A threat actor affiliated with Iran’s Ministry of Intelligence and Security (MOIS) has been observed waging a sophisticated cyber espionage campaign targeting financial, government, military, and telecommunications sectors in the Middle East for at least a year.
Israeli cybersecurity firm Check Point, which discovered the campaign alongside Sygnia, is tracking the actor under the name Scarred Manticore, which is said to closely overlap with an emerging cluster dubbed Storm-0861, one of the four Iranian groups linked to destructive attacks on the Albanian government last year.
Victims of the operation span various countries such as Saudi Arabia, the United Arab Emirates, Jordan, Kuwait, Oman, Iraq, and Israel.
Scarred Manticore also exhibits some degree of overlap with OilRig, another Iranian nation-state crew that was recently attributed to an attack on an unnamed Middle East government between February and September 2023 as part of an eight-month-long campaign.
Another set of tactical overlaps have been discovered between the adversary and an intrusion set codenamed ShroudedSnooper by Cisco Talos. Attack chains orchestrated by the threat actor have singled out telecom providers in the Middle East using a stealthy backdoor known as HTTPSnoop.
The activity represented by Scarred Manticore is characterized by the use of a previously unknown passive malware framework referred to as LIONTAIL that’s installed on Windows servers. The threat actor is believed to be active since at least 2019.
“Scarred Manticore has been pursuing high-value targets for years, utilizing a variety of IIS-based backdoors to attack Windows servers,” Check Point researchers said in a Tuesday analysis. “These include a variety of custom web shells, custom DLL backdoors, and driver-based implants.”
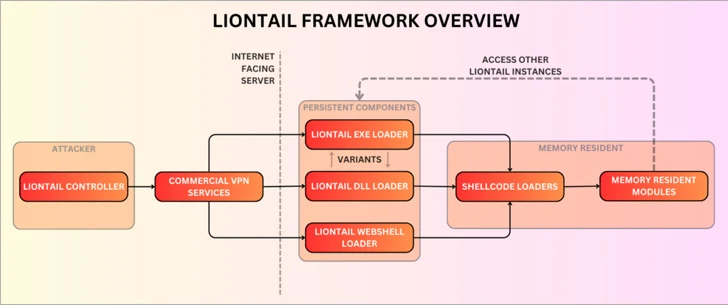
An advanced piece of malware, LIONTAIL is a collection of custom shellcode loaders and memory resident shellcode payloads. A noteworthy component of the framework is a lightweight-yet-sophisticated implant written in C that enables attackers to execute commands remotely via HTTP requests.
The attack sequences entail infiltrating publicly facing Windows servers to kick off the malware delivery process and systematically harvest sensitive data from infected hosts.
“Instead of using the HTTP API, the malware uses IOCTLs to interact directly with the underlying HTTP.sys driver,” the researchers said, detailing the command-and-control (C2) mechanism.
“This approach is stealthier as it doesn’t involve IIS or HTTP API, which are usually closely monitored by security solutions, but is not a straightforward task given that the IOCTLs for HTTP.sys are undocumented and require additional research efforts by the threat actors.”
It’s worth noting at this stage that the backdoor constituent of the LIONTAIL framework is the same as HTTPSnoop owing to the use of the HTTP.sys driver to extract payloads from incoming HTTP traffic.
From a technical standpoint, one intriguing facet of the operation is that the threat actor employs a tailor-made implant for each compromised server, allowing the malicious activities to blend into the victim environment and make it hard to distinguish between suspicious and legitimate network traffic.
Also deployed alongside LIONTAIL include various web shells and a web forwarder tool called LIONHEAD, a web forwarder.
Historical activity of Scarred Manticore indicates a continuous evolution of the group’s malware arsenal, what with the threat actor previously relying on web shells such as Tunna and a bespoke version called FOXSHELL for backdoor access.
Since mid-2020, the threat actor is also said to have used a .NET-based passive backdoor called SDD that establishes C2 communication through an HTTP listener on the infected machine with the ultimate goal of executing arbitrary commands, uploading and downloading files, and running additional .NET assemblies.
The progressive updates to the threat actor’s tactics and tools is typical of advanced persistent threat (APT) groups and demonstrates their resources and varied skills. This is best exemplified by Scarred Manticore’s use of a malicious kernel driver called WINTAPIX that was uncovered by Fortinet earlier this May.
In a nutshell, WinTapix.sys acts as a loader to execute the next stage of the attack, injecting an embedded shellcode into a suitable user mode process that, in turn, executes an encrypted .NET payload specifically designed to target Microsoft Internet Information Services (IIS) servers.
The targeting of Israel comes amid the ongoing Israel-Hamas war, prompting low-sophistication hacktivist groups to attack various organizations in the country, as well as nations like India and Kenya, suggesting nation-state actors’ reliance on information operations aimed at influencing the global perception of the conflict.
The U.S. Federal Bureau of Investigation (FBI), in a statement to the Senate Committee on Homeland Security and Governmental Affairs (HSGAC) earlier this week, warned that the situation has the potential to worsen the “cyber targeting of American interests and critical infrastructure” by Iran and non-state actors alike.
“LIONTAIL framework components share similar obfuscation and string artifacts with FOXSHELL, SDD backdoor, and WINTAPIX drivers,” Check Point said.
“Examining the history of their activities, it becomes evident how far the threat actor has come in improving their attacks and enhancing their approach which relies on passive implants.”