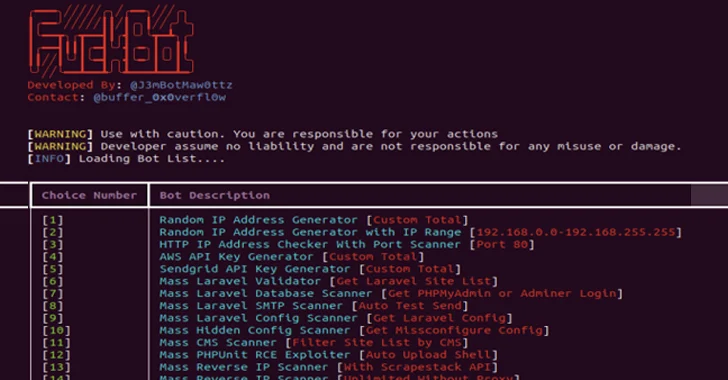
- Acquire Tools: These include computer programs that an attacker will use when launching the attack.
- Attack: Exploit the weaknesses in the target system.
Information gathered during the social engineering tactics such as names, birth dates of the organization founders etc for password guessing.
Social Engineering Techniques:
Social engineering techniques can take many forms. The following is the list of the commonly used techniques.
Familiarity Exploit
Users are less suspicious of individuals they’re accustomed to. AN assaulter will inform him/herself with the users of the target system before the social engineering attack. The assaulter could move with users throughout meals, once users are smoking he could be part of, on social events etc. This makes the assaulter acquainted to the users. Let’s suppose that the user works into a building that needs AN access code or card to realize access .The assaulter could follow the users as they enter such places.
The users are most prefer to hold the door open for the assaulter to travel in as they’re accustomed to them. The assaulter may kindle answers to queries like wherever you met your domestic partner. The users ar possibly to reveal answers as they trust the acquainted face. This data can be wont to hack email accounts,other accounts that raise similar queries if one forgets word.
Intimidating Circumstances
People tend to avoid those that intimidate others around them. The assaulter might faux to own a heated argument on phone or with associate degree confederate within the theme. The assaulter might then raise users for info which might be wont to compromise the safety of the users’ system. The users are presumably provide the proper answers simply to avoid having a confrontation with the assaulter. this system may be wont to avoid been checked at a security check purpose.
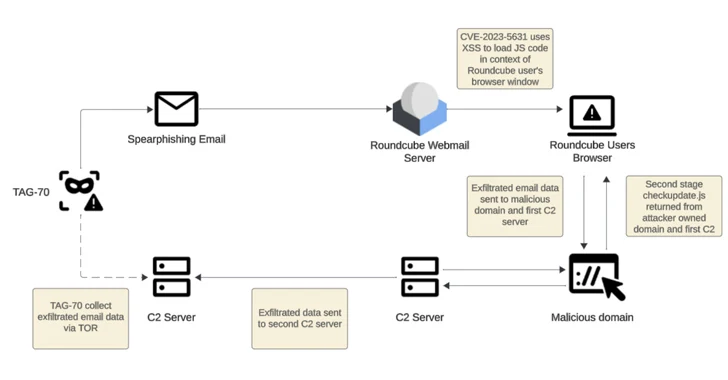
Phishing: this system uses trickery and deceit to get personal knowledge from users. The social engineer mighttry and impersonate a real web site like yahoo so raise the unsuspecting user to verify their account name and positive identification. this system may even be wont to get mastercard info or the other valuable personal knowledge.
Tailgating: this system involves following users behind as they enter restricted areas. As somebody’s courtesy, the user is presumably to let the social engineer within the restricted space.
Exploiting human curiosity: exploitation this system, the social engineer might deliberately drop an outbreakinfected flash disk in a district wherever the users will simply decide it up. The user can presumably plug the flash disk into the pc. The flash disk might motorcar run the virus or the user is also tempted to open a file with a reputation like workers assessment Report 2013.docx which can truly be associate degree infected file.
Exploiting human greed: exploitation this system, the social engineer might lure the user with guarantees of constructing lots of cash on-line by filling in an exceedingly type and ensure their details exploitationmastercard details etc.
Social Engineering Counter Measures
Most techniques employed by social engineers involve manipulating human biases. To counter such techniques, an organization can;
To counter the familiarity exploit, the users must be trained to not substitute familiarity with security measures. Even the people that they are familiar with must prove that they have the authorization to access certain areas and information.
To counter intimidating circumstances attacks, users must be trained to identify social engineering techniques that fish for sensitive information and politely say no.
For counter phishing techniques, most sites such as yahoo use secure connections to encrypt data and prove that they are who they claim to be. Checking the URL may help you spot fake sites. Avoid responding to emails that request you to provide personal information.
To counter tailgating attacks, users must be trained not to let others use their security clearance to gain access to restricted areas. Each user must use their own access clearance.
To counter human curiosity, it’s better to submit picked up flash disks to system administrators who should scan them.
To counter techniques that exploit human greed, employees must be trained on the dangers of falling for such scams.