If Pulse Connect Secure gateway is part of your organization network, you need to be aware of a newly discovered critical zero-day authentication bypass vulnerability (CVE-2021-22893) that is currently being exploited in the wild and for which there is no patch available yet.
At least two threat actors have been behind a series of intrusions targeting defense, government, and financial organizations in the U.S. and elsewhere by leveraging critical vulnerabilities in Pulse Secure VPN devices to circumvent multi-factor authentication protections and breach enterprise networks.
“A combination of prior vulnerabilities and a previously unknown vulnerability discovered in April 2021, CVE-2021-22893, are responsible for the initial infection vector,” cybersecurity firm FireEye said on Tuesday, identifying 12 malware families associated with the exploitation of Pulse Secure VPN appliances.
The company is also tracking the activity under two threat clusters UNC2630 and UNC2717 (“UNC” for Uncategorized) — the former linked to a break-in of U.S. Defense Industrial base (DIB) networks, while the latter was found targeting a European organization in March 2021 — with the investigation attributing UNC2630 to operatives working on behalf of the Chinese government, in addition to suggesting possible ties to another espionage actor APT5 based on “strong similarities to historic intrusions dating back to 2014 and 2015.”
Attacks staged by UNC2630 are believed to have commenced as early as August 2020, before they expanded in October 2020, when UNC2717 began repurposing the same flaws to install custom malware on the networks of government agencies in Europe and the U.S. The incidents continued until March 2021, according to FireEye.
The list of malware families is as follows –
- UNC2630 – SLOWPULSE, RADIALPULSE, THINBLOOD, ATRIUM, PACEMAKER, SLIGHTPULSE, and PULSECHECK
- UNC2717 – HARDPULSE, QUIETPULSE, AND PULSEJUMP
Two additional malware strains, STEADYPULSE and LOCKPICK, deployed during the intrusions have not been linked to a specific group, citing lack of evidence.
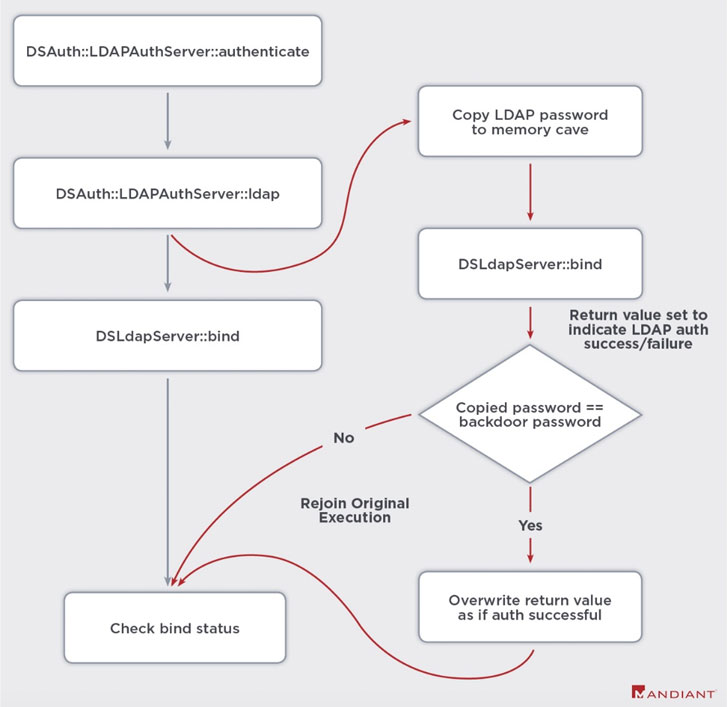
By exploiting multiple Pulse Secure VPN weaknesses (CVE-2019-11510, CVE-2020-8260, CVE-2020-8243, and CVE-2021-22893), UNC2630 is said to have harvested login credentials, using them to move laterally into the affected environments. In order to maintain persistence to the compromised networks, the actor utilized legitimate, but modified, Pulse Secure binaries and scripts to enable arbitrary command execution and inject web shells capable of carrying out file operations and running malicious code.
Ivanti, the company behind the Pulse Secure VPN, has released temporary mitigations to address the arbitrary file execution vulnerability (CVE-2021-22893, CVSS score: 10), while a fix for the issue is expected to be in place by early May. The Utah-based company acknowledged that the new flaw impacted a “very limited number of customers,” adding it has released a Pulse Connect Secure Integrity Tool for customers to check for signs of compromise.
Pulse Secure customers are recommended to upgrade to PCS Server version 9.1R.11.4 when it becomes available.
News of compromises affecting government agencies, critical infrastructure entities, and other private sector organizations comes a week after the U.S. government released an advisory, warning businesses of active exploitation of five publicly known vulnerabilities by the Russian Foreign Intelligence Service (SVR), including CVE-2019-11510, to gain initial footholds into victim devices and networks.