8 suspects behind 3VE have also been identified.
Last year in August, the Federal Bureau of Investigation organized a secret meet-up between cybersecurity and digital advertising experts in its Manhattan federal building. This included Google and nearly 20 tech firms while there were nearly 30 attendees at the meeting.
The agenda of the meeting was to devise a collaborative response strategy to thwart a massive ad fraud scheme called 3VE (“Eve”) that the bureau was investigating. According to the FBI, the ad fraud scheme was threatening the global ad industry – It is noteworthy that PornHub was also hacked during 3VE scheme.
A large-scale cyber-criminal network is reportedly involved in the creation of fake ad views and clicks that are being used to defraud ad networks and marketers. The scheme has been active for the past four years and so far the cybercriminals have made millions in illegal revenue.
Apart from a coordinated mediation to capture several criminal schemes botnets, the US Department of Justice (DOJ) has also announced to file a 13-count indictment against nearly eight suspects alleged to be involved in this scheme. Three of them have been arrested already and awaiting extradition to the United States.
The suspects are identified as:
Aleksandr Zhukov (38, Russia)
Boris Timokhin (39, Russia)
Mikhail Andreev (34, Russia and Ukraine)
Denis Avdeev (40, Russia)
Dmitry Novikov (age unknown, Russia)
Sergey Ovsyannikov (30, Kazakhstan)
Aleksandr Isaev (31, Russia)
Yevgeniy Timchenko (30, Kazakhstan)
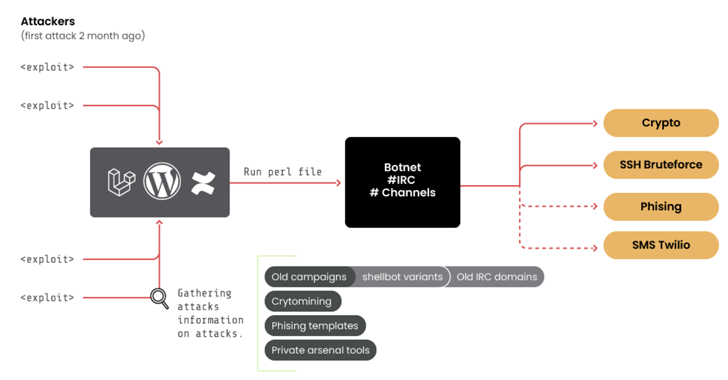
Google and cybersecurity firm White Ops have released a white paper [PDF] explaining the details of the 3VE scheme. Over time, according to investigators, a number of different schemes have been utilized by the operators of 3VE to generate more ad views and clicks. These include renting cybercrime botnets, hijacking IP address blocks, the creation of customized botnets hosted on different commercial data centers, using proxies for hiding original ID addresses, and developing websites to display these ads.
“3ve’s sheer size and complexity posed a significant risk not just to individual advertisers and publishers, but to the entire advertising ecosystem,” said Google.
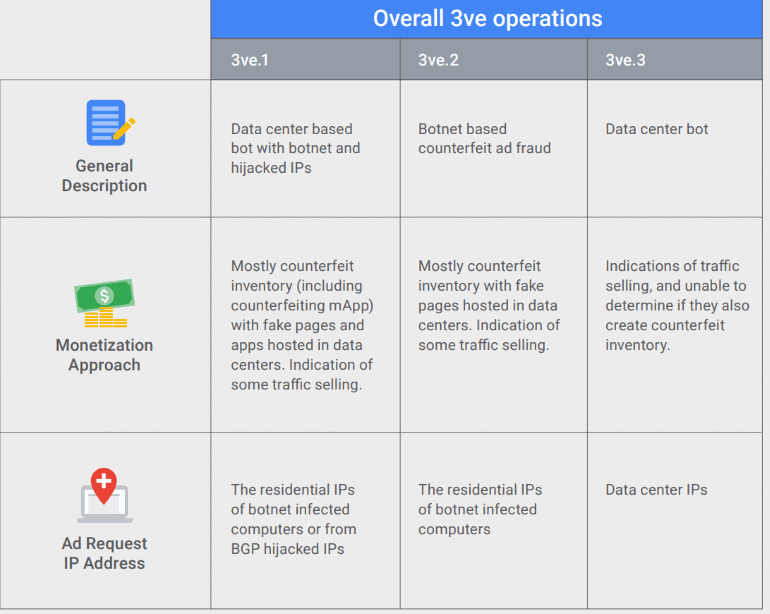
According to the observations of the companies collaborating in the investigations, 3VE’s operations can be categorized into three subgroups, and the dynamics of these groups are entirely different from each other.
