Researchers discovered a new malware dubbed “LookBack” distributed via spear-phishing email campaign to attack the entities in the United States.
Based on the telemetry data, the attack believed to be initiated by Chinese sponsored threat actors also known as APT 10, one of the sophisticated hacking group in the world and the group has a long history of targeting commercial activities including aviation, satellite, and maritime technology, industrial factory automation, finance, telecommunications and more.
Spear-phishing emails impersonate the US-based engineering licensing board and the email delivered from the threat actors who controlled domains nceess [.]com. Nceess[.]com which appears to be owned by the US National Council of Examiners for Engineering and Surveying.
Further analysis revealed that the spear-phishing emails carried malicious word documents with the macro that tricks victims to enable it to drop the malware dubbed “Lookback”.
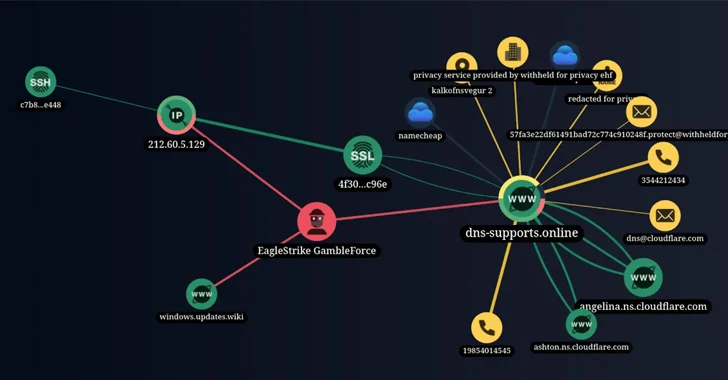
Researchers from Proofpoint found a remote access trojan associated with a proxy mechanism to establish a connection with the command & control server to communicate further operations.
Threat actors using a sophisticated delivery mechanism to deliver the Lookback malware to target the utilities and critical infrastructure.
LookBack Malware Exploitation Process
Through Malicious document, threat actors try to install the LookBack malware by tricking victims to enable the VBA macro which drops the three Privacy Enhanced Mail (PEM) files to the host: tempgup.txt, tempgup2.txt, and tempsodom.txt.
The result of LookBack malware execution, macro launches GUP.exe and the libcurl.dll loaders separately.
LookBack malware developed to act as a remote access trojan which is written in C++ that relies on a proxy communication tool which is responsible to transfer data from infected host to command & control server.
This RAT functionality is powerful enough to enumerate of services viewing of process, system, and file data; deleting files; executing commands; taking screenshots; moving and clicking the mouse; rebooting the machine and deleting itself from an infected host, Proofpoint reported.
Following components are carried by LookBack RAT,
A command and control proxy tool (referred to as GUP)
A malware loader comprised of a legitimate libcurl.dll file with one export function modified to execute shellcode.
A communications module (referred to as SodomNormal) which creates a C&C channel with the GUP proxy tool.
A remote access Trojan component (referred to as SodomMain), which is delivered following decoding the initial beacon response received via the GUP proxy tool and the SodomNormal local host proxy module.
A that is described in these components masquerade as legitimate opensource software and the legitimate GUP.exe versions were utilized that were digitally signed by Notepad++
The SodomMain module is LookBack malware’s remote access Trojan module that can send and receive numerous commands to the command and control server that including,
Get process listing
Kill process
Executes cmd[.] exe command
Gets drive type
Find files
Read files
Delete files
Write to files
Execute files
Enumerate services
Starts services
Delete services
Takes a screenshot of desktop
Move/Click Mouse and take a screenshot
Exit
Removes self (libcurl[.] dll)
Shutdown
Reboot
“The profile of this campaign is indicative of specific risk to US-based entities in the utility sector. Phishing emails leveraged the knowledge of the licensing bodies utilized within the utility sector for social engineering purposes that communicated urgency and relevance to their targets.” Proofpoint said.
Sponsored: Download Free GDPR Comics Book – Importance of Following General Data Protection Regulation (GDPR) to protect your Company Data and user privacy.
Also Read:
Chinese APT 10 Group Hacked Nearly 10 Telecom Networks and Stealing Users Call Records, PII, Credentials, Email Data and more