CyberX, a security firm has discovered that Ukraine is being targeted with an extensive cyber-reconnaissance operation. In this particular campaign, the targets are quite broad range and the basic purpose is to spy on confidential communications of key Ukrainian officials by remotely controlling PC microphones. Apart from Ukraine, CyberX has identified targets in Russia as well and to some extent in Austria and Saudi Arabia. Some of the targets are also discovered in the separatists’ states of Luhansk and Donetsk, which the Ukraine refers to as terrorist groups.
In this campaign, which has been dubbed by CyberX as Operation BugDrop, DropBox is used to store the acquired data. As per their research, 70 victims have been targeted successfully by the cyber-criminals. The victims come from a variety of fields including critical infrastructure, scientific research and media, etc.
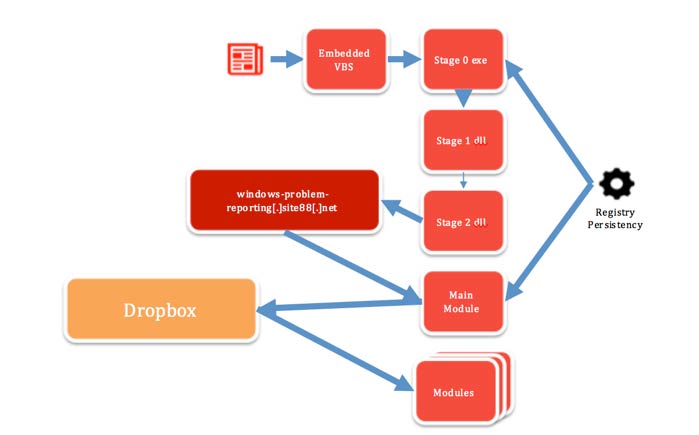
Malware architecture used in this campaign
In this operation, the focus is upon capturing sensitive information such as audio recordings of communications, login credentials, documents and screenshots. Usually, users can block video recordings by placing a tape upon the lens of the webcam but blocking the microphone of a computer is impossible without manually disabling it by manipulating the hardware.
According to CyberX, in Ukraine BugDrop has so far targeted companies that design remote monitoring systems primarily for Oil and Gas pipeline infrastructures, organizations that monitor human rights, cyber-attacks on main infrastructures and counter-terrorism institutions and engineering company that develops electrical substations, water supply plants and gas distribution pipelines.
It is a pretty well-organized operation in which very sophisticated malware is utilized and apparently a resourceful organization is sponsoring it. The operation is launched via a large back-end infrastructure that stores, decrypts and analyses various GB of unstructured data obtained from the victims on a daily basis. Moreover, a massive team of human analysts is required to sort out and process the captured data manually or using analytic tools like Big Data. It is worth noting that use of DropBox for data exfiltration is a strategically wise decision since it cannot be blocked or tracked by corporate firewalls.
[fullsquaread][/fullsquaread]
The malware infects the target computer using phishing emails in which malicious macros are embedded inside Microsoft Office attachments and users are tricked with sophisticated social engineering skills so that they activate the macros manually if these do not get activated on their own. CyberX stated that just a few anti-malware scanners could detect BugDrop, which is quite unfortunate.
For more technical details it is highly recommended to read CyberX’s blog post.
DDoS attacks are increasing, calculate the cost and probability of a DDoS attack on your business with this DDoS Downtime Cost Calculator.