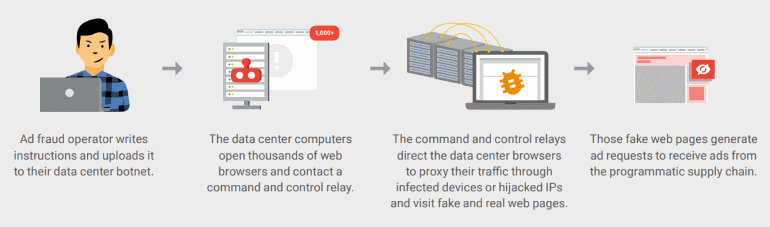
First Subgroup- 3VE.1
The 3ve.1 subgroup is a small component of a wide scale operation. WhiteOps dubbed it as MethBot, ESET termed it as Boaxxe, and Symantec has named it Miuref. The operations of this subgroup are powered by a network of bots, all of which are operating in various data centers located throughout the US and Europe.
The bots are basic scripts running on around 1,900 data center servers and have opened around 5,000 of counterfeit websites and web browsers that can hide the server’s IP address are also created using a fake proxy address. Fraudsters are making money by running fake ad networks that receive payments from different advertisers or ad networks for displaying ads on real websites.
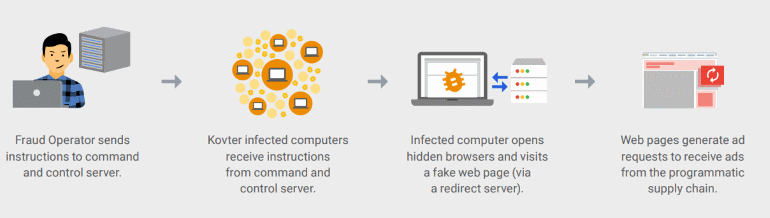
Second Subgroup- 3VE.2
After the advertising networks blacklisted the IP addresses linked with the 3ve.1 operations, cybercriminals changed their strategy and rented “install space” that Kovter malware botnet operators were offering. 3VE operators, hence, deployed a custom bot on nearly 700,000 computers to infect them with Kovter malware.
This bot could open hidden browser windows and could load websites operated by the 3VE gang to generate revenues like before. This time, instead of having data centers hosting bots, they used malware-infected computers.
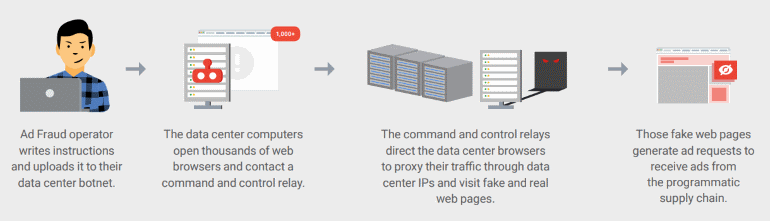
Third Subgroup- 3VE.3
It is simply a revamped version of 3VE.1 because it is almost identical to the first scheme with just two differences. The operators use a much smaller amount of data center bots this time and rented other data center servers to be used as proxies.
This time they didn’t hijack IP addresses from private networks. According to Google [PDF], this approach is although easier to detect, but 3VE operators adopted it to commit ad fraud way more efficiently.
We had to shut the operation down for good, which called for greater, more calculated measures. To that end, it was critical that we played the long game, endeavoring to have a more permanent, more powerful impact against this and future ad fraud operations, Google wrote in its whitepaper.
It is noteworthy that Trend Micro, Proofpoint, Malwarebytes, MediaMath, Amazon, CenturyLink, Adobe, F-Secure, and the National Cyber-Forensics and Training Alliance are some of the industry bigwigs participating in the investigation.